Amazon Detective features
Why Amazon Detective?
Amazon Detective makes it easier to analyze, investigate, and quickly identify the root cause of potential security issues or suspicious activities. Amazon Detective automatically collects log data from your AWS resources and uses machine learning, statistical analysis, and graph theory to build a linked set of data that enables you to easily conduct faster and more efficient security investigations.
Amazon Detective can analyze trillions of events from multiple data sources such as Amazon Virtual Private Cloud (Amazon VPC) Flow Logs, AWS CloudTrail logs, Amazon Elastic Kubernetes Service (Amazon EKS) audit logs, and security findings from multiple services like Amazon GuardDuty, AWS Security Hub, and more. Detective automatically creates a unified, interactive view of your resources, users, and the interactions between them over time. With this unified view, you can visualize all the details and context in one place to identify the underlying reasons for the findings, drill down into relevant historical activities, and quickly determine the root cause.
Overview
Automatic data collection across all your AWS accounts
Consolidates disparate events into a graph model
Interactive visualizations for efficient investigation
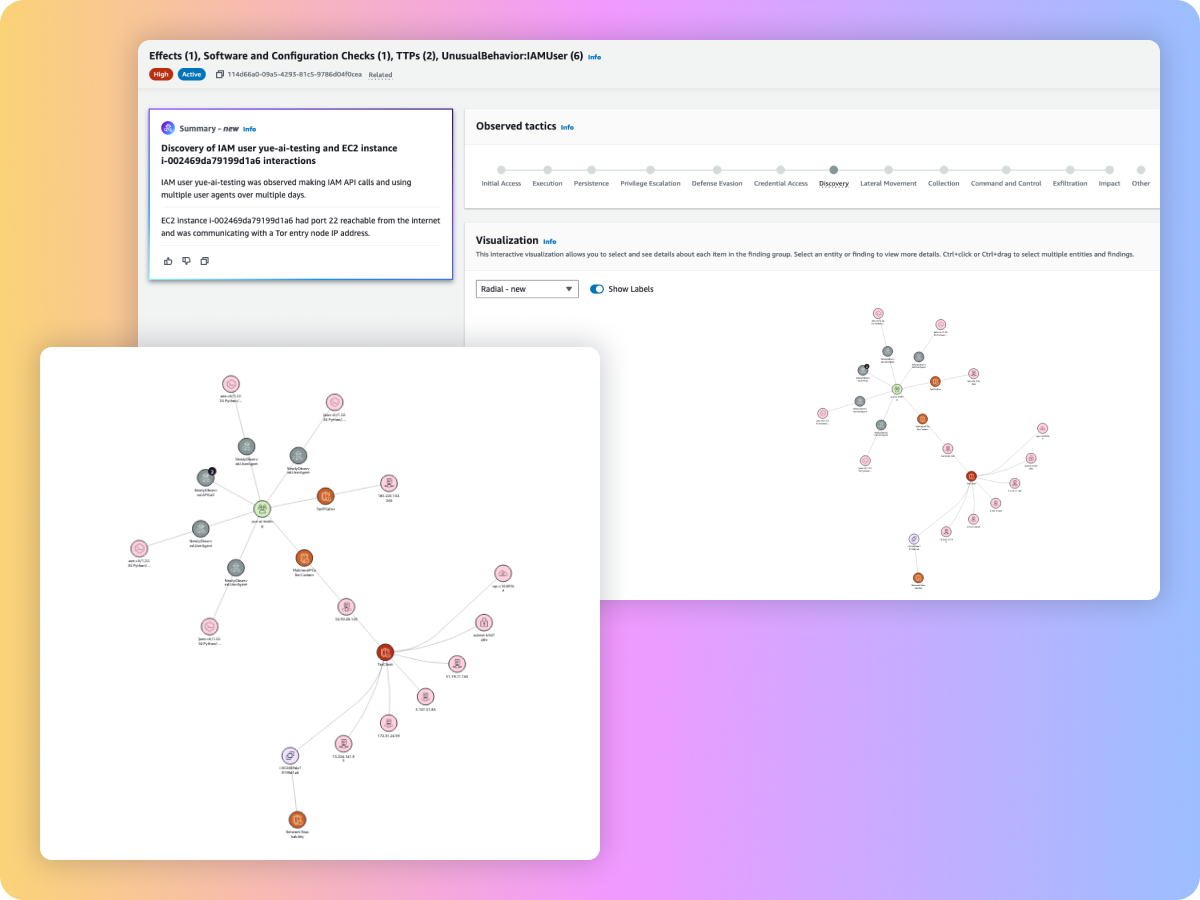
Amazon Detective provides interactive visualizations and insights using generative AI, making it easier to investigate issues faster and more thoroughly with less effort. With a unified view that enables you to visualize all the context and natural language summaries in one place, it becomes more easier to identify patterns that can validate or refute a security issue and understand all of the impacted resources within a security finding. Using these visualizations and insights, you can more easily filter large sets of event data into specific timelines, with all the details, context, and guidance to help you quickly investigate. Amazon Detective enables you to view login attempts by geolocation, drill down into relevant historical activities, and quickly determine a root cause and, if necessary, take action to resolve the issue.
Overall API call volume
The graph visualization shows you related AWS security findings and affected resources from a single security event, such as EC2 instances, IAM roles and users, S3 buckets, and IP addresses. The insights describe the events that took place during the security event in a natural language to help you understand the chain of events. This helps you investigate unusual or suspicious activity more quickly and with less effort. The Overall API call volume shows you successful and failed calls in a specific time period and compares it to the established baseline. This helps you to identify patterns of abnormal activity and validate a security finding.
