
Overview
Deception Platform Dashboard
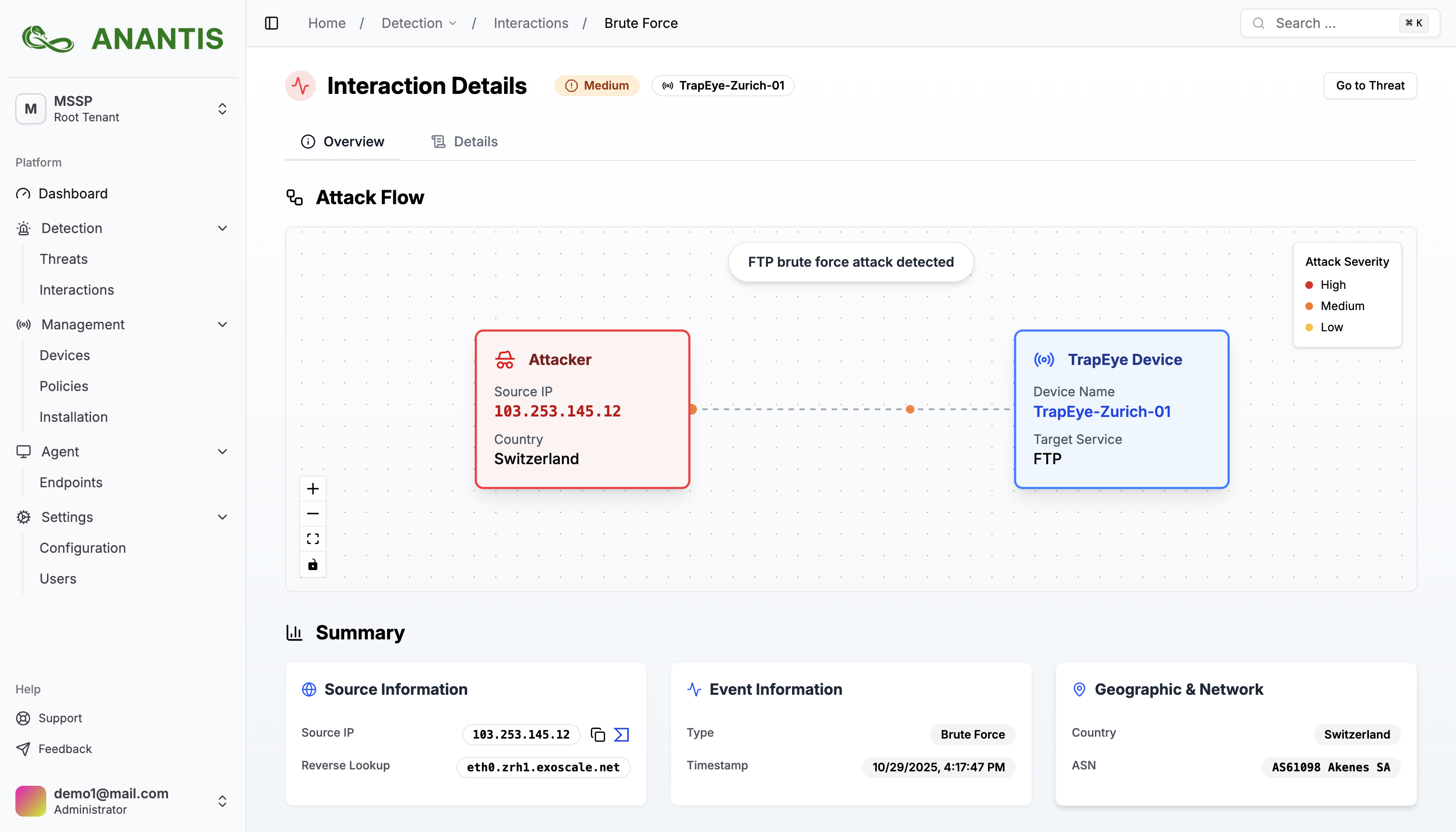
TrapEye by ANANTIS is a next-generation cybersecurity deception platform designed to detect and analyze sophisticated threats through active deception.
By deploying realistic traps, honeypots, and decoy assets, TrapEye detects intruders the moment they interact with the environment, significantly reducing Mean Time to Detect (MTTD).
High-fidelity, deception-based alerts eliminate noise and false positives, providing security teams with actionable intelligence. TrapEye integrates seamlessly with existing SOC workflows and SIEM platforms, and supports deployment across AWS, hybrid, and on-premise environments. Each detected interaction is automatically mapped to the MITRE ATT&CK® framework, giving analysts clear visibility into attacker tactics and techniques.
TrapEye appliances can be deployed in minutes via AWS AMI and securely connect to the TrapEye SaaS management console for centralized monitoring, analytics, and alerting. The SaaS platform is hosted in Switzerland under Swiss jurisdiction, ensuring strong data protection and regulatory compliance.
TrapEye follows a Bring Your Own License (BYOL) model. A valid TrapEye subscription is required to activate and manage deployed appliances.
Learn more: https://anantis.io
Highlights
- Real-time deception-based intrusion detection using honeypots and decoy assets with near-zero false positives.
- Deploy in minutes via AWS AMI + SaaS to protect AWS, hybrid, and on-premise environments with a single deception platform.
- Reduce MTTD dramatically by exposing lateral movement and attacker activity at first interaction.
Details
Introducing multi-product solutions
You can now purchase comprehensive solutions tailored to use cases and industries.

Features and programs
Financing for AWS Marketplace purchases

Pricing
Vendor refund policy
License and refund policies are governed by your agreement with Anantis.
How can we make this page better?

Legal
Vendor terms and conditions
Content disclaimer
Delivery details
64-bit (x86) Amazon Machine Image (AMI)
Amazon Machine Image (AMI)
An AMI is a virtual image that provides the information required to launch an instance. Amazon EC2 (Elastic Compute Cloud) instances are virtual servers on which you can run your applications and workloads, offering varying combinations of CPU, memory, storage, and networking resources. You can launch as many instances from as many different AMIs as you need.
Version release notes
Additional details
Usage instructions
Resources
Vendor resources
Support
Vendor support
Support is provided via email with responses within 24 hours. Our team offers guidance on setup, deployment, and troubleshooting.
AWS infrastructure support
AWS Support is a one-on-one, fast-response support channel that is staffed 24x7x365 with experienced and technical support engineers. The service helps customers of all sizes and technical abilities to successfully utilize the products and features provided by Amazon Web Services.
Customer reviews
Early threat detection has reduced noise and provides high‑value alerts for our SOC
What is our primary use case?
We deployed TrapEye to add an early detection layer focused on internal reconnaissance and lateral movement across our hybrid infrastructure. The goal was to detect attackers before they reach critical assets.
How has it helped my organization?
Even in a short period of time, what stood out is the quality of the alerts. With most security tools, I spend time filtering noise. With TrapEye, if there is an alert, it is immediately meaningful. There are no legitimate reasons for someone to interact with a decoy asset, so it becomes a very strong signal. We connected it to our SIEM quickly, and the alerts were usable immediately by the SOC. It complements our EDR and network monitoring stack well.
What is most valuable?
The alerts have a high signal-to-noise ratio, and the deployment is quick and agentless. The interface is clean with centralized visibility, and it integrates easily with the SOC.
For how long have I used the solution?
I have used this solution for 1 month.
Which solution did I use previously and why did I switch?
We did not use previous solutions.
Which other solutions did I evaluate?
We looked at other deception vendors including Alcavio Networks and Thinkst. TrapEye felt more straightforward to deploy and operate, which was important for us.
What other advice do I have?
TrapEye is a solid product with low complexity and high signal.