AWS Security Blog
Introducing AWS IAM Identity Center
September 12, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here.
Today, AWS introduced AWS IAM Identity Center (AWS IAM Identity Center), a service that makes it easy for you to centrally manage IAM Identity Center access to multiple AWS accounts and business applications. AWS IAM Identity Center provides a user portal so that your users can find and access all of their assigned accounts and applications from one place, using their existing corporate credentials. AWS IAM Identity Center is integrated with AWS Organizations to enable you to manage access to AWS accounts in your organization. In addition, AWS IAM Identity Center supports Security Assertion Markup Language (SAML) 2.0, which means you can extend IAM Identity Center access to your SAML-enabled applications by using the AWS IAM Identity Center application configuration wizard. AWS IAM Identity Center also includes built-in IAM Identity Center integrations with many business applications, such as Salesforce, Box, and Office 365.
In this blog post, I help you get started with AWS IAM Identity Center by answering three main questions:
- What benefits does AWS IAM Identity Center provide?
- What are the key features of AWS IAM Identity Center?
- How do I get started?
1. What benefits does AWS IAM Identity Center provide?
You can connect your corporate Microsoft Active Directory to AWS IAM Identity Center so that your users can sign in to the user portal with their user names and passwords to access the AWS accounts and applications to which you have granted them access. The following screenshot shows an example of the AWS IAM Identity Center user portal.

You can use AWS IAM Identity Center to centrally assign, manage, and audit your users’ access to multiple AWS accounts and SAML-enabled business applications. You can add new users to the appropriate Active Directory group, which automatically gives them access to the AWS accounts and applications assigned for members of that group. AWS IAM Identity Center also provides better visibility into which users accessed which accounts and applications from the user portal by recording all user portal sign-in activities in AWS CloudTrail. AWS IAM Identity Center records details such as the IP address, user name, date, and time of the sign-in request. Any changes made by administrators in the AWS IAM Identity Center console also are recorded in CloudTrail, and you can use security information and event management (SIEM) solutions such as Splunk and Sumo Logic to analyze the associated CloudTrail logs.
2. What are the key features of AWS IAM Identity Center?
AWS IAM Identity Center includes the following key features.
AWS IAM Identity Center user portal: In the user portal, your users can easily find and access all applications and AWS accounts to which you have granted them access. Users can access the user portal with their corporate Active Directory credentials and access these applications without needing to enter their user name and password again.
Integration with AWS Organizations: AWS IAM Identity Center is integrated with Organizations to enable you to manage access to all AWS accounts in your organization. When you enable AWS IAM Identity Center in your organization’s master account, AWS IAM Identity Center lists all the accounts managed in your organization for which you can enable IAM Identity Center access to AWS consoles.
Integration with on-premises Active Directory: AWS IAM Identity Center integrates with your on-premises Active Directory by using AWS Directory Service. Users can access AWS accounts and business applications by using their Active Directory credentials. You can manage which users or groups in your corporate directory can access which AWS accounts.
Centralized permissions management: With AWS IAM Identity Center, you can centrally manage the permissions granted to users when they access AWS accounts via the AWS Management Console. You define users’ permissions as permission sets, which are collections of permissions that are based on a combination of AWS managed policies or AWS managed policies for job functions. AWS managed policies are designed to provide permissions for many common use cases, and AWS managed policies for job functions are designed to closely align with common job functions in the IT industry.
With AWS IAM Identity Center, you can configure all the necessary user permissions to your AWS resources in your AWS accounts by applying permission sets. For example, you can grant database administrators broad permissions to Amazon Relational Database Service in your development accounts, but limit their permissions in your production accounts. As you change these permission sets, AWS IAM Identity Center helps you keep them updated in all relevant AWS accounts, allowing you to manage permissions centrally.
Application configuration wizard: You can configure IAM Identity Center access to any SAML-enabled business application by using the AWS IAM Identity Center application configuration wizard.
Built-in IAM Identity Center integrations: AWS IAM Identity Center provides built-in IAM Identity Center integrations and step-by-step configuration instructions for many commonly used business applications such as Office 365, Salesforce, and Box.
Centralized auditing: AWS IAM Identity Center logs all sign-in and administrative activities in CloudTrail. You can send these logs to SIEM solutions such as Splunk and Sumo Logic to analyze them.
Highly available multi-tenant IAM Identity Center infrastructure: AWS IAM Identity Center is built on a highly available, AWS managed IAM Identity Center infrastructure. The AWS IAM Identity Center multi-tenant architecture enables you to start using the service quickly without needing to procure hardware or install software.
3. How do I get started?
To get started, connect your corporate Active Directory to AWS IAM Identity Center by using AWS Directory Service. You have two choices to connect your corporate directory: use AD Connector, or configure an Active Directory trust with your on-premises Active Directory. After connecting your corporate directory, you can set up accounts and applications for IAM Identity Center access. You also can use AWS Managed Microsoft AD in the cloud to manage your users and groups in the cloud, if you don’t have an on-premises Active Directory or don’t want to connect to on-premises Active Directory.
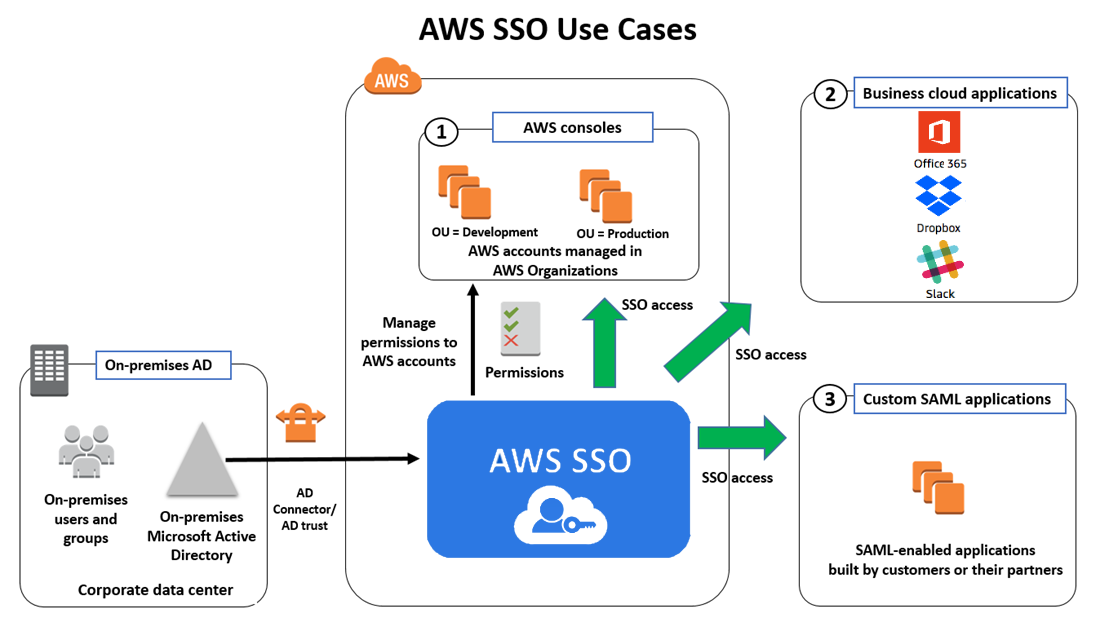
The preceding diagram shows how AWS IAM Identity Center helps connect your users to the AWS accounts and business applications to which they need access. The numbers in the diagram correspond to the following use cases.
Use case 1: Manage IAM Identity Center access to AWS accounts
With AWS IAM Identity Center, you can grant your users access to AWS accounts in your organization. You can do this by adding your users to groups in your corporate Active Directory. In AWS IAM Identity Center, specify which Active Directory groups can access which AWS accounts, and then pick a permission set to specify the level of IAM Identity Center access you are granting these Active Directory groups. AWS IAM Identity Center then sets up AWS account access for the users in the groups. Going forward, you can add new users to your Active Directory groups, and AWS IAM Identity Center automatically provides the users access to the configured accounts. You also can grant Active Directory users direct access to AWS accounts (without needing to add users to Active Directory groups).
To configure AWS account access for your users:
- Navigate to the AWS IAM Identity Center console, and choose AWS accounts from the navigation pane. Choose which accounts you want users to access from the list of accounts. For this example, I am choosing three accounts from my MarketingBU organizational unit. I then choose Assign users.

- Choose Users, start typing to search for users, and then choose Search connected directory. This search will return a list of users from your connected directory. You can also search for groups.

- To select permission sets, you first have to create one. Choose Create new permission set.

- You can use an existing job function policy to create a permission set. This type of policy allows you to apply predefined AWS managed policies to a permission set that are based on common job functions in the IT industry. Alternatively, you can create a custom permission set based on custom policies.

- For this example, I choose the SecurityAudit job function policy and then choose Create. As a result, this permission set will be available for me to pick on the next screen.

- Choose a permission set to indicate what level of access you want to grant your users. For this example, I assign the SecurityAudit permission set I created in the previous step to the users I chose. I then choose Finish.

- Your users can sign in to the user portal and access the accounts to which you gave them access. AWS IAM Identity Center automatically sets up the necessary trust between accounts to enable IAM Identity Center. AWS IAM Identity Center also sets up the necessary permissions in each account. This helps you scale your administrative tasks across multiple AWS accounts.

- The users can choose an account and a permission set to sign in to that account without needing to provide a password again. For example, if you grant a user two permission sets—one that is more restrictive and one that is less restrictive—the user can choose which permission set to use for a specific session. In the following screenshot, John has signed in to the AWS IAM Identity Center user portal. He can see all the accounts to which he has access. For example, he can sign in to the Production Account with SecurityAudit permissions.

Use case 2: Manage IAM Identity Center access to business applications
AWS IAM Identity Center has built-in support for IAM Identity Center access to commonly used business applications such as Salesforce, Office 365, and Box. You can find these applications in the AWS IAM Identity Center console and easily configure IAM Identity Center access by using the application configuration wizard. After you configure an application for IAM Identity Center access, you can grant users access by searching for users and groups in your corporate directory. For a complete list of supported applications, navigate to the AWS IAM Identity Center console.
To configure IAM Identity Center access to business applications:
- Navigate to the AWS IAM Identity Center console and choose Applications from the navigation pane.

- Choose Add a new application and choose one or more of the applications in the list. For this example, I have chosen Dropbox.

- Depending on which application you choose, you will be asked to complete step-by-step instructions to configure the application for IAM Identity Center access. The instructions guide you to use the details provided in the AWS IAM Identity Center metadata section to configure your application, and then to provide your application details in the Application metadata section. Choose Save changes when you are done.

- Optionally, you can provide additional SAML attribute mappings by choosing the Attribute mappings tab. You need to do this only if you want to pass user attributes from your corporate directory to the application.

- To give your users access to this application, choose the Assigned users tab. Choose Assign users to search your connected directory, and choose a user or group that can access this application.

Use case 3: Manage IAM Identity Center access to custom SAML-enabled applications
You also can enable IAM Identity Center access to your custom-built or partner-built SAML applications by using the AWS IAM Identity Center application configuration wizard.
To configure IAM Identity Center access to SAML-enabled applications:
- Navigate to the AWS IAM Identity Center console and choose Applications from the navigation pane.

- Choose Add a new application, choose Custom SAML 2.0 application, and choose Add.

- On the Custom SAML 2.0 application page, copy or download the AWS IAM Identity Center metadata from the AWS IAM Identity Center metadata section to configure your custom SAML-enabled application to recognize AWS IAM Identity Center as an identity provider.

- On the same page, complete the application configuration details in the Application metadata section, and choose Save changes.

- You can provide additional SAML attribute mappings to be passed to your application in the SAML assertion by choosing the Attribute mappings tab. See the documentation for list of all available attributes.

- To give your users access to this application, choose the Assigned users tab. Choose Assign users to search your connected directory, and choose a user or group that can access this application.

Summary
In this blog post, I introduced AWS IAM Identity Center and explained its key features, benefits, and use cases. With AWS IAM Identity Center, you can centrally manage and audit IAM Identity Center access to all your AWS accounts, cloud applications, and custom applications. To start using AWS IAM Identity Center, navigate to the AWS IAM Identity Center console.
If you have feedback or questions about AWS IAM Identity Center, start a new thread on the AWS IAM Identity Center forum.
– Anand
Want more AWS Security how-to content, news, and feature announcements? Follow us on Twitter.