AWS Security Blog
Tag: Identity
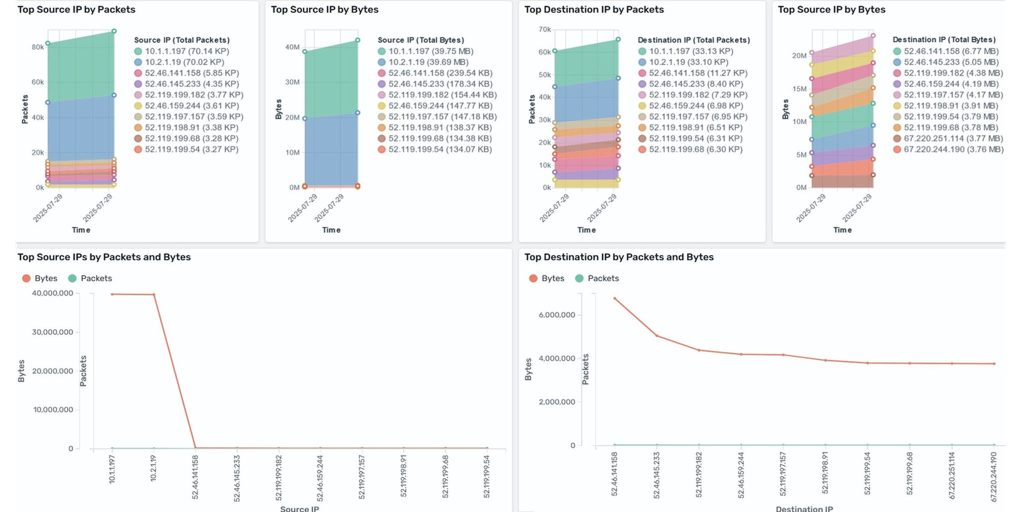
Analyze AWS Network Firewall logs using Amazon OpenSearch dashboard
Amazon CloudWatch and Amazon OpenSearch Service have launched a new dashboard that simplifies the analysis of AWS Network Firewall logs. Previously, in our blog post How to analyze AWS Network Firewall logs using Amazon OpenSearch Service we demonstrated the required services and steps to create an OpenSearch dashboard. The new dashboard removes these extra steps […]
Should I use managed login or create a custom UI in Amazon Cognito?
October 8, 2025: This blog post has been updated to include the Amazon Cognito managed login experience. The managed login experience has an updated look, additional features, and enhanced customization options. September 8, 2023: It’s important to know that if you activate user sign-up in your user pool, anyone on the internet can sign up […]
Use scalable controls to help prevent access from unexpected networks
As your organization grows, the amount of data you own and the number of data sources to store and process your data across multiple Amazon Web Services (AWS) accounts increases. Enforcing consistent access controls that restrict access to known networks might become a key part in protecting your organization’s sensitive data. Previously, AWS customers could […]
Effectively implementing resource control policies in a multi-account environment
Every organization strives to empower teams to drive innovation while safeguarding their data and systems from unintended access. For organizations that have thousands of Amazon Web Services (AWS) resources spread across multiple accounts, organization-wide permissions guardrails can help maintain secure and compliant configurations. For example, some AWS services support resource-based policies that can be used to […]
Connect your on-premises Kubernetes cluster to AWS APIs using IAM Roles Anywhere
February 26, 2025: We’ve updated this post to fix a typo in the code in Step 5 – Deploy your workload. Many customers want to seamlessly integrate their on-premises Kubernetes workloads with AWS services, implement hybrid workloads, or migrate to AWS. Previously, a common approach involved creating long-term access keys, which posed security risks and […]
Important changes to CloudTrail events for AWS IAM Identity Center
November 26, 2025: All changes to the CloudTrail events of IAM Identity Center described in this blog post are now deployed. December 30, 2024: In response to customer feedback, we updated the effective date for the announced changes from January 13, 2025, to July 14, 2025, and clarified that these changes apply exclusively to IAM […]
How to use interface VPC endpoints to meet your security objectives
October 28, 2024: We updated the text and figure for security objective 1 to show Amazon Route 53 Resolver DNS Firewall. Amazon Virtual Private Cloud (Amazon VPC) endpoints—powered by AWS PrivateLink—enable customers to establish private connectivity to supported AWS services, enterprise services, and third-party services by using private IP addresses. There are three types of […]
Establishing a data perimeter on AWS: Analyze your account activity to evaluate impact and refine controls
April 22, 2025: This post was updated to fix a typo in the Example 2 section. A data perimeter on Amazon Web Services (AWS) is a set of preventive controls you can use to help establish a boundary around your data in AWS Organizations. This boundary helps ensure that your data can be accessed only […]
How to use AWS managed applications with IAM Identity Center: Enable Amazon Q without migrating existing IAM federation flows
June 9, 2025: We added a section on how to use a service control policy to block permission sets from being used in your organization’s member accounts. AWS IAM Identity Center is the preferred way to provide workforce access to Amazon Web Services (AWS) accounts, and enables you to provide workforce access to many AWS […]
The curious case of faster AWS KMS symmetric key rotation
Today, AWS Key Management Service (AWS KMS) is introducing faster options for automatic symmetric key rotation. We’re also introducing rotate on-demand, rotation visibility improvements, and a new limit on the price of all symmetric keys that have had two or more rotations (including existing keys). In this post, I discuss all those capabilities and changes. […]