
Overview
Kali-AI v2 Platform Overview
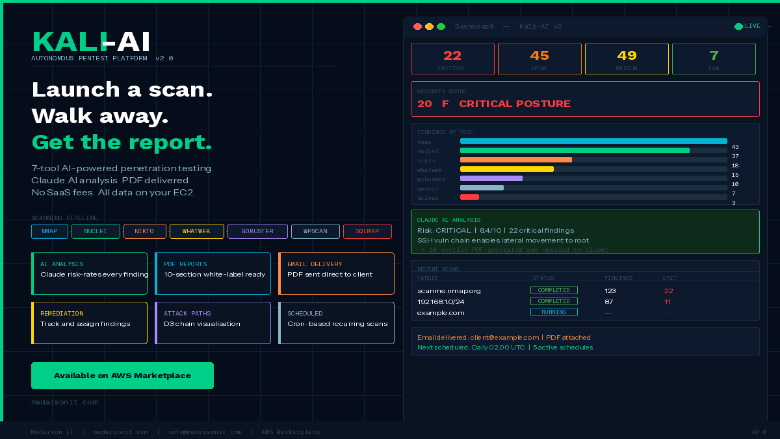
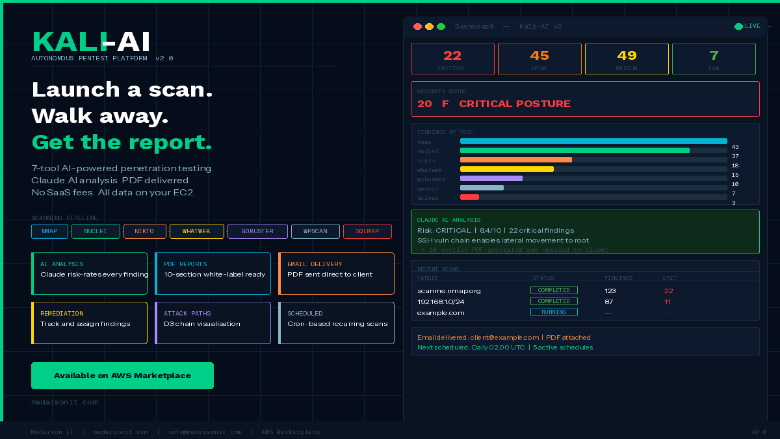
Kali-AI v2 autonomous pentest platform dashboard -- 7-tool pipeline, Claude AI analysis, PDF reports, security score, and findings tracker on AWS EC2
Kali-AI v2 Platform Overview
Kali-AI v2 Use Cases and Quick Start

Kali-AI v2 Full Feature Set

Kali-AI v2 - Autonomous PenetTesting Platform
This is a repackaged software product from Madarson IT with additional charges applied for seller support. Kali-AI v2 is a self-hosted autonomous penetration testing platform built on Hardened Ubuntu 24.04 LTS. It runs a 7-tool scanning pipeline, analyses every finding with Anthropic Claude AI, and generates professional 10-section PDF security reports automatically -- no manual steps between scan launch and final deliverable.
Designed for MSSPs, security teams, red teams, and penetration testers who need repeatable automated assessments without SaaS pricing or data residency risk. All data stays on your EC2 instance.
WHAT IT DOES
Kali-AI v2 runs on a security-hardened Ubuntu 24.04 base with Kali Linux security tools installed. It automatically runs Nmap, Nuclei, Nikto, WhatWeb, Gobuster, WPScan, and SQLMap in sequence. Findings are correlated, enriched with CVE data, and analysed by Claude AI to produce an executive summary, risk rating, attack path analysis, remediation plan, and NIST/PCI-DSS/ISO 27001 compliance observations -- delivered as a 10-section PDF.
FEATURES
7-Tool Pipeline: Nmap, Nuclei, Nikto, WhatWeb, Gobuster, WPScan, SQLMap run automatically in sequence. Claude AI Analysis: Every finding risk-rated and written up by Anthropic Claude automatically. 10-Section PDF Reports: Professional reports ready to deliver. White-label with your company name and logo. Email Delivery: PDF reports and scan alerts sent via SMTP on completion. Security Score Dashboard: Posture score (0-100, A-F), risk gauge, severity chart, 7-day timeline. Remediation Tracker: Assign findings, set due dates, track status, export to CSV. Attack Path Visualization: Interactive graph showing chained vulnerability sequences. Scan Delta: New vs resolved vs persistent findings across assessments. Scheduled Scans: Cron-based recurring scans. Full, Quick, Web, or Network types. Batch Scanning: Up to 20 targets with parallel execution. Client and Project Tagging: For MSSP workflow and report organization. Security Copilot: AI assistant for plain-language queries about results and remediation. RBAC: Admin, analyst, and auditor roles with JWT authentication. Integrations: Slack and Teams webhooks, SIEM JSON export, full REST API. First-Boot Setup Wizard: No default credentials. Admin created by operator on first access.
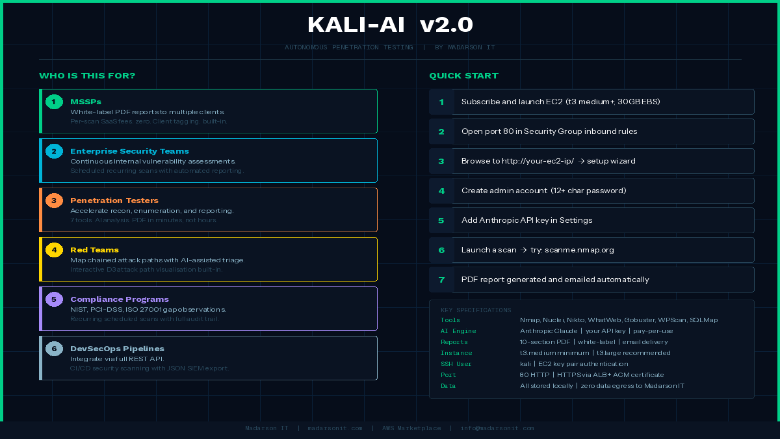
WHO IS THIS FOR?
MSSPs: White-label automated reports to multiple clients. No per-scan fees. Enterprise Teams: Continuous assessments on a recurring schedule. Penetration Testers: Accelerate recon and reporting. Focus on analysis, not tooling. Red Teams: AI-assisted attack path mapping and chained exploitation analysis. Compliance Programs: NIST, PCI-DSS, ISO 27001 gap observations on schedule. DevSecOps: Integrate scanning into CI/CD via REST API.
QUICK START
- Launch EC2 instance (t3.medium+, 30GB EBS). Open port 80 in Security Group.
- Browse to http://your-ec2-ip/ and complete the setup wizard.
- Create admin account (12+ character password).
- Add Anthropic API key in Settings (console.anthropic.com -- pay-per-use).
- Launch a scan. Try: scanme.nmap.org
- View AI-analyzed PDF report in Reports section.
CONFIGURATION
Edit /opt/kali-ai/.env then run: sudo systemctl restart kali-ai
ANTHROPIC_API_KEY -- Required. Claude AI analysis. APP_SECRET_KEY -- JWT signing secret. SMTP_HOST / SMTP_USER / SMTP_PASSWORD -- Email delivery. DISPLAY_TIMEZONE -- Report timestamps (e.g. America/New_York). REPORT_COMPANY_NAME / REPORT_COMPANY_LOGO -- White-label PDF branding. SLACK_WEBHOOK_URL / TEAMS_WEBHOOK_URL -- Webhook notifications.
SSH as kali user with EC2 key pair. For HTTPS use ALB or CloudFront with ACM certificate.
RESPONSIBLE USE AND DISCLAIMER:
AUTHORIZED USE ONLY. For security testing of systems you have explicit written permission to test. Unauthorized use violates the AWS Acceptable Use Policy, the Computer Fraud and Abuse Act (CFAA), and equivalent laws. By deploying this product you agree to: (1) only test systems you are authorized to test; (2) comply with all applicable laws; (3) comply with the AWS Acceptable Use Policy; (4) Madarson IT LLC bears no liability for misuse, unauthorized access, or damages of any kind.
Ubuntu is a registered trademark of Canonical Ltd. Claude is a third-party AI service billed directly to your Anthropic account and subject to Anthropic's Terms of Service. All open-source security tools included (Nmap, Nuclei, Nikto, WhatWeb, Gobuster, WPScan, SQLMap) are provided under their respective open-source licenses. Madarson IT does not relicense these tools.
Support: info@madarsonit.com
Highlights
- . 7-Tool Automated Pipeline on Hardened Ubuntu 24.04 LTS: Nmap, Nuclei, Nikto, WhatWeb, Gobuster, WPScan, and SQLMap run automatically in sequence. . Claude AI analyses every finding and generates a professional 10-section PDF report on completion.
- . Built for MSSPs and Security Teams . White-label PDF reports with your branding, client and project tagging, scheduled recurring scans, batch scanning of up to 20 targets, and a full REST API for pipeline integration.
- . Zero Data Egress - Your Key, Your Data . All scan data stays on your EC2 instance. AI analysis uses your own Anthropic API key with pay-per-use pricing. . No SaaS subscription, no hidden fees, no vendor data retention.
Details
Introducing multi-product solutions
You can now purchase comprehensive solutions tailored to use cases and industries.

Features and programs
Financing for AWS Marketplace purchases

Pricing
- ...
Dimension | Cost/hour |
|---|---|
m5a.large Recommended | $0.50 |
t3.micro | $0.50 |
t2.micro | $0.25 |
m3.large | $0.50 |
p3.16xlarge | $16.00 |
c8a.2xlarge | $2.00 |
r5a.xlarge | $1.00 |
i3.4xlarge | $4.00 |
t2.xlarge | $1.00 |
i2.4xlarge | $4.00 |
Vendor refund policy
There is no refund policy for this image
How can we make this page better?

Legal
Vendor terms and conditions
Content disclaimer
Delivery details
64-bit (x86) Amazon Machine Image (AMI)
Amazon Machine Image (AMI)
An AMI is a virtual image that provides the information required to launch an instance. Amazon EC2 (Elastic Compute Cloud) instances are virtual servers on which you can run your applications and workloads, offering varying combinations of CPU, memory, storage, and networking resources. You can launch as many instances from as many different AMIs as you need.
Version release notes
Kali-AI v2 - Autonomous Pentest Platform on Hardened Ubuntu 24.04 LTS
Additional details
Usage instructions
Allow inbound SSH access in your security group (TCP port 22) Allow inbound web access in your security group on TCP port 80 To connect to your instance using the Amazon EC2 console: Open the Amazon EC2 console at https://console.aws.amazon.com/ec2/ In the navigation pane, choose Instances. Select the instance and choose Connect. Choose the EC2 Instance Connect tab. For Connection type, choose Connect using EC2 Instance Connect. Access the ec2 with the default username: "kali" To Access Dashboard and setup admin account: http://your-vm-ip
Resources
Vendor resources
Support
Vendor support
To speak with us about private offers or additional pricing options, please contact us at info@madarsonit.com
AWS infrastructure support
AWS Support is a one-on-one, fast-response support channel that is staffed 24x7x365 with experienced and technical support engineers. The service helps customers of all sizes and technical abilities to successfully utilize the products and features provided by Amazon Web Services.