Containers
Introducing The CIS Amazon EKS Benchmark
Today, we’re announcing a new Center for Internet Security (CIS) benchmark for Amazon Elastic Kubernetes Service (EKS). This new benchmark is optimized to help you accurately assess the security configuration of Amazon EKS clusters, including security assessments for nodes to help meet security and compliance requirements.
Security is a critical consideration when configuring and maintaining Kubernetes clusters and applications. Amazon EKS provides secure, managed Kubernetes clusters by default, but you still need to ensure that you configure the nodes and applications securely and meet your security and compliance requirements. The CIS Kubernetes Benchmark provides good practice guidance on security configurations for unmanaged Kubernetes clusters where you typically manage the Kubernetes cluster control plane and nodes. The benchmark does not sufficiently cover the different configuration mechanisms used by Amazon EKS. This means that if you’re using the CIS Kubernetes benchmark with EKS clusters you’re faced with false positive errors. These errors incorrectly assert your clusters are not secure or properly configured. With the CIS Amazon EKS Benchmark, you now have guidance aligned to the Amazon EKS cluster configuration and you should use this benchmark to assess and configure security for your cluster nodes. You may use the recently published Amazon EKS Best Practices Guide for Security in conjunction with the CIS Amazon EKS Benchmark that we announce today.
The latest version of CIS Kubernetes Benchmark v1.5.1 provides guidance on security configurations for Kubernetes versions v1.15 for unmanaged Kubernetes clusters. The CIS Kubernetes Benchmark is scoped for implementations managing both the control plane, which includes etcd, API server, controller and scheduler, and the data plane, which is made up of one or more nodes. As Amazon EKS provides a fully managed control plane, not all of the recommendations from the CIS Kubernetes Benchmark are applicable as you are not responsible for configuring or managing the control plane. To ensure this scope is reflected with implementation specifics of Amazon EKS, we created the CIS Amazon EKS Benchmark starting from the CIS Kubernetes Benchmark and with the input of the community around specific configuration considerations for EKS clusters.
Understanding The Shared Responsibility Model For Amazon EKS
To best understand the changes introduced with the CIS EKS Benchmark, it helps to start with understanding the AWS Shared Responsibility Model and how it applies to Amazon EKS clusters. When using Amazon EKS, security and compliance are considered shared responsibilities. In the shared responsibility model, AWS is responsible for security “of” the cloud whereas you, the customer, are responsible for security “in” the cloud. With Amazon EKS, this means that AWS is responsible for managing the Kubernetes control plane including the Kubernetes API server, controller manager, scheduler, etcd datastore, and other infrastructure necessary for AWS to deliver a secure and reliable service. As an Amazon EKS user you are responsible for managing IAM users/roles and identity/resource-based policies, define and enforce node and pod security, runtime security, network security, configuring secrets encryption, and configuration recommendations described in the benchmark and EKS best practices guide for security.
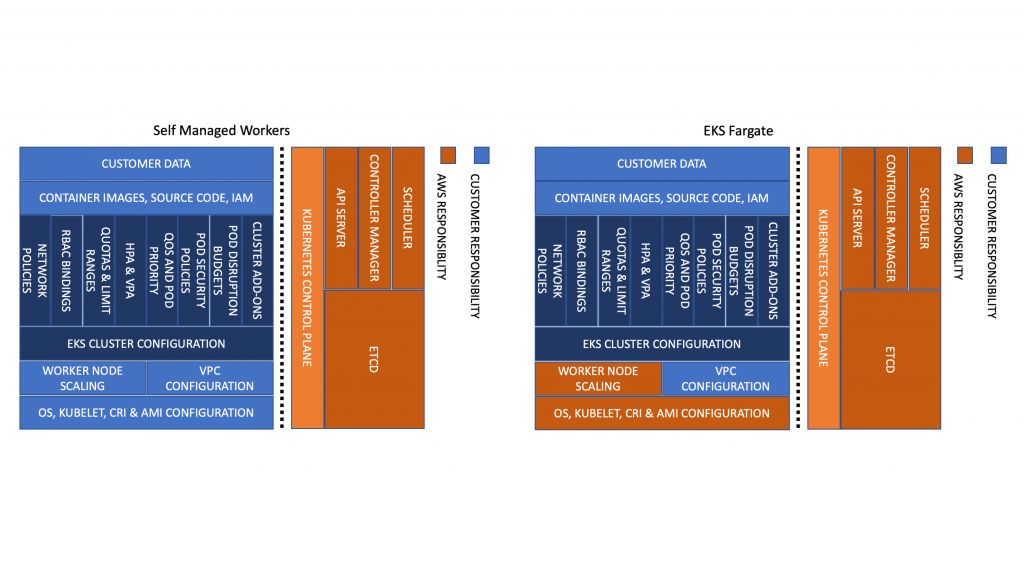
Figure 1. The AWS shared responsibility Model for Amazon EKS using self managed nodes and AWS Fargate.
For infrastructure security, AWS assumes additional responsibilities as you move from self-managed Kubernetes worker nodes, to managed node groups, to Fargate. For example, as shown in Figure 1 above, when using EKS Fargate we take on the additional responsibility for securing the underlying infrastructure used to run your pods.
CIS Benchmarks And Kubernetes Versions
We used the CIS Kubernetes Benchmark as the starting point for the CIS Amazon EKS Benchmark we developed in and with the CIS community. In below table we provide you with a mapping of the current (and upcoming) versions of the generic CIS Kubernetes Benchmark and the scope to the non-managed Kubernetes clusters from versions 1.15 to 1.18:
| CIS Kubernetes Benchmark version | Kubernetes version scope |
| 1.5.1 (current) | 1.15 |
| 1.6.0 (upcoming publication) | 1.16 |
| 1.17 | |
| 1.18 |
The newly developed CIS Amazon EKS Benchmark in version 1.0.0 provides guidance for node security configurations for EKS clusters, aligning with CIS Kubernetes Benchmark v1.5.1 (and upcoming v1.6.0). The EKS Benchmark is applicable to EC2 nodes (both managed and self managed) where you’re responsible for security configurations of Kubernetes components. This benchmark is, however, not applicable to Amazon EKS on AWS Fargate as you do not own or manage Kubernetes component configurations when using AWS Fargate. Additionally, this benchmark is not applicable to nodes’ operating system level security configuration as this is outside the scope for the CIS Kubernetes Benchmark. You may want to refer to the CIS Amazon Linux 2 Benchmark for further reference on applicable security controls for Amazon Linux 2 images. More information on nodes, available AMIs, and updates can be found in the EKS documentation.
The CIS Amazon EKS Benchmark covers all Amazon EKS supported Kubernetes versions. The newly announced CIS Amazon EKS Benchmark supports the currently available Kubernetes versions from 1.15 to 1.17 due to the scope of controls applicable to managed Kubernetes services.
| CIS Amazon EKS Benchmark version | Supported Kubernetes versions |
| 1.0.0 | 1.15 |
| 1.16 | |
| 1.17 |
With that out of the way, let’s have a look at how to use the new benchmark.
Using The CIS Benchmark
The CIS Amazon EKS Benchmark is available on the CIS website:
- Go to the full list of CIS Benchmarks.
- On the CIS Benchmarks page, click ‘Access all Benchmarks’.
- Complete the form to access the free download link to the CIS Amazon EKS Benchmark.
The CIS Amazon EKS Benchmark consists of four sections on control plane logging configuration (section 2), node security configurations (section 3), policies (section 4) and managed services (section 5). The CIS Kubernetes Benchmark committee agreed to remove controls for the appropriate control plane components (section 1) recommendations for managed Kubernetes cluster services. Within section 2, you will find guidance for Amazon EKS control plane logging configuration. In section 3, we describe configuration checks for the worker node configuration files and kubelet. Section 4 describes recommendations for various Kubernetes policies which are important to the security of Amazon EKS customer environment, and section 5 consists of security recommendations for Amazon EKS.
Getting Started With The Benchmark In EKSworkshop.com
The EKS workshop is an open source initiative we maintain and you can contribute as well. Starting today, we published a tutorial chapter on eksworkshop.com for CIS EKS Benchmark allowing you to run the benchmark against the tools available to help assess security configurations and expected results. In the new chapter named “CIS Amazon EKS Benchmark Assessment using kube-bench” on eksworkshop.com, we present step-by-step instructions to assess Amazon EKS cluster nodes against the CIS Amazon EKS Benchmark. As Amazon EKS and CIS Kubernetes Benchmark versions evolve in relation to Kubernetes versions, we will continue to publish hands-on guidance for you to assess your Amazon EKS node security configurations.
Using kube-bench
As part of a Continuous Delivery pipeline or for one-off CLI runs you can use kube-bench to assess node security configurations. Kube bench is an open source application that runs configuration checks against CIS Kubernetes Benchmark recommendations. It is developed and maintained by Aqua Security, an AWS Advanced Technology Partner.
Liz Rice, VP Open Source Engineering at Aqua Security and CNCF Technical Oversight Committee chair, tested the feature and published a video walkthrough demonstrating the use of kube-bench with the CIS Amazon EKS Benchmark:
Now that you have an idea how to use the CIS Amazon EKS Benchmark, let us discuss the next planned steps and how you can shape the future of the benchmark.
Next Steps And Contributions
Starting today, you can use the CIS Amazon EKS Benchmark to accurately assess the security configuration of Amazon EKS cluster nodes. We will continue to iterate the benchmark for updates and changes based on the inputs from the CIS Kubernetes Benchmark committee and the product and engineering teams.
If you are interested in related guidances, check out the following AWS benchmarks:
- CIS Amazon Web Services Foundations Benchmark
- CIS Amazon Web Services Three-tier Web Architecture Benchmark
- CIS Amazon Linux Benchmark
- CIS Amazon Linux 2 Benchmark
- CIS Amazon Linux 2 STIG Benchmark
We hope you find CIS Amazon EKS Benchmark useful to assess security configurations of your Amazon EKS cluster nodes and meet your compliance requirements and welcome your feedback via our containers roadmap or through direct participation in the CIS Kubernetes Benchmark project.