AWS Partner Network (APN) Blog
How BriteCore Improved Security and Scalability by Migrating Insurance Workloads with AWS Landing Zone
By Ben Hayden, VP Engineering at BriteCore
By Sal Darji, Strategic Alliances & Partnerships at BriteCore
By Sudeep John, Partner Solution Architect at AWS
 |
 |
 |
Traditionally, the insurance industry has relied on AS/400s, mainframes, and other infrastructures to run their workloads.
To help manage those on-premises workloads, six mutual insurance companies partnered in 2009 to build a modern administration system for Property & Casualty (P&C) insurance. That was the origin of BriteCore.
BriteCore was originally designed as an on-premises data center-based monolith; a state-of-the-art core insurance solution. However, the business agility, cost savings, and increased security of the cloud made it clear the insurance industry had to migrate.
BriteCore decided to lead that effort and looked to Amazon Web Services (AWS) and the AWS Landing Zone solution. AWS Landing Zone helped BriteCore set up a secure, multi-account AWS environment based on AWS best practices.
BriteCore is a fully managed, enterprise-level administration platform for insurers and AWS Partner Network (APN) Advanced Technology Partner with the AWS Financial Services Competency.
In this post, we explain how BriteCore used AWS Landing Zone to deliver a modern administrative system for P&C insurance that could be more agile, scale better, and be more secure than on-premises infrastructure.
BriteCore’s Cloud-Native Insurance Services
With the large number of design choices, setting up a multi-account environment can take a significant amount of time, involve the configuration of multiple accounts and services, and require a deep understanding of AWS services.
AWS Landing Zone saves time by automating the set-up of an environment for running secure and scalable workloads, and implementing an initial security baseline through the creation of core accounts and resources. It also provides a baseline environment to get started with a multi-account architecture, identity and access management (IAM), governance, data security, network design, and logging.
Using AWS Landing Zone, BriteCore provides an AWS-native core platform for property and casualty insurers.
The BriteCore Platform includes policy management, billing, claims, agent/policyholder/insurer portals, and a dozen other products needed by insurance carriers to manage their business.
BriteClaims combines claims administration and business process management (BPM) to support the end-to-end claims process. From open to close, agents and adjusters work collaboratively and efficiently within BriteCore to process first notice of loss (FNOL), establish reserves, upload reports, issue payments, and settle claims.
Another innovative offering in the core insurance space is BriteLines, a set of product configuration tools that empowers insurers to define their products and rates. Users can modify existing products, or build coverages, endorsements, underwriting rules, rates, and forms from the ground up. Product definitions are easy to maintain through a point-and-click interface without any coding required.
BriteCore has completed over 55 implementations across a diverse set of insurance carriers and managing general agents (MGA), and has a thriving system of partners and vendors.
Thanks to BriteCore’s own migration to the AWS Cloud, insurers now look to the BriteCore Platform to provide new digital channels for their customers, drive costs lower through automation and efficiency gains, and grow their business and enter new markets through new products and service offerings. Because it’s now a nimble, cloud-enabled platform, BriteCore provides the agility insurers cannot get from on-premises core systems.
Solution Architecture
The BriteCore migration team faced several challenges stemming from their original infrastructure. The first was consolidating existing AWS accounts and creating an inventory of all assets. The second challenge was to keep everything “hot” (working and online) during the migration.
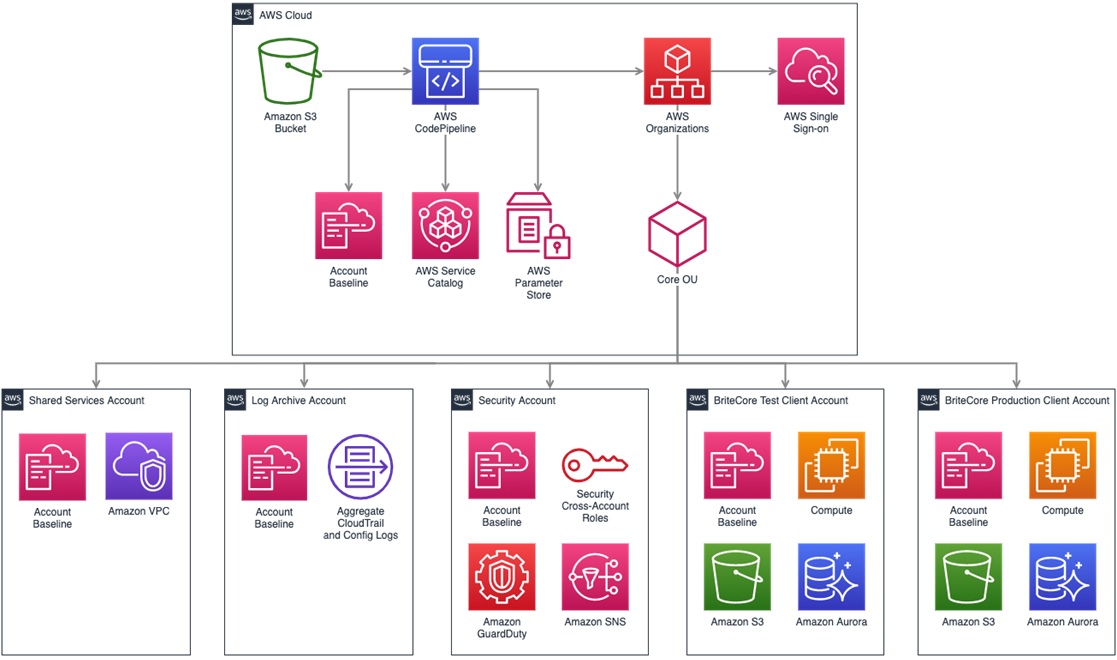
BriteCore built its cloud solution on many AWS services configured with the help of AWS Landing Zone. Figure 1 depicts the architecture that ensured a secure, multi-account AWS environment based on AWS best practices.
Figure 1 – BriteCore architecture configured by AWS Landing Zone.
At a high level, BriteCore has a root AWS Organizations account it uses to create and manage member AWS accounts. The first member account of note is the Shared Services account. It serves as a reference for creating shared infrastructure services, such as directory services or data lakes.
Next is a Log Archive account containing a central Amazon Simple Storage Service (Amazon S3) bucket storing copies of all AWS CloudTrail and AWS Config files.
A Security account serves as the master Amazon GuardDuty account, and is a single account for the security and compliance team to audit or perform emergency security operations on, in case of an incident.
Finally, the architecture provides client-specific BriteCore application accounts across varying stages, including separate staging and production accounts.
How BriteCore Migrated to AWS
To migrate to the architecture shows in Figure 1, BriteCore performed these major steps:
- Create the AWS environment.
- Define AWS Service Catalog offerings.
- Deploy across multiple AWS accounts.
- Implement data security at BriteCore.
Creating the AWS Environment
BriteCore separated infrastructure workloads, such as the logging and security masters, into different accounts. The team also launched each BriteCore client into its own AWS environment. That environment consisted of two client-specific, separate AWS accounts—one for testing/staging workloads, and one for all production workloads.
The primary benefit BriteCore derived from AWS Landing Zone was easier management of the increased number of accounts. It would have been unrealistic to manage every account manually.
Client isolation is nirvana for finance and accounting since BriteCore has complete billing clarity and understands what everything costs per billed customer. This transparency in billing allowed BriteCore to prevent a negative margin on hosting costs, and ensure clients could easily scale their deployments to their workload needs.
Defining Service Catalog Offerings
Definitions written in AWS CloudFormation provided all of the AWS resources deployed into BriteCore’s segregated accounts. The AWS Service Catalog products are AWS service representations of BriteCore’s different product offerings.
Current portfolio items include the AWS Lambda-powered parallel-rater configuration product BriteLines, as well as the robust Claims product BriteClaims built on top of Amazon API Gateway, Amazon Relational Database Service (Amazon RDS), Amazon S3, and other AWS services.
BriteCore also has its own authentication system, BriteAuth, built on Amazon Cognito. BriteAuth supports multi-factor authentication (MFA), federated identities, and robust password management. It ensures maximum security while keeping the login process simple.
These numerous AWS Service Catalog product definitions allowed BriteCore to automate management tasks, which resulted in infrastructure as code (IaC). This propels innovation along with fully automated AWS account creation and AWS Service Catalog portfolio configuration.
Deploying Across Multiple AWS Accounts
The AWS multi-account strategy was key to a secure, managed, and well-governed cloud presence for BriteCore. AWS Landing Zone made this strategy possible. As previously mentioned, Landing Zone deploys an AWS Account Vending Machine (AVM) product for provisioning, and automatically configures new accounts.
Before AWS Landing Zone, BriteCore used a single account to service its many customers. Despite facing some migration challenges, BriteCore quickly adopted AWS Landing Zone and started receiving many benefits like easier management of increased number of AWS accounts and client level isolation.
AWS Landing Zone also allowed BriteCore to innovate faster within each client’s independent staging account without impacting production workloads or other client staging environments. This isolation gives clients a shorter time to value in product R&D.
Also, as a growing organization, BriteCore’s IaC removed the barrier for new developers to start delivering value. For example, Jetty is an insurtech startup that had to meet an aggressive timeline for going live within one year of the company’s creation. Within six months, the team deployed an attractive direct-to-consumer web portal integrated with the BriteCore platform for policy management.
The segregated account approach, powered by AWS Landing Zone, also enables disaster recovery. BriteCore can failover individual client accounts in different AWS regions on demand. Multi-region support is essential in the case of a disaster, but this demonstrable capability makes it a simple way to pass audits.
Implementing Data Security at BriteCore
The final result was an AWS account architecture that follows the AWS Well-Architected Framework.
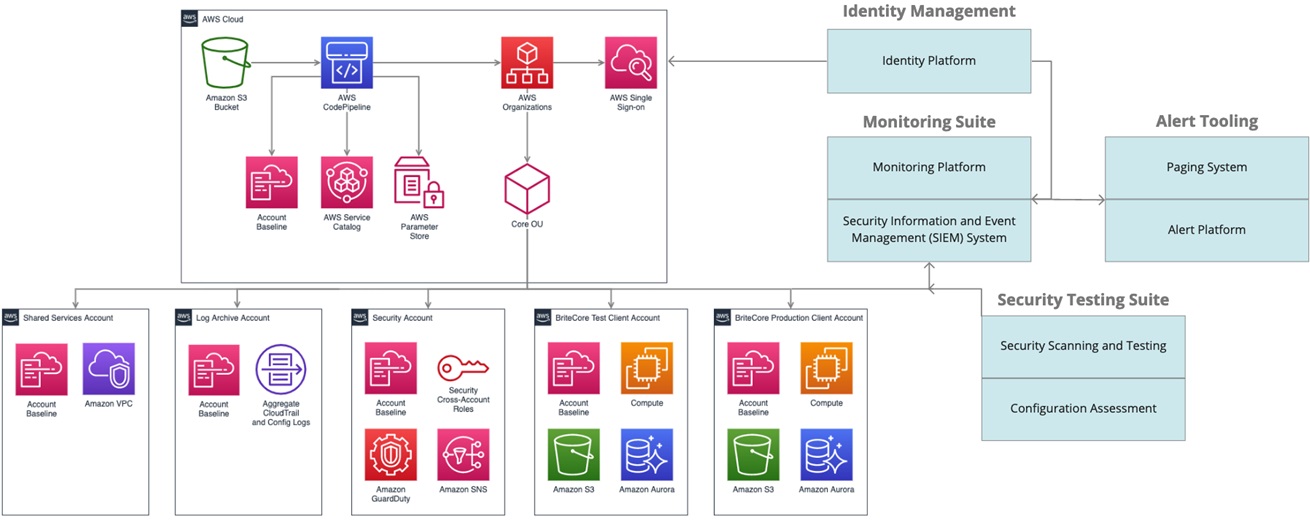
Figure 2 – BriteCore architecture configured by AWS Landing Zone.
By following the best practices in the Well-Architected Framework and separating all the workloads, BriteCore sharpened its security posture. Due to the nature of the personal health information (PII) records the insurance industry gathers, it has extremely stringent data security requirements.
BriteCore’s Security and Privacy program’s foundation are the NIST Cybersecurity Framework’s (CSF) NIST 800-53, and NIST 800-39 standards. The program’s focus is to govern design and operations at a program, controls, and risk management level.
Generally speaking, BriteCore deploys AWS services and other enterprise solutions, where possible, to automate controls that scale well instead of attempting to create homegrown solutions. This decision frees up time to spend on continually refining our control environment.
The following sections describe how BriteCore has implemented its program across multiple security domains.
Access Controls
BriteCore maintains a formal information security policy, which outlines the secure handling of business and client information. The policy provides guidance on logical access to critical systems, password policies for monitoring access rights, and the least privilege principle. The compliance team performs access reviews regularly to ensure this policy is operating effectively.
BriteCore employs a centralized identity provider to control and route access to systems and enforce multi-factor and password policies. Logs are routed from the identity provider to the Security Information and Event Management (SIEM) system. That system has a set of identity provider-specific alerts in place to inform the BriteCore Information Security and Compliance team of any unusual activity.
Business Continuity and Disaster Recovery
By design, BriteCore is resilient as a business. A business continuity and disaster recovery plan is in place and tested annually to help ensure operating effectiveness. Further, BriteCore leverages a set of cloud-native, redundant technologies to create a fault-tolerant environment.
This approach allows a remote workforce to work from anywhere, and to repurpose time spent managing physical infrastructure on efforts to incorporate redundancy into system architectures.
The BriteCore platform leverages native AWS capabilities using multiple AWS Availability Zones and regions coupled with the previously mentioned recovery plan and practices. This helps ensure BriteCore and its services are available to those who need them when they need them. For example, Amazon RDS backups are replicated to Amazon S3 and multiple regions to ensure redundancy and to support disaster recovery objectives.
Encryption
BriteCore provide two types of encryption:
- In Transit — Data transmitted over public networks, such as the internet, is encrypted using a 2048-bit RSA certificate and SHA-256 signature algorithm. Transport layer security (TLS) policies require at least TLS 1.1, and proxy software redirects HTTP requests to HTTPS.
- At Rest — Data at rest is protected using the AES-256 encryption algorithm. AWS Key Management Service (KMS) manages the cryptographic encryption keys. The keys are unique per client, and access to customer master keys is restricted to a small subset of staff who require access based on job responsibilities.
Mobile device management (MDM) software centrally manages all corporate devices such as laptops. MDM enforces full disk encryption using the XTS-AES-128 algorithm.
Monitoring
As detailed above, a SIEM system is in place to monitor logs and alert about suspicious behaviors. Signals are in place to notify the Information Security and Compliance team when configured thresholds have been met, and are continually being reviewed and tuned to be as effective as possible. Notifications are sent in real-time to dedicated communications channels within and thoroughly investigated.
Other monitoring capabilities review information from trusted intelligence sources, such as threat exchange data sources like AlienVault Open Threat Exchange, Amazon GuardDuty, and haveibeenpwned.com, for potential compromise indicators. BriteCore’s SIEM integrates all these sources where possible.
BriteCore is also exploring AWS services that use threat intelligence data, such as AWS WAF, to expand its threat intelligence program and improve log correlation and inspection capabilities. An incident response plan is in place, supplemented by procedures and annual testing to help ensure operating effectiveness.
Security Testing
Security assessment processes and tools continually assess BriteCore systems for potential vulnerabilities. According to internal risk management processes, BriteCore prioritizes mitigations based on industry-standard guidance such as NIST 800-39. Examples include annual penetration testing, quarterly phishing tests, regular vulnerability scanning, annual business continuity, disaster recovery testing, and yearly incident response testing.
Customer Success: Farmers Fire Insurance Company
BriteCore customers have realized significant benefits in agility, availability, and cost savings from their cloud-enabled capabilities. One example is Farmers Fire Insurance Company, which chose BriteCore in 2015 because of their cloud architecture. BriteCore’s dedication to and implementation of infrastructure as code throughout their products was immediately apparent to the team at Farmers Fire Insurance Company.
“BriteCore stood complete, individualized, full-access load-balanced application instances for us in minutes with the click of a button,” says Alex Gann, CIO/CTO at Farmers Fire Insurance Company. “Meanwhile, their competitors requested one to two weeks to pull a single demo instance together.”
Since then, BriteCore continued to deliver new products, such as serverless microservices deployed on AWS Lambda. BriteCore relies on AWS CloudFormation templates to keep everything repeatable, testable, and automated. They configure AWS Organizations to provide their more engineering-resourced customers with controlled yet powerful access and insights into their own AWS deployments.
“After a year on BriteCore, we were fully convinced; we migrated 100 percent of our company infrastructure to AWS,” says Gann. “Every local capability we had was efficiently, reliably, and cost-effectively replaced with Amazon Web Services. We have BriteCore to thank for demonstrating how powerful and positive a decision that would be for us.”
Conclusion
For BriteCore, the road to AWS Landing Zone began in an underground data center in Springfield, Missouri. A seminal moment in BriteCore’s history was the dismantling of the numerous server racks in that on-premises data center. It was the end of a journey and the start of a new era—an era of a fully cloud-native AWS solution.
Since 2012, BriteCore has migrated its original 11 clients to AWS, and deployed 43 more clients directly on the platform. BriteCore’s investment in the migration to AWS Landing Zone has paid dividends in more efficient management of resources, improved visibility, and hardened security.
BriteCore’s platform journey does not end at AWS Landing Zone, but continues with the adoption of new AWS services. BriteCore has realized and grown the original six mutual insurance companies’ vision to provide a truly modern property and casualty insurance system.
BriteCore – APN Partner Spotlight
BriteCore is an AWS Competency Partner and fully managed, enterprise-level administration platform for insurers.
Contact BriteCore | Solution Overview
*Already worked with BriteCore? Rate this Partner
*To review an APN Partner, you must be an AWS customer that has worked with them directly on a project.