AWS Compliance Programs
Overview
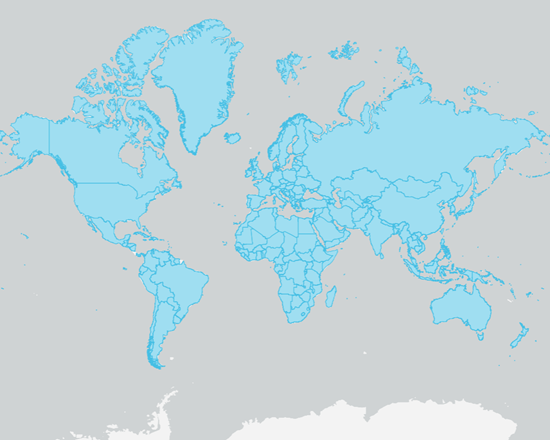
The AWS Compliance Program helps customers to understand the robust controls in place at AWS to maintain security and compliance of the cloud. By tying together governance-focused, audit-friendly service features with applicable compliance or audit standards, AWS Compliance Enablers build on traditional programs, helping customers to establish and operate in an AWS security control environment.
IT standards we comply with are broken out by Certifications and Attestations; Laws, Regulations and Privacy; and Alignments and Frameworks. Compliance certifications and attestations are assessed by a third-party, independent auditor and result in a certification, audit report, or attestation of compliance. AWS customers remain responsible for complying with applicable compliance laws, regulations and privacy programs. Compliance alignments and frameworks include published security or compliance requirements for a specific purpose, such as a specific industry or function.
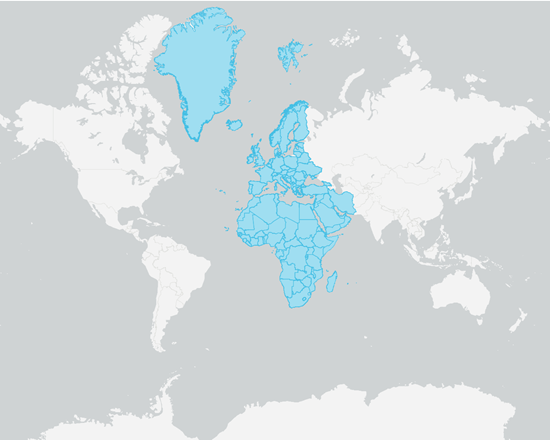
Certification / Attestation
Compliance certifications and attestations are assessed by a third-party, independent auditor and result in a certification, audit report, or attestation of compliance.
Europe, Middle East & Africa
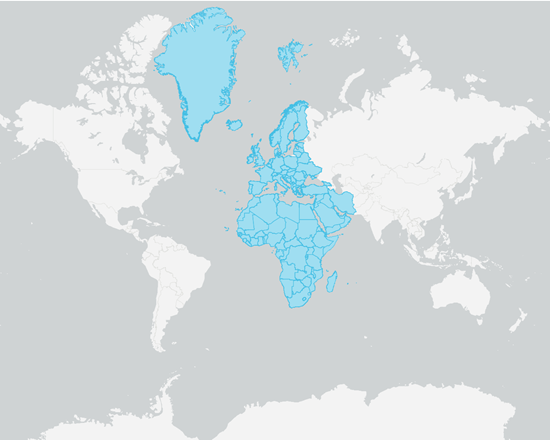
Laws / Regulations:
AWS customers remain responsible for complying with applicable compliance laws and regulations. In some cases, AWS offers functionality (such as security features), enablers, and legal agreements (such as the AWS Data Processing Agreement and Business Associate Addendum) to support customer compliance. No formal certification is available to (or distributable by) a cloud service provider within these law and regulatory domains.
Asia Pacific

Europe, Middle East & Africa
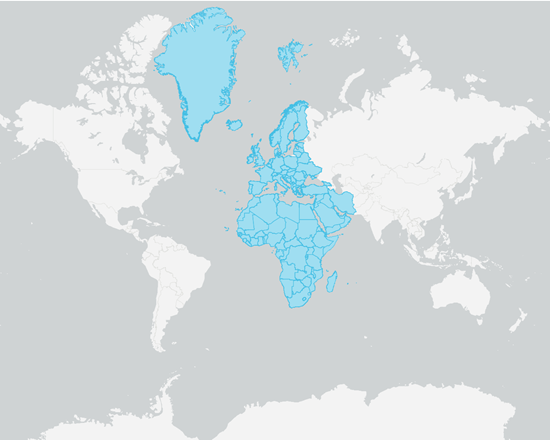
Alignment / Framework
Compliance alignments and frameworks include published security or compliance requirements for a specific purpose, such as a specific industry or function. AWS provides functionality (such as security features) and enablers (including compliance playbooks, mapping documents, and whitepapers) for these types of programs. Requirements under specific alignments and frameworks may not be subject to certification or attestation; however, some alignments and frameworks are covered by other compliance programs.
USA
- NIST 800-162
- NIST 800-172
- NIST 800-34 - Contingency Planning
- NIST 800-53
- NIST 800-64
- NIST CSF
- NIST RMF

Europe, Middle East & Africa
AWS European Sovereign Cloud
Built, operated, controlled, and secured in Europe
The AWS European Sovereign Cloud is a new, independent cloud for Europe entirely located within the European Union, designed to help customers meet their most stringent digital sovereignty needs.
Privacy
At AWS, customer trust is our top priority. We deliver services to millions of active customers, including enterprises, educational institutions, and government agencies in over 190 countries. Our customers include financial services providers, healthcare providers, and governmental agencies, who trust us with some of their most sensitive information.