AWS News Blog
Category: Compute
AWS Week in Review – September 19, 2022
Things are heating up in Seattle, with preparation for AWS re:Invent 2022 well underway. Later this month the entire News Blog team will participate in our now-legendary “speed storming” event. Over the course of three or four days, each of the AWS service teams with a launch in the works for re:Invent will give us […]
New – Direct VPC Routing Between On-Premises Networks and AWS Outposts Rack
Today, we announced direct VPC routing for AWS Outposts rack. This enables you to connect Outposts racks and on-premises networks using simplified IP address management. Direct VPC routing automatically advertises Amazon Virtual Private Cloud (Amazon VPC) subnet CIDR addresses to on-premises networks. This enables you to use the private IP addresses of resources in your […]
AWS Week In Review – September 12, 2022
I am working from London, UK, this week to record sessions for the upcoming Innovate EMEA online conference—more about this in a future Week In Review. While I was crossing the channel, I took the time to review what happened on AWS last week. Last Week’s Launches Here are some launches that got my attention: […]
AWS Week in Review – September 5, 2022
This post is part of our Week in Review series. Check back each week for a quick roundup of interesting news and announcements from AWS! As a new week begins, let’s quickly look back at the most significant AWS news from the previous seven days. Last Week’s Launches Here are the launches that got my […]
AWS and VMware Announce VMware Cloud on AWS integration with Amazon FSx for NetApp ONTAP
Update (10/20/2023): Information in this article was corrected. A previous version incorrectly stated that supplemental datastore support for Amazon FSx for NetApp ONTAP was available in AWS GovCloud (US-East), and AWS GovCloud (US-West). Our customers are looking for cost-effective ways to continue to migrate their applications to the cloud. VMware Cloud on AWS is a […]
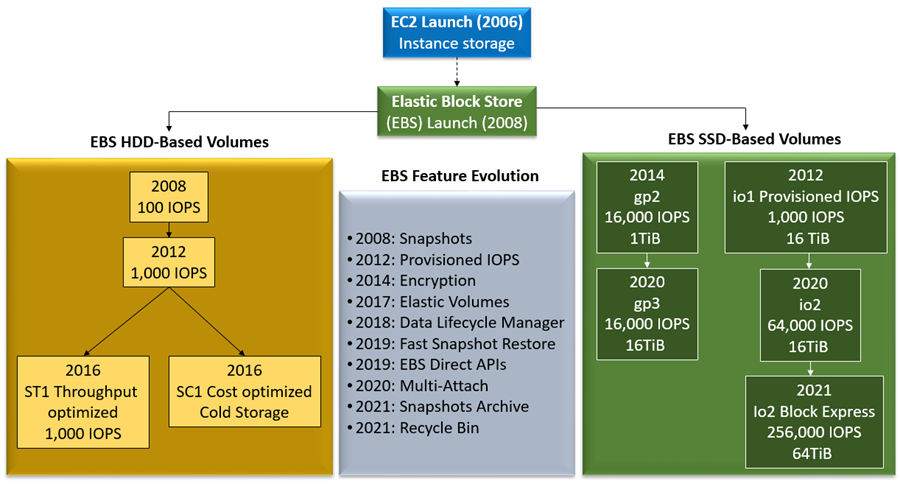
A Decade of Ever-Increasing Provisioned IOPS for Amazon EBS
Progress is often best appreciated in retrospect. It is often the case that a steady stream of incremental improvements over a long period of time ultimately adds up to a significant level of change. Today, ten years after we first launched the Provisioned IOPS feature for Amazon Elastic Block Store (Amazon EBS), I strongly believe […]
AWS Week in Review – August 8, 2022
As an ex-.NET developer, and now Developer Advocate for .NET at AWS, I’m excited to bring you this week’s Week in Review post, for reasons that will quickly become apparent! There are several updates, customer stories, and events I want to bring to your attention, so let’s dive straight in! Last Week’s launches .NET developers, […]
Graviton Fast Start – A New Program to Help Move Your Workloads to AWS Graviton
With the Graviton Challenge last year, we helped customers migrate to Graviton-based EC2 instances and get up to 40 percent price performance benefit in as little as 4 days. Tens of thousands of customers, including 48 of the top 50 Amazon Elastic Compute Cloud (Amazon EC2) customers, use AWS Graviton processors for their workloads. In […]