- AWS Solutions Library
- Guidance for External Connectivity to Amazon VPC Lattice
Guidance for External Connectivity to Amazon VPC Lattice
Overview
This Guidance demonstrates how to configure a proxy in a virtual private cloud (VPC) to connect external services to your Amazon VPC Lattice service network, enabling public, hybrid, or cross-Region access. While VPC Lattice simplifies service-to-service consumption within an AWS Region, if your applications reside outside that Region, you'll need to create and manage a proxy solution. By following this Guidance to build an ingress VPC and configure appropriate DNS resolution, you can easily establish connectivity to your external resources from your VPC Lattice service network.
How it works
Overview
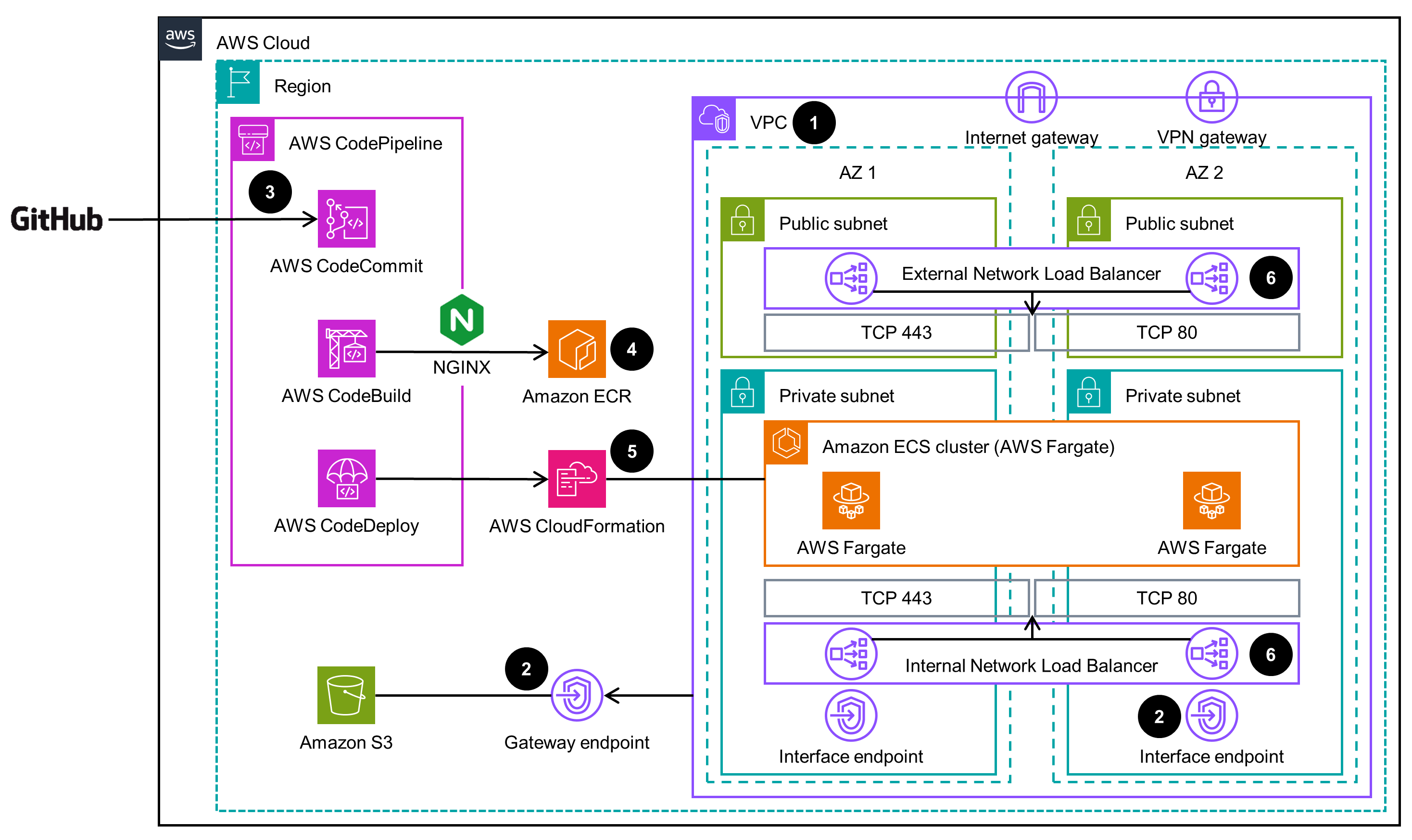
This architecture diagram shows how to configure a proxy in a virtual private cloud (VPC) to connect external services to Amazon VPC Lattice. There are three ways to use Amazon VPC Lattice for public, hybrid, or cross-Region access. Each are outlined further are in the corresponding tabs.
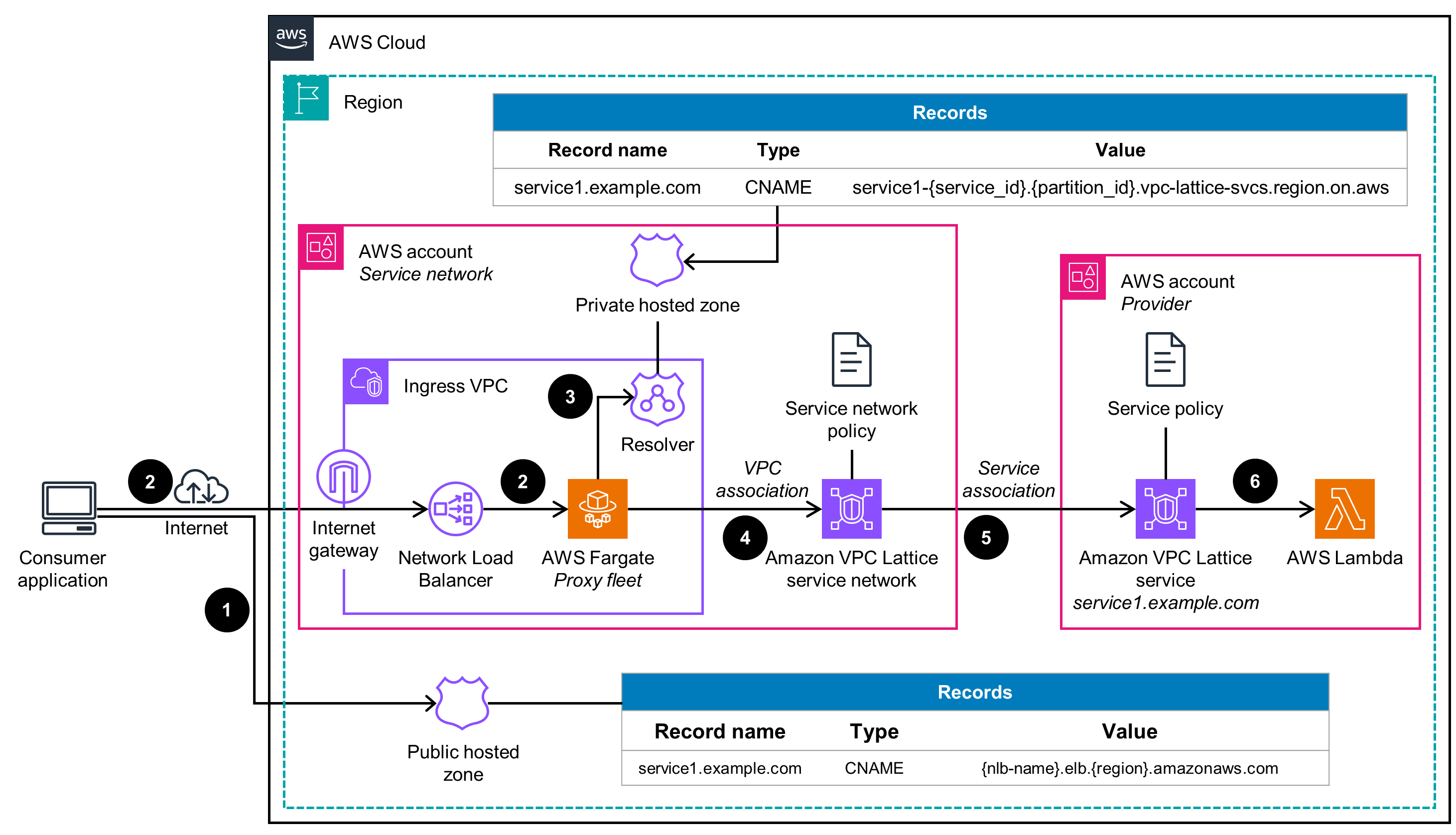
Public access
This architecture diagram shows how placing a proxy solution in an associated VPC enables external consumption of VPC Lattice services by adjusting the DNS resolution.
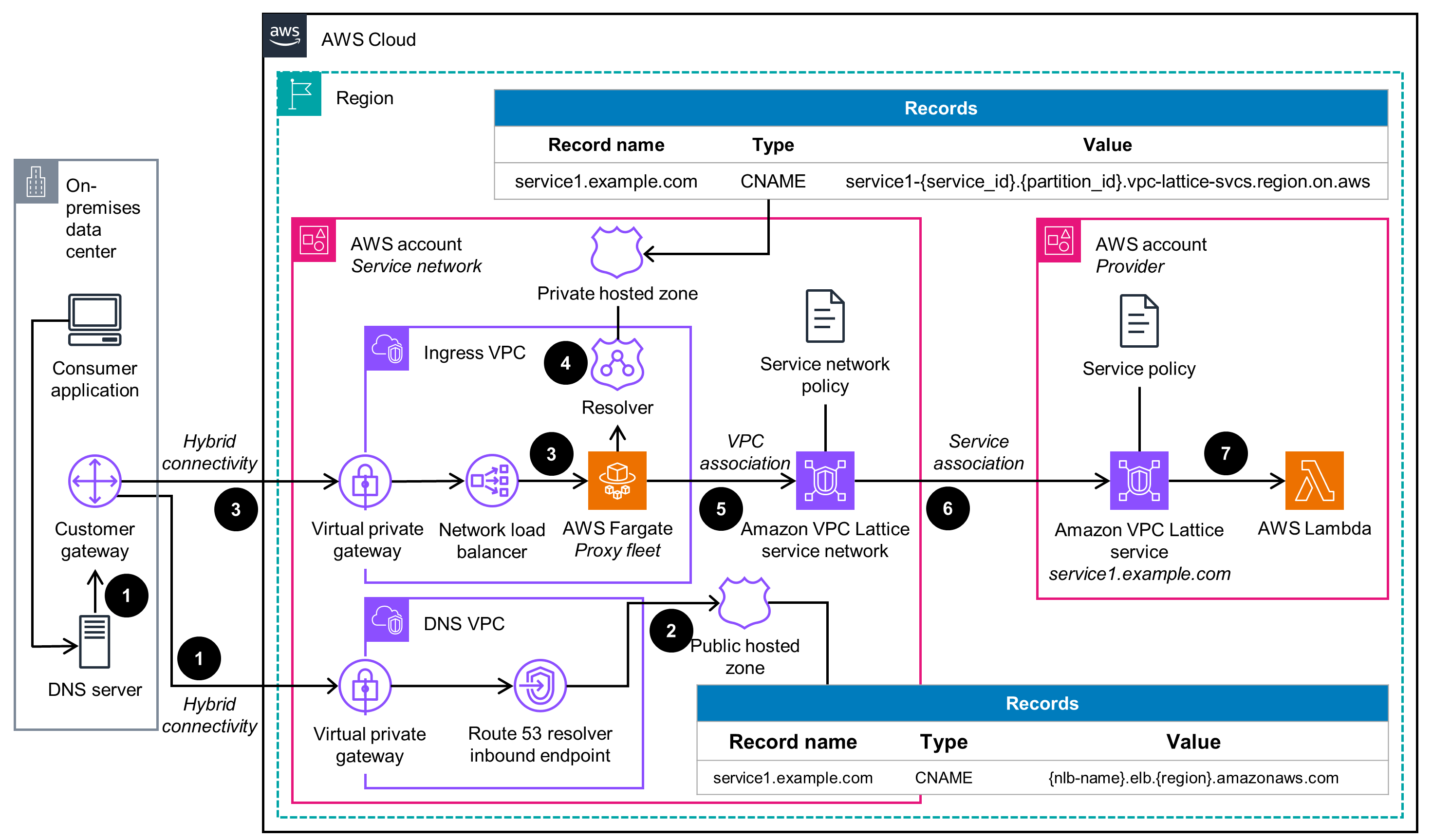
Hybrid access
This architecture diagram shows how placing a proxy solution in an associated VPC enables on-premises applications to have external consumption of VPC Lattice services by adjusting the hybrid DNS resolution.
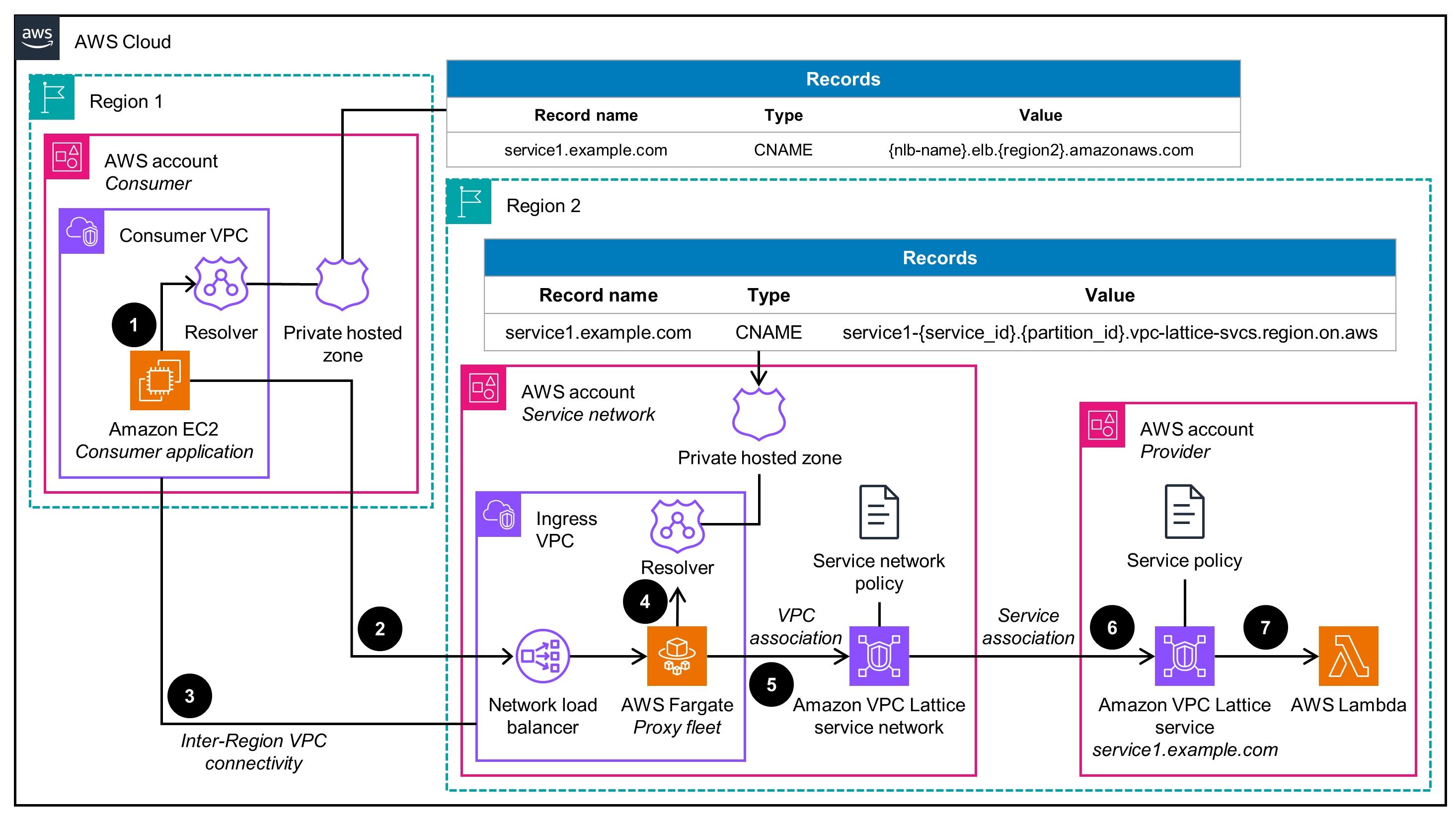
Cross-Region access
This architecture diagram shows how placing a proxy solution in an associated VPC enables cross-Region consumption of VPC Lattice services by adjusting the hybrid DNS resolution.
Well-Architected Pillars
The architecture diagram above is an example of a Solution created with Well-Architected best practices in mind. To be fully Well-Architected, you should follow as many Well-Architected best practices as possible.
CodePipeline enables you to use a pipeline to make controlled and auditable changes through an artifact repository for the NGINX proxy solution, helping you avoid undesired updates. In addition, CloudFormation uses infrastructure as code to deploy all resources, giving you visibility and control over the created resources.
VPC Lattice handles authentication and authorization by using optional auth policies, both in the VPC Lattice service network and services. AWS Identity and Access Management (IAM), which uses the Zero Trust on AWS security model, establishes secure authentication and authorization mechanisms for service-to-service communication. IAM security credentials generate AWS Signature Version 4 signatures, which are passed to VPC Lattice. Common network security measures for the VPC and application add a second layer of security control. For example, you can use security groups and network access control lists, and the NGINX configuration enables you to define an allowlist of the source IPs that can connect to the proxy targets.
This Guidance deploys resources in three AZs, providing high availability for your proxy solution, made using a Network Load Balancer and an Amazon ECSon Fargate fleet. Additionally, CodePipeline uses managed AWS services—including CodeCommit, CodeBuild, and CloudFormation—that are built to be highly available within a Region by default.
Note: This Guidance has been built on the assumption that it will automatically scale and contract using average CPU metrics for the Amazon ECS service as the dimension. Load testing revealed that the Guidance is CPU-bound as the load increases, based on the specifications of the chosen task sizes. You can adjust this Guidance to use a metric that best suits your application’s profile and load.
This Guidance uses a combination of AWS native services and customizable options. It uses a Network Load Balancer as the entry point because it provides high throughput, flexibility in protocol, and feature support when connecting to VPC Lattice. An Amazon ECS on Fargate proxy fleet provides flexibility in resolving the domain name generated by VPC Lattice to the link-local addresses (which might vary). The fleet uses Fargate to gain the scalability of serverless technologies and to simplify container management.
This Guidance automatically scales the Amazon ECS on Fargate tasks as required, depending on CPU utilization. This automatic scalability of Amazon ECS means that the proxy solution only uses the required compute capacity, so you do not have to pay for unnecessary compute.
Amazon ECS on Fargate handles scaling automatically so that your proxy solution has an optimal compute footprint based on CPU load. Additionally, the tasks use a lightweight version of NGINX to minimize the computational load when sending requests to VPC Lattice. By using configured and tested workload elasticity, this Guidance helps you efficiently match your cloud resource utilization to demand and avoid overprovisioned capacity, ultimately lowering your carbon footprint.
Deploy with confidence
Ready to deploy? Review the sample code on GitHub for detailed deployment instructions to deploy as-is or customize to fit your needs.
Disclaimer
Did you find what you were looking for today?
Let us know so we can improve the quality of the content on our pages