Guidance for Using Google Tag Manager for Server-Side Website Analytics on AWS
Enhance real-time data analytics to get better insights on website interactions
Overview
How it works
How it works
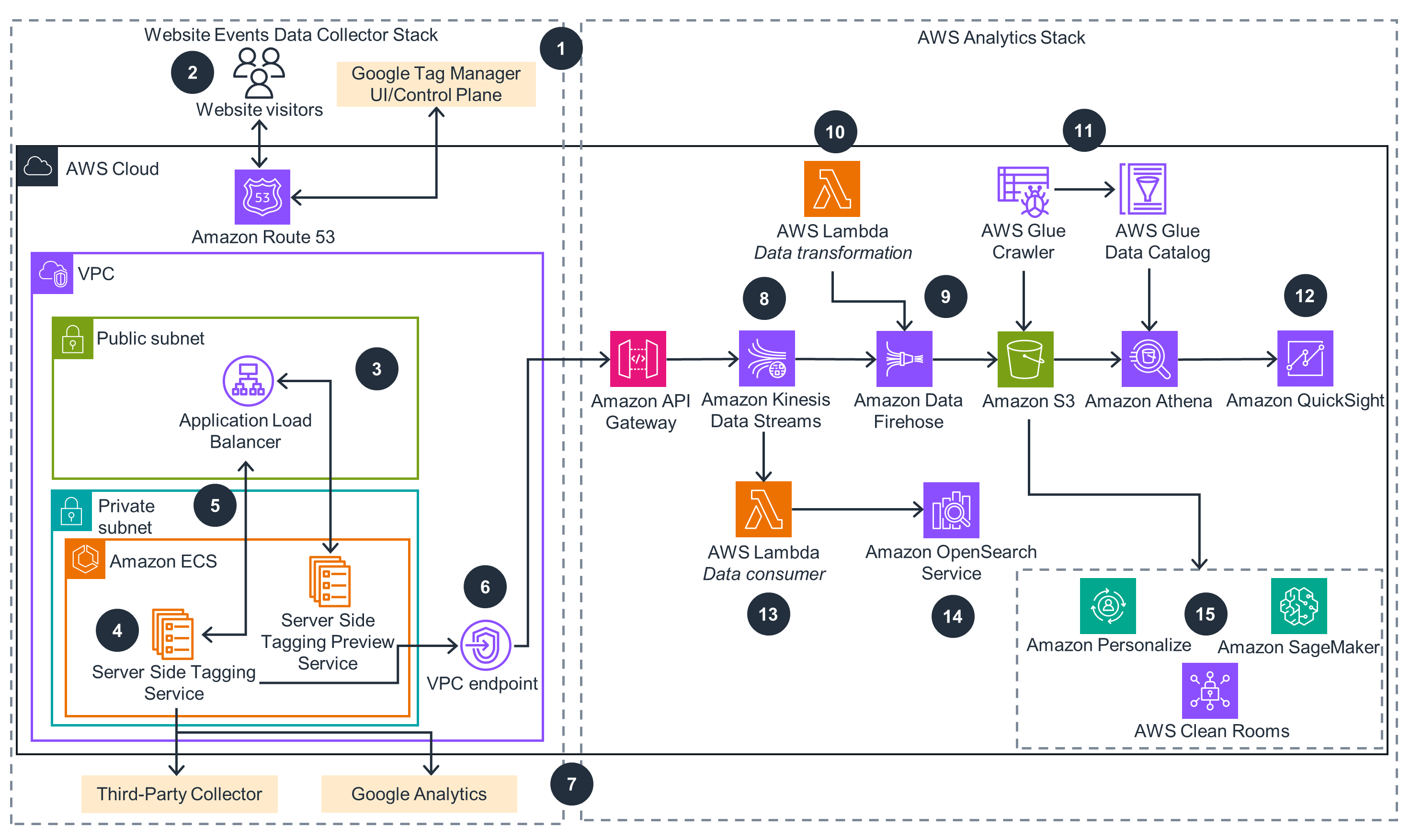
This architecture diagram demonstrates how to use Amazon API Gateway to build a near-real time website activity data collection and analytics stack on AWS with Google’s Server Side Tagging Service.
How it works
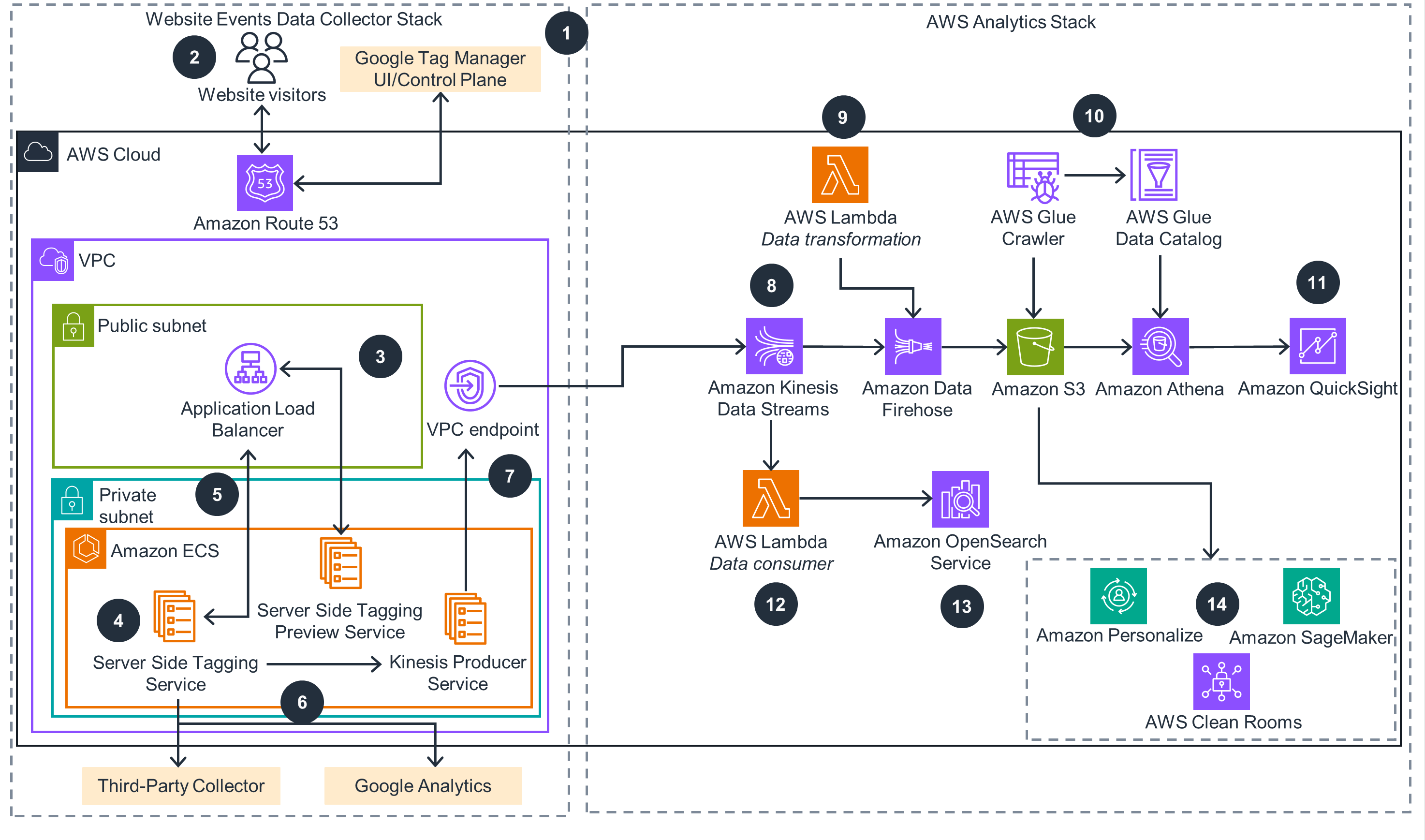
This architecture diagram demonstrates how to use Amazon Kinesis Producer Service to build a near-real time website activity data collection and analytics stack on AWS with Google’s Server Side Tagging Service.
Deploy with confidence
Everything you need to launch this Guidance in your account is right here.
We'll walk you through it
Let's make it happen
Well-Architected Pillars
The architecture diagram above is an example of a Solution created with Well-Architected best practices in mind. To be fully Well-Architected, you should follow as many Well-Architected best practices as possible.
This Guidance provides built-in observability. Each service in this Guidance publishes metrics to Amazon CloudWatch, through which you can configure dashboards and alarms. You can then use alarms or Amazon Simple Notification Service (Amazon SNS) to notify incident management systems of events and escalate based on event severity.
The data at rest in the S3 bucket is encrypted using AWS Key Management Service (AWS KMS) keys. The data in transit is encrypted and transferred over HTTPS. The Amazon ECS clusters run in an Amazon VPC. The connectivity between Amazon ECS clusters also run in Amazon VPC, and the connectivity between Amazon ECS and API Gateway is routed through a secure Amazon VPC interface endpoint.
You can use OpenSearch Service-automated snapshots for backup and recovery. You can back up Kinesis Data Firehose data to Amazon S3, and static content is stored in Amazon S3, which offers industry-leading storage durability. Amazon ECS clusters come with capabilities to stop non-responding containers and create new ones that handle incoming traffic without manual interventions.
All components of this Guidance are co-located in a single AWS Region and multiple Availability Zones. This Guidance also uses a serverless stack so that you don’t have to make infrastructure decisions about locations, aside from your choice of Region and Availability Zone. You can use automated deployments to deploy the Guidance components into any Region quickly, providing you with reduced latency and support for data residency requirements.
This Guidance uses a multi-Availability Zone deployment to support the high availability and resilience requirements for server-side tagging and the near real-time event collection workload. There will be charges for data transfer within the Region and charges for data transfer out to Google Analytics™ service and each third-party collector service. As an industry standard, we recommend estimating your data transfer out charges early on in the deployment.
All of the services used in this architecture are managed services. With Amazon ECS, you can horizontally scale and implement an elastic scaling mechanism. Additionally, by decoupling microservices within the architecture, you can scale services in a way that allocates instance types and number of instances based on the exact amount of resources used by your workloads.
Disclaimer
The sample code; software libraries; command line tools; proofs of concept; templates; or other related technology (including any of the foregoing that are provided by our personnel) is provided to you as AWS Content under the AWS Customer Agreement, or the relevant written agreement between you and AWS (whichever applies). You should not use this AWS Content in your production accounts, or on production or other critical data. You are responsible for testing, securing, and optimizing the AWS Content, such as sample code, as appropriate for production grade use based on your specific quality control practices and standards. Deploying AWS Content may incur AWS charges for creating or using AWS chargeable resources, such as running Amazon EC2 instances or using Amazon S3 storage.
References to third-party services or organizations in this Guidance do not imply an endorsement, sponsorship, or affiliation between Amazon or AWS and the third party. Guidance from AWS is a technical starting point, and you can customize your integration with third-party services when you deploy the architecture.
Did you find what you were looking for today?
Let us know so we can improve the quality of the content on our pages