
Overview
Sentrilite Real-Time Threat Detection and Response
Sentrilite Real-Time Threat Detection and Response

Product video
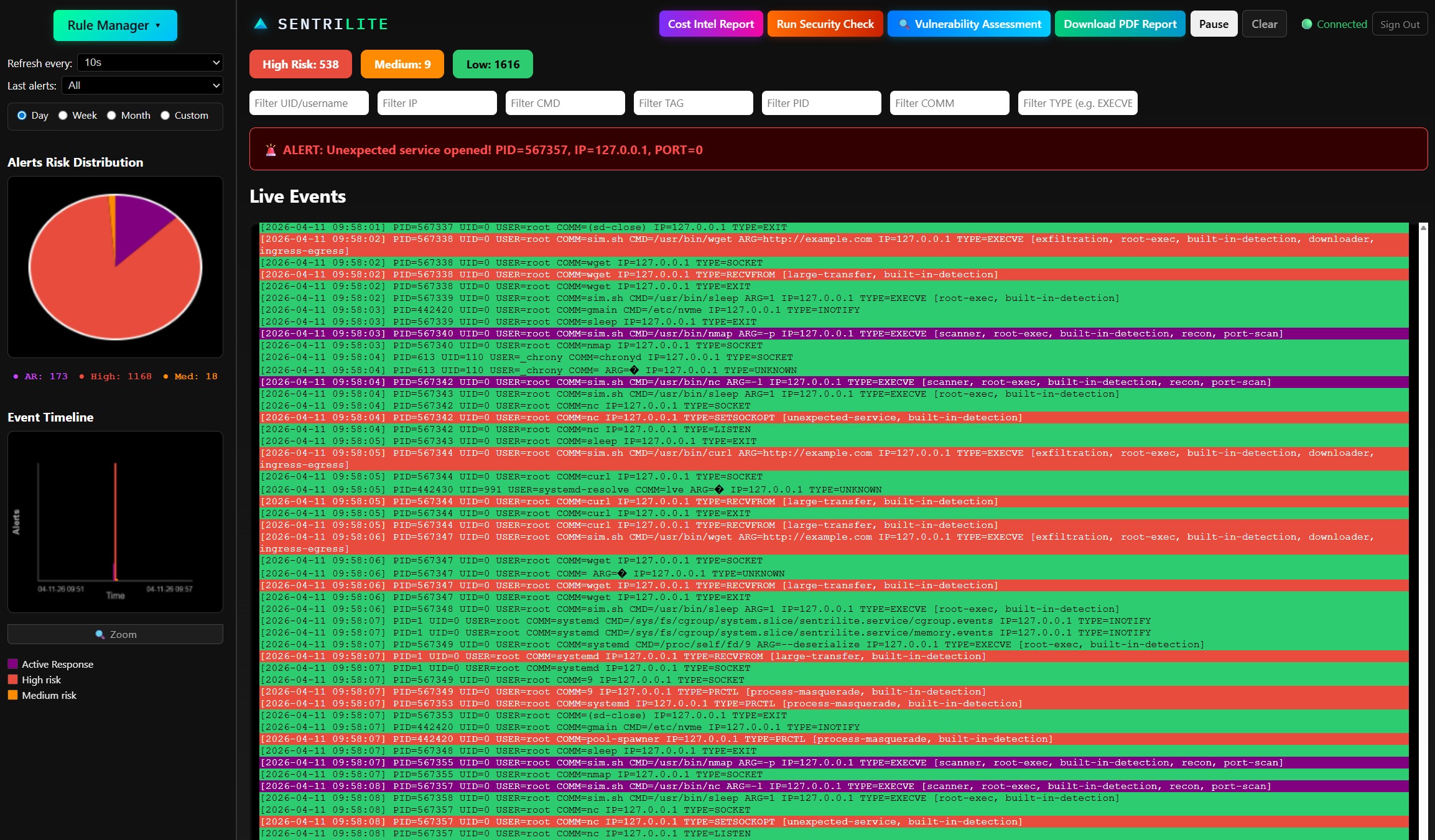
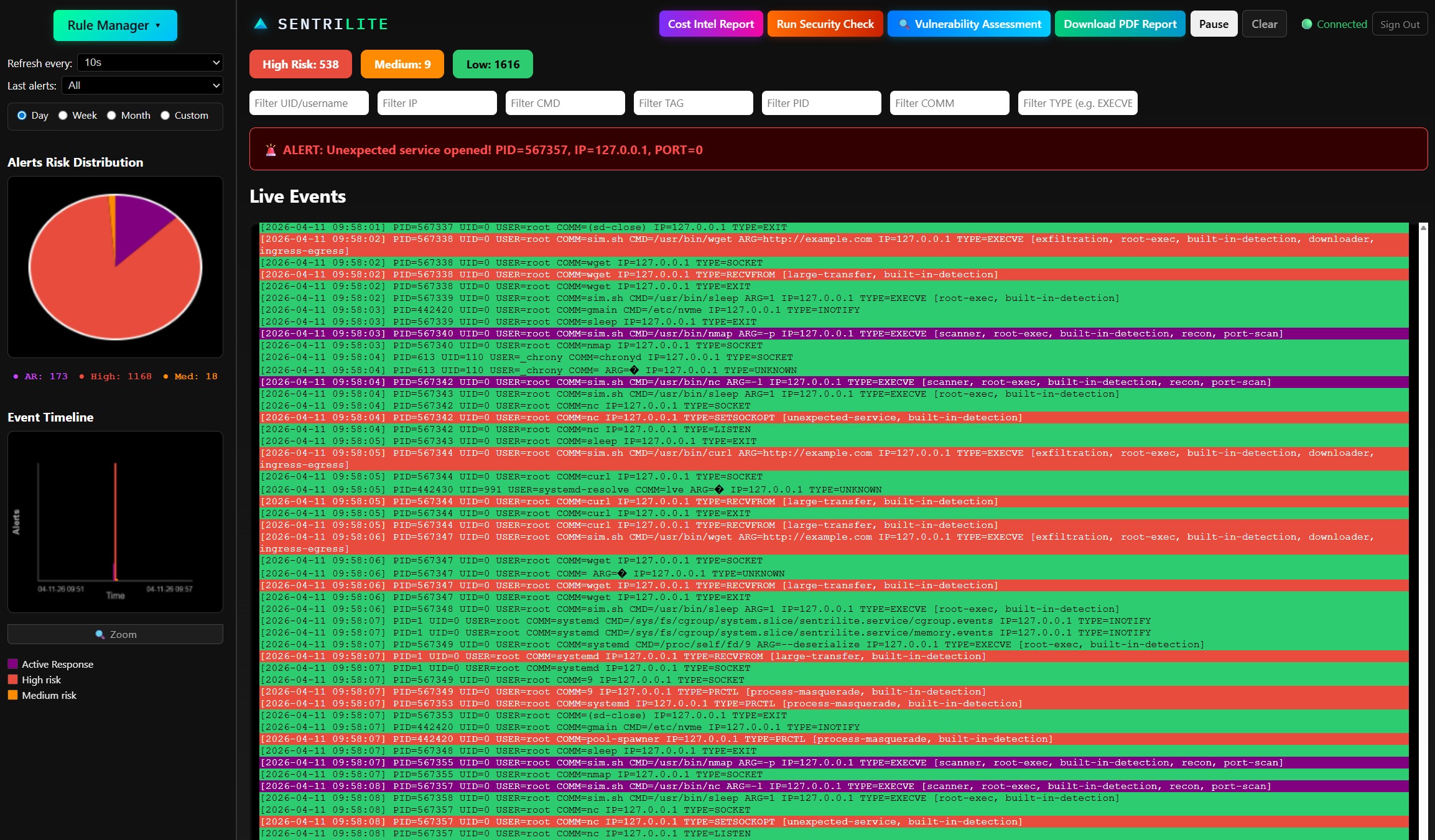
Sentrilite is a kernel-level Cloud Runtime Detection and Response (CDR) platform built for teams running workloads on Kubernetes, public cloud, and hybrid-cloud infrastructure. By operating at the eBPF level, Sentrilite captures threat activity below the application and container boundary, where most security tools have no visibility. This means attacks that bypass signature-based detection, including zero-day exploits and newly disclosed CVEs, are caught based on behavior, not signatures, the moment they occur. Real-Time Cloud Runtime Detection and Response Modern cloud attacks move fast. By the time a CVE is disclosed, threat actors are already scanning for exposed instances. Sentrilite responds to newly disclosed CVEs instantly, because detection rules are behavior-based and can be written, tested, and deployed in seconds without restarting services or modifying infrastructure. Your security posture adapts as fast as the threat landscape does. Detection-as-Code with Automated Response Security rules in Sentrilite are defined in plain JSON, version-controlled, and fully customizable. Teams can write new detection logic for emerging threats, tune existing rules to reduce false positives, and automate response actions, all without touching application code or redeploying workloads. This gives security engineers the same workflow they use for application code, applied directly to cloud threat detection. 300+ Pre-Built Detection Rules Sentrilite ships with over 300 pre-built detection rules covering the most critical threat categories out of the box, including suspicious process execution, anomalous network connections, sensitive file access, privilege escalation attempts, Kubernetes namespace escapes, container breakouts, and lateral movement patterns. Teams get immediate coverage across cloud workloads from the first minute of deployment, with the ability to extend and customize from there. Cloud Workload Protection (CWPP) and Container Security Sentrilite provides continuous runtime protection for containers, Kubernetes clusters, and cloud workloads across hybrid environments. By monitoring at the kernel level, it enforces workload behavior policies without agents inside containers, sidecars, or changes to existing CI/CD pipelines. Security teams gain deep visibility into container activity, inter-pod communication, and workload-level anomalies across every node in the cluster. Zero-Day Threat Defense Because Sentrilite detects based on kernel-level behavior rather than known signatures, it provides protection against zero-day threats that no signature database has seen yet. When a new CVE drops, teams can write a targeted behavioral rule and push it instantly across their entire fleet, without waiting for a vendor patch cycle or rule update. Unified Real-Time Dashboard Sentrilite provides a single pane of glass for monitoring and securing Kubernetes clusters, containers, and hybrid cloud workloads. Security teams get real-time visibility into alerts, process activity, network connections, and system call patterns across every node in their infrastructure, without switching between tools or correlating data from multiple sources. Centralized Alert Storage and Forensic Analysis All security alerts are aggregated and retained in a centralized database, giving teams the historical depth needed for forensic investigation, compliance reporting, and long-term trend analysis. When an incident occurs, the full chain of events is available immediately, with timestamps, process context, triggered rules, and attribution details. AI-Powered Incident Insights Sentrilite automatically summarizes security incidents, surfaces risk trends across your infrastructure, and delivers actionable remediation recommendations. Instead of raw alert feeds that require manual triage, teams receive clear, prioritized guidance on what happened, what is at risk, and what to do next. One-Click Audit-Ready Runtime Security Reports With a single click, Sentrilite generates comprehensive PDF reports covering Runtime Security events across your entire infrastructure. Each report includes full attribution, contextual details, triggered detection rules, and remediation steps, making them ready for security reviews, compliance audits, and executive briefings without additional formatting or manual compilation. Deployment and Compatibility Sentrilite deploys in under five minutes with a single Docker command or Helm chart. It requires no application code changes, no sidecars, no cloud billing API credentials, and no manual tagging. It runs on AWS EC2, EKS, GKE, AKS, bare metal, virtual machines, and hybrid on-premises workloads, making it suitable for any Linux-based Kubernetes or cloud infrastructure regardless of where it runs.
Highlights
- Cloud Runtime Detection & Response: Detection-as-Code with Automated Response - Define and update custom security rules in seconds using simple JSON. No redeploys. No downtime.
- One Command Install & One-Click Reports for Runtime Security, Vulnerability Management - with full attribution, context and remediation details.
- AI-Powered Incident Insights - Automatically summarize incidents, surface risk trends, and receive actionable remediation recommendations.
Details
Introducing multi-product solutions
You can now purchase comprehensive solutions tailored to use cases and industries.

Features and programs
Financing for AWS Marketplace purchases

Pricing
Vendor refund policy
Refunds are handled in accordance with AWS Marketplace policies. Customers may request a refund through AWS Support. Refunds are evaluated on a case-by-case basis and may be granted for technical issues or billing errors. For assistance, please contact our support team.
How can we make this page better?

Legal
Vendor terms and conditions
Content disclaimer
Delivery details
64-bit (x86) Amazon Machine Image (AMI)
Amazon Machine Image (AMI)
An AMI is a virtual image that provides the information required to launch an instance. Amazon EC2 (Elastic Compute Cloud) instances are virtual servers on which you can run your applications and workloads, offering varying combinations of CPU, memory, storage, and networking resources. You can launch as many instances from as many different AMIs as you need.
Version release notes
Kernel-level EDR/XDR runtime security engine using eBPF, detects threats below the application and container boundary with zero application instrumentation Real-time detection of privilege escalation, namespace escapes, process masquerade, lateral movement, shell spawns, and anomalous network behavior Zero-day threat defense, behavior-based detection catches novel attacks that bypass signature-based tools Detection-as-Code, define, update, and deploy custom threat detection rules in plain JSON in seconds, with no redeployments and no downtime 300+ pre-built detection rules covering suspicious process execution, sensitive file access, anomalous network connections, and container escape patterns Automated response actions triggered directly from detection rules Unified real-time dashboard for monitoring Linux servers across cloud, on-premises, and hybrid environments from a single pane of glass Centralized alert storage for long-term forensic analysis, compliance reporting, and incident investigation AI-powered incident summaries with risk trend analysis and actionable remediation recommendations One-click audit-ready Runtime Security PDF reports with full attribution, triggered rules, and remediation details Lightweight single-agent deployment, one Docker command or Helm chart, running in under 5 minutes Supports AWS EC2, EKS, GKE, AKS, bare metal, VMs, and hybrid on-premises Linux workloads
Additional details
Usage instructions
Open the dashboard on http://server-ip:8080 to see live telemetry and report generation for cloud runtime security and generate reports.
Resources
Vendor resources
Support
Vendor support
AWS infrastructure support
AWS Support is a one-on-one, fast-response support channel that is staffed 24x7x365 with experienced and technical support engineers. The service helps customers of all sizes and technical abilities to successfully utilize the products and features provided by Amazon Web Services.
Similar products

