The Internet of Things on AWS – Official Blog
How to implement zero trust IoT solutions with AWS IoT
Introduction
Zero trust is often misunderstood. It’s not a product but a security model and associated set of architectural principles and patterns. One of the main challenges customers face is determining how zero-trust principles can be applied to Internet of Things (IoT) and how to get started with incorporating zero trust with Amazon Web Services (AWS) IoT.
In this blog post, we discuss zero trust according to the NIST 800-207 architecture as a benchmark and how AWS IoT services, which support zero trust by default, can be used to create a zero-trust IoT implementation.
What is zero-trust security?
Zero trust is a conceptual model and an associated set of mechanisms that provide security controls. These security controls do not depend solely on traditional network controls or network boundaries. It requires your users, devices, and systems to prove their trustworthiness, and it enforces fine-grained, identity-based rules that govern access to applications, data, and other assets.
Zero-trust principles are intended for an organization’s infrastructure, which includes operational technology (OT), IT systems, IoT, and Industrial Internet of Things (IIoT)—it’s about trying to secure everything everywhere. Traditional security models rely heavily on network segmentation and give high levels of trust to devices based on their network presence. In comparison, zero trust is an integrated approach for verifying your connected devices, regardless of network location. It asserts least privilege and relies on intelligence, advanced detection, and real-time threat response.
With the increasing proliferation of IoT and IIoT devices, organizations are faced with protecting an expanding attack surface. Zero trust offers enhanced security than traditional network-based security because of its inherent principles, and it’s an area of increasing government and enterprise scrutiny.
A zero-trust model can improve an organization’s security posture by reducing its sole reliance on perimeter-based protection. But this doesn’t mean getting rid of perimeter security altogether. Where possible, combine identity and network capabilities to protect core assets, and apply zero-trust principles, working backward from specific use cases, with a focus on extracting business value.
Solution overview
AWS provides IoT services that you can use alongside other AWS identity and networking services to provide zero-trust building blocks as standard features for enterprise IoT and IIoT implementations.
Aligning AWS IoT with NIST 800-207 zero-trust principles
AWS IoT can help you adopt a NIST 800-207–based, zero-trust architecture (ZTA) by following the seven tenets described here:
1. All data sources and computing services are resources.
At AWS, we model your data sources and computing services as resources, which is intrinsic to access management. For example, AWS IoT Core and AWS IoT Greengrass are services which contain customer resources, as are services, such as Amazon Simple Storage Service (Amazon S3) and Amazon DynamoDB, which IoT devices are designed to securely call. Each connected device must have a credential to interact with AWS IoT services. All traffic to and from AWS IoT services are sent using Transport Layer Security (TLS). AWS Cloud security mechanisms protect data as it moves between AWS IoT services and other AWS services.
2. All communication is secured, regardless of network location.
With AWS IoT services, all communications are secured by default. This means that all communications among devices and cloud services are secured independently of network location by individually authenticating and authorizing AWS API calls using TLS. When a device connects to other devices or cloud services, it must establish trust by authenticating using principals such as X.509 certificates, security tokens, and custom authorizers. The AWS IoT security model supports certificate-based authentication or custom authorizers for legacy devices, authorization using IoT policies, and encryption using TLS 1.2. Along with strong identity provided by AWS IoT services, zero trust requires least-privilege access to control a device’s operations after it connects to AWS IoT Core. This lets AWS IoT policies limit the impact in case of unauthorized access.
AWS provides device software to allow IoT and IIoT devices to connect securely to other devices and AWS services in the cloud. AWS IoT Greengrass is an IoT open-source edge runtime and cloud service that helps build, deploy, and manage device software. AWS IoT Greengrass authenticates and encrypts device data for both local and cloud communications. Another example is FreeRTOS, an open-source, real-time operating system for microcontrollers that makes small, low-power edge devices easier to manage. FreeRTOS provides support for TLS 1.2 for secure communications and PKCS #11 for use with cryptographic elements that secure stored credentials. AWS IoT Device Client helps to connect your IoT devices securely to AWS IoT services.
3. Access to individual enterprise resources is granted on a per-session basis, and trust is evaluated using least privileges before access is granted.
AWS IoT services and AWS API calls grant access to resources on a per-session basis. IoT devices must authenticate with AWS IoT Core and be authorized before it can perform an action. Each time a device connects to AWS IoT Core, it presents its device certificate or custom authorizer to authenticate with AWS IoT Core. During this process, IoT policies are enforced to check if the device is authorized to access the resources it’s requesting, and this authorization is valid only for the current session. The next time the device connects, it goes through the same steps. A similar process applies if a device tries to connect to other AWS services using AWS IoT Core credential provider.
4. Access to resources is determined by a dynamic policy that includes the observable state of client identity, application and service, and requesting asset, all of which may include other behavioral and environmental attributes.
A core principle behind zero trust is that no IoT device should be granted access to other devices and applications until assessed for risk and approved within the set parameters of acceptable behavior. This principle applies perfectly to IoT devices because they have limited, stable, and predictable behaviors by nature, and it’s possible to use their behavior as a measure of device health.
Once identified, every IoT device should be verified against baseline behaviors before being granted access to other devices and applications in the network. A device’s state can be detected using the AWS IoT Device Shadow service, and device anomalies can be detected using AWS IoT Device Defender.
AWS IoT Core policies are applied to a collection of devices (also known as a thing group), in AWS IoT and are evaluated at runtime before access is granted. Membership in a group is dynamic and can be configured to change based on a device’s behavior using AWS IoT Device Defender. AWS IoT Device Defender uses Rules Detect and ML Detect features to determine a device’s normal behaviors and any potential deviation from the baseline. When an anomaly is detected, the device can be quarantined with limited permissions based on the static group’s policy, or it can be disallowed from connecting to AWS IoT Core.
5. No asset is inherently trusted. The enterprise monitors and measures the integrity and security posture of all owned and associated assets. The enterprise evaluates the security posture of the asset when evaluating a resource request. An enterprise implementing a ZTA should establish a nearly continuous diagnostics and mitigation (CDM) system to monitor, patch, and fix the state of devices and applications.
AWS IoT Device Defender continuously audits and monitors your fleet of IoT devices. You can also use other AWS services for nearly continuous auditing and monitoring of non-IoT components and services, which can be used to evaluate the compliance and security posture of resource assets. For example, AWS IoT Device Defender can take mitigation actions, such as the following:
- Placing a device in static thing groups with limited permissions.
- Revoking permissions.
- Quarantining a device.
- Applying patches using the AWS IoT Jobs feature for over-the-air updates to keep devices healthy and in compliance.
- Remotely connecting to a device for service or troubleshooting using the AWS IoT secure tunneling feature.
6. All resource authentications and authorizations are dynamic and strictly enforced before access is allowed. This involves a nearly continuous cycle of obtaining access, scanning and assessing threats, adapting to threats, and reevaluating the trust of ongoing communications.
By default, zero trust denies access—including any API calls—among IoT devices. With AWS IoT, access is granted with proper authentication and authorization, which takes into account the health of your devices. Zero trust requires the ability to detect and respond to threats across IoT, IIoT, IT, and cloud networks. This can be achieved using AWS IoT Device Defender and other AWS services.
7. The enterprise collects as much information as possible about the current state of assets, network infrastructure, and communications, which it uses to improve its security posture.
Using AWS IoT Device Defender, you can use IoT device data to make nearly continuous improvements to the security posture. For example, you can turn on AWS IoT Device Defender Audit features to get a security baseline for IoT devices. You can then add the Rules Detect or ML Detect features to detect anomalies found in connected devices and make improvements based on detected results.
In addition, with AWS IoT Device Defender custom metrics, you can define and monitor metrics that are unique to their device fleet or use case. You can also derive insights from other data collected on AWS (for example, auditing, logging, telemetry, and analytics) and use AWS IoT features such as AWS IoT Jobs to apply patches to improve security posture and AWS IoT Secure Tunneling to connect securely to devices for troubleshooting and remote service. Continuous improvements to an enterprise’s security posture can be achieved by fine-tuning permissions.
AWS IoT Zero Trust workshop
To get started, see the AWS IoT Zero Trust workshop, which can help you get experience using multiple AWS IoT services to safely and securely deploy commercial and industrial IoT devices. Working through a scenario where you deploy devices outside of your corporate perimeter, you use AWS IoT Core, AWS IoT Device Defender, AWS IoT Device Management, and Amazon Simple Notification Service (Amazon SNS) to build a resilient architecture that includes unique identity, least privilege, dynamic access control, health monitoring, and behavioral analytics to ensure the security of your devices and data.
If a security anomaly is detected, you can investigate and take mitigation actions, such as quarantining an anomalous device, securing connectivity to the device for remote troubleshooting, and apply a security patch to fix device vulnerabilities and keep devices healthy.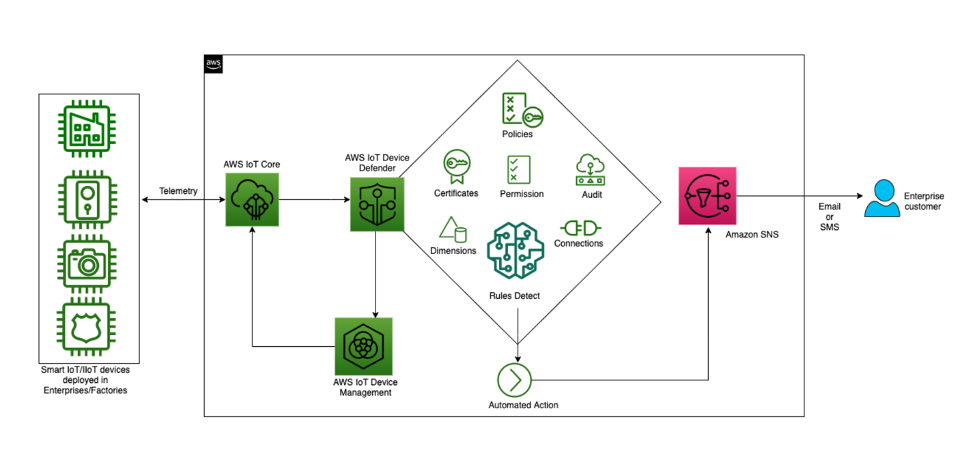
Figure 1. Implementing zero trust using the AWS IoT workshop architecture
Conclusion
Zero trust requires a phased approach, and because every organization differs, the journey is unique and based on the maturity and cybersecurity threats you face. But the core of zero-trust principles outlined here still apply.
For IoT and IIoT, AWS recommends a multilayered security approach to secure IoT solutions, including the need to use strong identities, least privileged access, continuously monitor device health and anomalies, securely connect to devices to fix issues and apply continual updates to keep devices up to date and healthy.
When transitioning to a zero-trust architecture, it’s unnecessary to replace existing networks and eliminate traditional security approaches. Instead, you can incrementally move to zero trust using an iterative approach, starting with the most critical assets first, to protect one asset at a time until the entire environment is protected. Before decommissioning your current security controls and adopting zero-trust components, ensure that you completely test your environment.
AWS recommends using a zero-trust approach for modern IoT and IIoT devices and combining identity and network capabilities, such as micro-network segmentation, AWS Direct Connect and virtual private cloud (VPC) endpoints to connect legacy OT systems. In addition, AWS offers AWS Outposts for certain workloads that are better suited for on-premises management and AWS Snowball Edge for applications that must process IIoT data at the edges. This enables the industrial edge to guard local interfaces with less-capable OT systems by combining them with cloud services and strong identity patterns.
Always work backward from specific use cases, and apply zero trust to your systems and data in accordance with their value. For more information about this value-driven approach, see Zero Trust on AWS.
About the authors
 Ryan Dsouza is a global solutions architect for IIoT at AWS. Based in New York City, Ryan helps customers design, develop, and operate more secure, scalable, and innovative solutions using the breadth and depth of AWS capabilities to deliver measurable business outcomes. Ryan has over 25 years of experience in digital platforms, smart manufacturing, energy management, building and industrial automation, and IIoT security across a diverse range of industries. Before AWS, Ryan worked for Accenture, SIEMENS, General Electric, IBM, and AECOM, serving customers for their digital transformation initiatives. Ryan Dsouza is a global solutions architect for IIoT at AWS. Based in New York City, Ryan helps customers design, develop, and operate more secure, scalable, and innovative solutions using the breadth and depth of AWS capabilities to deliver measurable business outcomes. Ryan has over 25 years of experience in digital platforms, smart manufacturing, energy management, building and industrial automation, and IIoT security across a diverse range of industries. Before AWS, Ryan worked for Accenture, SIEMENS, General Electric, IBM, and AECOM, serving customers for their digital transformation initiatives. |
 Syed Rehan is a global IoT specialist solutions architect at AWS in London. He covers a global span of customers and supports them as lead IoT solutions architect. Syed has in-depth knowledge of IoT and cloud environments, and he works in this role with global customers ranging from start-up to enterprises to enable them to build AWS IoT solutions. Syed Rehan is a global IoT specialist solutions architect at AWS in London. He covers a global span of customers and supports them as lead IoT solutions architect. Syed has in-depth knowledge of IoT and cloud environments, and he works in this role with global customers ranging from start-up to enterprises to enable them to build AWS IoT solutions. |
 Eknath Venkataramani is a security engineer on the AWS IoT team. He currently focuses on helping to secure multiple AWS IoT service releases by identifying and designing new IoT features that make security easier for IoT customers. Eknath Venkataramani is a security engineer on the AWS IoT team. He currently focuses on helping to secure multiple AWS IoT service releases by identifying and designing new IoT features that make security easier for IoT customers. |