AWS Startups Blog
Tag: Guest Post
Why Brex Chose Elixir
Almost every engineer that starts at Brex asks, “Why are we using Elixir?” It’s a question with an interesting answer, and one that we thought a lot about before we even began building Brex.
Read MoreHow Machine Learning Fits Into Product Developement
AI picked up a lot of heat through 2017 and 2018. In what felt like an overnight rush, interest exploded, as fresh information, new techniques, new products, and new risks hit the scene. News reports came in massive waves, and businesses scrambled to figure out where AI fit into their product offerings.
Read MoreAchieving a Swiss Bank Security Level with Nummo
Like many startups today, Nummo was born in the cloud and given our industry and our future goals, we wouldn’t compromise any other aspects of our offering. People needed to feel their data is secure when using Nummo.
Read MoreWhy Snapt Built the ADC for the DevOps of Today
The need for Fast, Secure Delivery of Business-Critical Applications has never been greater: Snapt’s disruptive software-only Applications Delivery Controller (ADC) Solution ensures best performance.
Read MoreVERO Talks Through Its Migration to the Cloud
VERO’s infrastructure was hosted in a Rackspace data center in London. After facing some capacity and scalability issues with Rackspace, VERO had decided to explore external options. This migration was critical for the customer.
Read MoreWhat is an Engineering Manager?
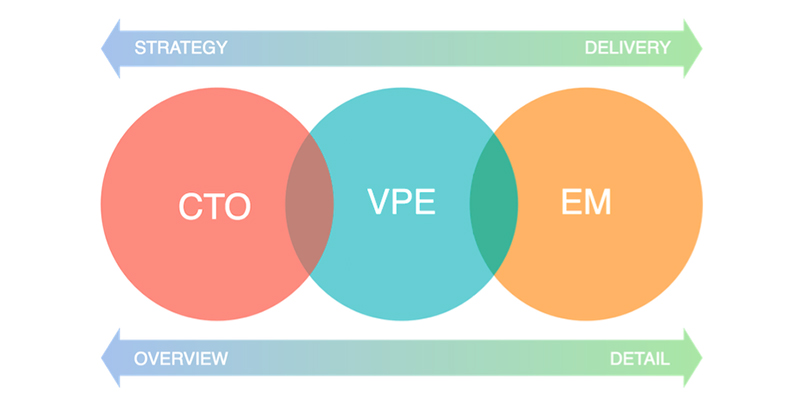
I have held many titles in the tech industry: Engineer, Lead Engineer, Head of Engineering, VP of Engineering, and CTO. You would think that each of these titles would be self-explanatory, but as I’ve transitioned from one company to another, I’ve been surprised by how differently these roles are interpreted by different organizations.
Read MoreCould This New Speech-to-Text Tech Break the Internet?
You might remember when Kim Kardashian’s 2014 Paper magazine cover boldly stated it would “Break the Internet.” All due apologies to Ms. Kardashian, but the Internet didn’t actually break as a result of her racy cover—it went on functioning normally. The truth is the Internet can’t be broken. It doesn’t work like that. Bad actors can try to cause regional disruptions, but aside from a cataclysmic event like the meteor that finished off the dinosaurs, the Internet will keep plugging along.
Read MoreEngineering the Future of 5G
If you talk to the Big Network providers—the AT&Ts, Verizons, and Vodaphones of the world—you might think that 5G was already here, or at the very least, right around the corner. On the other hand, if you talk to your average mobile RF Front-End (RFFE) engineer, he or she might tell you that 5G is a few years away. Why the discrepancy?
Read MoreUsing the Cloud to Secure the Cloud: Moving From a Network-Centric to a Cloud-First Approach
Most security solutions used by enterprises today emphasize a traditional network approach. Today’s modern organizations prize agility and transformation as underlying principles of their IT infrastructures. These enterprises that use the cloud to drive an innovative, agile business and technology agenda must adopt a security strategy that uses cloud principles to address cloud issues.
Read MoreHow Signal Media uses EC2 Spot and ECS
Every day, Signal ingests millions of documents from a growing number of publishers, including online media, print newspapers, broadcast, regulation and legislation.
Read More