AWS Partner Network (APN) Blog
Automated Cloud Governance Using the Superwerker on AWS Quick Start
By Joern Barthel, Program Management Cloud – kreuzwerker GmbH
By Sebastian Müller, Sr. Cloud Consultant and AWS Serverless Hero – superluminar GmbH
 |
With AWS Organizations, Amazon Web Services (AWS) provides the foundational services and features to manage multiple AWS accounts from a central location.
For customers, multi-account setups enable improved security and cost outcomes. They also contribute to key metrics like development and deployment velocity by retaining the technological freedom for small and independent workload teams.
Managing a cloud infrastructure consisting of multiple AWS accounts is therefore one of the most important but also complex topics for Well-Architected cloud environments.
To address this, AWS introduced in 2018 an AWS Solutions Implementation called AWS Landing Zone. With a complex set of AWS CloudFormation templates, custom resources, and pre-configured best practices, Landing Zone laid the foundation for a professional and reliable baseline when using an AWS environment consisting of multiple accounts.
Based on Landing Zone and customer feedback, AWS in 2019 then launched AWS Control Tower and wrapped the Landing Zone solution into a product.
The superwerker on AWS Quick Start builds on this history by integrating additional foundational services and configuring them to provide best practices as a ready-to-use solution.
In this post, we’ll introduce you to superwerker, an open source project created by kreuzwerker and superluminar—both AWS Advanced Consulting Partners and members of the AWS Well-Architected Partner Program.
Our companies regularly assist customers in setting up complex and secure AWS environments. When doing the exact same tasks and configurations for multiple clients, our DevOps mindset requires an automated drop-in response to this problem.
This is why superwerker was created as a free and open source AWS Quick Start, which helps you deploy popular technologies on AWS based on best practices for security and high availability.
Check out the superwerker on AWS Quick Start >>
How it Works
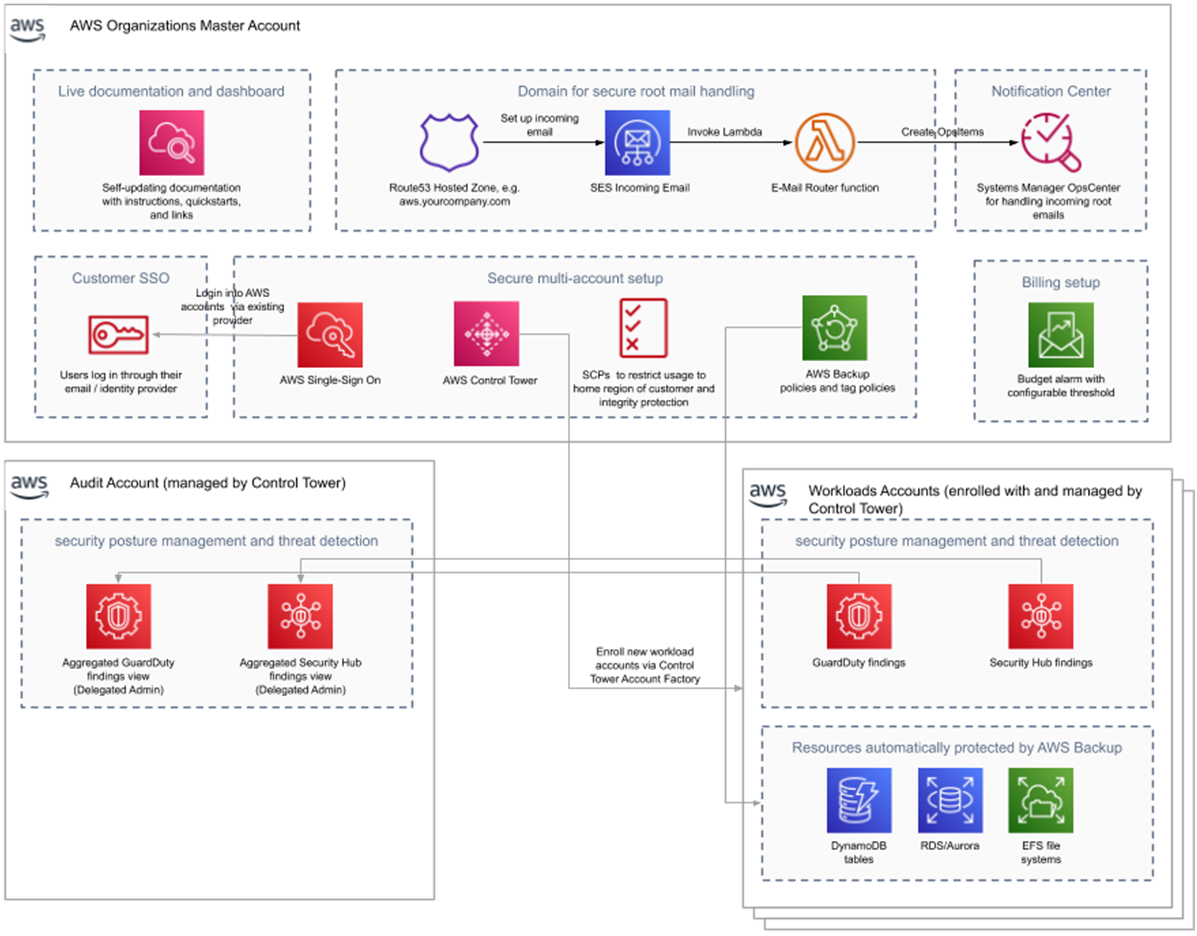
Two services enabled by the superwerker on AWS Quick Start are AWS Control Tower and AWS Single Sign-On (SSO), providing current best practices for multi-account setups such as security and compliance guardrails.
Together with AWS Organizations, these services provide features and workflows to manage multiple AWS accounts in a central place.
Multi-account setups are a recommended best practice even for smaller organizations, enabling customers to scope individual user and/or group access to AWS accounts (such as workload A in production) instead of implementing an access strategy on a policy level.
Since the effective AWS Identity and Access Management (IAM) policies being applied to specific resources can be complex (and therefore hard to debug and audit), scoping access to AWS accounts and matching coarse grained policies is preferred. This pattern is well supported through the usage of Control Tower and SSO.
On top of that, SSO enables modern WebAuth multi-factor authentication (MFA), as well as delegation to upstream corporate identity providers such as Okta and other SAML-based solutions.
Next, AWS Security Hub (for a continuous monitoring of AWS security standards) and Amazon GuardDuty (for continuous threat detection) are enabled. Both services are configured to work on all available accounts and aggregate their findings into the audit account provided automatically by Control Tower.
Parallel to this, AWS Backup is enabled for Amazon DynamoDB, Amazon Elastic Block Store (EBS), and Amazon Relational Database Service (Amazon RDS) in all accounts, with an opt-out for dev/test accounts.
An automated billing and budget setup is created in the management account that creates alerts based on an increase in actual usage (as opposed to setting fixed budgets for filterable sets of resources).
We believe this reflects an outcome many customers prefer when entering the cloud: start with a reasonable upper spent limit and getting alerts when this goal post moves (and so forth).
Figure 1 – Superwerker architecture overview of configured services.
Service control policy-based integrity protection and common policies are applied as well, and an Amazon CloudWatch dashboard is set up as a living documentation for the Quick Start. Currently, this is being used as an interactive README for the installation process, but in the future it will contain technical and process pointers as well.
Amazon Simple Email Service (SES) is used to provide secure mailboxes for the root email accounts of all AWS member accounts. This also enables future workflow, such as the automated recovery of newly-created member accounts, adding additional features like MFA and security questions in the process.
Furthermore, unified workflow notifications using the OpsCenter in AWS Systems Manager are implemented. This built-in issue tracking system is set up as a foundation for all kinds of notifications. It serves as a bridge into customers’ ticketing systems using Amazon EventBridge integrations or solutions such as AWS Service Management Connector for Jira Service Management.
Technical Implementation
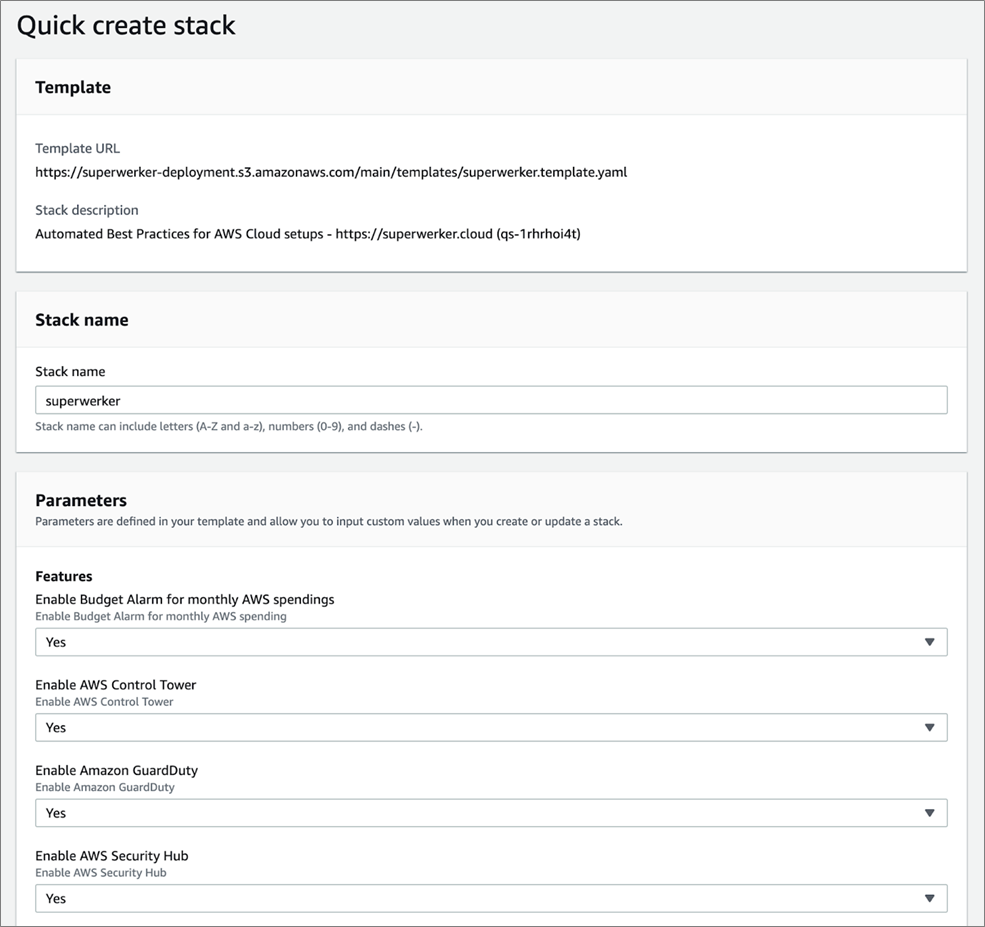
Technically, superwerker is implemented as a collection of nested CloudFormation YAML stacks. The top-level stack implements a number of feature flippers which can be used to selectively disable certain optional features of superwerker (such as backups).
Figure 2 – The superwerker CloudFormation template configuration.
Internally, the CloudFormation stacks utilize serverless transforms to provide inline AWS Lambda functions to implement various functionality, such as the ability of superwerker to parse incoming emails, automatically filter them, and create appropriate OpsCenter items. Other Lambda functions supplement missing CloudFormation support for certain AWS APIs.
In some cases where no API exists at all, superwerker utilizes Puppeteer scripts running in a CloudWatch Synthetics Canary runtime environment to use an actual headless browser to click on the appropriate links in the AWS Management Console.
This last resort style of automation is used for certain actions, such as the Control Tower setup and in our CI/CD pipeline that performs a set of integration tests against specifically vended, clean management accounts.
Figure 3 – Overview of a CloudWatch Synthetics Canary in superwerker.
AWS CloudFormation StackSets with service managed permissions are utilized as well. These are deployed to circumvent the missing regional support of certain features, such as SES email recipiency as well as deploying certain resources to member accounts in the case of the backup feature.
Figure 4 – Included CloudFormation stacks in superwerker.
Due to the synchronous nature of the superwerker architecture, the net installation time takes approximately 90 minutes.
Video: Superwerker Installation (3:34)
Summary
The superwerker on AWS Quick Start provides an automation of what a consultant from either kreuzwerker or superluminar who’s charged with building a platform and landing zone would build for a customer.
As an individual consulting solution, this typically involves a mix of consulting and hands-on click ops, as well as building some automation in the customer’s preferred infrastructure provisioning tooling.
We believe that having automation to abstract this undifferentiated heavy lifting away is the way to go, freeing customers from having to come up with individual solutions to run their workloads on a Well-Architected AWS platform.
Learn more on the superwerker website, by joining our mailing list, the #superwerker Slack channel on the OG-AWS Slack, or by reaching out to info@superwerker.cloud.
Superwerker is available on GitHub and as an AWS Quick Start.