AWS Public Sector Blog
Practical digital sovereignty: Navigating the pillars of compliance, continuity, and control
The concepts of digital sovereignty and sovereign cloud are gaining significant traction, especially in highly regulated sectors such as public sector, finance, telecom, and healthcare. According to the IDC report, Ten Trends That Shaped the Cloud Market in 2024, the drive for digital self-determination has become a business-critical imperative. In fact, according to IDC’s Cloud Pulse Survey (Q3 2025) shows that 93% of organizations are now operating or in the process of deploying hybrid cloud infrastructure to balance innovation with the need for data residency and operational control. These two pillars—ensuring data stays within legal borders and maintaining independent authority over system management—form the backbone of a sovereign strategy. But what exactly does digital sovereignty look like in practice, and how do you meet these evolving requirements?
In this series of blog posts, we examine digital sovereignty and provide practical steps you can apply to your Amazon Web Services (AWS) workloads and environments to address the requirements of your business. This post is the first in the series and introduces the topic, exploring the concepts and how you can practically implement them. Future posts will focus on specific topics, such as:
- How AWS can help you meet specific compliances standards, such as BSI C5, NIS2, ISO/IEC 27001, GDPR, SOC 2, NIST Cybersecurity Framework (CSF) and other such as listed here.
- How to meet sovereignty requirements for your AI and generative AI applications on AWS
- Using the AWS European Sovereign Cloud to meet compliance requirements
What is digital sovereignty?
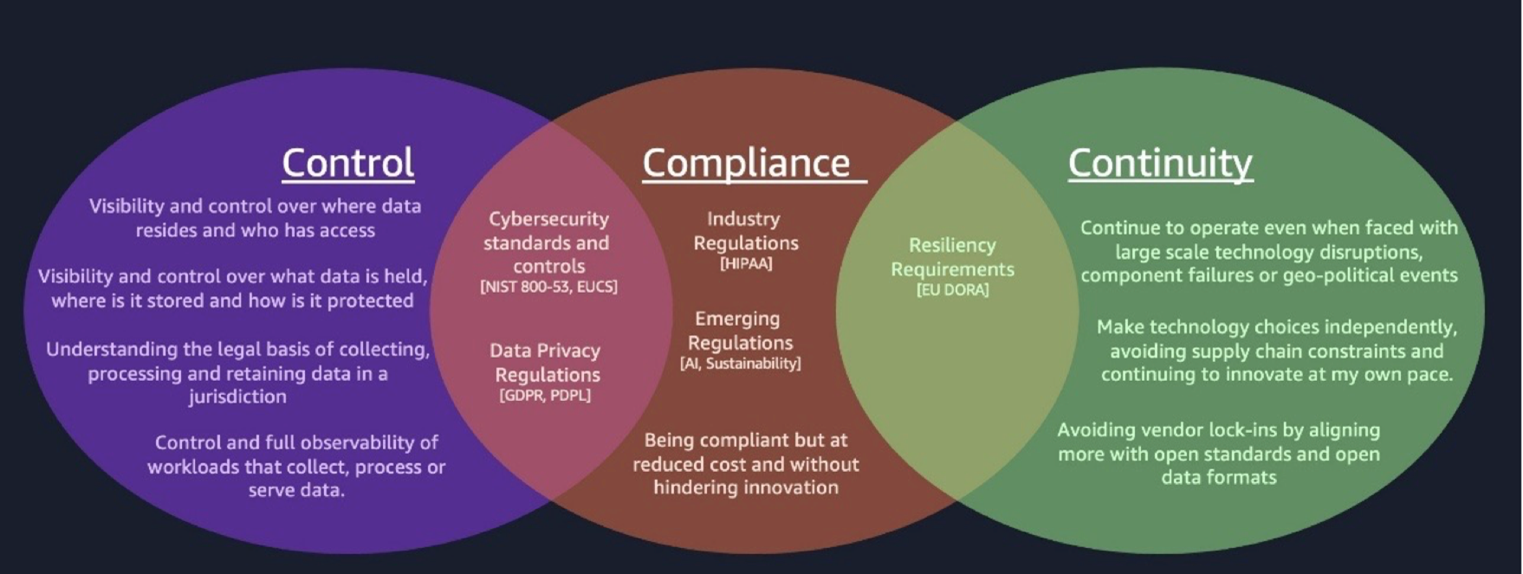
Digital sovereignty is a multifaceted concept that covers topics such as data residency, privacy, control and protection, resiliency and survivability, and independence and transparency, which can be consolidated into three pillars: control, continuity, and compliance. At its core, it’s a framework for organizations to meet data regulation requirements, maintain the security and resilience of their digital assets, and preserve control over their technology infrastructure and data. Success requires balancing these competing priorities while managing risk and cost effectively.
Control focuses on maintaining oversight of data location, protection, access, processing, and movement. Verified controls demonstrate compliance with local regulations and organizational policies. Key considerations include legal requirements for data handling (that is, collection, use, and retention), maintaining visibility over data management and protection, and ensuring observability of data-related workloads.
Continuity emphasizes business survivability and resilience against various threats, from system outages to geopolitical events and malicious actors. Organizations need to maintain critical operations, protect data, and rapidly recover in the event of disruptions. This requires comprehensive planning, redundancy, backup systems and strategies for high availability and disaster recovery.
Compliance involves adherence to cybersecurity standards, privacy regulations, industry-specific rules, and internal organizational policies. This encompasses requirements related to data residency, movement, handling, use, encryption, access controls, and auditing. Understanding what regulations must be followed requires knowing what data you have, implementing appropriate controls to manage it, establishing monitoring to verify ongoing compliance, and defining remediation mechanisms for addressing non-compliance.
The following graphic illustrates these three pillars of digital sovereignty.
Understanding your sovereignty requirements
Understanding sovereignty requirements is a foundational step before building any environment, particularly regarding workload requirements and data handling obligations. This process involves three key components: discovery, cataloging, and establishing ownership.
Organizations must first establish and understand what data they have, what data they will receive, and where this data needs to reside from a regulatory perspective. Key considerations include factors such as data sensitivity, whether the data contains personal information, applicable related data or metadata, and operator and user access requirements or restrictions. AWS Global Infrastructure offers multiple options to meet these requirements, including AWS commercial Regions, AWS Local Zones, AWS Dedicated Local Zones, AWS Outposts, and AWS AI Factories each serving different sovereignty needs.
The next step involves undertaking comprehensive data discovery and cataloging across all storage locations. This systematic approach supports proper identification and classification of data, particularly sensitive data, such personal or confidential data, and mapping of data flows, especially concerning cross-border transfers that can affect residency compliance. A centralized data catalog serves as a single source of truth, whereas clear ownership designation creates accountability through appointed data stewards who manage specific assets according to regulatory requirements.
AWS provides powerful tools to support these objectives. Amazon Macie employs machine learning (ML) to identify and classify sensitive data, which can initiate AWS Glue workflows for data anonymization when necessary. AWS Glue Data Catalog and Amazon DataZone create unified metadata repositories and business data catalogs, facilitating organization-wide discovery and sharing. Governance is maintained through AWS Identity and Access Management (IAM) for service-level access control AWS IAM Identity Center (or Amazon Cognito) for end-user authentication and authorization, AWS Organizations for centralized management, and AWS Control Tower for compliance guardrails.
Key implementation steps include:
- Using an AWS Glue crawler to discover datasets across storage locations
- Deploying Amazon Macie and AWS Glue to detect personally identifiable information (PII)
- Implementing AWS Glue Data Catalog and Amazon DataZone to create a comprehensive data catalog
This structured approach keeps data from being overlooked, particularly sensitive information that is subject to strict regulatory controls, while maintaining a centralized repository for effective data management.
Implement control (data sovereignty)
To help achieve comprehensive data sovereignty, we propose a three-step approach that organizations should develop, test, and apply controls to: establishing foundational controls, implementing specific security measures, and maintaining continuous monitoring of control effectiveness.
1. Establish a foundational control layer
Action: Establishing a robust foundational framework is essential for creating a comprehensive control layer that safeguards both environments and workloads. This critical infrastructure protects data whether it’s at rest or in transit, incorporating specialized controls for sensitive data such as PII. Additionally, the framework includes localization solutions that verify data usage complies with jurisdictional requirements and regulatory boundaries.
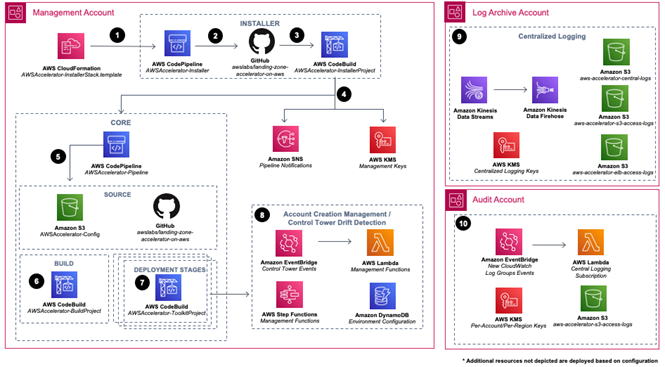
AWS implementation: Landing Zone Accelerator can help establish a layer with security, compliance, and operational capabilities. Landing Zone Accelerator uses AWS Control Tower, which orchestrates a foundational layer through AWS Organizations on which you can build proactive, preventive, and detective controls. Within AWS Control Tower, there are also a group of digital sovereignty controls that are specifically for maintaining control over your digital assets.
The following architecture diagram illustrates an example landing zone.
2. Encryption
Action: Encrypt sensitive data at rest and in transit to make sure it is protected from unauthorized access and breaches. Encrypt the data using an appropriate method such as customer managed keys or AWS managed keys. Store these keys on AWS or externally with appropriate IAM policies to protect access to the keys.
AWS implementation: AWS offers multiple encryption key management options: AWS Key Management Service (AWS KMS) for centralized control of encryption keys, AWS CloudHSM for dedicated hardware security modules meeting Federal Information Processing Standard (FIPS) 140-2 Level 3 standards, and AWS KMS external key store (XKS) for specific regulated workloads that require encryption keys to be stored and managed in an external key management system outside of AWS.
3. Define ownership and access policies
Action: Define data owners to establish accountability and proper data governance. Data owners are responsible for specific data assets, ensuring they are managed according to regulatory requirements. Set up permission structures, attributes, and roles to restrict access based on job responsibilities and security requirements.
AWS implementation: AWS Glue Data Catalog provides centralized metadata management and Amazon DataZone enables data governance through self-service data discovery and access controls. Together, they help organizations define data ownership, implement fine-grained access policies, and maintain data lineage while facilitating regulatory compliance through built-in governance frameworks.
4. Track data movement
Action: Monitor and log data movement, both across and within trust boundaries, for communications within systems, external API calls, data replication, and backups. Monitor all traffic and capture boundary crossings using gateway and firewall logs at network edges. Consider third-party document management tooling to enhance visibility.
AWS implementation: Amazon Virtual Private Cloud (Amazon VPC) Flow Logs, DNS query logs, and AWS WAF logs provide comprehensive visibility into network traffic patterns. AWS Network Firewall rules enable granular network traffic monitoring at network boundaries. These services, combined with specialized third-party monitoring tools from AWS Marketplace, create a complete data movement tracking system across trust boundaries.
5. Use standardized, automated, verifiable, and enforceable controls
Action: Manual documentation and interpretation of control requirements often lead to complexity and errors. To address this, integrate controls early into the software development and infrastructure provisioning processes rather than adding them as an afterthought. Embed preventative and proactive controls into continuous integration and continuous deployment (CI/CD) workflows to stop noncompliant resources from being deployed early and use hardware-enforced security boundaries for data processing. Complement these with detective controls and automated remediation capabilities to identify and quickly restore compliance when preventative measures are bypassed or when unforeseen events occur. This layered approach ensures that if preventative or proactive controls are compromised, detective controls provide visibility and enable rapid response.
AWS implementation: AWS provides comprehensive tools for implementing standardized, automated, and enforceable controls across cloud infrastructure. Core services include AWS Config rules for compliance monitoring, AWS CloudFormation Guard for infrastructure validation, and AWS Control Tower for custom controls implementation. AWS Security Hub provides centralized security management, AWS Audit Manager enables continuous compliance monitoring, and Amazon EventBridge detection and routing of compliance violations to trigger remediation workflows (which must be built using services like AWS Lambda, AWS Systems Manager Automation, or AWS Step Functions). These services, along with AWS Organizations and IAM for policy enforcement and AWS Nitro System for hardware-level security controls and isolation, create a robust, automated control framework providing consistent compliance across AWS offerings.
Monitor control
The final step in control is to establish full observability of workloads to maintain continuous compliance.
1. Identify and map compliance controls
Action: As a first step in Understanding your sovereignty requirements, identify and define the regulatory standards and compliance frameworks relevant to your sovereignty requirements, such as GDPR, data residency regulations, industry-specific standards, or internal organizational policies. Map these requirements to specific technical controls that must be monitored. For each compliance obligation, document the control objectives, implementation requirements, and the evidence needed to demonstrate compliance. This mapping ensures comprehensive coverage that goes beyond standard out-of-the-box compliance frameworks.
AWS implementation: AWS Audit Manager provides pre-built frameworks for many compliance standards and allows creation of custom frameworks and controls tailored to specific sovereignty requirements. AWS Config enables definition of custom Config rules to monitor organization-specific compliance requirements. Together, these services help organizations map their unique compliance obligations to measurable technical controls, whether using standard frameworks or building custom control sets for specialized sovereignty regulations.
2. Continuous monitoring
Action: Use tools and dashboards to track compliance metrics and identify potential areas of noncompliance. Automate evidence collection for audits to streamline the audit process and verify that necessary documentation is readily available.
AWS implementation: AWS Audit Manager automates evidence collection and AWS Security Hub and AWS Config provide comprehensive compliance dashboards. These integrate with Amazon EventBridge for automated notifications.
3. Identify noncompliant resources
Action: Identify noncompliant resources, the affected workloads, and the root cause. Build automation to either temporarily pause a workload or initiate immediate and scheduled remediation. For more serious incidents, such as data breaches, promptly identify and report the impact to the relevant authority for the jurisdiction.
AWS implementation: AWS Security Hub and AWS Config detect noncompliant resources. Amazon EventBridge routes compliance violations to trigger remediation workflows, which must be built using AWS Lambda functions, AWS Systems Manager Automation runbooks, or AWS Step Functions.
AWS Incident Manager, a capability of Systems Manager, coordinates breach response activities. For critical incidents, AWS Audit Manager helps track and document incidents for reporting to regulatory authorities.
4. Vendor compliance
Action: Define specific compliance requirements for vendors based on data handling, security protocols, and regional regulations. Require vendors to demonstrate compliance through certification and regular reporting on security measures. Track vendor compliance through automated monitoring tools, regular audits, and compliance dashboards.
AWS implementation: Track vendor compliance using AWS Audit Manager to define custom frameworks mapping vendor obligations to security controls and regional regulations, and to collect compliance evidence automatically. AWS Security Hub and AWS Config centralize compliance monitoring and track vendor adherence to defined standards. Create compliance dashboards in Amazon QuickSight to visualize vendor metrics and performance against SLAs. Use Amazon EventBridge with AWS Lambda to trigger notifications when vendor compliance status changes and route violations to remediation workflows.
5. Retain evidence
Action: Retain logs, such as network flow logs, usage logs, access logs, application logs, audit trails, and security findings. This practice aligns with regulatory requirements and allows analysis for prevention and investigation into regulatory compliance issues. To protect these logs, use immutable storage options and protect the chain of evidence to maintain the integrity of records.
AWS implementation: Amazon Security Lake automatically centralizes security data from AWS environments, SaaS providers, on-premises, and cloud sources into a purpose-built data lake stored in your account. Amazon CloudWatch Logs and AWS CloudTrail capture comprehensive system logs and Amazon Security Lake stores data in Amazon S3 buckets in your account, allowing you to retain control and ownership of your data. To ensure immutability and protect the chain of evidence, configure S3 Object Lock on the Security Lake S3 buckets (and other log storage buckets) using Write Once Read Many (WORM) storage. (Note: that WORM configuration must be set manually on the S3 buckets, as it is not automatically enabled by Security Lake.) Amazon Simple Storage Service Glacier (Amazon S3 Glacier) also provides additional immutable storage with vault lock policies. AWS Security Hub aggregates security findings and Amazon OpenSearch Service enables log analysis. CloudWatch Logs retention policies support compliance with regulatory requirements while maintaining log integrity and chain of custody.
Implement continuity (operational sovereignty)
Digital sovereignty demands can require operational continuity to extend beyond traditional business continuity planning. Here’s a comprehensive guide to implementing sovereign operations.
1. Survivability
Sovereignty requirements: Organizations must maintain operations during major disruptions while preserving data sovereignty. This includes responding to natural disasters, mitigating infrastructure attacks, handling geopolitical incidents, and managing service outages, all while maintaining regulatory compliance.
AWS implementation: AWS offers a suite of services to support sovereign survivability. Multi-AZ deployments provide redundancy, while Outposts enables local processing for strict data residency. AWS Control Tower and Organizations establish governance, with IAM enforcing sovereign access control. Amazon Route 53 Application Recovery Controller manages compliant failover scenarios. This blog outlines possible options for sovereign failover.
2. Resiliency
Sovereignty requirements: Resiliency focuses on managing frequent disruptions. This includes handling traffic spikes, component failures, and service degradations. Automated responses must respect jurisdictional boundaries and include auto scaling and compliant load balancing.
AWS implementation: AWS provides tools for resiliency, including AWS Auto Scaling to manage traffic spikes and Amazon Aurora Global Database and S3 Cross-Region Replication (CRR) to help keep data in defined regions. Amazon DynamoDB global tables offer distributed access within sovereign limits. EventBridge orchestrates sovereign workflows and Systems Manager automates compliant recovery procedures.
3. Operational Independence
Sovereignty requirements: Operational independence enables organizations to maintain control over critical operations. This includes processing data within jurisdictional boundaries, maintaining service levels during regional incidents, and operating independently when needed. It also requires the ability to prove compliance to regulators at any time.
AWS implementation: AWS Control Tower establishes regional governance, and Amazon CloudWatch and AWS Config provide sovereign monitoring and compliance validation. AWS Security Hub aggregates regional security findings, and AWS CloudTrail creates audit trails. Additionally, AWS operates a separate partition for Europe alongside its standard commercial partition: the AWS European Sovereign Cloud (ESC) partition, which is physically and logically separated with independent instances of critical global services, such as its own independent AWS Identity and Access Management (IAM) instance. This provides a hard boundary for identity and access control that ensures credentials and policies remain within the partition.
4. Infrastructure and data management
Sovereignty requirements: Sovereign infrastructure requires multisite deployment capabilities, support for local processing requirements, and strict data residency controls. Data management must verify that replication remains within jurisdictional boundaries and that all data access adheres to sovereign requirements.
AWS implementation: AWS offers multiple Availability Zones within all regions for redundant deployments. Local Zones provide low-latency access. AWS Outposts enable on-premises sovereign processing.
5. Recovery and testing
Sovereignty requirements: Recovery and testing in a sovereign context require automated, compliant recovery procedures, regular compliance validation, and comprehensive testing of disaster scenarios. All recovery actions must respect jurisdictional data boundaries and maintain regulatory compliance.
AWS implementation: AWS Resilience Hub provides continuous assessment of resilience posture. AWS Elastic Disaster Recovery enables failover. AWS Fault Injection Service allows testing of sovereign architectures. Systems Manager Automation and AWS Lambda enable the creation of sovereignty-aware recovery procedures.
6. Interoperability and portability
Sovereignty requirements: Organizations should prioritize system portability and interoperability to enable flexible workload deployment across different infrastructures and regions. This involves using open standards and formats, implementing single responsibility, open–closed, Liskov substitution, interface segregation, dependency inversion (SOLID) principles to reduce platform dependencies, and developing comprehensive data migration strategies. Although portability focuses on workload mobility, interoperability enables functionality across different environments. Regular testing validates these capabilities.
AWS implementation: AWS offers container services such as Amazon Elastic Container Service (Amazon ECS) and Amazon Elastic Kubernetes Service (Amazon EKS) for portable workloads, along with AWS Transfer Family for data migration. Lambda supports open standards and AWS App Runner enables platform-agnostic deployments. AWS DataSync and AWS Migration Hub facilitate seamless data and workload portability between environments.
Follow these guidelines for implementation best practices:
- Regional control: Maintain control planes, implement strict data residency controls, and design compliant failover paths.
- Sovereign operations: Deploy compliance-aware automation, maintain continuous monitoring, and document regulatory evidence.
- Future readiness: Plan sovereign migration paths and maintain operational flexibility.
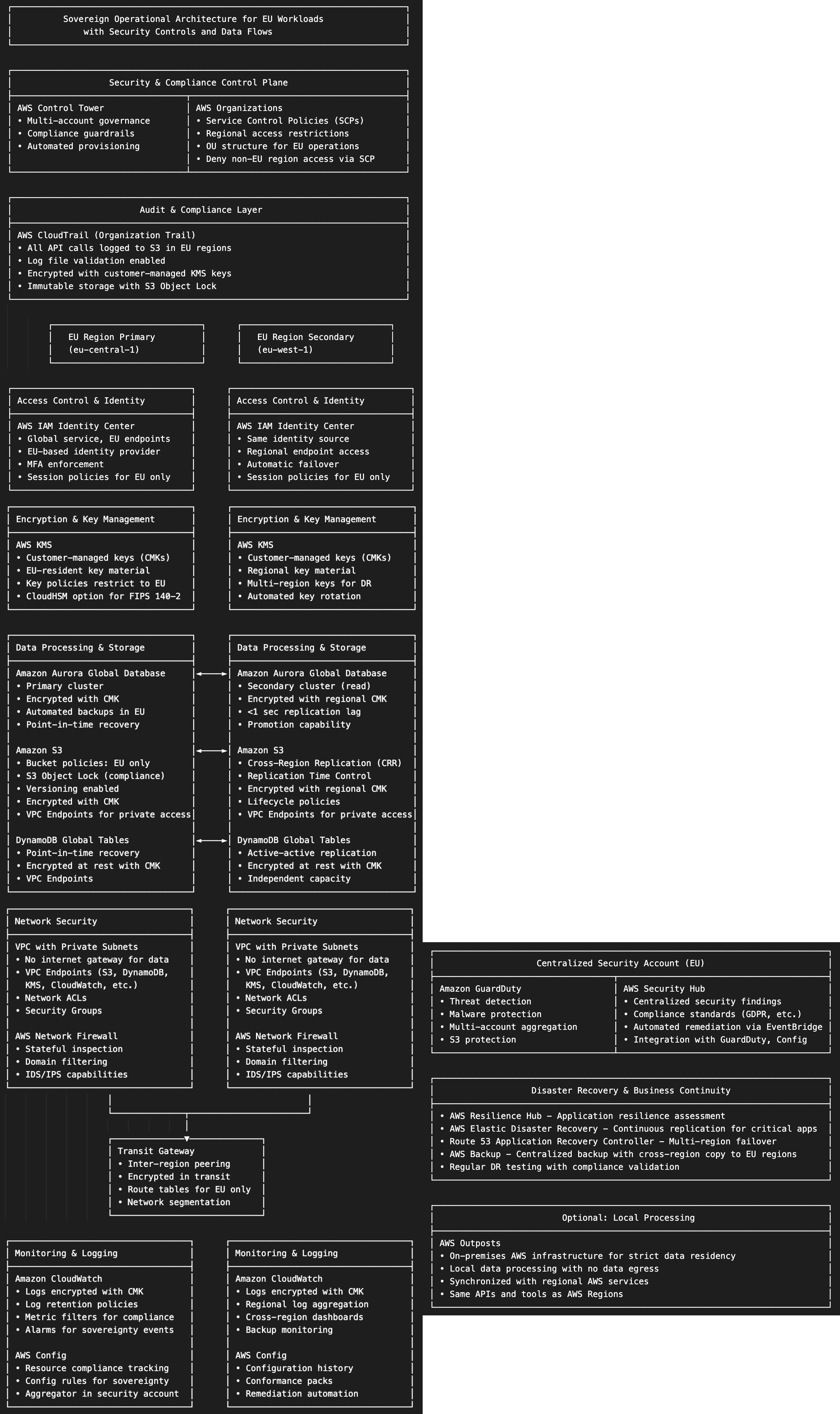
The following diagram depicts the components and their interactions, with example EU regional boundaries and data flow controls.
Concepts and implementation for compliance
Organizations must identify and understand applicable compliance requirements that apply across multiple dimensions. Regulatory frameworks, such as General Data Protection Regulation (GDPR), Health Insurance Portability and Accountability Act (HIPAA), or other regional data protection laws, establish mandatory requirements for the collection, use, storage, and transfer of personal data. Industry standards such as Payment Card Industry Data Security Standard (PCI DSS), ISO 27001, and National Institute of Standards and Technology (NIST) frameworks provide structured approaches to security and compliance, often becoming important if not formally recognized requirements in specific sectors. Service agreements, including cloud service provider terms, data processing agreements, and vendor contracts, add another layer of compliance obligations. Success requires maintaining a comprehensive compliance matrix that maps these overlapping requirements to specific controls and regularly updating it as regulations evolve. This understanding forms the foundation for implementing appropriate technical and operational measures.
A compliance matrix serves as a centralized mapping tool that aligns regulatory requirements, industry standards, and contractual obligations with organizational controls and policies. This living document identifies overlapping compliance requirements across different frameworks, eliminating redundant efforts and ensuring comprehensive coverage. The matrix should detail specific controls, responsible parties, implementation status, evidence requirements, and audit frequencies for each compliance obligation. Regular reviews and updates help keep the matrix up to date with evolving regulations and organizational changes. Organizations can use this structured approach to efficiently manage multiple compliance frameworks, identify gaps, and demonstrate compliance during audits. Rather than treating compliance as a periodic exercise, organizations should integrate it into their core processes and culture, enabling continuous compliance that reduces disruptions and maintains consistent security standards. Tools such as AWS Audit Manager can help automate the maintenance and tracking of these compliance requirements across the organization’s infrastructure.
Implementing compliance with AWS
1. Observe and remediate
Sovereignty requirements: Effective digital sovereignty compliance requires continuous automated monitoring and remediation capabilities. Organizations should implement automated tools to track compliance metrics, monitor data movement across trust boundaries, and collect audit evidence through logs and reports. This includes using VPC Flow Logs, DNS query logs, and AWS WAF logs to monitor traffic and data flows. Systems should be capable of quickly identifying noncompliant resources and automatically initiating remediation actions. For serious incidents like data breaches, automated processes should facilitate prompt reporting to relevant authorities while streamlining the return-to-compliance process.
AWS implementation: AWS Security Hub provides cloud security posture management (CSPM) by continuously monitoring security posture and generating findings based on AWS Foundational Security Best Practices (FSBP). AWS Audit Manager collects compliance evidence from AWS Config and AWS Security Hub, while AWS CloudTrail tracks user activity and API calls. For comprehensive visibility into data flows, monitor network traffic using VPC Flow Logs, Amazon Route 53 DNS query logs, and AWS WAF logs.
To detect potential data leakage and misconfigurations, use Amazon GuardDuty for threat detection, Amazon Inspector for vulnerability assessment and Amazon Detective for security investigation. Amazon Macie provides for sensitive data discovery and classification in Amazon S3, identifying where sensitive data resides and assigning sensitivity scores to buckets. For continuous monitoring of sensitive data access patterns and movement, combine Macie’s discovery findings with Amazon CloudWatch for metrics monitoring, AWS CloudTrail for API activity tracking, and VPC Flow Logs for network traffic analysis.
AWS EventBridge can orchestrate automated remediation workflows through AWS Systems Manager, AWS Lambda, and AWS Step Functions. AWS Control Tower provides governance guardrails, while AWS Organizations enables centralized compliance management across accounts.
2. Audit
Sovereignty requirements: Maintain comprehensive audit readiness by retaining critical logs (such as network flow, usage, access, application, audit trails, and security findings) in immutable storage with a protected chain of custody. Implement automated log analysis tools and establish retention periods aligned with regulatory requirements. Verify vendor compliance through clearly defined requirements, regular attestations, and automated monitoring. Conduct periodic internal audits, maintain updated compliance documentation, and implement continuous compliance monitoring. Establish a formal audit response process, including designated response teams and documented procedures. Regular compliance training and updates should be mandatory for all relevant staff.
AWS implementation: AWS Config provides detailed resource configuration history while AWS Audit Manager automates evidence collection and compliance reporting. Store audit logs immutably in Amazon S3 with S3 Object Lock and S3 Glacier for long-term retention, using S3 Lifecycle policies for cost optimization. AWS CloudTrail Lake enables searchable audit history and CloudWatch Logs provides centralized log management. Landing Zone Accelerator implements multi-account audit logging using Organizations, with centralized logging accounts and automated log aggregation. Additional services include OpenSearch Service for log analytics, AWS Lake Formation for data lake security, and AWS Backup for compliant backup retention.
3. Secure processing
Sovereignty requirements: Secure processing provides hardware-enforced security boundaries and isolation that help organizations meet strict regulatory and compliance requirements. By ensuring verifiable protection against unauthorized access and tampering during data processing, organizations can demonstrate adherence to cybersecurity standards and data protection regulations while maintaining auditable control over their processing environments.
AWS implementation: Nitro System provides hardware-level isolation and secure processing capabilities, while AWS KMS and CloudHSM enable compliant encryption key management. These services, combined with AWS Certificate Manager for secure communications, help verify that regulated workloads operate within verified, hardware-enforced security boundaries that meet compliance requirements.
The digital sovereignty stack
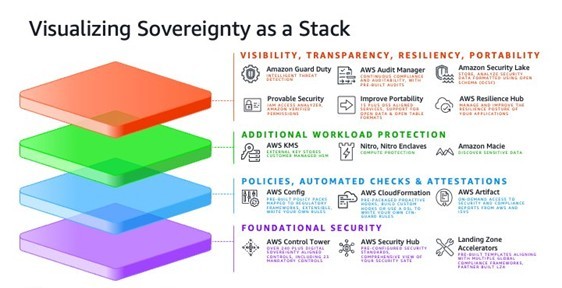
To help organizations understand the various components and capabilities required to build sovereign workloads, it’s helpful to visualize digital sovereignty as a layered stack. This stack represents the different categories of services and controls that work together to address the three pillars of digital sovereignty: control, continuity, and compliance. This stack is illustrated in the following graphic.
Conclusion and next steps
Digital sovereignty implementation requires a holistic approach encompassing control, continuity, and compliance. AWS provides comprehensive tools and services to help organizations meet these requirements while maintaining operational efficiency and security. The journey to digital sovereignty is ongoing, requiring regular assessment and updates to align with evolving regulations and business needs.
AWS customers should first understand the regulatory requirements their workloads must comply with, developing a comprehensive compliance matrix that maps these requirements to specific controls. Implementation should begin with foundational controls using AWS Control Tower and Landing Zone Accelerator, followed by establishing continuous monitoring and automated remediation workflows. Organizations should plan for data residency requirements using appropriate AWS infrastructure options, including consideration of the AWS European Sovereign Cloud for the EU’s stringent sovereignty requirements. Engaging AWS Professional Services or AWS Partners can provide valuable guidance throughout this transformation.