AWS Public Sector Blog
Domino Data Lab secures container supply chains at scale using Chainguard on AWS
Ivanti’s 2025 State of Cybersecurity Report revealed that only one in three organizations feel prepared to protect themselves from software supply chain threats. According to Cowbell’s Cyber Roundup Report 2024, with respect to supply chain threats, operating systems pose the greatest immediate threat as “they form the foundational layer of an organization’s entire IT infrastructure.”
This industry sentiment is critical when we consider that organizations are rapidly adopting containerization across both enterprise and startup environments. The average software container has 604 known vulnerabilities in its underlying software components, a new study claims, with over 45% of these vulnerabilities being 2–10 or more years old, according to new research by NetRise.
Considering this industry adoption of containers, the vulnerabilities and supply chain risk become particularly acute for organizations operating in regulated industries or handling sensitive data—especially those building in cloud-focused environments, such as Amazon Web Services (AWS)—where security breaches can result in significant financial and reputational damage.
To mitigate supply chain threats, a root requirement is to continuously secure the operating system that serves as the foundation of these containerized workloads. And to reduce risk in regulated industries, organizations can pursue segmentation and enclave isolation to meet security framework control requirements.
Customer success story: Domino Data Lab
Domino Data Lab (Domino), a leading enterprise MLOps platform, needed to enhance the security posture of its containerized data science workloads while maintaining the flexibility and performance that its customers demand. As a platform serving Fortune 500 companies across regulated industries, Domino required thorough supply chain security without compromising its ability to support diverse data science frameworks and tools.
Domino faced several challenges, including managing security across hundreds of data science container images with varying dependency chains, prioritizing compliance with customer security requirements across multiple industries, maintaining rapid deployment cycles for new data science tools and frameworks, and providing customers with transparency into the security posture of their workloads.
The solution
Chainguard provides trusted open source artifacts for every layer of your modern software stack, containers, language libraries, and virtual machine images. Chainguard protects workloads, makes achieving compliance more straightforward, and maintains resilience in modern cloud environments.
As one of Chainguard’s earliest customers, the company built a uniquely flexible ML platform that came pre-packaged with production-ready container images for Spark, Zookeeper, and Prometheus from day one. By standardizing these core services early, they enabled data scientists to move from experimentation to scalable deployment faster than competitors, without sacrificing security.
Chainguard—an AWS Advanced Partner—delivers hardened, secure, and production‑ready container images built from source and updated continuously. Together with AWS, Chainguard helps teams start secure and stay secure across the container lifecycle—from build to runtime—so they can ship faster, stay compliant, and eliminate risk.
Domino Data Lab Enterprise AI Platform provides an integrated experience encompassing model development, machine learning operations, collaboration, and governance that helps to mitigate supply chain threats and regulates risk using Chainguard on AWS GovCloud (US).
Domino is certified in ISO 27001:2022, ISO 9001:2015, SOC 2, the General Data Protection Regulation (GDPR), and the Health Insurance Portability and Accountability Act (HIPAA). Additionally, Domino supports customer compliance with 21 CFR Part 11, EudraLex Annex 11, World Health Organization (WHO) Annex 5, GDPR, and HIPAA requirements.
In their customer obsession to meet as many regulatory requirements as possible, Domino uses AWS GovCloud (US) to deploy the Domino Data Labs Enterprise AI Platform in a U.S. Department of Defense Impact Level 5 (DoD IL5) environment.
Technical implementation
Domino partnered with Chainguard and AWS to implement a container supply chain security strategy. The implementation at the core of their Domino Data Labs Enterprise AI Platform uses Chainguard’s minimal, hardened base images alongside AWS container services to create a more secure-by-default platform and meet stringent regulatory requirements with AWS GovCloud (US) services.
Technical architecture extending to AWS GovCloud (US)
The Chainguard and AWS reference pipeline extends into AWS GovCloud (US) to secure regulated workloads demanding isolation, compliance, and traceability.
Infrastructure diagram
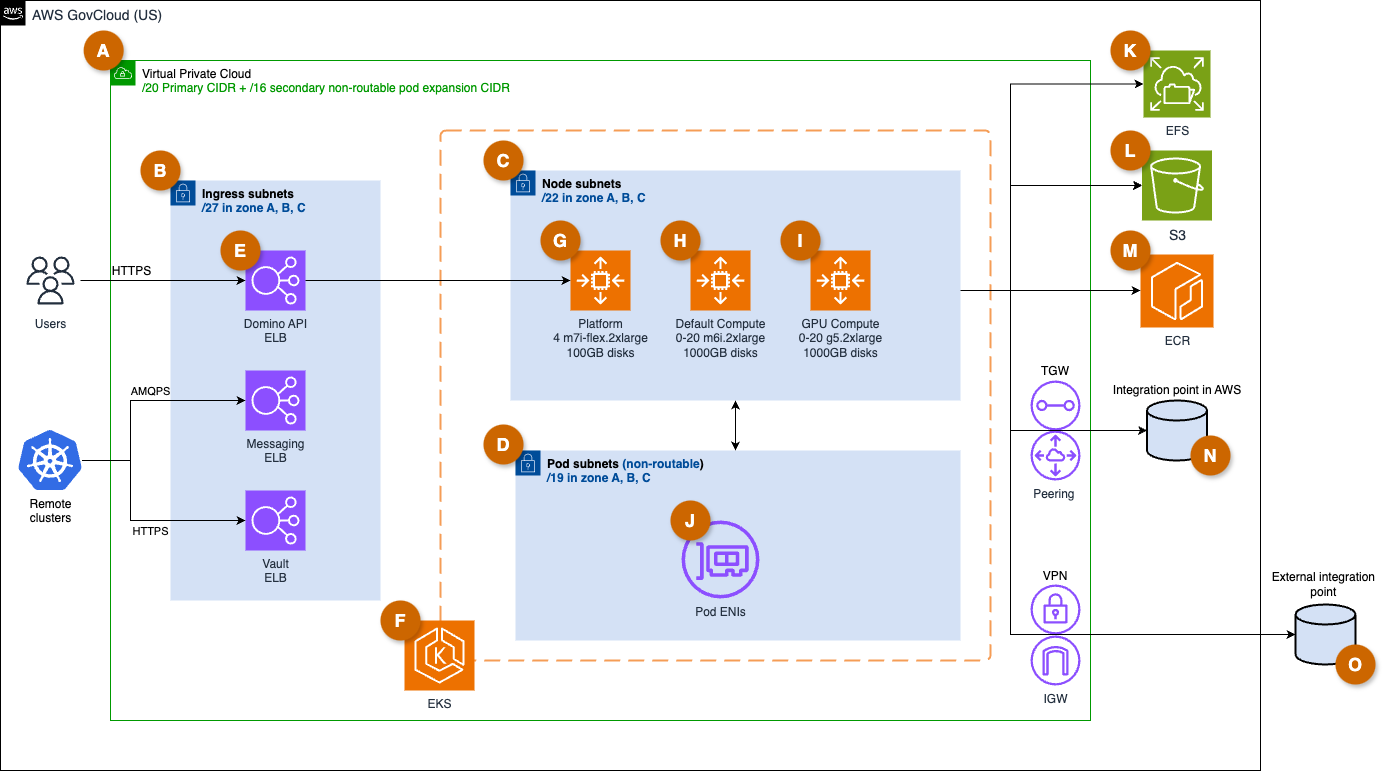
The following architecture in Figure 1 details the secure and scalable architecture for the Domino Data Labs Enterprise AI Platform deployment. The design emphasizes compliance and integration with external systems through controlled network pathways to balance security, scalability, and service integration within AWS GovCloud (US).
Figure 1: Domino Data Labs AWS infrastructure diagram
Infrastructure overview
The following lettered list maps to the letters within Figure 1, and explains components of the design in detail.
A. Domino Hosting Amazon Virtual Private Cloud (Amazon VPC), with /20 primary and /16 secondary routable CIDRs for pod-level isolation. The “/” signifies CIDR notation, /20 representing 4094 useable addresses and /16 representing 65,534 useable addresses respectively.
B. Ingress subnets, in three Availability Zones, accessible to users and API clients, used to host ingress load balancers
C. Node subnets, in three Availability Zones for hosting autoscaling Amazon Elastic Kubernetes Service (EKS) worker nodes
D. Pod subnets, in three Availability Zones for secondary pod Elastic Network Interfaces (ENI), managed via AWS VPC CNI custom networking, not routable by the rest of the VPC or broader network
E. AWS Elastic Load Balancer (ELB), ELBs are managed from Kubernetes with the ELB service, pointing to an in-cluster ingress controller, and can be made internal or public. Domino can terminate TLS with certificates from Amazon Certificate Manager or pass TLS through to the ingress controller.
F. Amazon EKS cluster hosting Domino application and workloads, orchestrating Chainguard-hardened images with cryptographic verification.
G. Domino Platform Nodes, three zonal Amazon Elastic Compute Cloud (Amazon EC2) autoscaling groups of 0-3 m7i-flex.2xlarge instances hosting always-on components of the Domino platform. Autoscaling is available to accommodate a zonal outage
H. Default Compute Nodes, three zonal Amazon EC2 autoscaling groups with configurable minimum and maximum and instance type, used to host user-deployed CPU workloads.
I. GPU Compute Nodes, three zonal Amazon EC2 autoscaling groups with configurable minimum and maximum and instance type, used to host user-deployed GPU workloads.
J. Secondary Pod Interfaces, secondary ENIs attached to all EKS worker nodes by AWS VPC CNI to provide pod networking, non-routable from the rest of the network
K. Amazon Elastic File System (EFS), secondary ENIs attached to all EKS worker nodes by AWS VPC CNI to provide pod networking, non-routable from the rest of the network.
L. Amazon Simple Storage Service (S3) used for Domino internal storage of versioned artifacts, persisted user execution logs, application backups, and monitoring data.
M. AWS Elastic Container Registry (ECR), for storing Domino Environment container images. These are images built in Domino by its build service to user specifications, using Chainguard Images.
N. Integration Points in AWS, AWS native services and other applications hosted on EC2 can be connected to from Domino via public AWS APIs, VPC gateway endpoints, VPC peering connections, and AWS Transit Gateways.
O. External Integration Points, services outside AWS can be connected to from Domino via AWS Site-to-Site VPN gateways, AWS Internet Gateways, or AWS Direct Connect.
External Integration Points overview
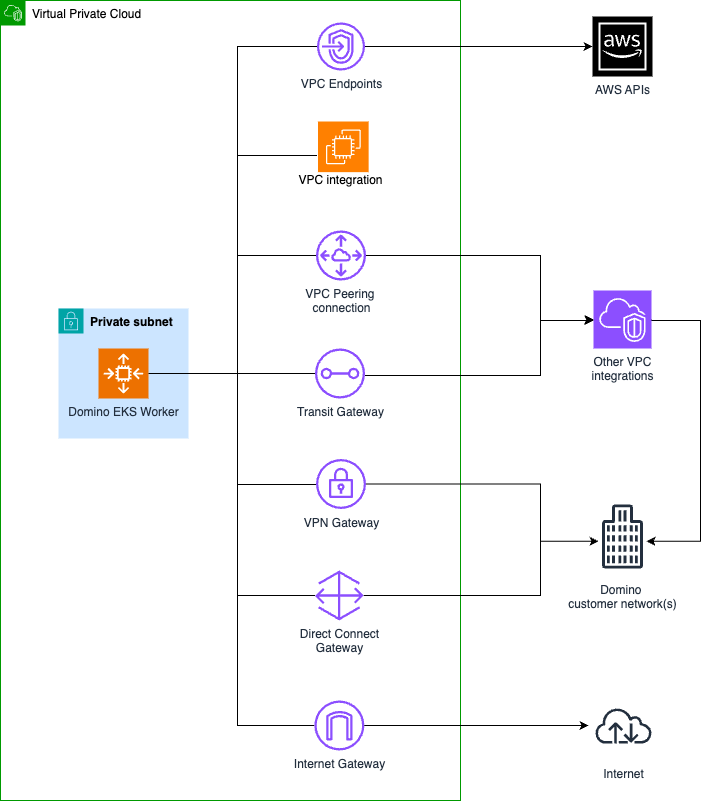
Connections from Domino application components and user-deployed workloads on Domino will originate from the primary networking interface on their host EKS worker node. These connections can reach integration points in the Domino VPC via local routing, other AWS-hosted integration points via VPC Peering connections or Transit Gateways, and integration points in other networks via VPN Gateway, Internet Gateway, or Direct Connect.
Figure 2: Domino Data Labs External Integration Points infrastructure diagram
Pipeline and infrastructure hardening process
The Domino Data Labs development lifecycle testing including code reviews, Static Application Security Testing (SAST), Dynamic Application Security Testing (DAST), third-party penetration testing, and comprehensive automated test suites.
- Source and catalog control – Only Chainguard-verified base images and Helm charts are on allowlist
- Automated updates – Renovate consumes daily Chainguard rebuilds, pinning immutable Secure Hash Algorithms (SHAs)
- Build and validation – GitHub Actions in isolated subnets rebuild and validate containers
- Scanning and governance – JFrog Xray, Prisma Cloud, Trivy, and Grype integrate for multi-layered scanning
- Promotion and release – Merge gates enforce scan evidence before Helm rollouts
- Runtime on AWS – Terraform provisions infrastructure; Amazon EKS applies Chainguard images; IRSA and Pod ENIs isolate workloads
- Resilience and monitoring – Amazon CloudWatch, Amazon GuardDuty, and AWS Resilience Hub enforce runtime visibility and posture
Technical outcomes
Defense in depth for regulated workloads. By combining Chainguard’s supply chain controls with AWS GovCloud (US) network segmentation, Domino Data Labs delivers:
- Immutable deployment from source
- Provable software integrity through daily rebuilt images
- Reduced attack surface using ingress zoning and federated access
The results
The collaboration between Domino, Chainguard, and AWS delivered significant measurable outcomes:
- 95% reduction in critical vulnerabilities – Chainguard’s minimal base images fixed the vast majority of critical and high-severity vulnerabilities.
- 50% faster security reviews – Automated compliance reporting and attestation reduced customer security review cycles from weeks to days.
- Zero security incidents – Resolution of supply chain-related security incidents after implementation.
- 40% improvement in deployment velocity – Streamlined security processes enabled faster rollout of new data science tools and capabilities.
“The partnership between Chainguard and AWS has transformed how we approach container security. We have eliminated the traditional trade-off between security and velocity, enabling our customers to innovate with confidence while meeting the most stringent compliance requirements.”
Matthew Bonyak, principal product manager for Domino Cloud and Platform
Why does this matter for your business?
Organizations choosing to work with Chainguard and AWS can expect transformative benefits that directly impact their bottom line and competitive market position:
- Accelerated innovation – By resolving the traditional security bottleneck in the development process, teams can focus on building differentiated features rather than managing vulnerabilities. Our automated security controls enable continuous deployment without compromising security posture.
- Reduced risk – Supply chain security significantly reduces the likelihood and impact of security incidents. Organizations using Chainguard’s solutions typically observe a 90%+ reduction in container vulnerabilities and do away with entire classes of supply chain attacks.
- Streamlined compliance – Built-in compliance reporting and attestation capabilities streamline audit processes and reduce the overhead of meeting regulatory requirements. Customers report 50%+ reductions in compliance preparation time.
- Cost optimization – Automated security processes and reduced incident response requirements translate to significant cost savings. Organizations typically observe ROI within the first year of implementation through reduced security overhead and faster time-to-market.
Get started with Chainguard and AWS
Ready to transform your container supply chain security? Get started with Chainguard and AWS:
- Assessment and planning – Contact your account manager for a thorough assessment of your container security posture and development of a tailored implementation roadmap
- Pilot implementation – Start with a pilot project using Chainguard Images in your existing AWS environment to demonstrate immediate value
- Full deployment – Scale the solution across your container portfolio with integration into your AWS infrastructure
Amazon ECR Public: The Amazon ECR Public platform now offers the free tier of Chainguard’s trusted container images.
AWS Marketplace: Explore Chainguard’s solutions directly through AWS Marketplace for streamlined procurement and billing. Learn more about Chainguard Images on AWS Marketplace.
AWS Professional Services: Use our joint professional services offerings to accelerate implementation and assist with configuration for your specific requirements.
Conclusion
The partnership between Chainguard and AWS demonstrates how innovative security solutions can solve traditional trade-offs between security and velocity. As container adoption continues to accelerate and supply chain threats evolve, organizations can rely on the combined expertise of Chainguard and AWS to maintain their competitive advantage while meeting the most stringent security requirements.
By choosing Chainguard and AWS, organizations can join a growing community of forward-thinking organizations that have transformed container security from a barrier into a competitive advantage, innovating with confidence in an increasingly complex threat landscape.
About Chainguard
Chainguard is a leading provider of container supply chain security solutions, offering minimal, hardened base images and sophisticated security tooling for cloud-focused applications. As an Advanced AWS Partner, Chainguard helps organizations fix supply chain vulnerabilities while maintaining development velocity.