
Overview
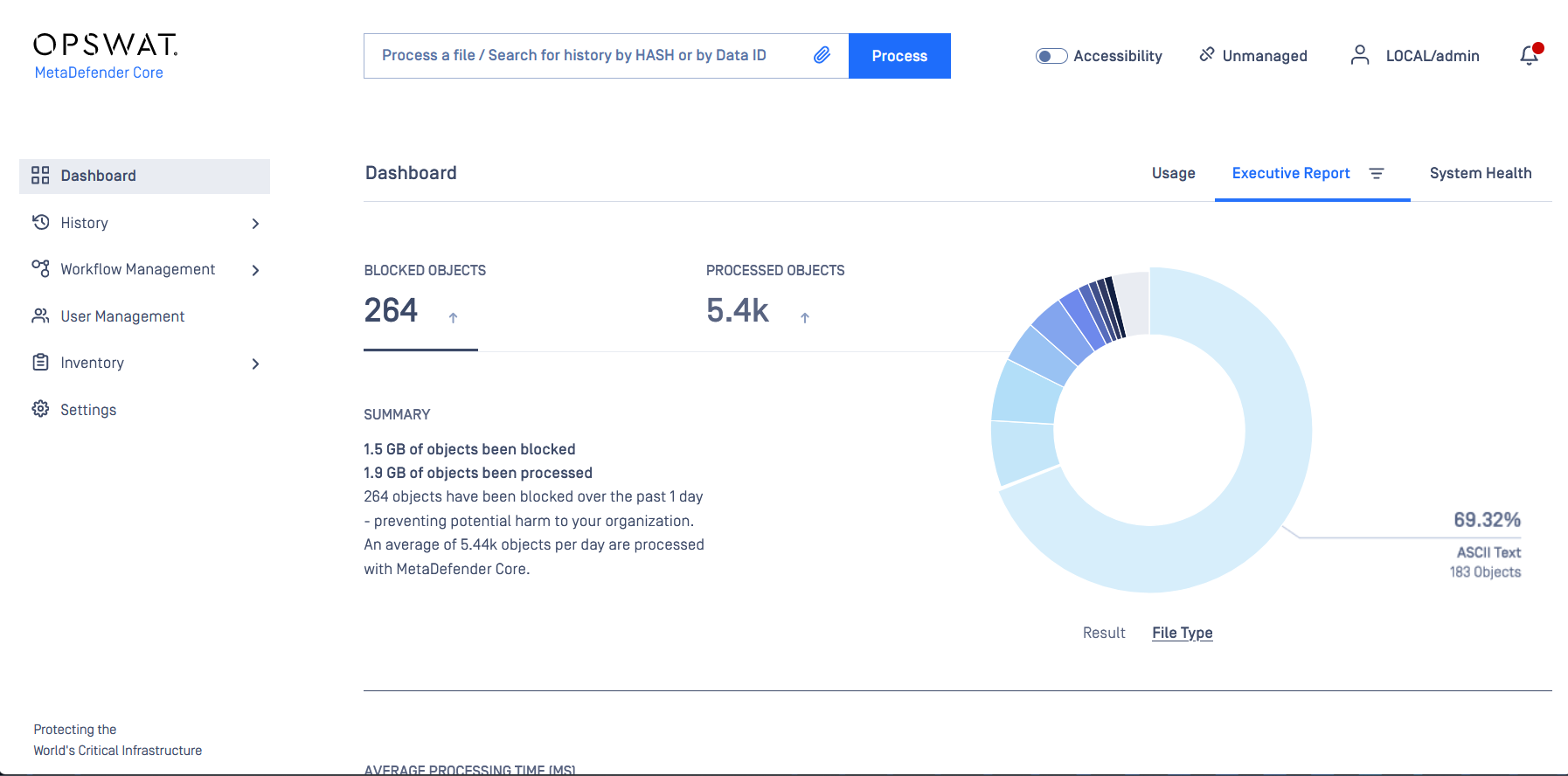
OPSWAT MetaDefender Core Security Dashboard
The dashboard displays blocked threats and processed objects, with a donut chart summarizing file types detected by MetaDefender Core.
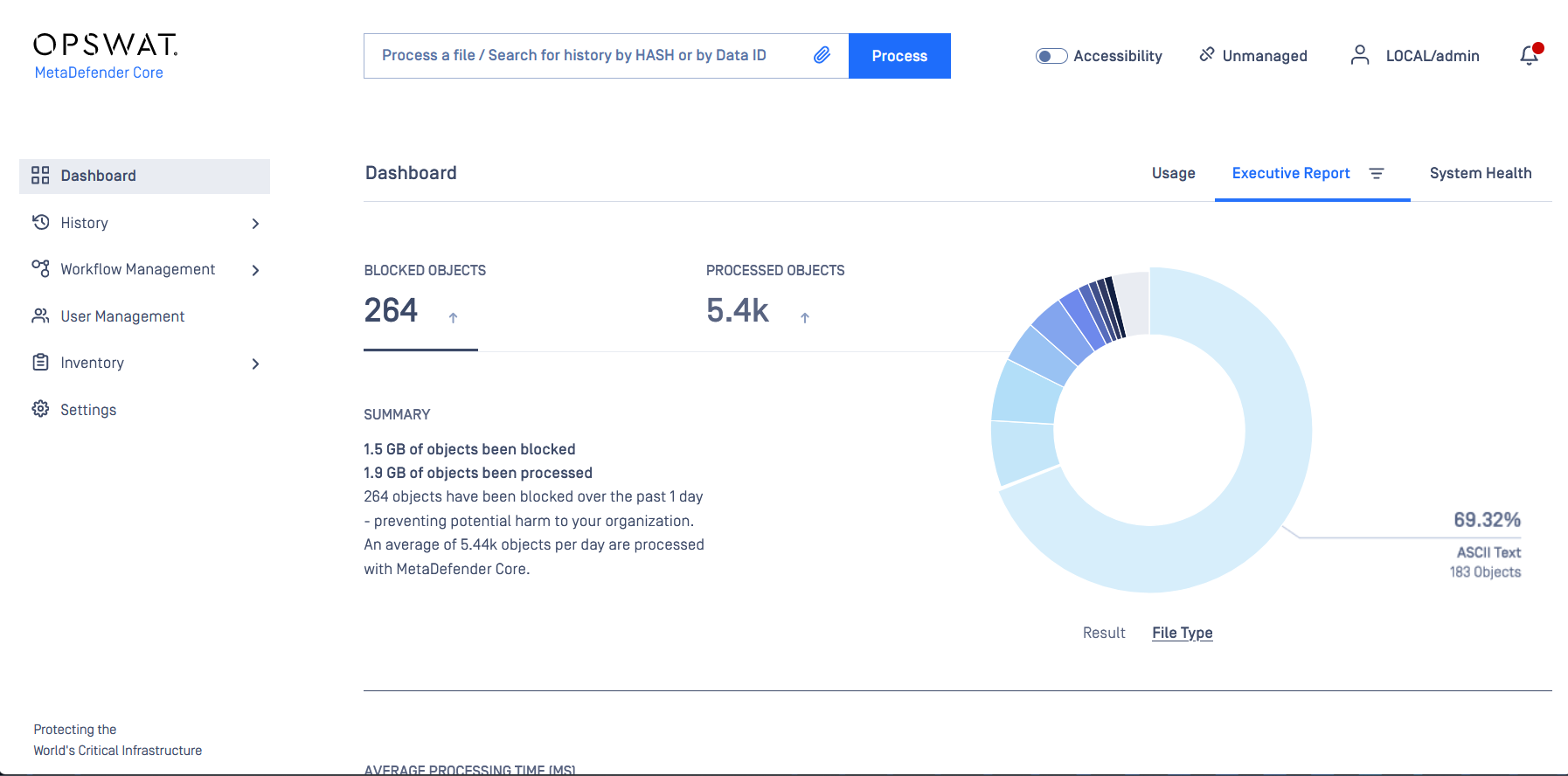
OPSWAT MetaDefender Core Security Dashboard
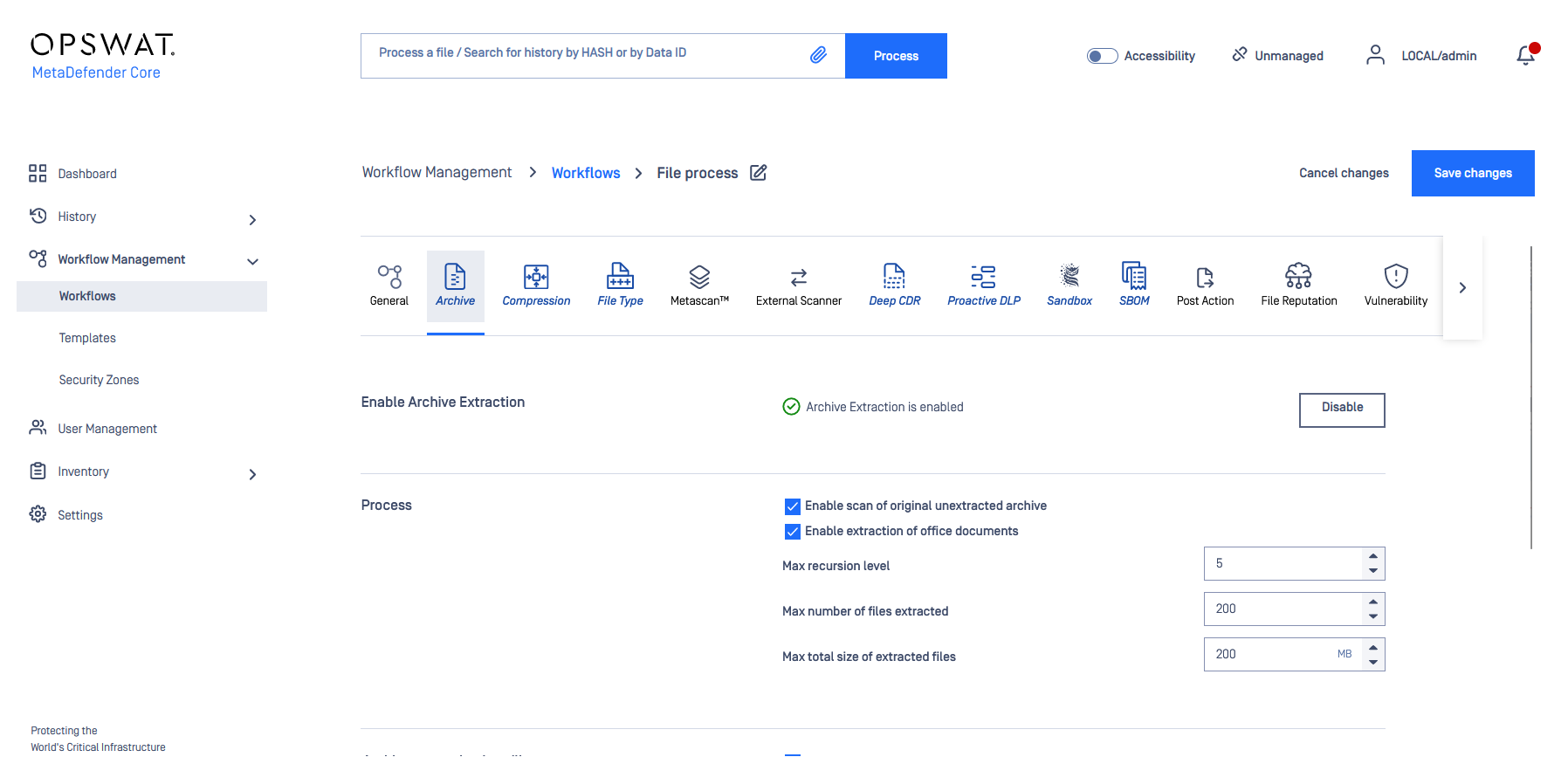
OPSWAT MetaDefender Core Workflow
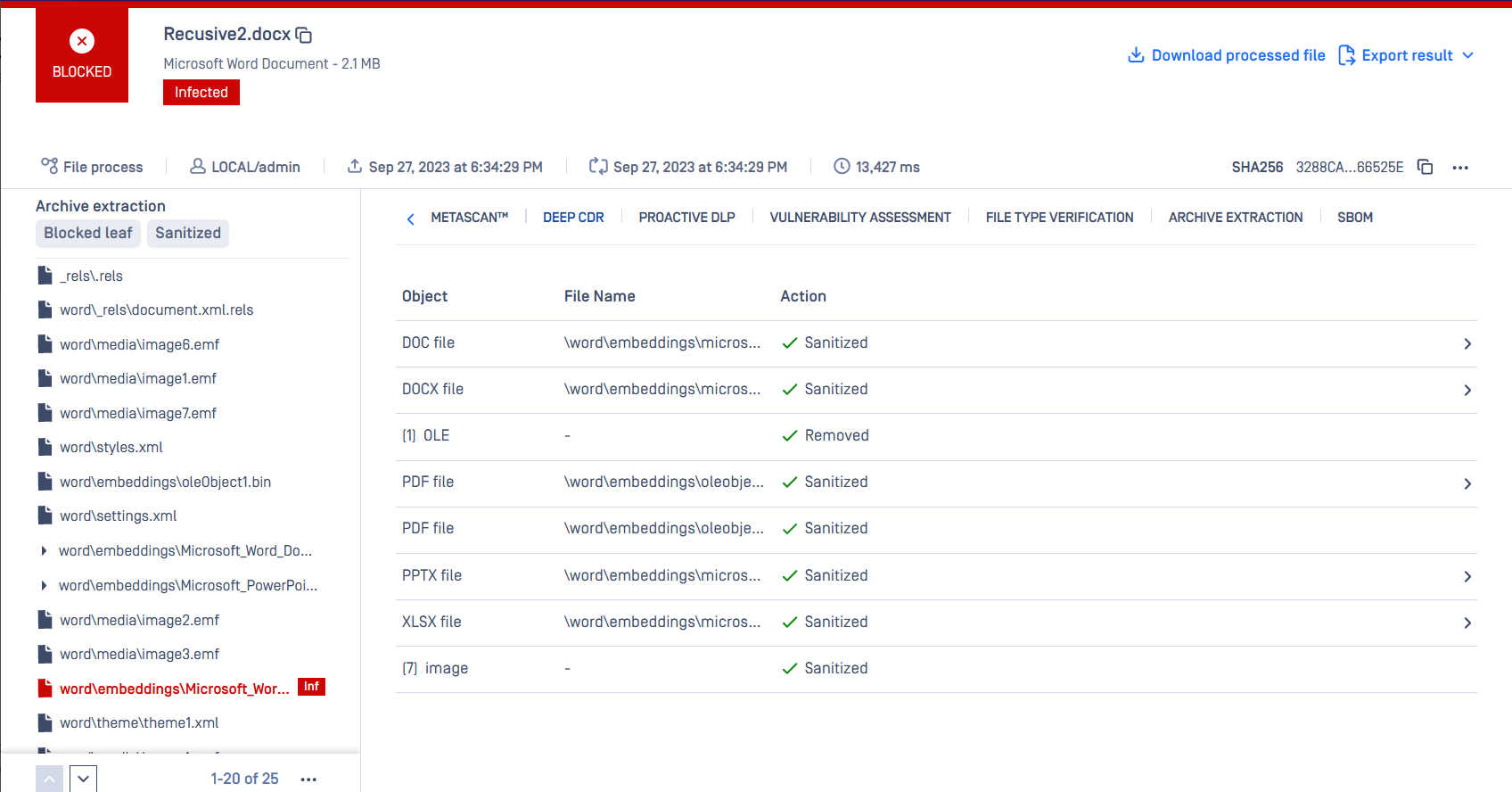
OPSWAT MetaDefender Core Archive Extraction

Product video
Note: This is a BYOL listing for MetaDefender Core. To inquire about a Private Offer, please contact us at apn-sales@opswat.com .
OPSWAT MetaDefender Core offers an advanced multi-layer security platform that prevents malicious traffic from infiltrating your AWS Cloud deployment to protect your mission-critical data from deliberate theft or inadvertent leakage and compromise. The solution combines superior malware detection with market-leading threat detection and prevention with multiscanning, broad file-type Deep CDR (Content Disarm and Reconstruction), and vulnerability scanning and reporting of installers, binaries or applications. MetaDefender Core offers flexible deployment options via AMI, along with support for containers and Amazon EKS. Integration is available via REST API for custom applications, as well as plug-and-play support for ICAP-enabled network appliances and enterprise storage solutions.
Highlights
- Quickly scan all files with top 30+ antivirus engines to detect over 99% of known malware.
- Recursively sanitize 100+ file types with market-leading Deep CDR technology to remove all potential embedded threats.
- Reliable, scalable solution to meet the needs of both small customers and large or complex enterprises.
Details
Introducing multi-product solutions
You can now purchase comprehensive solutions tailored to use cases and industries.

Features and programs
Trust Center

Buyer guide

Financing for AWS Marketplace purchases

Pricing
How can we make this page better?

Legal
Vendor terms and conditions
Content disclaimer
Delivery details
64-bit (x86) Amazon Machine Image (AMI)
Amazon Machine Image (AMI)
An AMI is a virtual image that provides the information required to launch an instance. Amazon EC2 (Elastic Compute Cloud) instances are virtual servers on which you can run your applications and workloads, offering varying combinations of CPU, memory, storage, and networking resources. You can launch as many instances from as many different AMIs as you need.
Version release notes
Resources
Support
Vendor support
NOTE: Pricing displayed in the Pricing Section above is for illustration purposes only and varies depending on customer environment, requirements and other factors. Please contact us at apn-sales@opswat.com for more details.
AWS infrastructure support
AWS Support is a one-on-one, fast-response support channel that is staffed 24x7x365 with experienced and technical support engineers. The service helps customers of all sizes and technical abilities to successfully utilize the products and features provided by Amazon Web Services.
Similar products




Customer reviews
Centralized endpoint security has strengthened patching, compliance and USB control across devices
What is our primary use case?
I have used MetaDefender for various use cases on my PCs at home and also enrolled it on some of my virtualized devices in my virtualized lab, which runs on Linux and Windows. I tried it on Windows 11, Windows 10, Ubuntu, and Kali Linux, and I enrolled the devices after trying quite a few use cases.
I blocked USB access on all the Windows machines, and it successfully blocked it, so I cannot use USB devices on these machines. I also utilize MetaDefender for patching my Windows devices, as it picks up outdated software and often identifies vulnerable third-party programs. Sometimes I need to patch the software or uninstall older versions before installing the new ones. I also use it for Windows updates, as it flags when my Windows updates and OneDrive application need to be updated. Additionally, it checks my browser extensions for status and compliance.
For malware protection, I am using McAfee, but if it has not scanned for some time, MetaDefender flags that too. I need to fine-tune my policy because it identifies McAfee, Windows Defender, and Microsoft Teams as unapproved products, so I will look into that. I have configured a policy, but since I am using a free version, I could not use DLP, and some intensive endpoint management functionalities are limited. It performs many tasks, including patching my devices, tracking critical issues, third-party vulnerabilities, and showing device locations on a graph. In brief, I am using it mostly for endpoint security.
I did not manage to enroll my IoT devices, including my child's device running on iOS and some Amazon products. I could not enroll my Fire Stick or monitor certain network devices. I initially thought I could enroll all those devices, including some children's IoT devices, but there seem to be limitations with Linux endpoint management as well. I hoped MetaDefender could help with parental controls for my Amazon Kids products.
I have not contacted technical support, though I thought I might need assistance fine-tuning my policy. When MetaDefender flagged some Windows DLL files as infections, I looked up information online and needed to whitelist them if they run directly from the Windows folder. If I could not resolve that, I would reach out for support, but I have not raised any tickets with MetaDefender yet.
What is most valuable?
MetaDefender is flexible because, for a free product, you can enroll up to 50 devices, and I have only used about eight devices so far. This flexibility allows you to explore its features before committing to a contract with MetaDefender, unlike other products that provide trial versions for a limited time.
I appreciate that you can use MetaDefender for various tasks, including patching, monitoring, vulnerability assessment, and compliance checking for up to 50 devices on the free license.
On the free version, I can only monitor device compliance, which includes the total enrolled devices and my compliance dashboard showing critical issues and warnings. It compiles data by desktops, laptops, virtual machines, servers, and mobile devices, including my enrolled Windows, Android, and one iOS device. The reports show compliant and non-compliant devices, allowing me to fine-tune my policies and group my devices for different policy applications.
There is no maintenance required on my end because the application on my endpoint automatically patches itself. When there is a new update, it handles the patching and alerts me when I am running the latest version. However, a feature I wish MetaDefender had is the ability to patch my devices centrally from my dashboard, including scheduling patches during off-peak times. I cannot provide a full review since I am using the free version, but based on my experiences, I would recommend MetaDefender to peers and companies using Windows endpoints.
What needs improvement?
I am not using the Expanded File Type and Archive Coverage feature, as it is not part of the free version. I was wondering if I could enroll more devices and replace McAfee with MetaDefender if it can serve as antivirus as well.
The initial deployment is straightforward, as there is an enroll link on the portal. Clicking that gives me options to enroll in MetaDefender Core, Endpoint, or Industrial File. I receive a QR code, and for devices like phones, scanning it enrolls them automatically. For Windows devices, it provides links to download the EML or EXE files, enabling easy Active Directory use. This straightforward enrollment process applies to Linux and macOS as well. However, for IoT devices, it is not so straightforward since it requires building the application from a downloaded file and running it, especially for Linux-based IoTs.
For how long have I used the solution?
I have been working with the solution for more than eight months.
What do I think about the stability of the solution?
MetaDefender does not crash and runs well without conflicts with other Windows or Linux applications, indicating that the developers have optimized its performance very well.
What do I think about the scalability of the solution?
I have only enrolled about eight devices, and I cannot comment on scalability for corporate networks with more than 500 endpoints since I have not tested it with larger numbers. I could consider testing on a licensed version to push patches automatically from the portal to assess its full capabilities. I would appreciate a trial period of one or two weeks for better testing of the full version features.
How are customer service and support?
I have not contacted technical support, though I thought I might need assistance fine-tuning my policy. When MetaDefender flagged some Windows DLL files as infections, I looked up information online and needed to whitelist them if they run directly from the Windows folder. If I could not resolve that, I would reach out for support, but I have not raised any tickets with MetaDefender yet.
Which solution did I use previously and why did I switch?
I have previously used other endpoint products like Fortinet's FortiEDR, but only in a virtualized environment. I could do similar use cases with that one as well.
How was the initial setup?
The initial deployment is straightforward, as there is an enroll link on the portal. Clicking that gives me options to enroll in MetaDefender Core, Endpoint, or Industrial File. I receive a QR code, and for devices like phones, scanning it enrolls them automatically. For Windows devices, it provides links to download the EML or EXE files, enabling easy Active Directory use. This straightforward enrollment process applies to Linux and macOS as well. However, for IoT devices, it is not so straightforward since it requires building the application from a downloaded file and running it, especially for Linux-based IoTs.
Which other solutions did I evaluate?
I have previously used other endpoint products like Fortinet's FortiEDR, but only in a virtualized environment. I could do similar use cases with that one as well.
What other advice do I have?
I am not using the Expanded File Type and Archive Coverage feature, as it is not part of the free version. I was wondering if I could enroll more devices and replace McAfee with MetaDefender if it can serve as antivirus as well.
On the free version, I can only monitor device compliance, which includes the total enrolled devices and my compliance dashboard showing critical issues and warnings. It compiles data by desktops, laptops, virtual machines, servers, and mobile devices, including my enrolled Windows, Android, and one iOS device. The reports show compliant and non-compliant devices, allowing me to fine-tune my policies and group my devices for different policy applications.
I would rate this product an 8 out of 10.
Content policies have protected cloud file uploads and provide clear visibility into blocked data
What is our primary use case?
I have been working with MetaDefender for the past year. I am a customer of MetaDefender . I use MetaDefender for CDR in an Azure Blob environment. The features of MetaDefender that I have found the most valuable include the option to connect to the storage account and create a connection between different blobs and containers, as well as creating a CDR policy and workflow that works for us.
What is most valuable?
I am using the Expanded File Type and Archive Coverage feature. I am using the Enhanced Reporting and Audit Visibility features. The Enhanced Reporting and Audit Visibility features help us to understand what exact type of files are uploaded to the blob and which type of files are blocked or get scanned. We can understand exactly where we might miss the business logical flow and correct it.
The impact of MetaDefender on my organization's scanning process is great because I have the option to harden the platform. If the developers make mistakes in the application development cycle and miss hardening the types of files or the archive levels on the application layer, with MetaDefender, I can restrict it on my end and be sure that no other files are accepted except those that I permit. It will not even be considered to be scanned.
What needs improvement?
MetaDefender could be improved in the future regarding the notification issue. OPSWAT delivers an API structure that you can query via APIs for a lot of data from OPSWAT. However, many customers, including us, are looking for more responsive notifications. If OPSWAT sees that the file uploaded has failed because it doesn't fit the policy or the file types, we would like to get a notification about it rather than developing something on our own that would query OPSWAT for the data.
What do I think about the stability of the solution?
The stability and reliability of MetaDefender are good. I have not yet tested it for disaster recovery. I am planning to do so to understand how it really works in different recovery solutions, such as a cluster or an active-active solution. Therefore, I cannot tell you about this because I have not tested it yet.
What do I think about the scalability of the solution?
When considering the scalability of MetaDefender, I cannot really size it because when you are planning a CDR solution in your company, you should understand where you could have a bottleneck of the files or the hardware. Is it possible to upload a lot of files and still have OPSWAT scan them all, or would they be queued and how much time would it take? You need to plan it. You need to do some sizing before installation and understand exactly what you are seeking from the solution and how it fits your organization.
How are customer service and support?
I do not often communicate with the technical support of MetaDefender, only with the integration team. I am happy with my interaction and communication with MetaDefender's team. The communication was great and understanding. It was easy because I was familiar with OPSWAT Core, not so much with MetaDefender, but with OPSWAT Core I was familiar, and the policy and everything else that you configure on OPSWAT Core. The communication was great.
Which solution did I use previously and why did I switch?
Before MetaDefender, we were using Sasa, which is a platform for CDR, but we use Sasa not exactly for the same business logic. We use Sasa on a different path inside the company, and OPSWAT is really convenient for use via APIs and connecting with storage accounts and other resources that we can upload files from.
How was the initial setup?
I participated in the initial setup and deployment of MetaDefender. The initial setup process was pretty easy. There were a few problems with the SSO configuration, but everything else was pretty straightforward. To integrate the platform and install it very fast and in a good manner, you should plan it very well and understand exactly what your environment is in the company. Whether you are going to install it on-premise or in the cloud environment as a VM or any other solution that they are suggesting. I did not see any problems except the SSO configuration. Everything else was pretty fast and convenient.
What's my experience with pricing, setup cost, and licensing?
I am not much aware of the pricing and licensing of MetaDefender. I know that the SaaS platform is very expensive, and we did it on the IaaS platform in Azure . So I am not very familiar, but because it is IaaS , most of the money goes for the VM and the infrastructure in Azure, and of course the license for the CDR engines. I am not very familiar with the prices.
Which other solutions did I evaluate?
Before choosing MetaDefender, I evaluated other options and other vendors for these use cases, and there are not many vendors doing a great CDR. I know only two that really do the job. We chose MetaDefender because it gives us the option to do more with the CDR, and of course, because of the APIs and the storage accounts because this is the environment that we looked for. We looked for a solution for a specific cloud environment, so MetaDefender was a better solution.
What other advice do I have?
From the beginning, I worked with OPSWAT MetaDefender for other customers at my other job a few years ago. From the last year that we integrated OPSWAT in our company, I have not seen any improvements. It is still okay. It still does the job and makes a good assurance that the files that are coming are really whitelisted and content disarmed. It has not become worse, but it has not become better either. The percentage of accuracy is great. I do not miss anything, but I have not felt any improvement. The effectiveness of MetaDefender in blocking or sanitizing content based on policy is effective. I did not see any problems with the sanitation or something that should be blocked in the test. I did not have such issues.
Before deployment, when looking for a safe path to upload files, you will definitely look for CDR solutions because it depends on the workflow that you are trying to achieve. If there are customers at the end that will upload the files, or some internal business logic that your partners inside the company will upload the files, it depends on what you are trying to achieve. If the files are coming from outside the company, of course, CDR will be the best solution because you would want to restrict the type of files, even the size of the files, and be very restrictive on that end because those files are from the outside, and this path is published outside and is external. When you are looking from the inside, when you are working with partners inside the company, such as different departments, you will not always use the CDR solution. The integration of multi-scanning and Content Disarm and Reconstruction affects my data security operations effectively. If you are trying to disable any active links or anything that could be malicious, OPSWAT did that. It blocks the file types that we are not willing to have inside the company or are not approved. Therefore, it helped us. My impression of the detection rates provided by MetaScan Multi-scanning is great. I have not seen a lot of malicious content on those files that we are scanning, but in the test, I had a pretty high assurance that MetaDefender would find the content that is not welcome at our application end. It is quite easy to research and understand what exactly happened.
I describe the effectiveness of Deep CDR in reconstructing files safely and without signatures as very effective. That is why we chose a CDR platform for those specific workflows that our business wants to accomplish, and not any sandbox or EDR solution that will block the files because they are malicious or suspicious. The CDR still gives us the option to retrieve the file but without any malicious content inside. I do not think I am using Adaptive Sandbox analysis. My overall rating for this solution is eight out of ten.
Advanced threat controls have secured endpoints and simplified safe device access to the network
What is our primary use case?
The use cases for MetaDefender involve checking an endpoint, such as a laptop or USB, to ensure that they are safe, clean, and meet security policy before they connect to the network. I can use it for malware and unknown devices' security status.
What is most valuable?
The best feature of MetaDefender is that it can isolate USB devices from the connected network, blocks malware and unsafe files, and ensures all endpoints follow security policy, so that my organization remains safe and reduces the risk of these threats.
I find MetaDefender effective when it comes to blocking or sanitizing content based on the policies in place because it removes hidden threats and scans devices and endpoints, protecting the environment against unknown and advanced attacks.
The integration of Multi-Scanning and Content Disarm and Reconstruction affects my data security operations positively as it is easy to integrate into my environment.
I find the multi-scanning mechanism and content disarm and reconstruction features beneficial for data security, as MetaDefender's endpoint creates a secure layer to protect my organization from threats and attacks.
The main benefits that MetaDefender brings include isolating USB devices from attacks, removing hidden threats such as malware and malicious attacks, and protecting against unknown and advanced attacks.
My impression of the detection rates provided by MetaScan Multi-Scanning is that they are good, as the scanning of MetaDefender removes hidden threats, detects known issues, and protects devices from unknown malware and attacks.
I assess the effectiveness of Deep CDR in reconstructing files safely without signatures. CDR used in MetaDefender effectively removes dangerous and unsafe attacks by taking a file, removing risky parts, and delivering a clean version to the user, as it removes scripts, hidden links, and malicious components.
I use Adaptive Sandbox Analysis and a sandbox to detect advanced threats, as it receives files, runs them in a VM environment, and discovers the behavior of these files, allowing safe files to return while blocking any that behave poorly.
I find that the features of MetaDefender are strong, and its work is effective for scanning and securing the environment from malware and operates well.
What needs improvement?
I am not using the expanded file type and archive coverage feature because I was unaware of it.
I am not using the enhanced reporting and audit visibility features, and I am unsure about them.
Regarding the reporting, analytics, and audit visibility, I cannot provide a comprehensive answer. I do not know if the audit requirements help me with deep enhanced reporting and audit visibility in MetaDefender.
I have not noticed any improvements in workflow automation with recent enhancements to policy orchestration and engine parallelization.
What I would like to see improved in MetaDefender includes reducing the high cost of the license, as the pricing is very high.
Functionality-wise, I find installation and setup very difficult, and I needed support to help me understand the setup of MetaDefender. The process requires good planning and understanding of the environment to configure it, as the integration with policies takes more time to build and requires more experience.
For how long have I used the solution?
I have been using MetaDefender for one year.
What do I think about the stability of the solution?
When it comes to stability, I find it stable as it maintains good external stability with good availability and no major issues. The setup is difficult, but generally, the product stability is good.
What do I think about the scalability of the solution?
I find it scalable, as more users can work smoothly without any crashing or slowing down.
How are customer service and support?
I evaluate customer service and technical support as good, as they respond in a timely manner.
Which solution did I use previously and why did I switch?
Before MetaDefender, I used EDR, which is the product that I used before switching to MetaDefender.
How was the initial setup?
The deployment process was difficult; I needed a vendor to help me because the setup of MetaDefender is complex.
What about the implementation team?
SIS helped me to deploy MetaDefender.
What was our ROI?
I believe it is worth the money, as it brings time-saving, cost-saving, and efficiency improvements, especially in large environments. However, in smaller environments, it incurs high costs. Overall, it is good because it has many features for scanning and cleaning the environment from malware and saves time.
What's my experience with pricing, setup cost, and licensing?
I do not find it cost-effective, as the costing is high.
Which other solutions did I evaluate?
I decided to switch to MetaDefender because Kaspersky could only detect malware but not take action, whereas MetaDefender detects and prevents threats simultaneously.
I chose MetaDefender because it is capable of adding multi-layered security that prevents threat detection and removes unknown threats, working without signature-based detection, which is beneficial.
What other advice do I have?
I recommend MetaDefender to others because it is effective, has high stability, and is beneficial for environments. I have rated this review a ten out of ten.
Advanced file sanitization has reduced email threats and saves SOC teams significant analysis time
What is our primary use case?
My main use case for MetaDefender is for our client's environment, which is using MetaDefender for their OT security or for their email side. All clients use MetaDefender, and it is especially great for Content Disarm and Reconstruction, which they want to leverage.
For example, one of our clients is using MetaDefender for their email gateway site as their mail gateways, scanning emails. Generally, they use MetaDefender's Content Disarm and Reconstruction property for that email scanning.
None of my customers are using the reporting and audit visibility features on MetaDefender platform.
Integrating multi-scanning and Content Disarm and Reconstruction positively affects my clients' data security operations, prioritizing security over potential delays experienced by end users.
What is most valuable?
The best features MetaDefender offers include its Content Disarm and Reconstruction, which is a key feature chosen by our clients because many other products claim to provide that functionality, but generally, they cannot do it as cleanly. Through Proof of Concept sessions with our clients and the OPSWAT team, they see that MetaDefender's Content Disarm and Reconstruction is strong, usable, and valuable for our customers, making them want to work with OPSWAT specifically for this feature.
For example, one of our customers was not using any Content Disarm and Reconstruction technology but was receiving emails containing PDF documents or XLSX documents, some with malicious content. MetaDefender's technology worked effectively, disarming and reconstructing PDFs to deliver clean copies to their users, while allowing their analysts to see the malicious code.
MetaDefender has positively impacted my clients' organizations by saving time for their SOC teams who were previously receiving false positives and unnecessary alarms from other products, allowing them to focus on analyzing real threats, which has led to fewer incidents.
For one of my clients, a major bank in Turkey, they reported saving approximately 30 percent of their SOC time on analyzing emails since implementing MetaDefender.
MetaScan multi-scanning feature is excellent because it provides multiple vendors for scanning. If one vendor fails, the others remain operational, ensuring continued protection.
Assessing the effectiveness of Deep Content Disarm and Reconstruction in reconstructing files safely and without signatures reveals it to be effective, as clients receive identical documents without changes other than the removal of malicious code.
MetaDefender's file-based vulnerability assessment analyzes binaries and installers for known vulnerabilities before they enter a network, providing a proactive defense that is highly valuable for our customers.
What needs improvement?
While MetaDefender's mail gateway already gives fewer false positives, there is still room for improvement in reducing those even further.
Additionally, MetaDefender could benefit from a better graphical user interface for administrators, making it more usable, although this is not an urgent need but an area for potential improvement.
For how long have I used the solution?
I have been using MetaDefender for three years.
Which solution did I use previously and why did I switch?
It was a fresh sell to our customers for MetaDefender, and I evaluated other options before choosing MetaDefender.
What was our ROI?
I have not seen a direct return on investment, but clients have noted that the product saves time and may reduce the need for fewer employees since the SOC team focuses on critical incidents as MetaDefender handles current analyses efficiently.
What's my experience with pricing, setup cost, and licensing?
Pricing, setup costs, and licensing are handled by my sales team, but feedback indicates that our pricing is better than other vendor solutions.
Which other solutions did I evaluate?
I can specify that my clients considered other options before choosing MetaDefender.
What other advice do I have?
I do not have anything else to add about how my clients use MetaDefender. My review rating for MetaDefender is ten out of ten.
File sanitization has blocked phishing payloads and now reduces manual incident analysis
What is our primary use case?
MetaDefender is used in one of our client environments where every file upload to their web portal goes through the scanning process. It scans using multiple engines and applies CDR before allowing the file into the system. This has helped us stop suspicious documents even before users interface with them.
With the increase in phishing and document-based attacks recently, this kind of file sanitization layer has become very important for us.
What is most valuable?
MetaDefender offers some of the best features such as multiple engine malware scanning, content disarm and reconstruction (CDR), deep file inspection, and strong API-based integrations. Deep file inspection is the feature I find myself using the most, as it helps in my workflow significantly. The multi-engine approach gives more confidence compared to relying on a single antivirus engine, especially for zero-day threats.
MetaDefender's effectiveness in blocking or sanitizing content based on policy is very strong. A combination of multi-engine scanning and CDR makes a big difference. It does not just rely on a signature; it enforces policy at the file level. Policies like blocking files with high-risk indicators, sanitizing documents with embedded macros, and allowing only clean files into the environment show its strengths. MetaDefender is very effective in sanitizing files without breaking usability. The integration of multi-scanning and Content Disarm and Reconstruction affects our data security operations. MetaDefender plays a very important role in today's threat landscape, which heavily uses documents and file-based payloads.
What needs improvement?
The UI can be more user-friendly, and initial steps and policy tuning take some time. Reporting can be improved as extracting detailed insights for management reports takes extra effort.
For how long have I used the solution?
I have been using MetaDefender for 1.5 to 2 years.
What do I think about the stability of the solution?
MetaDefender is stable. We have not faced major downtime.
What do I think about the scalability of the solution?
MetaDefender's scalability is excellent, as it handles larger volumes of file scanning without major issues.
How are customer service and support?
Support for MetaDefender is very responsive, though sometimes complex issues take time to resolve.
Which solution did I use previously and why did I switch?
We evaluated sandbox-based solutions and some email security tools, but MetaDefender's CDR approach was more practical.
What was our ROI?
MetaDefender has positively impacted my organization by reducing the risk of file-based attacks, which has significantly improved our overall defense against phishing and malware delivery techniques. We have seen around a 40% drop in malicious file incidents, and our SOC team is spending less time on manual file analysis now.
What other advice do I have?
MetaDefender is a very time-saving and effort-saving tool. I advise others looking into using MetaDefender to understand their file flow properly before deployment. If integrated correctly, it becomes a very strong layer against modern file-based attacks.
Threats in a file are cleaned before they reach the core, creating a silent shield in place. The SOC workload has reduced because fewer suspicious files reach analysis, and users do not complain much since files still open normally after sanitization. I would rate this review an 8.