AWS Partner Network (APN) Blog
Automating Security, Governance, and Monitoring in AWS Landing Zone to Save Time, Effort, and Cost
By Jon Myer, Senior Cloud Solutions Architect at NetEnrich
By Jim Huang, Partner Solutions Architect at AWS
 |
 |
 |
Enterprises migrating to Amazon Web Services (AWS) with multiple applications and distributed teams often lack centralized governance, management, or security systems.
With AWS Landing Zone, you can configure and provision a secure, scalable, automated, multi-account AWS environment aligned with AWS best practices without existing resources. It gives you granular, centralized control over your cloud workloads, with a consistent level of security and compliance across all accounts.
Core elements of AWS Landing Zone include a multi-account approach with the following:
- Multi-account monitoring
- Security baseline with preventative and detective controls
- Identity and access management
- Centralized logging
- Automation with infrastructure as code (IaC)
- Account Vending Machine and Add-On for environment extension
This post describes the best practices underlying the AWS Landing Zone solution using an implementation by NetEnrich, an AWS Partner Network (APN) Advanced Consulting Partner. NetEnrich provides comprehensive cloud services for AWS, including migration, DevOps, monitoring, management, and optimization.
Overview
It can be intimidating to build a comprehensive, multi-account environment on AWS on your own. It can take time and in-depth knowledge of AWS services to set up the environment and configure multiple accounts and services with security and compliance controls.
AWS Landing Zone saves time, effort, and cost by automating the process, while ensuring self-service security guardrails through the creation of critical accounts and resources.
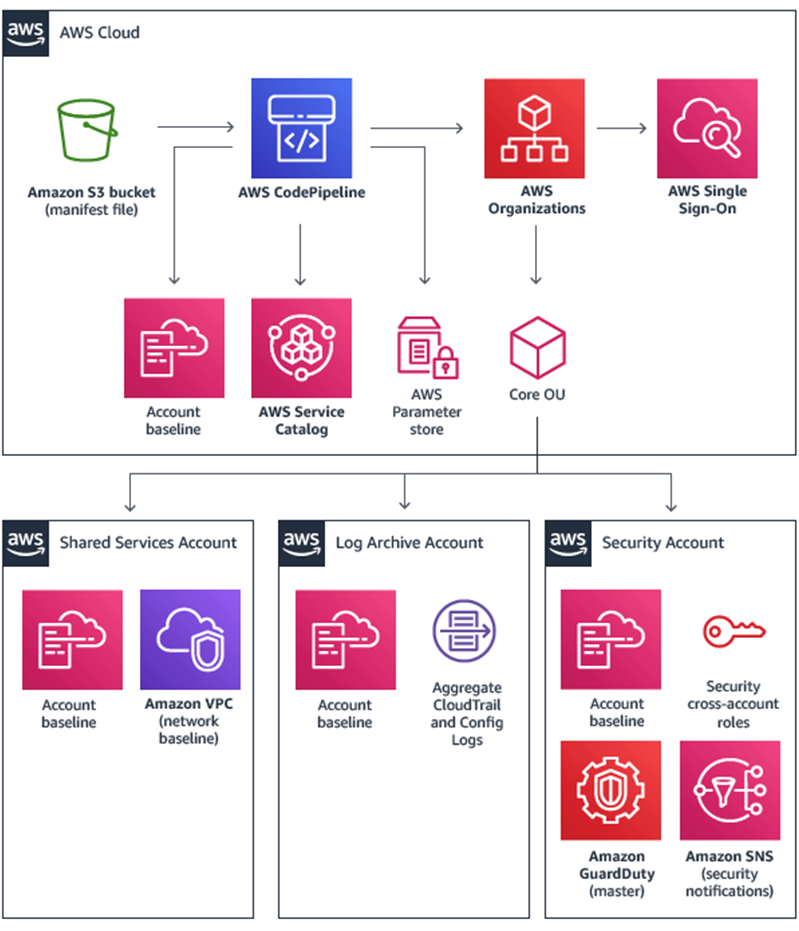
The multi-account structure includes an AWS Organizations account and Core OU, which consists of Shared Services, Log Archive, and Security accounts.
Figure 1 – Multi-account structure on AWS Landing Zone.
In addition to the multi-account structure, AWS Landing Zone provides three mechanisms for landing zone extension or modification for customer-specific environments:
- Account Vending Machine for creating new accounts.
- Add-On for adding a new service or product via AWS Service Catalog.
- Configuration templates tailored to introducing customer-specific solutions.
NetEnrich Use Case: Financial Services Customer
AWS Landing Zone is one of the core competencies of NetEnrich, which we leverage when executing any large-scale AWS migration for customers. Because data security is a significant concern during migrations, enterprises look to NetEnrich to enforce a system of checks, balances, and access controls. That system must be compliant with regulatory frameworks like HIPAA, SOC1, SOC2, and PCI-DSS.
NetEnrich was approached by a renowned American investment-management firm that wanted to gain full control of its existing AWS environment with a centralized logging system for multiple accounts and services. The company wanted global and account-level security and visibility into its users.
The customer had the following requirements for NetEnrich:
- Automated setup: Launch a new AWS account with AWS best practices blueprints and security.
- Policy enforcement: Enable pre-packaged security guardrails to enforce policies and detect violations.
- Dashboard for visibility: Get continuous visibility into how workloads comply with guardrails.
The customer’s business growth over the years led it to establish operations in multiple countries with more than 2,500 employees. This contributed to a massive environment sprawl with minimum visibility into the organization’s existing AWS environment and no centralized logging system.
Apart from the fact that its environment lacked a security baseline and governance policies, the customer had additional challenges, including lack of AWS training and no policy enforcement or automated configuration monitoring. Furthermore, its alert triggering was based off specific events without resolution automation.
This customer was perfect for the multi-account approach offered by AWS Landing Zone. NetEnrich assessed its existing environment and provisioned a new Landing Zone environment designed to secure, monitor, and scale its multi-account AWS environment based on AWS best practices.
We then migrated the customer’s existing accounts and redeployed its workloads to the new environment created by the Landing Zone.
The baseline environment and configurations included governance, data security, logging, automated account provisioning, and AWS Identity and Access Management (IAM). During the deployment, each account was configured to automatically create an identity provider with the appropriate roles and policies. The roles were integrated with the customer’s Active Directory Federation Services (AD FS) for AWS Single Sign-On (AWS SSO).
How to Implement AWS Landing Zone
Here’s a look at the steps NetEnrich took to implement AWS Landing Zone and help the customer gain full control of its existing AWS environment.
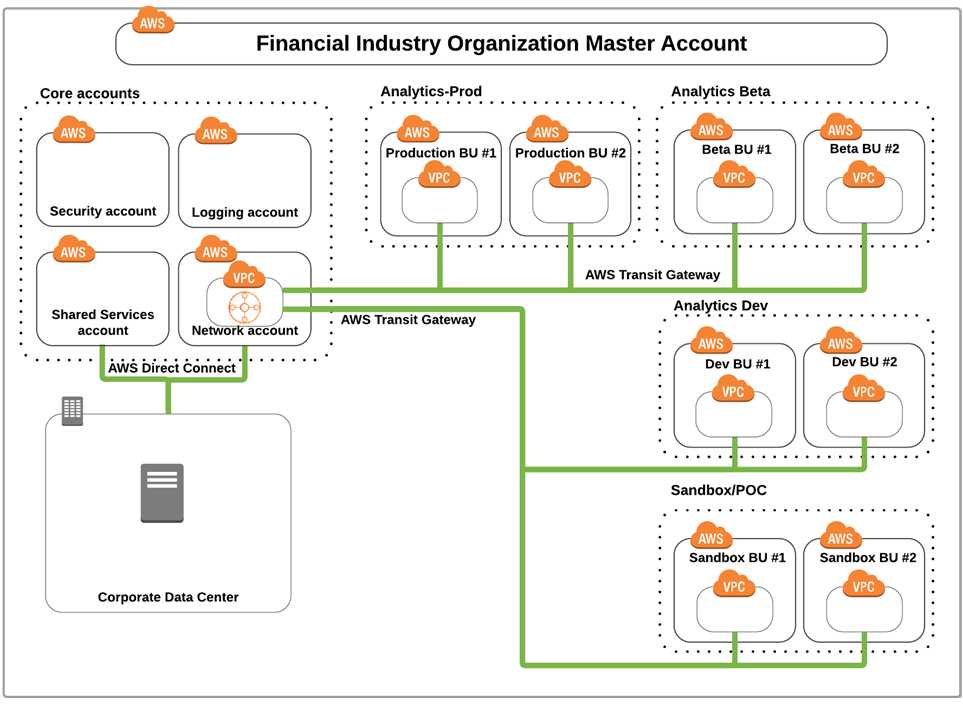
- First, we deployed the landing zone foundation implemented by AWS Landing Zone.
. - Next, we customized the secure multi-account environment with the following:
- Logging account: Centralized location for Amazon VPC Flow Logs.
- Security account: AWS Config aggregator, Amazon GuardDuty, and alerts.
- Shared Services account: Shared virtual private cloud (VPC) for remote connectivity to other accounts.
- Network account: Primary AWS Direct Connect setup with an AWS Transit Gateway setup to communicate with VPCs from other accounts.
- Business Unit accounts:
- Analytics-Prod, Analytics-Beta, and Analytics-Dev accounts to separate each business unit into its own account for ease of management.
- Sandbox/POC account for isolation testing and different security rules and policies.
Figure 2 – Multi-account environment in the customer’s landing zone.
- We enabled automatic configuration of rules and aggregated dashboards using AWS Config, which helped identify non-compliant/compliant resources through AWS Landing Zone deployment.
. - NetEnrich customizations of AWS Landing Zone included:
- Automated account alias: When a new account is created using the account vending machine (AVM), the account alias doesn’t exist. It has to be entered manually after logging into the newly-created account. Without the account alias, some of the customized implementation features aren’t possible.
.
NetEnrich integrated the account alias into the original AWS Landing Zone code. When a new account is created now, it takes the name during deployment and updates the account alias.
. - AD FS integration: Using AWS CloudFormation, NetEnrich takes the customer’s AD FS metadata and integrates it into AWS Landing Zone. When the CloudFormation template is deployed, the identify provider is created along with the updated metadata and AD FS roles.
.
The roles are later used for Active Directory security groups after the customer updated its AD FS claims relay to support a new account.
. - IAM 90-day access/secret key rotation enforcement: The customization used an AWS Lambda function that runs once a day to check the access/secret key age of all local users. If the key age reaches 76 days, an email is generated to the existing notification topic and sent out as an alert.
.
An email is sent each day until a new access/secret key is created or the old one is removed. If the age of the access/secret key reaches 91 days without rotation, it is disabled.
.
NetEnrich also built in an access/secret key whitelisting or exception group to support a service or specific account that can’t reset or change the access/secret key.
. - MFA for local accounts through automation: Using a Lambda function, this customization monitors AWS CloudTrail Events for any newly-created local user account. If a new account is created, it’s automatically added to a group that enforces multi-factor authentication (MFA) before the account can access resources. This function also runs every six hours to check if a user was removed from the MFA group. If so, the function moves the local user account back into the MFA group.
.
NetEnrich also built in an MFA whitelisting or exception group to support services or specific accounts that cannot handle MFA.
. - Amazon CloudWatch status check for all instances: NetEnrich set up a Lambda function to monitor CloudTrail for any new Amazon EC2 RunInstance API calls. Upon initiation of the function, CloudWatch status checks are added to the instance.
. - Customized service control policies for global security: NetEnrich set up three additional security policies:
- Deny Amazon Simple Storage Service (Amazon S3) public access to all accounts.
- Deny the creation of an internet gateway for accounts.
- Deny the deletion of VPC flow logs.
.
- Budgeting and billing notifications for accounts: This customization creates automated billing alerts for each account, using the Landing Zone topic for alerting and notification.
. - Additional AWS Config rules and remediation: An AWS Config custom rule handles non-compliant security group rules and support SSH/Port 22. This customization uses a Lambda function to monitor Security Groups for any rule containing a rule to allow SSH. If a security group includes an SSH rule, it’s evaluated against a whitelisting group, also known as parameters, within the AWS Config custom rule.
.
If the IP address is part of the parameters, then the function does nothing, but if it isn’t, then the Lambda function removed the rule from the security group.
. - Automated Amazon Inspector setup: Automatically enabled Amazon Inspector for each account provisioned by Landing Zone to analyze the behavior of AWS resources to help identify potential security issues.
. - AWS KMS key rotation enforcement: Implemented a Lambda function to check for any AWS Key Management Service (KMS) key and enforce annual rotation, or else the key is disabled.
.
- Automated account alias: When a new account is created using the account vending machine (AVM), the account alias doesn’t exist. It has to be entered manually after logging into the newly-created account. Without the account alias, some of the customized implementation features aren’t possible.
- Next, we resolved newly-created accounts having zero service limits. Whenever the AVM deployed a new account, all service limits for the account are set to zero as a security feature by AWS to validate the account. Originally, we needed to open a service limit ticket and request support to reset all the limits to defaults for each reason. Unfortunately, by doing so, it delayed allowing the end user to start using the environment.
.
NetEnrich incorporated an AWS CloudFormation template that deployed a VPC, subnet, and Amazon EC2 instance, and then removed them after a few minutes. In doing so, it automatically reset all service limits to defaults within that region.
. - NetEnrich integrated DevOps capabilities, such as:
- Setting up a daily scrum using the Atlassian stack (JIRA, retro, sprint).
- Integrating the customer’s internal GitLab to push changes continuously into Dev and promote them to production.
- Setting up Slack alerts and notifications for the pipeline process.
Recap of AWS Landing Zone Modifications
NetEnrich made the customer landing zone extensions, adding customized templates to the AWS Landing Zone deployment. Specifically, NetEnrich tailored its setup by adding the following customized baseline template files:
- aws-landing-zone-autotagging.template—Automatically tags instances (owner, account alias).
- aws-landing-zone-budget.template—Standard budget alerting for all accounts.
- aws-landing-zone-cweventrules.template—Automatically adds CloudWatch alarms to Amazon EC2 instances.
- aws-landing-zone-default-adfs-roles.template—Creates AD FS roles for integration.
- aws-landing-zone-ebs-datalifecycle-manager.template—Automatically creates a data-lifecycle management policy based on the account alias environment type for all Amazon EBS volumes.
- aws-landing-zone-iam-accesskeyroation.template—Enforces IAM user access/secret key rotation.
- aws-landing-zone-iam-enforcemfa.template—Enforces MFA for IAM users.
- aws-landing-zone-iam-user-check.template—Checks if a new user was created and sends a notification
- aws-landing-zone-kmscheck.template—Automatically enforces the annual KMS rotation.
- aws-landing-zone-vpc-flowlogs.template—Automatically creates a VPC flow log for newly created VPCs.
In addition to the baseline templates, AWS Landing Zone has a specific section in the configuration manifest file for service control policies (SCP). The customized policies incorporated into the configuration allow the customer to apply the additional policies across the accounts in an organizational unit.
To provide the customer with the customizations listed, NetEnrich made the changes using the following process:
- Download the AWS Landing Zone configuration .zip file from the Amazon S3 bucket and extract the contents.
- Use a text editor to open the entire folder.
- Browse to: aws-landing-zone-configuration/parameters/aws_baseline.
- Open: aws-landing-zone-iam-password-policy.json.
- Locate the following ParameterKey value: MinimumPasswordLength.
- Update the ParameterValue from 12 to 14.
- Save aws-landing-zone-iam-password-policy.json.
- Rezip all of the sub folders below the root of aws-landing-zone-configuration.
- Because AWS CodePipeline looks for the modification or update of the .zip file, rename it to aws-landing-zone-configuration.zip.
- To overwrite the previous file, upload the newly created .zip file into the Amazon S3 bucket.
- Browse to CodePipeline and open AWS-Landing-Zone-CodePipeline to see the progress from one stage to the next.
- After CodePipeline completes the last stage “LaunchAVM,” all changes will be made to each account and a newly-created AVM version is available within AWS Service Catalog.
After performing these tasks, you may want to clean up what you’ve created to avoid incurring any unnecessary charges.
Conclusion
In this post, we showed how NetEnrich customized a secure, multi-account environment initially deployed by the AWS Landing Zone solution for a customer. We added additional customizations, enforced security at the global and account levels, and integrated DevOps capabilities.
While a primary AWS Landing Zone environment includes a multi-account approach with integrated security and governance, the environment can be scaled as needed. Other benefits of AWS Landing Zone include improved efficiency, flexibility, effective resource management, and monitoring while adhering to security and regulatory standards.
.
 |
NetEnrich – APN Partner Spotlight
NetEnrich is an APN Advanced Consulting Partner. They help enterprise and mid-market customers modernize IT infrastructure and achieve cloud adoption goals on an outcome-based model that reduces costs.
Contact NetEnrich | Practice Overview
*Already worked with NetEnrich? Rate this Partner
*To review an APN Partner, you must be an AWS customer that has worked with them directly on a project.