
Overview
Maidenhead Bridge Cloud Security Connectors Family
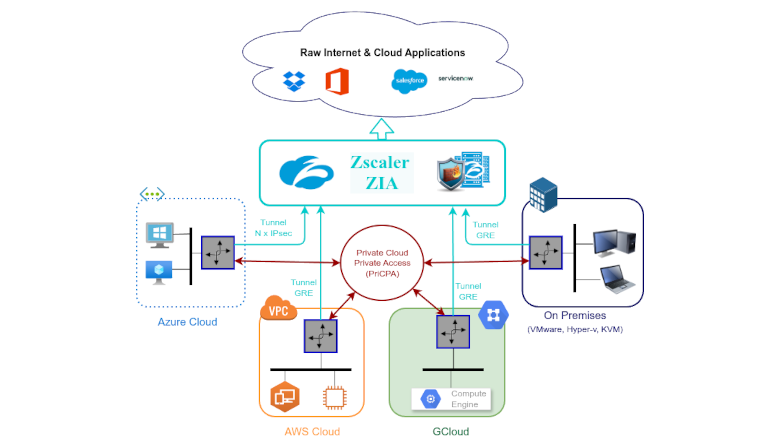
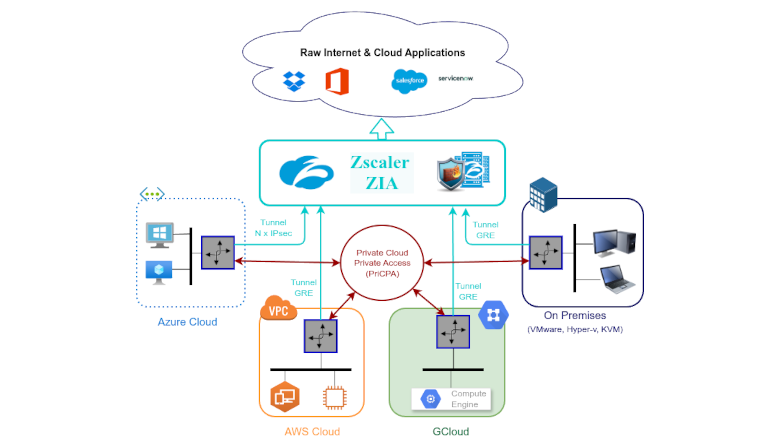
The Maidenhead Bridge Cloud Security Connectors family provides complete protection for Public and Private traffic.
Maidenhead Bridge Cloud Security Connectors Family
The Cloud Security Connector in High Availability
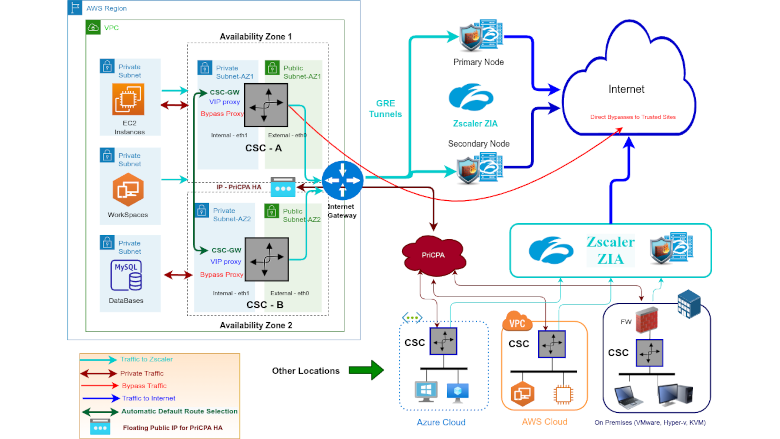
The CSC in Routing Mode using Transit Gateway
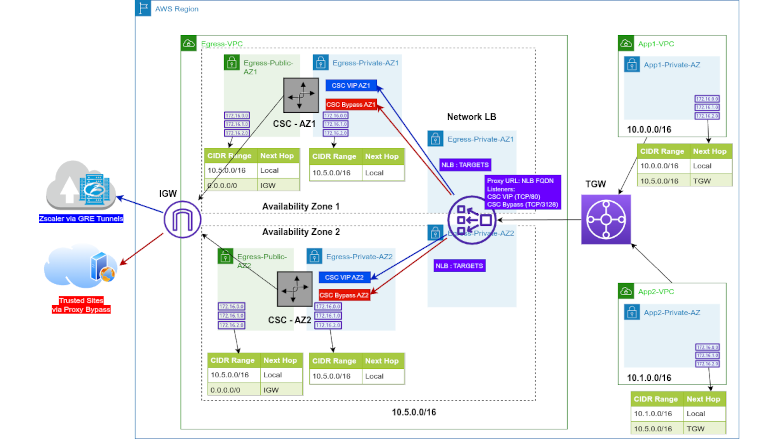
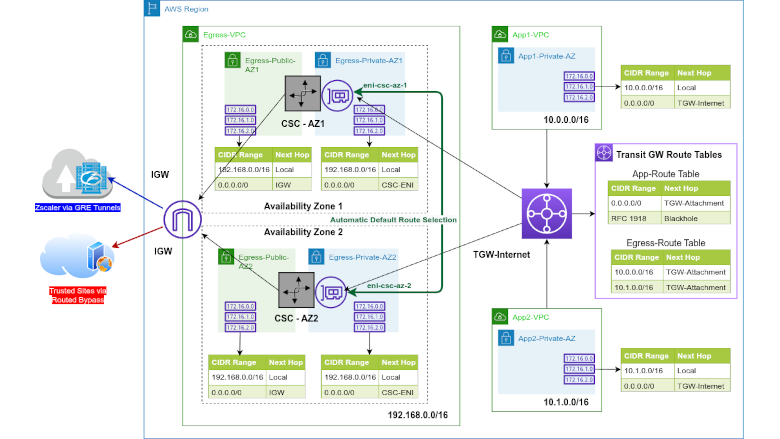
The CSC in Proxy Mode using Transit Gateway

Product video
The Cloud Security Connector (CSC) for AWS is an EC2 instance that connects internal AWS resources to Zscaler Internet Access (ZIA). The CSC for AWS lets you connect securely to Zscaler ZIA up to 3 Gbps without hassle. The primary purpose of the CSC family is simplicity. The CSC for AWS comes with all the configurations required, and it works with the Zscaler API. After launching the CSC from the AWS Marketplace using the CloudFormation template provided, the CSC will automatically select the best ZEN nodes, do the GRE tunnels and create the Location on your Zscaler console. All Zscaler ZIA functionalities are available, providing complete visibility of all Internet traffic. In addition, the CSC provides high availability, changing the default route to Zscaler when configured as a High Availability pair and an easy way to manage direct bypasses to trusted sites using your public IP. Includes Private Cloud Private Access (PriCPA) functionality that allows you to create a full mesh among the CSCs communicating your private traffic on a Zero Trust model. It is simple to install and completely manageable using Amazon Systems Manager, Rundeck (or a similar tool, like Ansible, Salt, etc.), and SSH.
Highlights
- The CSC protects your Public (ZIA) and Private (PriCPA) Traffic.
- The CSC is simple to deploy and fully compliant with Zscaler's best practices.
- The CSC provides automatic detection and configuration of the Zscaler Nodes, automatic default route selection for High Availability and easy Bypass functionality.
Details
Introducing multi-product solutions
You can now purchase comprehensive solutions tailored to use cases and industries.

Features and programs
Buyer guide

Financing for AWS Marketplace purchases

Pricing
Free trial
Dimension | Cost/hour |
|---|---|
r5.large | $0.18 |
m5n.large | $0.18 |
r5a.xlarge | $0.18 |
m5zn.xlarge | $0.18 |
m5.large | $0.18 |
t2.small | $0.18 |
t3.small | $0.18 |
m5a.xlarge | $0.18 |
t3a.small | $0.18 |
t3a.medium | $0.18 |
Vendor refund policy
We do not currently support refunds, but you can cancel at any time.
How can we make this page better?

Legal
Vendor terms and conditions
Content disclaimer
Delivery details
Cloud Security Connector for Zscaler with PriCPA
The Cloud Security Connector (CSC) for AWS is an EC2 instance that connects internal AWS resources to Zscaler Internet Access (ZIA). The CSC for AWS lets you connect securely to Zscaler ZIA up to 3 Gbps without hassle. The primary purpose of the CSC family is simplicity. The CSC for AWS comes with all the configurations required, and it works with the Zscaler API. After launching the CSC from the AWS Marketplace using the CloudFormation template provided, the CSC will automatically select the best ZEN nodes, do the GRE tunnels and create the Location on your Zscaler console. All Zscaler ZIA functionalities are available, providing complete visibility of all Internet traffic. In addition, the CSC provides high availability, changing the default route to Zscaler when configured as a High Availability pair and an easy way to manage direct bypasses to trusted sites using your public IP. Includes Private Cloud Private Access (PriCPA) functionality that allows you to create a full mesh among the CSCs communicating your private traffic on a Zero Trust model. It is simple to install and completely manageable using Amazon Systems Manager, Rundeck (or a similar tool, like Ansible, Salt, etc.), and SSH
CloudFormation Template (CFT)
AWS CloudFormation templates are JSON or YAML-formatted text files that simplify provisioning and management on AWS. The templates describe the service or application architecture you want to deploy, and AWS CloudFormation uses those templates to provision and configure the required services (such as Amazon EC2 instances or Amazon RDS DB instances). The deployed application and associated resources are called a "stack."
Version release notes
Additional details
Usage instructions
Access the Cloud Security Connector configuration console via SSH to the first IP of the internal interface (eth1, labelled: csc-gre-single-internal-interface), using your SSH key and the user: "cscadmin". Example: ssh -i <yourkey.pem> cscadmin@<eth1 IP> . All Configuration and Monitoring tools are available via menu selection. Alternatively, if you deployed the CSC passing UserData values and registering the SSM Agent, you can check the status "Running Commands" from AWS Systems Manager.
Resources
Vendor resources
Support
Vendor support
We provide support for all our customers via Support Portal. Our response time is usually less than 24 hrs. Support Portal page: http://support.maidenheadbridge.com , Support Email: support@maidenheadbridge.com
AWS infrastructure support
AWS Support is a one-on-one, fast-response support channel that is staffed 24x7x365 with experienced and technical support engineers. The service helps customers of all sizes and technical abilities to successfully utilize the products and features provided by Amazon Web Services.



Standard contract
Customer reviews
Zero trust connectivity has simplified multi cloud security and has unified workload protection
What is our primary use case?
My main use case for Cloud Security Connector for Zscaler is that it provides security as a cloud connectivity security service that extends Zscaler Internet Access and Private Access to cloud-native workloads across AWS , Azure , and GCP . It is designed to secure workload-to-internet, workload-to-SaaS, and workload-to-private app communication without relying on traditional VPN, cloud firewall, or complex routing models.
One specific example of how I use Cloud Security Connector for Zscaler in my environment is that it secures cloud workload traffic and gives zero-trust connectivity across AWS , Azure , GCP , and on-prem environments without depending on legacy VPN or firewall-heavy design. This is the main use case of Cloud Security Connector for Zscaler.
The product has its own feature set, starting with extended ZIA and ZPA to cloud workloads, secure internet-bound traffic from workloads, enable app-to-app or app-to-private access connectivity using Zero Trust Exchange, and support AWS, Azure, and GCP deployment.
How has it helped my organization?
Cloud Security Connector for Zscaler has positively impacted my organization by improving the ROI side, as it reduced tool and architecture complexity because it can replace or reduce dependence on VPN, virtual firewall, NAT, proxy tools, and other similar solutions. That impact is approximately a 20 to 30% reduction in cloud networking and security operation center efforts. Additionally, faster multi-cloud deployment, automation support, and official deployment templates help reduce rollout effort compared with building infrastructure from scratch. Furthermore, it provides better policy consistency across the cloud environment, improved visibility for SOC, and reduced risk from overexposed cloud connectivity.
The 20 to 30% reduction is an improvement in monitoring efficiency and is a reasonable estimate where my team currently depends on separate cloud-native logs and manual correlation from an effort perspective. From an example perspective, a SOC team can investigate workload access and egress behavior faster when logs are normalized and streamed centrally.
What is most valuable?
The best features Cloud Security Connector for Zscaler offers include extended ZIA and ZPA to cloud workloads, secure internet inbound traffic from workloads with capabilities such as SSL inspection, IPS, firewall control, and DLP by ZIA. It enables app-to-app and app-to-private access connectivity using Zero Trust Exchange, including multi-cloud and hybrid cloud use cases. It supports AWS, Azure, and GCP deployment and includes centralized policy and visibility, automated orchestrated deployment support, Azure Resource Manager , and a highly scalable architecture.
Out of those features, I find the strong zero-trust approach for cloud workloads to be the most valuable day-to-day because Cloud Security Connector for Zscaler is designed around zero-trust connectivity, not legacy network extension. It provides inside-out connections through Zscaler Zero Trust Exchange, which reduces exposure and avoids broad network-level access. For example, a workload in AWS can securely connect to a private application in Azure through Zscaler policy controls without building site-to-site VPNs or opening large network paths. This is a good replacement for legacy cloud networking components. Cloud Security Connector for Zscaler positions itself as a simple alternative to legacy cloud VPN, virtual firewall routers, proxy NATs, and other tools. This is a strong advantage for organizations trying to reduce architecture complexity.
What needs improvement?
Cloud Security Connector for Zscaler can be improved because I find it relies on a VM-based connector model. While Cloud Security Connector for Zscaler simplifies traffic forwarding, it is still based on deploying virtual machine instances in a cloud. Some organizations prefer a fully agentless or native-embedded cloud solution. The best value comes when you already use the Zscaler ecosystem, so if you have anything other than the Zscaler ecosystem, it may not work optimally. It is tightly coupled with the Zscaler ecosystem, which is one drawback. Additionally, the learning curve for design and traffic steering is required because it supports several use cases including internet egress, private app access, and multi-cloud connectivity.
Another aspect I could mention is that executive reporting could be more business-focused, as that area is currently lagging.
For how long have I used the solution?
I have been using Cloud Security Connector for Zscaler for the last five years.
What do I think about the stability of the solution?
Cloud Security Connector for Zscaler is stable.
What do I think about the scalability of the solution?
Its scalability is good and it is highly scalable. Based on your requirement, you could go with either one cloud connector or two, which will depend on the criticality of your application.
How are customer service and support?
The customer support for Cloud Security Connector for Zscaler is good.
Which solution did I use previously and why did I switch?
Before choosing Cloud Security Connector for Zscaler, I have not evaluated any other option in terms of Cloud Connector, but I have worked on Netskope as well.
How was the initial setup?
My experience with pricing, setup cost, and licensing for Cloud Security Connector for Zscaler is good because whoever is buying Zscaler purchases it from an ecosystem perspective, so I do not have any other choice in that regard.
What about the implementation team?
I did not purchase Cloud Security Connector for Zscaler through the AWS Marketplace ; it is from a partner.
What was our ROI?
I have seen a return on investment from this solution, and I have already shared those details.
What's my experience with pricing, setup cost, and licensing?
My experience with pricing, setup cost, and licensing for Cloud Security Connector for Zscaler is good because whoever is buying Zscaler purchases it from an ecosystem perspective, so I do not have any other choice in that regard.
Which other solutions did I evaluate?
It is not about using a different solution for me. I am a customer support executive, so I need to support different customers and solutions. Based on the customer requirement, I give them different solutions. Sometimes it is Zscaler and sometimes it is Netskope . It is not about switching one solution to another solution for me.
What other advice do I have?
While I do not have a surprise, I think others should know that consistent security policy across cloud and user is one of the most top use cases along with multi-cloud and hybrid cloud flexibility.
My advice to others looking into using Cloud Security Connector for Zscaler is that it is all about the Zscaler ecosystem. Whoever is using Zscaler knows Cloud Security Connector for Zscaler's importance, and they could use it from a centralized connectivity perspective. I have given this product a review rating of 10.
Which deployment model are you using for this solution?
If public cloud, private cloud, or hybrid cloud, which cloud provider do you use?
Secure access to sensitive financial data has improved and now protects confidential recipes
What is our primary use case?
I am mostly using Cloud Security Connector for Zscaler as a VPN only. If I want to access any company-related web apps, I am using Cloud Security Connector for Zscaler for connection so that I do not want any third party to access my web apps. To explain how it works, consider that we are developing a web app which will hold financial-level information. On the organizational level, we do not want any of our competitor companies to access our web app even though they know the web app link. Because anyone can log into a particular web app using the username and password, which can be easily hacked, and they could be able to see our financial-related and recipe information because we are currently working for a CPG-related company. To restrict that, we are hosted in a very secure environment. To access our web app in that particular secure environment, we either need to connect to our office email or if I am accessing from home while working from home, I need some VPN to get connected. That is why instead of connecting to any third-party VPN, we have Cloud Security Connector for Zscaler, which enables us to connect. The main use case is to restrict any other third-party persons from accessing our recipe-level information or financial-level information. We are using Cloud Security Connector for Zscaler as a VPN so that we can be able to access the app securely.
What is most valuable?
The best features Cloud Security Connector for Zscaler offers are that even in our secure environment, we have a different region hosted, such as US and UK. Before that, we were using some private VPN, so we needed a US VPN separately and UK VPN separately. But now after using Cloud Security Connector for Zscaler, which becomes a centralized VPN, we are able to access the US-hosted app as well as UK-hosted app so that we can bypass using different VPNs for different regions. That is the main use case.
Regarding ease of use, to connect to Cloud Security Connector for Zscaler, we need our org ID. Whenever we are authenticating using our org ID, it is easy to connect to Cloud Security Connector for Zscaler. It is pretty handy and user-friendly. Once it is connected, we can be able to access all the apps which are hosted inside our private environment.
Cloud Security Connector for Zscaler has positively impacted my organization. Previously, as I mentioned, we needed to connect to VPN every time separately. But now whenever we log into our VDI , we can connect to the VPN by pre-default because Cloud Security Connector for Zscaler is already installed. Once it is already installed, we can access our apps directly without connecting to the VPN. Because of this, we are saving approximately 5 to 10 minutes of time, so that increases our productivity and screen time. If I want to access some information quickly, before it would take time because I would need to connect to VPN and open the app. But now because Cloud Security Connector for Zscaler is pre-defaultly connected, I do not need to connect to any private VPN separately, so it reduces my time.
Previously, if a particular task was taking 10 minutes, now it is significantly reduced to two to three minutes only. We saved seven minutes of time in each and every task. It is actually an improvement.
What needs improvement?
Every improvement is already done on Cloud Security Connector for Zscaler. We do not need any improvement on Cloud Security Connector for Zscaler because to be honest, I did not see any flaw on this. It is already working well. However, whenever I turn on or turn off and turn on my VDI , every time while opening, it will ask me to sign into Cloud Security Connector for Zscaler. If you make the login pre-defaultly available in Cloud Security Connector for Zscaler, such as one-time login is permitted, then it will be easy for me to access Cloud Security Connector for Zscaler. Other than that, I am not seeing any flaw. It is already good.
For how long have I used the solution?
I have been using Cloud Security Connector for Zscaler for the past one year.
What do I think about the stability of the solution?
Cloud Security Connector for Zscaler is stable.
What do I think about the scalability of the solution?
Cloud Security Connector for Zscaler's scalability is good. It can handle growth and changes. It is very easy to scale also, and it is good.
How are customer service and support?
I did not interact with customer support because I did not face any issues till now. Maybe if I get the chance, I will.
Which solution did I use previously and why did I switch?
Previously, I used Trellix as my solution. But now I changed to Cloud Security Connector for Zscaler because of its pricing.
How was the initial setup?
Security-wise, Cloud Security Connector for Zscaler is good. As I mentioned, I am mainly using Cloud Security Connector for Zscaler for security only. Governance-wise, it is also good and it is easy to set up. It is pretty easy.
What was our ROI?
I will say return on investment as time saved. It is saved from 10 minutes to three minutes now. I saved seven minutes on each task.
What's my experience with pricing, setup cost, and licensing?
My experience with pricing, setup cost, and licensing is that it is handled by my organization only, so I do not know the pricing and setup cost. But I think it is very less compared to other systems.
Which other solutions did I evaluate?
I did not evaluate any other options before choosing Cloud Security Connector for Zscaler.
What other advice do I have?
My advice to others looking into using Cloud Security Connector for Zscaler is to definitely go with Cloud Security Connector for Zscaler. It is a good security connector. I would rate this product a 9 out of 10.
Secure access to internal web apps has been ensured through strict identity-based VPN control
What is our primary use case?
My main use case for Cloud Security Connector for Zscaler is to use it as a VPN. Instead of directly connecting to a separate VPN link, I connect to Cloud Security Connector for Zscaler , which acts as a VPN so that whenever I have a web app hosted in a firewall, I can access that particular web app via Cloud Security Connector for Zscaler only. I cannot access it using other networks.
This setup has worked well for me because my company has a different environment called DNA. Whenever a web app or any other resources in Azure are hosted inside that DNA, I need to use or connect to Cloud Security Connector for Zscaler to access that particular resource. Cloud Security Connector for Zscaler acts as a VPN, so only users with a particular company ID can access that resource. No third party can access it. Even if I try to access the web app using my personal laptop or mobile phone, I cannot access it. I can only access those particular web apps and other resources like Key Vault inside Azure using Cloud Security Connector for Zscaler on my company's laptop only.
I find Cloud Security Connector for Zscaler pretty useful for my main use case on a day-to-day basis because it really helps us as a security firewall. I do not want any other third-party companies or competitor companies to access my web app and see what I have developed. I need to keep it secure and do not want other companies to copy my web app or see the confidential information available in my web app. Cloud Security Connector for Zscaler is pretty useful while connecting.
What is most valuable?
The best features that Cloud Security Connector for Zscaler offers include a great login feature because I cannot log into Cloud Security Connector for Zscaler without my company's ID, and it requires Okta verification. It is pretty easy and safe as well. No other person can access Cloud Security Connector for Zscaler on their laptop because it has some separate code to log in and log out, which is provided by the administrator only. Security-wise, Cloud Security Connector for Zscaler is very helpful.
Cloud Security Connector for Zscaler has positively impacted our organization in securing a lot. Previously, there were many security issues. Before using Cloud Security Connector for Zscaler, around five percent of security breaches happened without our notice. Thankfully, our client noticed these breaches and found them before they became problematic. We wanted to ensure it does not happen in the future, which is why we moved to Cloud Security Connector for Zscaler. Everything is good, and it has been working well. From a security perspective, everything is good in Cloud Security Connector for Zscaler, and our organization is mostly relying on Cloud Security Connector for Zscaler to safeguard everything.
What needs improvement?
One thing we can improve regarding Cloud Security Connector for Zscaler is that every time I log into my laptop, it asks me to sign in to Cloud Security Connector for Zscaler again and again. Perhaps we could change that login feature to reset once a month, but currently it resets every day. That is the one feature I feel can be improved; everything else is good.
I do not need any other improvement currently; everything is good aside from the login issue. I am okay with other things.
For how long have I used the solution?
I have been using Cloud Security Connector for Zscaler for the past one year.
What do I think about the stability of the solution?
Cloud Security Connector for Zscaler is stable; sometimes there is downtime, but not every time. That obviously happens with every cloud security platform. Compared to Trellix, we have not faced much downtime with Cloud Security Connector for Zscaler, so it is generally okay. The team can look into the downtime issue.
What do I think about the scalability of the solution?
Cloud Security Connector for Zscaler's scalability is good because we are currently handling Cloud Security Connector for Zscaler connections to multiple regions, so scaling-wise, it is working well.
How are customer service and support?
The customer support for Cloud Security Connector for Zscaler is pretty good. Whenever I have issues and raise a concern, they resolve it within two or three hours.
Which solution did I use previously and why did I switch?
We previously used a private VPN, but instead of using it, we are now directly connecting to Cloud Security Connector for Zscaler. We switched because we needed to connect to a VPN every time, and it was taking more time to connect. Cloud Security Connector for Zscaler, being on-premises and organization-level, offers more security compared to accessing the private VPN. Thus, we switched to Cloud Security Connector for Zscaler.
What was our ROI?
I do not have much information about return on investment, but from a time saved perspective, previously when we wanted to access apps securely, we needed to connect to a VPN, which took around two minutes to connect. Now, with Cloud Security Connector for Zscaler, we do it in about thirty seconds, which shows significant time saved.
What's my experience with pricing, setup cost, and licensing?
I do not have any idea about pricing because it is handled by the organization, but as far as I know, the cost of Cloud Security Connector for Zscaler is similar to other security cloud platforms. Cost-wise, there is no difference, but protection-wise, Cloud Security Connector for Zscaler is very good.
Which other solutions did I evaluate?
We evaluated something called Trellix before choosing Cloud Security Connector for Zscaler, but compared to Trellix, Cloud Security Connector for Zscaler is better, which is why we switched to Cloud Security Connector for Zscaler.
What other advice do I have?
I rate Cloud Security Connector for Zscaler a nine out of ten. I reduce that one point because of the login feature only; otherwise, everything is good. From a security protection perspective, Cloud Security Connector for Zscaler plays a major role, so I am giving it a nine.
I choose nine specifically because, as I mentioned, aside from the login feature, the rest is good. From a security perspective, Cloud Security Connector for Zscaler is very good.
My advice for others looking into Cloud Security Connector for Zscaler is that it is the perfect cloud security system. If you have other options in mind, you should definitely give Cloud Security Connector for Zscaler a try because it is good. I have been using it for the past year. Even though I sometimes face downtime or other issues such as multiple login attempts, I still feel that from a security perspective, Cloud Security Connector for Zscaler is good, so proceed with it.
Unified cloud policies have improved zero-trust controls and simplified workload monitoring
What is our primary use case?
Cloud Security Connector for Zscaler securely routes traffic from cloud workloads, such as applications running in AWS or Azure , through the Zscaler cloud for inspection and policy enforcement. In a traditional setup, Zscaler is primarily used for user traffic, but with Cloud Security Connector for Zscaler , the same security controls extend to server-side or workload traffic inside the cloud environment. For example, if application servers in an AWS VPC require internet access, instead of allowing direct outbound access, that traffic routes through Cloud Security Connector for Zscaler into Zscaler. This ensures that all traffic is inspected for threats, URL filtering policies are applied, and data protection controls are enforced. Another important use case is for east-west and server-to-internet communication, where visibility and control over workload behavior is desired, especially for compliance in industries such as banking or finance. Cloud Security Connector for Zscaler also helps maintain a consistent security posture across users and workloads since both are governed by Zscaler policies. Overall, Cloud Security Connector for Zscaler enables a zero-trust approach for cloud workloads by eliminating direct internet exposure and ensuring all traffic is inspected through Zscaler.
A specific example from a banking client involved application servers hosted in AWS that required outbound internet access for updates and API communication. Initially, these servers had direct internet access through the NAT gateway, which created a visibility and security gap since the traffic was not being inspected or controlled centrally. To address this, Cloud Security Connector for Zscaler was implemented in the AWS environment. Routing was configured so that all outbound traffic from the application subnet was redirected through Cloud Security Connector for Zscaler into the Zscaler cloud. Once integrated, Zscaler policies such as URL filtering, SSL inspection, and threat protection were applied to the workload traffic. This ensured that even server-to-internet communication was fully inspected, similar to user traffic. As a result, centralized visibility and control were achieved, the risk of malicious outbound connections was reduced, and the environment was aligned with compliance requirements such as PCI DSS. Additionally, the architecture was simplified by removing the need for additional proxy or firewall appliances in the cloud.
Apart from outbound workload protection, Cloud Security Connector for Zscaler adds value in controlling traffic in microservices architecture, where applications often communicate with external APIs or third-party services. Using Cloud Security Connector for Zscaler, this traffic is routed through Zscaler for inspection, which helps detect any malicious behavior or potential data exfiltration attempts. Another important use case is enforcing consistent security policies across both users and workloads. Instead of having separate security controls for endpoints and cloud servers, Cloud Security Connector for Zscaler allows unified policies to be applied through Zscaler, which improves visibility and simplifies management. Cloud Security Connector for Zscaler also plays a key role in compliance-driven environments, especially in banking and finance, where monitoring and logging all outbound traffic is mandatory for audit purposes. Overall, Cloud Security Connector for Zscaler extends zero-trust principles beyond users to cloud workloads, ensuring that no traffic is trusted by default and everything is verified and inspected.
What is most valuable?
The most valuable features of Cloud Security Connector for Zscaler include centralized visibility and control. It allows routing of all cloud workload traffic through Zscaler, which means full visibility into what applications and servers access externally. This is very critical in banking environments where audit and monitoring are mandatory. The second key feature is unified policy management. Instead of managing separate security controls for users and cloud workloads, the same Zscaler policies such as URL filtering, SSL inspection, and threat protection can be applied across both. This simplifies operations and ensures a consistent security posture. Another important aspect is the ease of integration with cloud security environments such as AWS and Azure , without needing traditional firewall appliances, which reduces complexity and improves scalability.
These features make a significant impact on day-to-day operations, especially in terms of visibility, troubleshooting, and policy management. With centralized visibility, instead of checking multiple tools or cloud logs, all cloud workload traffic can be directly viewed in Zscaler logs. This makes troubleshooting much faster when users or applications report issues because it is possible to quickly identify whether traffic is being blocked, allowed, or flagged as suspicious. Unified policy management also simplifies operations since the same policies apply across users and cloud workloads. There is no need to maintain separate rule sets, which reduces configuration errors and makes policy changes much faster and more consistent across the environment. From an operational standpoint, it reduces the dependency on traditional firewalls or proxies in cloud environments, which means less infrastructure to manage, fewer points of failure, and easier scalability. Overall, Cloud Security Connector for Zscaler helps the team be more efficient by reducing troubleshooting time, simplifying policy management, and giving better control and visibility from a single platform.
What needs improvement?
A challenge faced during the initial implementation involved routing and application dependency. After routing cloud workload traffic through Cloud Security Connector for Zscaler, a few applications started failing because they depended on specific external services that were getting blocked due to strict policies or SSL inspection. To resolve this, traffic was analyzed using Zscaler logs, the exact domains and services being impacted were identified, and a controlled policy exception was created while maintaining overall security. This helped strike the right balance between security and application availability, which is very important in production environments. A key learning from this was that while Cloud Security Connector for Zscaler provides strong security control, proper policy tuning and understanding application behavior is critical for smooth deployment.
Cloud Security Connector for Zscaler has had a very positive impact, especially in terms of security and operational efficiency. Before implementation, cloud workloads had direct internet access through the NAT gateway, which limited visibility and control over outbound traffic. After adopting Cloud Security Connector for Zscaler, all traffic was routed through Zscaler, giving centralized visibility and full policy enforcement. One improvement observed was a significant increase in threat detection. The ability to identify and block suspicious outbound connections that were previously not visible improved the overall security posture. From an operational perspective, troubleshooting became much faster. Instead of checking multiple cloud logs, Zscaler logs could be directly used to analyze traffic behavior, which reduced incident resolution time. The dependency on traditional firewall appliances in cloud environments was reduced, which simplified the architecture and lowered operational overhead. Additionally, for compliance-driven clients in banking, it helped meet audit requirements by providing detailed logs and consistent policy enforcement across both users and workloads.
Measurable improvements were observed after implementing Cloud Security Connector for Zscaler. In terms of visibility and threat detection, a 25 to 35 percent increase in identifying suspicious outbound connections was seen that were previously not visible when traffic was going through NAT. From an operational standpoint, troubleshooting time reduced by 45 to 55 percent because Zscaler logs could be directly analyzed instead of checking multiple cloud logs. Dependence on additional security appliances in the cloud was also reduced, which helped lower operational overhead and simplified the architecture. In terms of compliance, better audit readiness was achieved with centralized logging and consistent policy enforcement across workloads and users.
While Cloud Security Connector for Zscaler is a strong solution, one area that could be improved, especially for teams that are new, is configuring route tables, ensuring proper traffic flow, and avoiding asymmetric routing, which can be challenging, particularly in large or multi-VPC environments. More automated deployment options or guided configurations, especially for AWS or Azure, would simplify the onboarding process. Another area for improvement is better visibility at the cloud-native level, such as tighter integration with cloud logs or more context-aware insight for workload behavior, which would make troubleshooting even faster. Once properly implemented, it works efficiently and provides strong security and visibility.
In addition to deployment simplicity, improvements around policy tuning and documentation would add significant value. From a policy perspective, when Zscaler policy is extended to cloud workloads, it sometimes requires careful fine-tuning to avoid impacting application dependency. More predefined templates or workload-specific policy recommendations would help teams implement it faster with fewer disruptions. In terms of documentation, while the existing guides are helpful, more step-by-step real-world deployment examples, especially for multi-VPC or hybrid environments, would make onboarding smoother for teams. Tighter integration guidance with cloud-native tools such as AWS logging or monitoring services would further improve troubleshooting and visibility. From a support standpoint, faster access to best practice recommendations or reference architecture would help teams avoid common misconfigurations during the initial setup.
For how long have I used the solution?
I have around 4.5 years of experience in the cybersecurity domain, primarily working with enterprise customers in the banking and financial sector, and in my current role, I handle end-to-end security operations. Overall, this experience has helped develop strong technical skills and a customer-focused mindset, where I act as a trusted advisor rather than providing support. Over these 4.5 years, strong hands-on experience in cloud security was built, especially with Cloud Security Connector for Zscaler, and work has been done on SSL inspection, traffic forwarding using pack files, policy creation and optimization, troubleshooting user access issues, and improving overall security posture while minimizing false positives.
What do I think about the stability of the solution?
Cloud Security Connector for Zscaler has been quite stable and reliable once properly deployed. There have not been any major downtime or critical issues. Most of the challenges encountered were during the initial setup and routing configuration, but after stabilization, it has been performing consistently, handling workload traffic effectively.
What do I think about the scalability of the solution?
Cloud Security Connector for Zscaler performs very in terms of scalability since it is deployed within the cloud environment. Horizontal scaling is easily achieved by adding more connector instances based on traffic requirements. As workloads grow, routing can be updated and traffic can be distributed across multiple connectors without major architecture changes. Since inspection happens in the Zscaler cloud, there is no need to worry about scaling the security infrastructure separately.
How are customer service and support?
The experience with Zscaler support has been generally positive. For most issues, especially those related to configuration or troubleshooting, timely responses and useful guidance were received. In more complex scenarios such as routing or policy tuning, support provided best practices and recommendations, which made the implementation smoother.
Which solution did I use previously and why did I switch?
Before adopting Cloud Security Connector for Zscaler, the primary approach involved traditional cloud security methods, mainly NAT gateway combined with firewall-based controls for managing outbound traffic from cloud workloads. While this setup worked, it had limitations. Visibility on the outbound traffic was limited and policy enforcement was not centralized. Troubleshooting also required checking multiple tools such as cloud logs and firewall logs, which made operations more complex. Cloud Security Connector for Zscaler was adopted to achieve centralized visibility and consistent policy enforcement through Zscaler. This allowed the same security controls such as URL filtering, SSL inspection, and threat protection to be applied to both users and cloud workloads. The switch was primarily driven by the need for a zero-trust approach, better visibility, and reduced dependency on traditional firewall infrastructure in the cloud.
How was the initial setup?
The primary factor regarding initial setup is deployment and routing complexity, especially in larger or multi-VPC environments where ensuring correct traffic flow and avoiding asymmetric routing can take considerable effort. Another aspect is policy tuning for cloud workloads. Since application servers may have specific dependencies, it requires careful fine-tuning of policies and SSL inspection to avoid impacting functionality during the initial rollout. Additionally, while the platform provides good visibility, having more cloud-native context and tighter integration with services such as AWS monitoring tools would further enhance troubleshooting and insights. These challenges are mainly around initial setup and optimization. Once implemented properly, the solution works effectively and delivers strong security and visibility.
What about the implementation team?
Before finalizing Cloud Security Connector for Zscaler, a few other approaches were evaluated, mainly traditional firewall-based solutions in the cloud and native cloud controls such as AWS security services. While those options provide basic security, they lack centralized visibility and unified policy enforcement across both users and workloads. Managing multiple tools can also increase operational complexity. Cloud Security Connector for Zscaler stood out because it allowed the same security policies to be extended to cloud workloads, giving a more consistent and scalable zero-trust approach. In terms of stability, Cloud Security Connector for Zscaler has been quite stable and reliable once properly deployed. There have not been any major downtime or critical issues. Most of the challenges encountered were during the initial setup and routing configuration, but after stabilization, it has been performing consistently, handling workload traffic effectively.
What was our ROI?
A return on investment has been observed, especially in terms of time savings, operational efficiency, and improved security visibility. For example, incident troubleshooting time reduced by 35 to 45 percent because Zscaler logs could be directly used instead of correlating multiple cloud and firewall logs. The need for managing additional firewall or proxy infrastructure in the cloud was also reduced, which helped lower operational overhead and reduce support burden on the team. From a security standpoint, around 25 to 30 percent improvement was seen in detecting and blocking suspicious outbound traffic, which reduced potential risk and manual investigation efforts. Overall, while it did not necessarily reduce headcount, it significantly improved team efficiency, allowing more workloads to be handled with the same team and enabling faster incident response.
What's my experience with pricing, setup cost, and licensing?
In terms of additional improvements, one small enhancement would be having more predefined policy templates for common cloud workload use cases, which would make initial policy tuning faster and reduce dependency on manual configuration. Regarding pricing and licensing, Cloud Security Connector for Zscaler was part of the overall Zscaler enterprise licensing, so it was more of a bundled approach rather than a separate purchase. From a setup perspective, there was not a significant additional cost beyond the cloud infrastructure itself, such as compute resources in AWS. The value comes from the security capabilities it adds rather than from the licensing component. Overall, while pricing depends on the enterprise agreement, the solution delivers good value considering the visibility, control, and security it provides.
Which other solutions did I evaluate?
Before finalizing Cloud Security Connector for Zscaler, a few other approaches were evaluated, mainly traditional firewall-based solutions in the cloud and native cloud controls such as AWS security services. While those options provide basic security, they lack centralized visibility and unified policy enforcement across both users and workloads. Managing multiple tools can also increase operational complexity. Cloud Security Connector for Zscaler stood out because it allowed the same security policies to be extended to cloud workloads, giving a more consistent and scalable zero-trust approach.
What other advice do I have?
Organizations should plan the deployment carefully, especially around routing and network design. Understanding the traffic flow and dependencies upfront helps avoid issues later. It is important to start with a phased rollout and proper policy tuning rather than enabling stricter policies immediately. This ensures minimal impact on applications while maintaining security. This review has been given an overall rating of 8.
Which deployment model are you using for this solution?
If public cloud, private cloud, or hybrid cloud, which cloud provider do you use?
Addressed complex learning curve yet has improved automated routing and cloud security visibility
What is our primary use case?
In our current organization, we have been using Cloud Security Connector for Zscaler by Maiden Edge, Maidenhead Bridge for almost two and a half years. They are providing us specialized virtual appliances to simplify and secure connectivity between cloud environments. For our case, this involves AWS and Zscaler Internet Access , with a focus on zero trust and high availability, and it also helps with performance enhancement.
Our main use case for Cloud Security Connector for Zscaler is that we have been using it as a pre-configured virtual machine that we deploy on our AWS system with minimal networking requirements. This connector helps us automate Zscaler node detection and route selection, which reduces the manual configuration and operational burden for our organization's administrators. Management is quite straightforward through it being available with SSH and AWS System Manager. The appliance also includes built-in utilities for traffic monitoring and troubleshooting and log export to syslog. Our day-to-day use case is primarily that it helps us automate Zscaler node detection and route selection.
Automating node detection and route selection has helped us reduce the number of errors we were getting and made Zscaler more reliable and less dependent on Zscaler directly. Before using this solution with Zscaler, the Zscaler used to malfunction frequently, impacting our productivity. After implementing Cloud Security Connector for Zscaler along with Zscaler, we have seen positive effects, saving time as well as resources, which has left a very good impression on us.
How has it helped my organization?
Cloud Security Connector for Zscaler has positively impacted our organization by helping us in our cloud environment to connect our resources to Zscaler, ensuring that security policies are consistent with zero-trust access and increasing reliability by 28%. It has also helped us with site-to-cloud networking at high performance, optimizing performance and reducing the bottlenecks of cloud connectivity, saving resources and time by at least 78%. Additionally, it has automated workloads using Cloud Security Connector for Zscaler's high availability and ensured that connectivity is uninterrupted to Zscaler, even during network outages or maintenance.
What is most valuable?
Cloud Security Connector for Zscaler offers multiple features, but the major feature I love specifically is automated Zscaler node detection, which helps detect any kind of problem first. Additionally, it is available all the time, providing high availability routing for seamless failover, which is one of my favorite features. It also provides Layer 4 routed bypass for TCP, UDP, and ICMP traffic, enabling granular traffic control that streamlines our services working with Zscaler. It has provided complete visibility of internal IPs on the Zscaler console, allowing us to monitor and troubleshoot whenever there is a problem, making things transparent and easy for us to monitor. The integration with SIEM or syslog enhances centralized log management for our organization.
What needs improvement?
I feel that they are doing great with Cloud Security Connector for Zscaler. If I need to suggest an improvement, it would be to simplify the steep learning curve, as it can be complex for newcomers without prior experience. Apart from that, I did not face any challenges with them in these two and a half years.
For how long have I used the solution?
I have been working in my current field for almost 10 years.
What do I think about the scalability of the solution?
Cloud Security Connector for Zscaler's scalability is definitely impressive, as it has handled growth and changes in our organization well. Whenever we have increased our employees and the number of users, it has contributed positively to our growth without any scalability issues.
How are customer service and support?
We reached out to customer support three weeks back due to an issue where Zscaler got stuck, and they identified and solved the problem within 45 minutes, which is exceptional. I give them a 10 out of 10 for customer support.
How would you rate customer service and support?
Positive
How was the initial setup?
The deployment of Cloud Security Connector for Zscaler in our environment is very straightforward with the option to pass configuration parameters via user data during initial setup. The connector integrates seamlessly with cloud-native services, in our case AWS, and it also works with load balancers, firewalls, and monitoring solutions, making the deployment straightforward and easy, with no challenges I remember in our organization.
The configuration process for Cloud Security Connector for Zscaler is excellent. We did not encounter any challenges, and it was very smooth. Even if it is complex, the team is always there to help, and customer service is excellent—always there to assist with deployment or configuration challenges.
What was our ROI?
We have definitely seen a return on investment with Cloud Security Connector for Zscaler, saving us money by at least 20 to 25%. In terms of time, we have saved at least 22 to 25% related to security and automation. The employees have become more productive and focused on the right direction.
What's my experience with pricing, setup cost, and licensing?
The experience with pricing, setup cost, and licensing for Cloud Security Connector for Zscaler is definitely competitive. They provide us a good cost, and since we obtained it through AWS Marketplace , we are well supported in this area.
Which other solutions did I evaluate?
We did not use a different solution, but we have evaluated some alternatives, including Fortinet SASE , Cisco Umbrella , Netskope Security Cloud, and Palo Alto Networks Prisma Access .
Before choosing Cloud Security Connector for Zscaler, we definitely evaluated other options and looked at several solutions. We chose Cloud Security Connector for Zscaler because it is a scalable solution. Increasing the number of seats or users did not show any signs of crashing or lagging.
What other advice do I have?
One more thing I want to mention is the built-in tools for testing and troubleshooting, which include traffic logs, TCP dump, speed test, and MTR.
Everything else is good. The user interface is very attractive and does not require any change.
If you are looking into using Cloud Security Connector for Zscaler, I recommend it highly if you are committed to Zscaler and want a very simple automated GRE and IP routing from Azure , AWS, or GCP, without having to manage tunnels or custom NVA designs yourself.
Cloud Security Connector for Zscaler is a good solution that can help your Zscaler work better and secure your environment more effectively. It can also integrate with multiple cloud platforms like Azure , AWS, and GCP, making it a must-have solution for organizations based on my observation. I provide this review with an overall rating of 4 out of 5.