The Internet of Things on AWS – Official Blog
Tag: AWS IoT best practices
Optimize long-term video storage costs with Amazon Kinesis Video Streams warm storage tier
Introduction Amazon Kinesis Video Streams provides powerful solutions for cloud-based video management in physical security and surveillance organizations. While organizations need continuous recording capabilities, traditional storage approaches often lead to increased costs. Kinesis Video Streams excels at real-time video management and short-term storage, serving enterprise deployments with extensive camera networks. Now, the innovative Kinesis Video […]
When data is all you need: An overview of IoT communication with the cloud
Technical and marketing teams working on internet of things (IoT) programs, sooner or later, manage a project that requires data flow between a fleet of devices and the cloud. This data is critical because marketing wants to provide more features to the users, business teams require data driven decisions, and technical teams work to optimize […]
Amazon Kinesis Video Streams Privacy and E2E Security Overview
Introduction In a world increasingly driven by Internet of Things (IoT) devices and real-time video streaming, privacy and security has become more critical than ever. Whether used in smart homes, industrial automation, or healthcare, Amazon Kinesis Video Streams offers a fully managed, scalable, and secure platform for streaming live video from devices to the AWS […]
Delivering an integrated approach to safety: How AWS workforce safety solutions make work safer
With over 395 million workers worldwide sustaining non-fatal injuries yearly, companies are increasingly recognizing the need to adopt integrated, proactive safety measures. They seek to provide safer work environments overall, reduce risk of accidents and injuries across the site, and improve employee well-being. Traditional siloed approaches have led to key insights being missed due to […]
Sharing a vision for a more connected world with AWS IoT
AWS IoT VP, Yasser Alsaied, talks IoT strategy, commitment, and outlook Introduction The future of the Internet of Things (IoT) has been a topic of ongoing discussion and speculation. With implications for IoT hyperscalers, vendors, and customers alike, the landscape is rapidly evolving. To shed light on this topic, I spoke with Yasser Alsaied, vice […]
Identify misconfigured IoT policies using AWS IoT Device Defender
Introduction We are excited to announce a new AWS IoT Device Defender audit feature to identify potential misconfigurations when using wild cards in Internet of Things (IoT) policies. AWS IoT Device Defender is a fully managed IoT security service that enables you to audit and monitor your IoT device fleet and secure your IoT configurations […]
Use AWS IoT Core MQTT broker with standard MQTT libraries
Introduction AWS IoT Core connects Internet of Things (IoT) devices to AWS IoT and other AWS services. Devices and clients can use the MQTT protocol to publish and subscribe to messages. MQTT libraries, such as the AWS IoT Device SDKs, include open-source libraries, developer guides with samples, and porting guides so that you can build innovative IoT […]
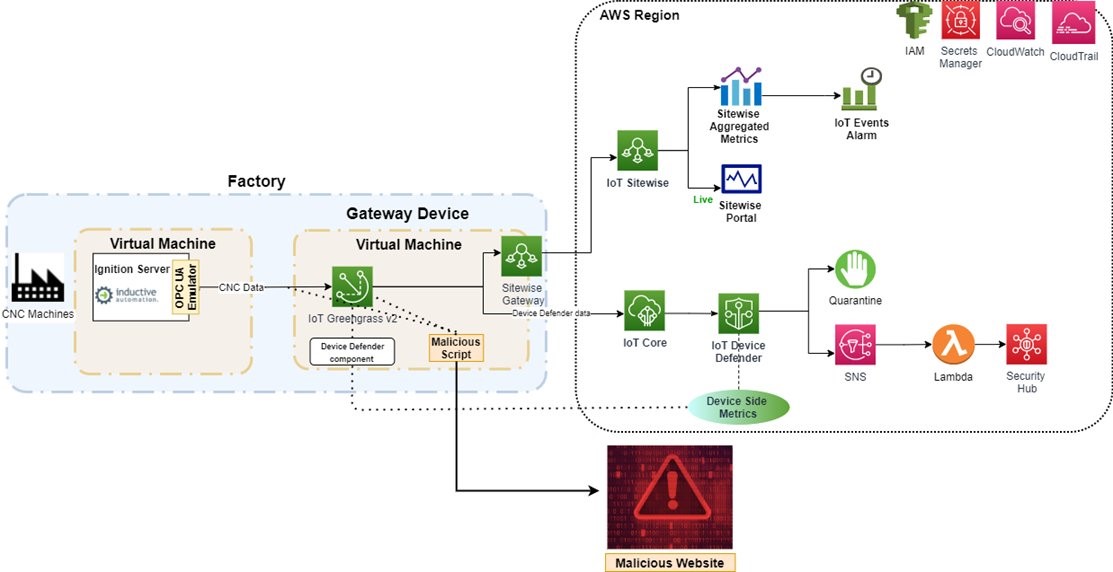
Detect Cryptocurrency Mining Threats on Edge Devices using AWS IoT
Introduction Machine learning (ML) at the edge requires powerful edge requires powerful edge devices with a unique set of requirements. The availability, safety, and security requirements for the edge differ from cloud since they are located at the customer site, outside the data center, and interface directly with operational technology (OT) and the internet. Since […]
Learn how to secure your IIoT solutions with AWS IIoT security workshop
Introduction Industrial digital transformation is driving changes to the Operational Technology (OT) landscape, making it more connected to the internet and IT systems and solutions. With OT/IT convergence, OT environments are leveraging more IT solutions to improve productivity and efficiency of production operations. Industrial customers can use AWS edge and cloud services to securely access […]
Automate global device provisioning with AWS IoT Core and Amazon Route 53
Introduction Use AWS IoT Core together with Amazon Route 53 to choose an AWS Region based on geo location or latency and register your devices automatically when they connect for the first time to AWS IoT Core. Time to read 10 minutes Learning level 300 Services used AWS IoT Core,Amazon Route53, Amazon Certificate Manager Private […]