Attribute-Based Access Control (ABAC) for AWS
What is attribute-based access control?
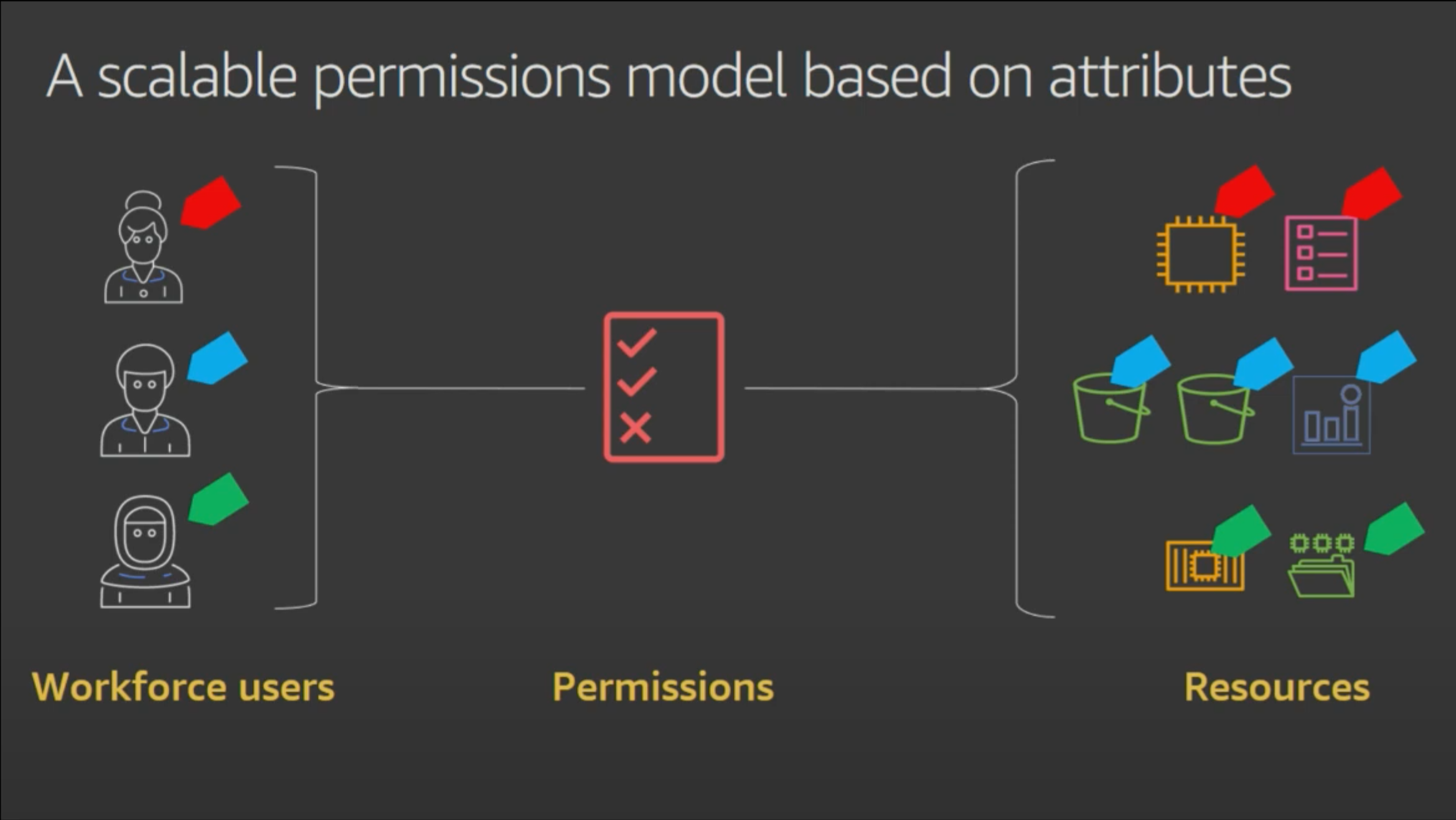
Attribute-based access control (ABAC) is an authorization strategy that lets you create fine-grained permissions based on user attributes, such as department, job role, and team name. User attributes make permissions more intuitive, and they simplify the administrative experience of managing access. By specifying permissions using attributes, you can reduce the number of distinct permissions that you need for creating fine-grained controls in your AWS account.
For example, instead of creating AWS Identity and Access Management (IAM) roles with distinct policies for every team or individual to ensure the right levels of access, you can use ABAC to group attributes to identify which resources a set of users can access. Then, as you add new users and resources, you can associate the appropriate attributes so that the right users have access to the right resources. It’s no longer necessary to update existing policies to allow new users to access resources. With attribute-based access controls, your authorization strategy can scale at the pace of your innovation. Learn about the services you can use in your ABAC strategy.
Benefits
Simplify IAM role management
Apply fine-grained permissions as resources change
Monitor actions that users have performed
Fundamentals of ABAC for AWS


Use cases
Grant developers and workloads read and write access to only their project resources
When you base permissions on user attributes, you can ensure that developers and workloads have read and write access to only the resources that belong to their projects. If developers’ or workloads’ attributes match those of the project resources, the developers or workloads are allowed access. Otherwise, they are denied. For example, you can assign developers from two different teams, Alejandro and Mary, to the same IAM role, and then choose the team name attribute for access control. When Alejandro and Mary sign in to AWS, their identity provider (IdP) sends their team name as an attribute in the AWS session, and Alejandro and Mary are granted access to only their team’s project resources as indicated by the tags on those resources.
Mary and Alejandro also could be restricted to create IAM roles that have their respective team name set as a tag, so workloads they create on AWS can access only the resources that belong to their teams.
Ensure that permissions are granted based on IAM attributes when accessing shared resources
When you base permissions on attributes, you can control the level of access a user has to shared AWS resources. For example, by using the same IAM role, you can grant one developer, John, read-only access to an AWS Secrets Manager secret owned by another developer, Saanvi, on his same team because John’s team attribute is equal to the team tag on Saanvi’s secret. This is possible because their IAM role’s permissions are based on a team name attribute. The secret instance may be tagged as created by Saanvi, so she is granted full access to the secret.
Because entitlements are based on the human user’s attributes and not their role’s permissions, John and Saanvi might be granted the same level of access to that secret across different roles.
Use your corporate directory for ABAC
For example, you can leverage user attributes such as login and department to control access to your EC2 instances and Systems Manager Session Manager.
Your IdP also can include information about the user’s authorization context as attributes in AWS. This information can include elements such as whether the user used multi-factor authentication to authenticate to your IdP.
If you use AWS IAM Identity Center (successor to AWS SSO) to authenticate to your AWS accounts, you also can use ABAC whether or not your AWS SSO instance is connected to an external directory or used standalone.
Use tags to manage and secure access to IAM resources
Require developers to tag new resources they create
Get started
Did you find what you were looking for today?
Let us know so we can improve the quality of the content on our pages