
Overview
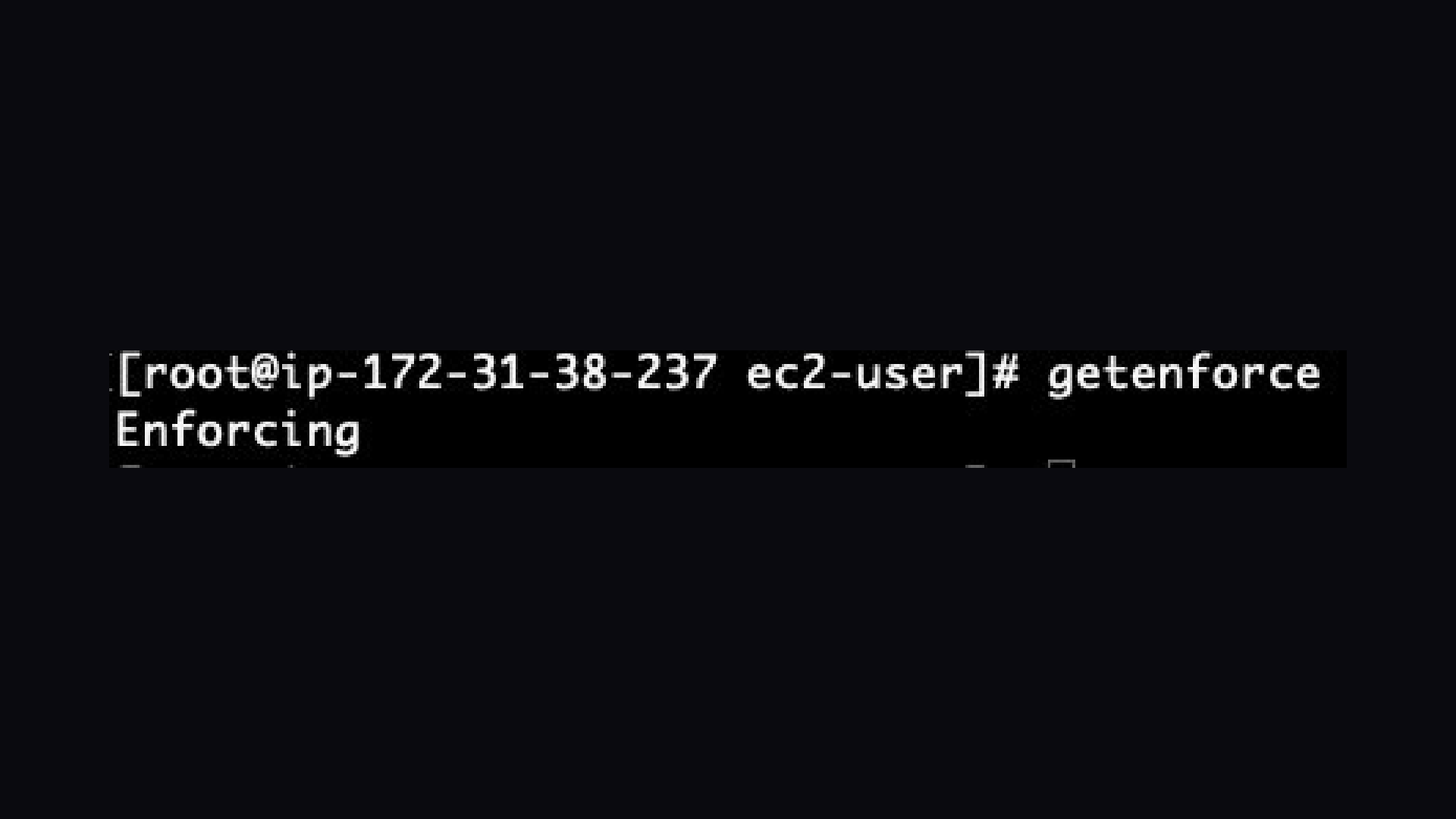
SELinux Enforcing Validation
SELinux Enforcing Validation
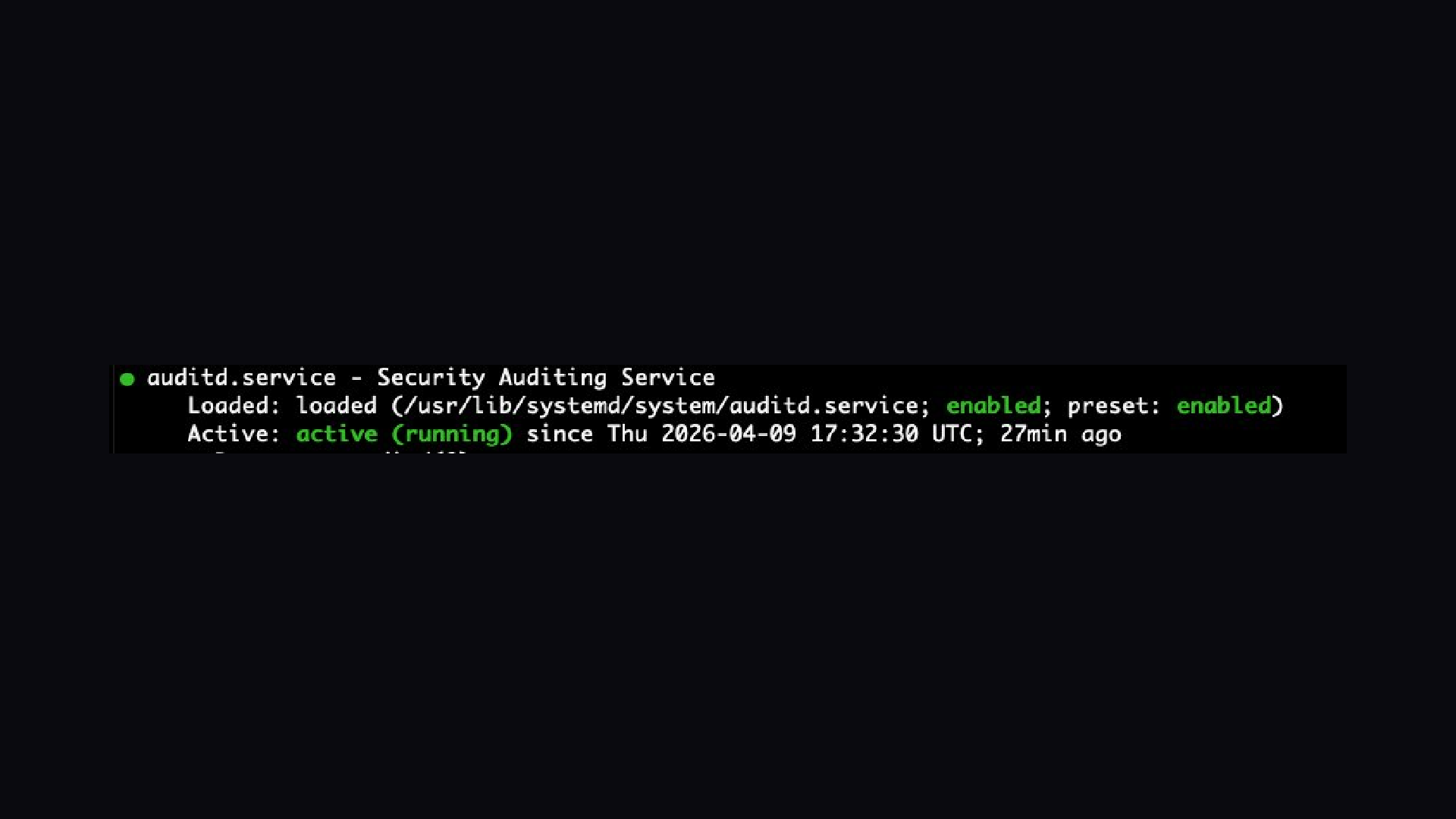
Auditd status
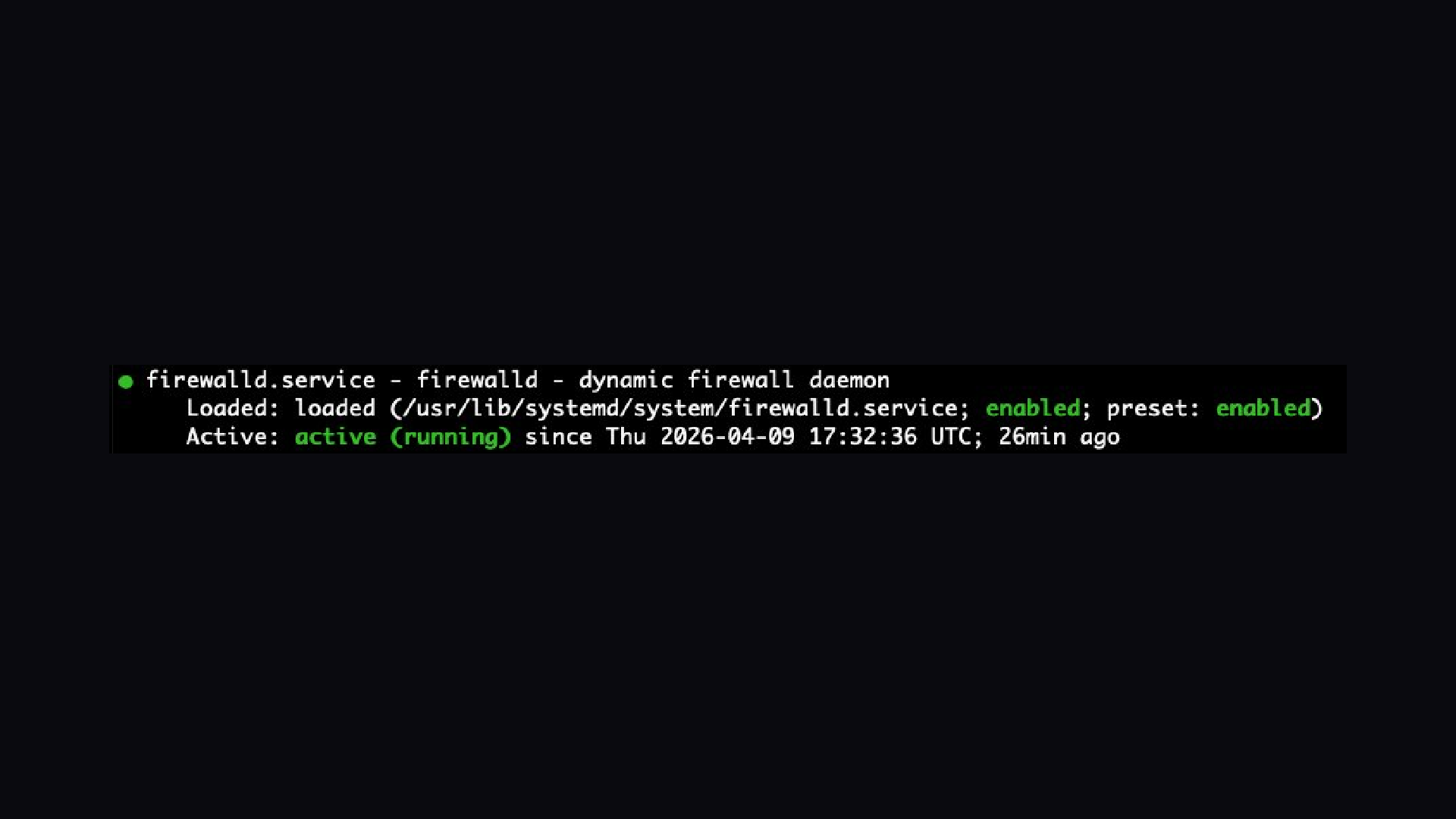
Firewall Status
PTG Hardened RHEL 9 delivers a production-ready, CIS Level 2 compliant base image for teams that need secure infrastructure without the setup overhead.
COMPLIANCE AND HARDENING
- CIS Level 2 hardening via ansible-lockdown RHEL9-CIS role
- SELinux enforcing mode (targeted policy)
- auditd with full CIS audit ruleset and immutable rules (-e 2)
- Lynis hardening score: 85/100
- OpenSCAP compatible
NETWORK AND ACCESS SECURITY
- firewalld active, default zone set to drop, SSH explicitly allowed
- fail2ban active with SSH jail (5 retries, 1-hour ban)
- SSH hardened: PermitRootLogin no, PasswordAuthentication no, MaxAuthTries 3
- AllowTcpForwarding no, X11Forwarding no, AllowAgentForwarding no
KERNEL AND SYSTEM HARDENING
- CIS + Lynis sysctl profile applied
- Firewire blacklisted, core dumps disabled
- Compiler access restricted to root only
- Legal banners on /etc/issue and /etc/issue.net
- PATH hardened for all users
MONITORING AND ACCOUNTING
- psacct and sysstat enabled for process accounting
- rkhunter rootkit detection
- AIDE file integrity monitoring
- dnf-automatic for unattended security updates
AWS NATIVE
- amazon-ssm-agent active; no SSH key required for Systems Manager
- cloud-init compatible, clean on every customer launch
- Compliance manifest generated at /opt/PTG/compliance/manifest.txt
WHO THIS IS FOR Security teams, MSPs, healthcare organizations, fintech companies, and any team that needs a hardened RHEL 9 base they can build on immediately without spending days on manual CIS hardening.
QUICKSTART
- Launch on t3.medium or larger
- SSH: ssh -i your-key.pem ec2-user@PUBLIC_IP
- sudo getenforce > Enforcing
- sudo systemctl status auditd > active (running)
- sudo systemctl status firewalld > active (running)
- cat /opt/PTG/compliance/manifest.txt
- sudo lynis audit system > score 85+ SUPPORT: admin@powelltechnologygroup.com
Highlights
- CIS Level 2 Compliant Out of the Box, Full ansible-lockdown RHEL9-CIS hardening applied at the build time. SELinux enforcing, auditd with immutable rules, and firewalld active. Lynis hardening score 85/100. Skip weeks of manual hardening work and launch compliant from minute one.
- Built for AWS. Works Natively With Your Stack, SSM Agent pre-installed and active. No SSH password auth. Cloud-init compatible. IAM-ready. Compliance manifest at /opt/PTG/compliance/manifest.txt on every instance. Designed for teams that need hardened Linux on EC2 without the setup overhead.
- Active Security Stack Included, fail2ban with SSH jail enabled, rkhunter, AIDE file integrity monitoring, dnf-automatic for unattended security updates, compiler access is restricted to root, firewire blacklisted, and core dumps are disabled. Everything a security-conscious team expects, pre-configured and verified.
Details
Introducing multi-product solutions
You can now purchase comprehensive solutions tailored to use cases and industries.

Features and programs
Financing for AWS Marketplace purchases

Pricing
Free trial
Dimension | Cost/hour |
|---|---|
t3.medium Recommended | $0.10 |
c5.large | $0.10 |
t3.large | $0.10 |
m5.large | $0.10 |
t3.xlarge | $0.10 |
m5.xlarge | $0.10 |
c5.xlarge | $0.10 |
Vendor refund policy
Refunds are available within 7 days of the initial subscription date for any reason. To request a refund, contact admin@powelltechnology-group.com with your AWS account ID and subscription date. Pro-rated refunds are provided for annual subscriptions cancelled after the 7-day window on a case-by-case basis. No refunds are issued for hourly usage already consumed.
How can we make this page better?

Legal
Vendor terms and conditions
Content disclaimer
Delivery details
64-bit (x86) Amazon Machine Image (AMI)
Amazon Machine Image (AMI)
An AMI is a virtual image that provides the information required to launch an instance. Amazon EC2 (Elastic Compute Cloud) instances are virtual servers on which you can run your applications and workloads, offering varying combinations of CPU, memory, storage, and networking resources. You can launch as many instances from as many different AMIs as you need.
Version release notes
Initial release. CIS Level 2 hardened RHEL 9 with SELinux enforcing, auditd immutable ruleset, firewalld, fail2ban SSH jail active, and Lynis score 85/100.
Additional details
Usage instructions
- Launch this AMI on t3.medium or larger 2. Assign a key pair and allow inbound SSH port 22 from your IP 3. Connect: ssh -i your-key.pem ec2-user@PUBLIC_IP 4. Verify SELinux: sudo getenforce (expected: Enforcing) 5. Verify auditd: sudo systemctl status auditd (expected: active running) 6. Verify firewall: sudo systemctl status firewalld (expected: active running) 7. View manifest: cat /opt/PTG/compliance/manifest.txt 8. Full scan: sudo lynis audit system (expected score: 85+) For Systems Manager access without SSH: Ensure your EC2 instance role has AmazonSSMManagedInstanceCore attached - SSM Agent is pre-installed and active on all instances.
Support
Vendor support
Supported instance types: t3.medium, t3.large, t3.xlarge, m5.large, m5.xlarge, c5.large, c5.xlarge. Support contact: admin@powelltechnology-group.com
Response time: 48 hours Monday through Friday, Eastern Time
Support includes:
- Configuration questions about the pre-installed security stack
- Guidance on CIS compliance controls baked into this image
- Assistance verifying hardening settings after launch
- Documentation on what each security control does and why
For urgent issues contact: admin@powelltechnology-group.com with subject line: PTG RHEL9 AMI - Urgent
AWS infrastructure support
AWS Support is a one-on-one, fast-response support channel that is staffed 24x7x365 with experienced and technical support engineers. The service helps customers of all sizes and technical abilities to successfully utilize the products and features provided by Amazon Web Services.