AWS Partner Network (APN) Blog
Preventing Security Fires with Amazon GuardDuty and Alert Logic Cloud Insight Essentials
By Rich Vorwaller, Sr. Product Manager at Alert Logic
By Sameer Kumar Vasanthapuram, Partner Solutions Architect at AWS
 You have probably heard the proverb that an “ounce of prevention is worth a pound of cure.” It’s a quote from Ben Franklin discussing fire prevention for his home town of Philadelphia. Before the 20th century, fires were a major hazard to urban areas.
You have probably heard the proverb that an “ounce of prevention is worth a pound of cure.” It’s a quote from Ben Franklin discussing fire prevention for his home town of Philadelphia. Before the 20th century, fires were a major hazard to urban areas.
Today, fires cause nowhere near the scale of destruction they used to. Why is that? Because we have come a long way in not only early detection, but also in containing and preventing fires. For example, the smoke detector alone won’t completely save us, but smoke detectors in combination with fire inspections, drills, and emergency response teams gives us a better chance to survive and incur less damage.
What does this have to do with cyber security? Like fires in the 18th century, security breaches are a huge problem today. It’s all too common to read reports about breaches and how this puts customer data at risk.
At Alert Logic, an AWS Partner Network (APN) Advanced Technology Partner with AWS Competencies in both Security and Marketing & Commerce, we provide vulnerability scanning and assessment solutions to help customers become more secure and not end up on tomorrow’s news.
That’s why we jump at the chance to see how we can use any product from Amazon Web Services (AWS) to enhance our solutions for customers. This line of thinking brought us to our latest vulnerability scanning and assessment release with Amazon GuardDuty.
What is Amazon GuardDuty?
Launched at AWS re:Invent 2017, Amazon GuardDuty is a managed threat detection service that continuously monitors for malicious or unauthorized behavior in your AWS accounts and workloads. GuardDuty does this by analyzing VPC Flow Logs, DNS logs, and AWS CloudTrail event logs. It combines this information with rule-sets, threat intelligence feeds, and machine learning to detect suspicious behavior.
With GuardDuty, we saw an immediate opportunity to enhance the service with our vulnerability scanning and assessment solution that helps customers find and fix potential security attacks faster. Like the smoke detector, GuardDuty provides detection when something suspicious is happening, but we saw potential in educating customers and providing more context to help them prevent future findings.
This is why we released an integration with GuardDuty for Cloud Insight Essentials.
What is Cloud Insight Essentials?
Cloud Insight Essentials, an Alert Logic solution available in AWS Marketplace, is a vulnerability assessment solution that allows customers to continuously find risky configurations that go against AWS Security Best Practices.
The solution does this by analyzing AWS APIs and scanning CloudTrail events looking for unsafe configurations like Amazon Simple Storage Service (Amazon S3) buckets with global access, users not using Multi-Factor Authentication (MFA), or use of the root account.
Reducing Short- and Long-Term Security Threats
In addition to identifying misconfigurations, Cloud Insight Essentials provides easy to understand security context for the complete list of GuardDuty findings so customers can take short- and long-term actions to reduce potential security threats.
Let’s review a GuardDuty finding like a Secure Shell (SSH) brute force attack. Looking at the finding in Figure 1, you may not know how to respond or what exactly caused the Amazon Elastic Compute Cloud (Amazon EC2) instance to be exposed to the attack.
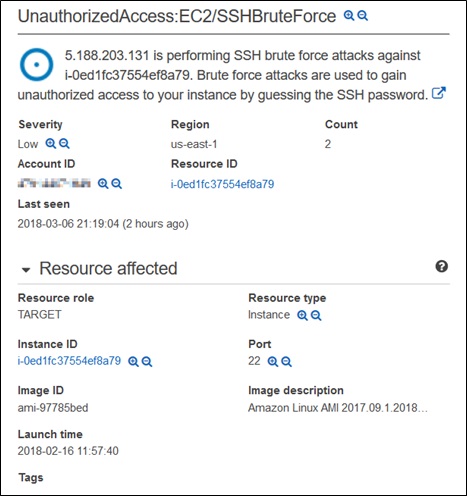
Figure 1 – Amazon GuardDuty finding in Cloud Insight Essentials.
Now look at the same GuardDuty finding in Figure 2 but with additional context provided by Cloud Insight Essentials.
Cloud Insight Essentials provides an Investigation Report that shows the topology of the attack with details like the connected Security Group, Amazon Machine Image (AMI), subnet, VPC, and region with context on what may have caused the attack.
Amazon GuardDuty has detected a SSH brute force attempt against i-0ed1fc37554ef8a79. Brute force attempts against this protocol are common if the port is open to the internet. Automated attacks are scanning new hosts constantly and an unrestricted port 22 will be targeted heavily.
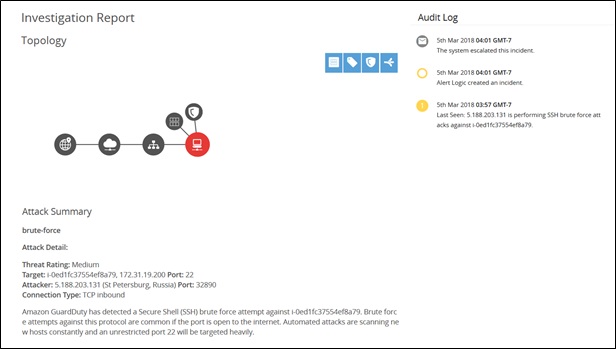
Figure 2 – Investigation report shows the topology of the attack.
In Figure 3, you can see that Cloud Insight Essentials shows you Short-Term and Structural Actions you can take with links to the AWS Management Console so you can make changes that ensure the finding doesn’t occur again.

Figure 3 – Recommendations for Short-Term and Structural actions you can take.
Lastly, Figure 4 shows you how Cloud Insight Essentials also deploys vulnerability scanners that identify Common Vulnerabilities and Exposures (CVEs) in your software. You can use this information to quickly identify Amazon EC2 instances that have a high number of GuardDuty findings and known CVEs—a combination that presents a high security risk for your AWS environment.

Figure 4 – Amazon EC2 instances with GuardDuty findings and CVEs.
How Cloud Insight Essentials Integrates with GuardDuty
Cloud Insight Essentials integrates with GuardDuty by allowing customers to forward all findings via an AWS Lambda function called CloudWatch Events Collector. You can deploy the Lambda function using an AWS CloudFormation template so you can get up and going in a few minutes. Let’s show you briefly how the integration works.
As outlined in Figure 5, GuardDuty identifies suspicious behavior and sends notifications based on CloudWatch Events. The CloudWatch Event Rule then matches those GuardDuty events and puts the events into an Amazon Kinesis Data Stream. Next, the Kinesis Data Stream triggers a Lambda function that securely forwards the data to the Cloud Insight API endpoint.
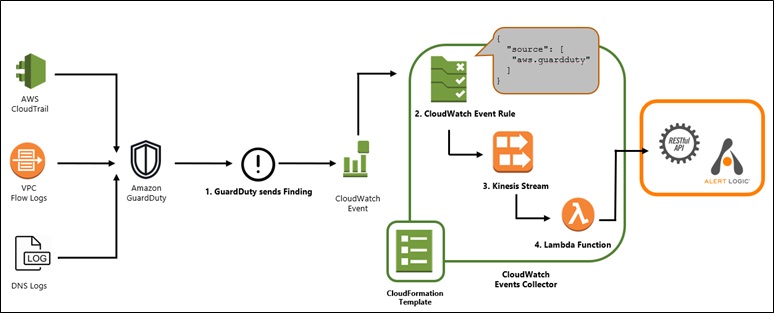
Figure 5 – GuardDuty integration overview.
As shown in Figure 6, while this is Alert Logic code, the Lambda function is running in your account and you have full access to review what the function is doing at any time.

Figure 6 – You have full access to review the AWS Lambda function.
Deploying the AWS CloudWatch Events Collector
To integrate Cloud Insight Essentials with GuardDuty, follow these steps:
- Enable GuardDuty by following the steps outlined in Setting Up Amazon GuardDuty
- Subscribe to Cloud Insight Essentials in AWS Marketplace
- As part of your subscription, you will receive an email with instructions on how to create an Alert Logic Account
- After you’ve created an Alert Logic account, set up and manage deployments.
- Deploy the CloudWatch Events Collector using the steps outlined in the Alert Logic GitHub repository
Customer Examples
Some of our customers are using Cloud Insight Essentials to consolidate findings across all AWS regions. Others are using our integration with Jira to automatically cut tickets to different service teams to resolve configuration issues related to GuardDuty findings. And some customers are using Cloud Insight Essentials with our Threat Manager with ActiveWatch service where Alert Logic cyber security experts monitor their AWS environment 24x7x365.
Next Steps
You can get started with Cloud Insight Essentials with a 30-day free trial. Then, you pay only $49 per account per month. There are no contracts or long-term commitments and you can cancel at any time.
You can also upgrade from Cloud Insight Essentials to Cloud Insight to add vulnerability scanning checks for 91,000+ Common Vulnerabilities and Exposures (CVEs) and 8,600+ software configuration issues.
Here are a couple of links to help answer any questions you may have:
- Cloud Insight Essentials FAQs with Amazon GuardDuty
- Effectively Respond to Amazon GuardDuty Findings using Cloud Insight Essentials
- GitHub Repository for Cloud Insight Essentials
Contact Alert Logic
If you would like to see how Alert Logic can help transform your business, please contact Alert Logic >>