AWS IoT Device Management features
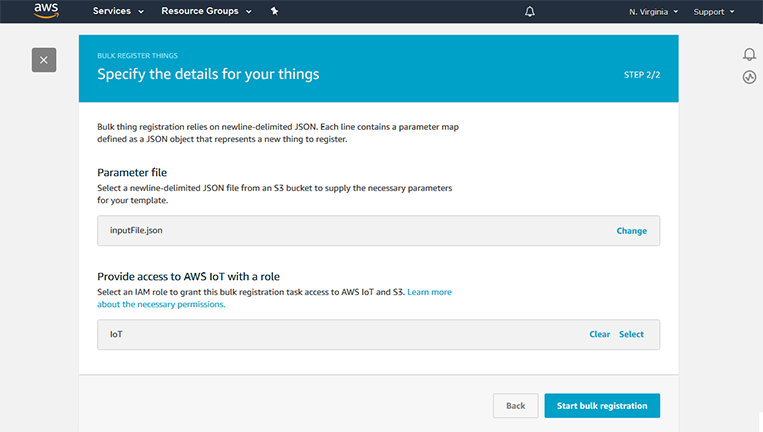
Register connected devices in bulk
Register new devices with AWS IoT Device Management. Using the IoT management console or API, you can upload templates that you populate with information like device manufacturer and serial number, X.509 identity certificates, or modify configurations on-demand for specific devices at scale. Then, you can configure the entire fleet of devices with this information in a few steps in the management console.
Learn more about the bulk registration process.
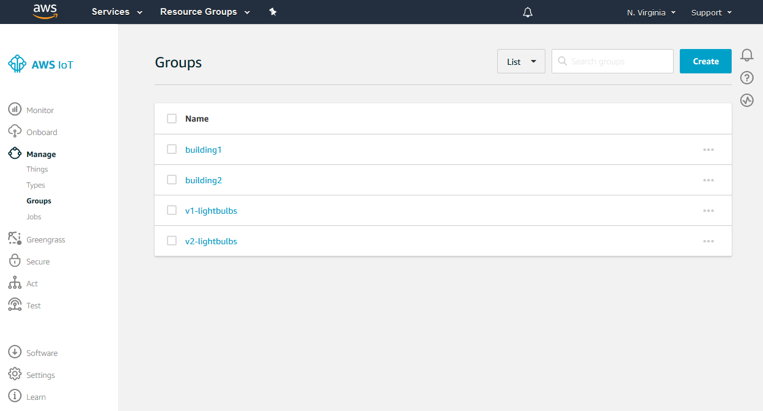
Organize connected devices into groups
Group your device fleet into a hierarchical structure based on function, security requirements, or any other category. You can group one device in a room, group devices together that operate on the same floor, or group all the devices that operate within a building. Then, you can use these groups to manage access policies, view operational metrics, or perform actions on your devices across the entire group. You can also automate organization of your devices with dynamic thing groups. Your dynamic thing groups will automatically add devices that meet your specified criteria and remove the devices that no longer match the criteria.
Learn more about how to create static groups and dynamic groups.
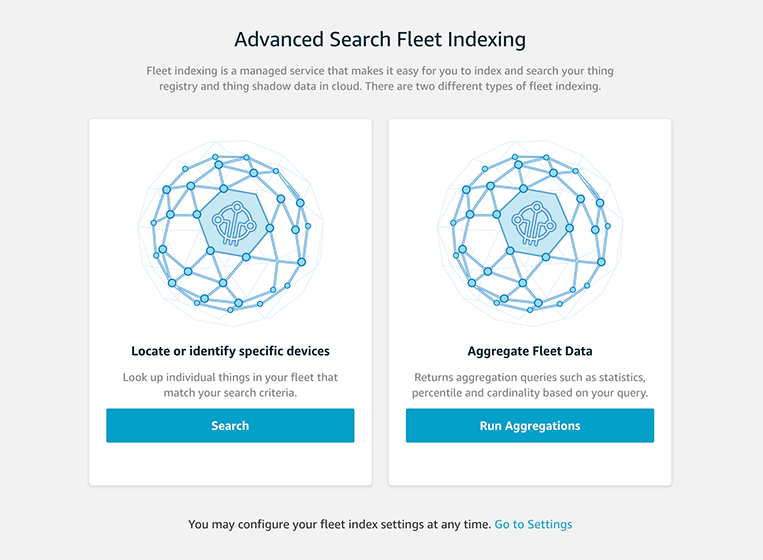
Index and search your fleet
Query a group of devices and aggregate statistics on device records based on any combination of device attribute, state, and connectivity indexing so that you can better organize and understand your fleet. For example, you can search for a group of connected temperature sensors in a manufacturing facility, count the number of sensors with a specific firmware version, and find the average temperature reading for those sensors.
Learn more about fleet indexing.
Simplify device setup and unify control
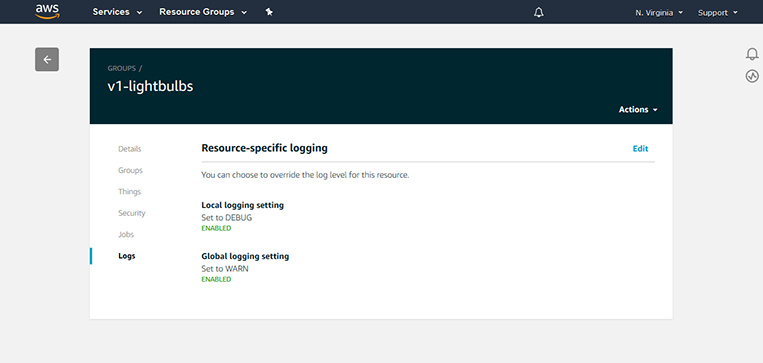
Monitor system performance
Monitoring is an important part of maintaining the reliability, availability, and performance of your IoT solutions. With AWS IoT Device Management, collect device logs so that, in the event of a problem, you can query the log data to figure out what went wrong. You can configure the logs to include only the metrics that are critical to device performance so that you can identify issues quickly. For example, you can include device metrics like error codes that indicate download failures or device restart counters, and quickly identify and troubleshoot issues on devices within the device group.
Learn more about monitoring IoT resources on AWS.
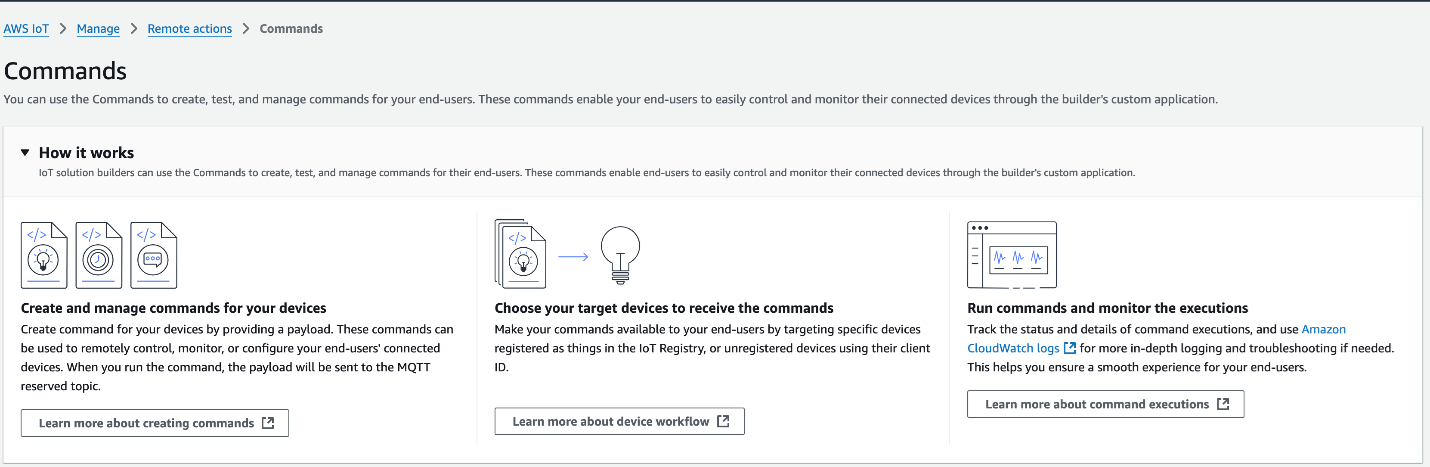
Deliver action-oriented remote messages to targeted devices efficiently
The Commands feature of AWS IoT Device Management supports efficient remote and targeted device interactions, enabling you to send instructions, trigger actions, or modify configurations on-demand on specific devices at scale. With the commands feature, you can quickly define custom payloads in any format as reusable AWS resources for recurrent use. The feature enables you to initiate executions as needed, configure the timeout settings, receive real-time updates, and set fine-grained access control, making it easier for you to build flexible and scalable IoT applications.
Learn more about sending targeted messages using AWS IoT Device Management Commands.
Manage and perform updates remotely
Push software and firmware to devices in the field to patch security vulnerabilities and improve device functionality. You can initiate bulk updates, configure rollout schedule, control deployment velocity, set failure thresholds, and define continuous jobs to update device software automatically so that they are always running the latest version. You can send actions such as device reboots or factory resets remotely to fix software issues in the device or restore the device to its original settings. You can also digitally sign files that you send to your devices, helping to ensure that your devices are not compromised.
FreeRTOS over-the-air (OTA) update job allows you to use AWS IoT Device Management to schedule your FreeRTOS device software updates. You can also use the code signing feature.
You can also create an AWS IoT Greengrass Core update job for one or more AWS IoT Greengrass Core devices using AWS IoT Device Management to deploy security updates, bug fixes, and new AWS IoT Greengrass features to connected devices.
Learn more about how to keep your system up to date with AWS IoT Device Management Jobs.
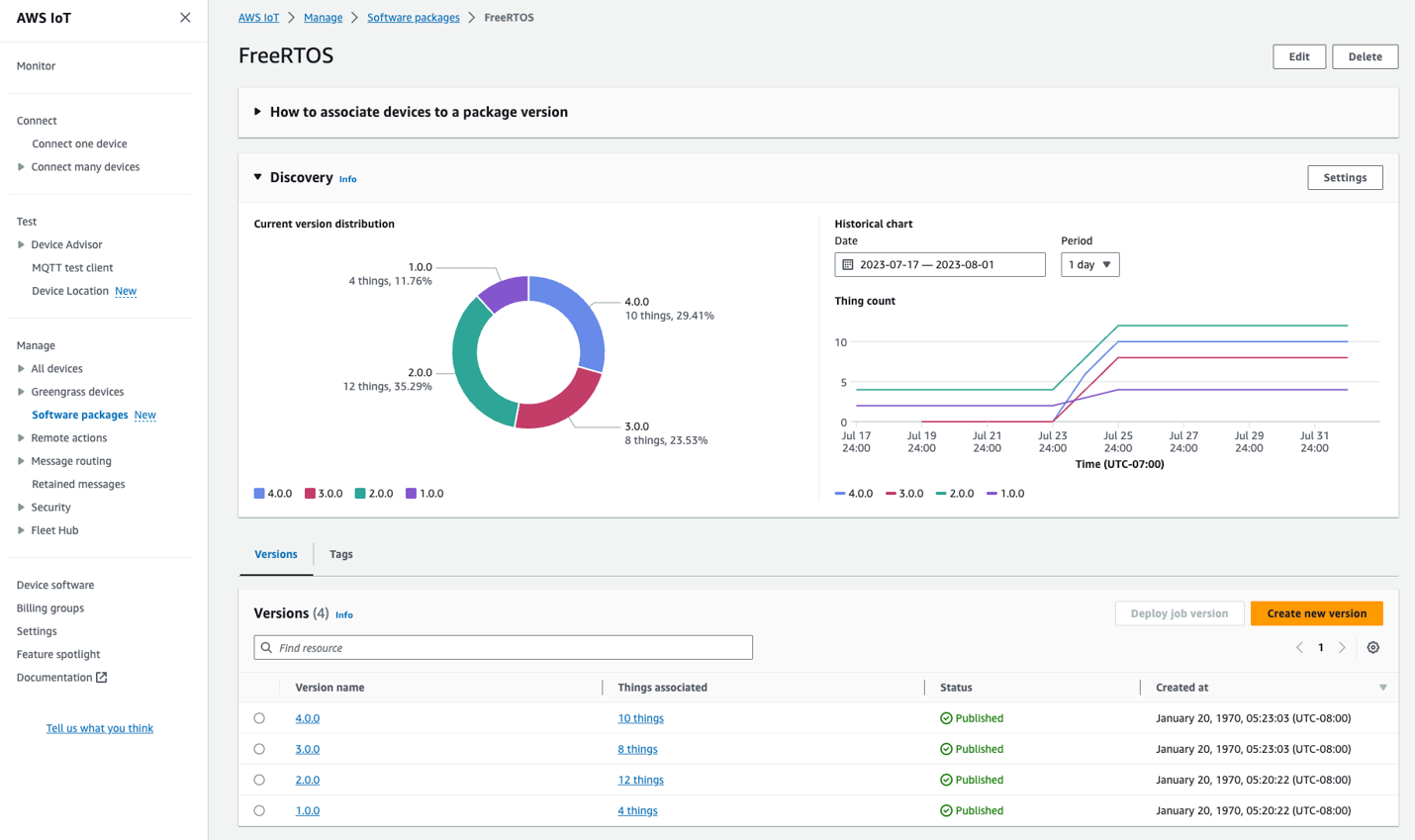
Manage software package versions
With AWS IoT Device Management Software Package Catalog, easily track and monitor software package versions, gain valuable insights from a central dashboard, and perform targeted updates on IoT devices running specific software version. The deep integration between Software Package Catalog and AWS IoT Device Management fleet indexing makes it seamless for you to index, search, and gain a complete overview of software package version distribution and associated metrics across your entire device fleet. Moreover, the visibility provided by Software Package Catalog helps you easily implement targeted actions on devices running specific software versions. For example, you can use AWS IoT Device Management Jobs to perform OTA updates only on devices that are explicitly operating on a particular software version.
Learn more about Software Package Catalog.
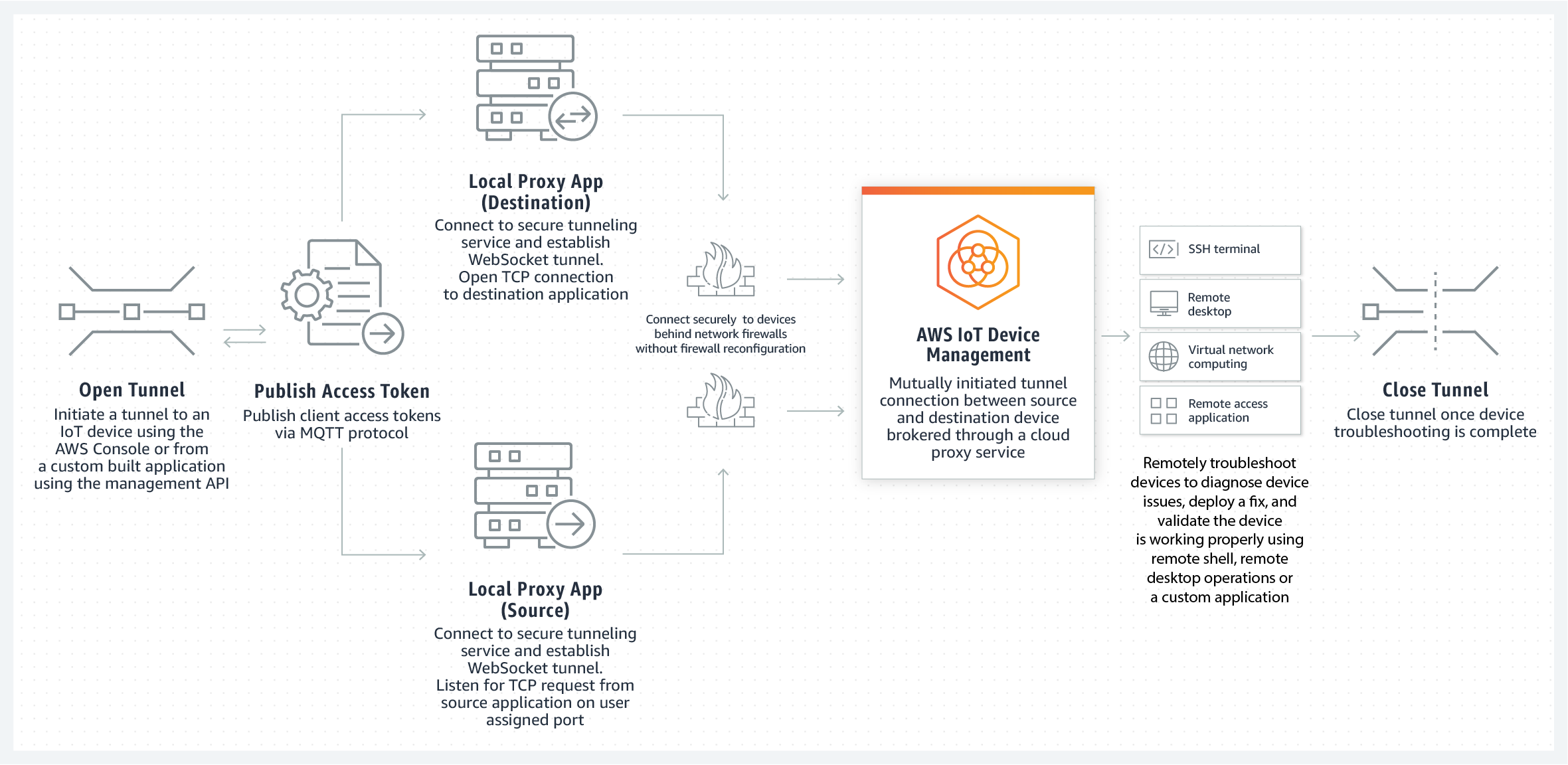
Establish bidirectional communication to remote devices with secure tunneling
AWS IoT Device Management supports the creation of a device tunnel—a secure remote communications session to a device. This provides secure connectivity to individual devices, which you can then use to diagnose issues and act to solve in just a few steps. You can also make multiple concurrent client connections over a single secure tunnel, so you can perform more advanced device troubleshooting, such as issuing remote shell commands to a device while simultaneously debugging a web application on the same device.
With secure tunneling, you can rapidly build remote access solutions to connect to devices on isolated networks or behind firewalls. You can establish these trusted connections that allow you to comply with your customers’ corporate security policies without the need to adjust inbound firewall configurations or manage proxies for each user network. This is accomplished by a mutually initiated tunnel connection between source and destination devices that is brokered through the secure tunneling feature in AWS IoT Device Management. These secure device connections are authenticated and encrypted using Transport Layer Security (TLS). They can be configured with a user-defined timeout setting that will ensure connections close after a certain period of time.
Learn more about secure tunneling.
Learn more about AWS IoT Device Management pricing
Visit the pricing pageHave more questions?
Contact usDiscontinued Soon
New customer sign-ups and account upgrades are no longer available for Fleet Hub. Learn more »


