AWS News Blog
New – AWS Control Tower Account Factory for Terraform
|
|
December 7, 2023: Post updated to clarify AWS Regions availability.
AWS Control Tower makes it easier to set up and manage a secure, multi-account AWS environment. AWS Control Tower uses AWS Organizations to create what is called a landing zone, bringing ongoing account management and governance based on our experience working with thousands of customers.
If you use AWS CloudFormation to manage your infrastructure as code, you can customize your AWS Control Tower landing zone using Customizations for AWS Control Tower, a solution that helps you deploy custom templates and policies to individual accounts and organizational units (OUs) within your organization.
But what if you use Terraform to manage your AWS infrastructure?
Today, I am happy to share the availability of AWS Control Tower Account Factory for Terraform (AFT), a new Terraform module maintained by the AWS Control Tower team that allows you to provision and customize AWS accounts through Terraform using a deployment pipeline. The source code for the development pipeline can be stored in AWS CodeCommit, GitHub, GitHub Enterprise, or BitBucket. With AFT, you can automate the creation of fully functional accounts that have access to all the resources they need to be productive. The module works with Terraform open source, Terraform Enterprise, and Terraform Cloud.
Let’s see how this works in practice.
Using AWS Control Tower Account Factory for Terraform
To set up AFT in my account, I follow the instructions in the documentation. To follow along, please refer to Deploy AWS Control Tower Account Factory for Terraform (AFT) and the Post-deployment steps in the documentation because there can be different requirements depending on your configuration.
First, I create a main.tf file that uses the AWS Control Tower Account Factory for Terraform (AFT) module:
The first six parameters are required. As a prerequisite, I need to pass the ID of four AWS accounts in my AWS organization:
ct_management_account_id– AWS Control Tower management accountlog_archive_account_id– Log Archive accountaudit_account_id– Audit accountaft_management_account_id– AFT management account
Then, I have to pass two AWS Regions:
ct_home_region– The Region from which this module will be executed. This must be the same Region where AWS Control Tower is deployed.tf_backend_secondary_region– The backend primary Region is the same as the AFT Region. This parameter defines the secondary Region to replicate to. AFT creates a backend for state tracking for its own state. It is also used for Terraform when using the open-source version.
The other parameters are optional and are set to their default value in the previous main.tf file:
terraform_distribution– To select between Terraform open source (default), Enterprise, or Cloudvcs_provider– To choose the version control system to use between AWS CodeCommit (default), GitHub, GitHub Enterprise, or BitBucket.
These feature flags are disabled by default and can be omitted unless you want to enable them:
aft_feature_delete_default_vpcs_enabled– To automatically delete the default VPC for the AFT management account.aft_feature_cloudtrail_data_events– To enable AWS CloudTrail data events for new accounts. Be aware that this option, usually required for compliance in highly regulated environments, can have an impact on your costs.aft_feature_enterprise_support– To automatically enroll new accounts with Enterprise Support (if you have an Enterprise Support Plan).
First, I initialize the project and download the plugins:
Then, I use AWS Single Sign-On to log in with the AWS Control Tower management account and start the deployment:
I confirm with a yes and, after some time, the deployment is complete.
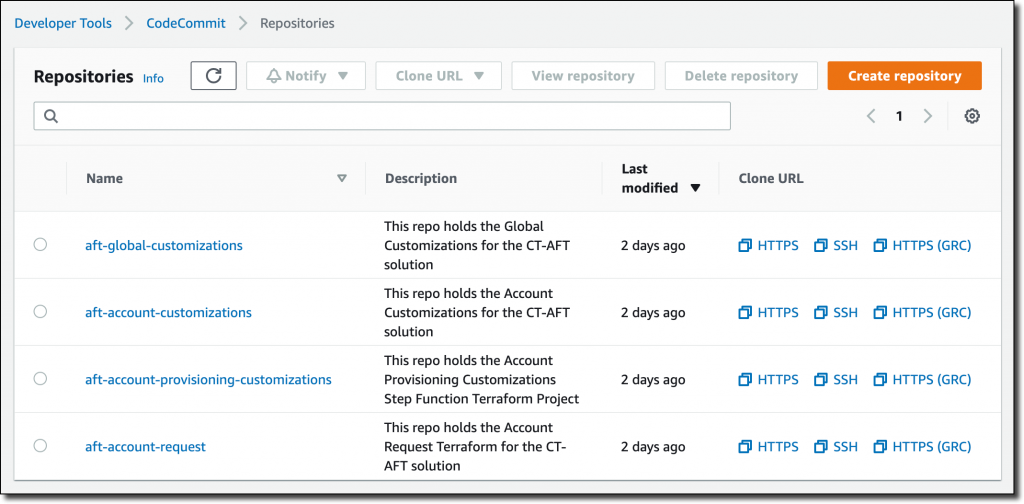
Now, I use AWS SSO again to log in with the AFT management account. In the AWS CodeCommit console, I find four repositories that I can use to customize the accounts created with AFT.
These repositories are used by pipelines managed by AWS CodePipeline to automate the account creation:
aft-account-request– This is where I place requests for accounts provisioned and managed by AFT.aft-global-customizations– I can use this repository to customize all provisioned accounts with customer-defined resources. The resources can be created through Terraform or through Python.aft-account-customizations– Here, I can customize provisioned accounts depending on the value of theaccount_customizations_nameparameter in theaft-account-requestrepository. In this way, I can create different sets of customizations depending on the role the account will be used for.aft-account-provisioning-customizations– This repository uses AWS Step Functions to customize the provisioning process for new accounts and simplify the integration with additional environments. State machines can use AWS Lambda functions, Amazon Elastic Container Service (Amazon ECS) or AWS Fargate tasks, custom activities hosted either on AWS or on-premises, or Amazon Simple Notification Service (Amazon SNS) and Amazon Simple Queue Service (Amazon SQS) to communicate with external applications.
Currently, these four repositories are all empty. To start, I use the code in the sources/aft-customizations-repos folder in the GitHub repo of the AFT Terraform module.
Using the example in the aft-account-request repository, I prepare a template to create a couple of AWS accounts. One of the two accounts is for a software developer.
To help software developers be productive quickly, I create a specific account customization. In the template, I set the parameter account_customizations_name equal to developer-customization.
Then, in the aft-account-customizations repository, I create a developer-customization folder where I put a Terraform template to automatically create an AWS Cloud9 EC2-based development environment for new accounts of that type. Optionally, I can extend that with my Python code, for example, to invoke internal or external APIs. Using this approach, all new accounts for software developers will have their development environment ready as they go through the delivery pipeline.
I push the changes to the main branch (first for the aft-account-customizations repository, then for the aft-account-request). This triggers the execution of the pipeline. After a few minutes, the two new accounts are ready to be used.
You can customize accounts created by AFT based on your unique requirements. For example, you can provide each account with its own specific security setup (such as IAM roles or security groups) and storage (for example, pre-configured Amazon Simple Storage Service (Amazon S3) buckets).
Availability and Pricing
AWS Control Tower Account Factory for Terraform (AFT) works in any Region where AWS Control Tower is available with the exception of Europe (Spain), Europe (Zurich), Israel (Tel Aviv), Middle East (UAE), and Asia Pacific (Hyderabad) because some dependencies are not available. For updated information on Regional availability, see Limitations and quotas in AWS Control Tower in the documentation.
There are no additional costs when using AFT. You pay for the services used by the solution. For example, when you set up AWS Control Tower, you will begin to incur costs for AWS services configured to set up your landing zone and mandatory guardrails.
When building this solution, we worked together with HashiCorp. Armon Dadgar, HashiCorp Co-Founder and CTO, told us: “Managing cloud environments with hundreds or thousands of users can be a complex and time-consuming process. Using a software delivery pipeline integrating Terraform and AWS Control Tower makes it easier to achieve consistent governance and compliance requirements across all accounts.” For more information on our collaboration, see HashiCorp Teams with AWS on New Control Tower Account Factory for Terraform and the HashiCorp tutorial Manage AWS Accounts Using Control Tower Account Factory for Terraform.
The pipeline provides an account creation process that monitors when account provisioning is complete and then triggers additional Terraform modules to enhance the account with further customizations. You can configure the pipeline to use your own custom Terraform modules or pick from pre-published Terraform modules for common products and configurations.
Simplify and standardize AWS account creation using AWS Control Tower Account Factory for Terraform.
— Danilo