AWS News Blog
Federated Users and Temporary Security Credentials for AWS CloudFormation
My colleague Chetan Dandekar brings word of a powerful enhancement to AWS CloudFormation that will make it an even better fit for large-scale corporate deployments.
— Jeff;
AWS CloudFormation gives developers and systems administrators an easy way to create and manage a collection of AWS resources. Today, we added support for the CloudFormation APIs to be called using temporary security credentials provided by the AWS Security Token Service.
This enables a number of scenarios such as federated users using CloudFormation and authorizing Amazon EC2 instances with IAM roles to call CloudFormation. Before this launch, calling CloudFormation required use of an IAM user or AWS account credentials.
AWS supports federated user access to AWS service APIs and resources. Federated users are managed in an external directory and are granted temporary access AWS services. You now have the option of authorizing federated users to call AWS CloudFormation APIs, as an alternative to creating IAM users to use CloudFormation. A federated user can also sign in and manage CloudFormation stacks from the AWS Management Console (if interested, here is a sample proxy server that demonstrates setting this up).
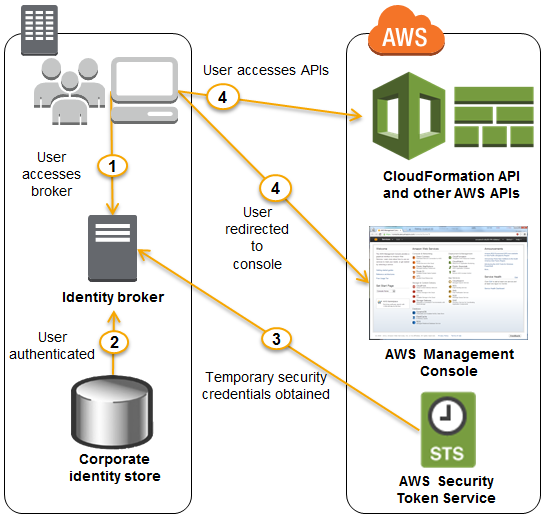
Consider an example where you have a 100 person IT department. The department would likely have specialists such as network architects, database admins, and application developers. Since CloudFormation enables you to model and provision infrastructure as well as applications, many of those specialists would need access to CloudFormation. Now, the IT department does not have to create an IAM user for each of those employees in order to access CloudFormation. You can choose to authorize existing federated users to use CloudFormation. Also, the IT department can fine tune access, for instance, by authorizing the database admins to call CloudFormation and Amazon RDS, while authorizing the application developers to call CloudFormation, and EC2 or AWS Elastic Beanstalk. Furthermore, when members join or leave the IT department, you do not need to add or remove corresponding IAM users. The following diagram shows the flow of a federated user calling CloudFormation:
IAM roles enable easy and secure access to AWS APIs from EC2 instances, without sharing the long-term security credentials (i.e., access keys). The CloudFormations Describe* APIs can already be called using temporary security credentials generated by assuming an IAM role. We now support the complete set of CloudFormation APIs.
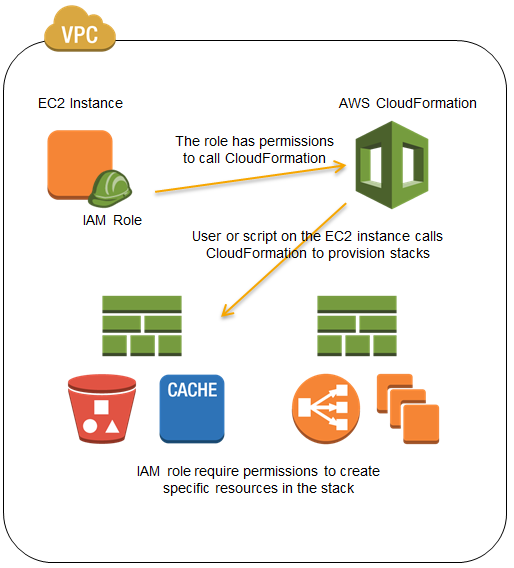
Consider an example where you have a regulatory requirement to perform all AWS resource provisioning and management operations from within an Amazon VPC. One approach to comply would be to provision an EC2 instance inside a VPC, which in turn calls the CloudFormation service to provision and manage infrastructure and applications using your CloudFormation templates. You can now use an IAM role to define permissions that allow calling CloudFormation, and delegate those permissions to the EC2 instance. IAM roles use temporary security credentials and take care of rotating credentials on the instance for you. Here is a visualization of this scenario:
To learn more about the AWS CloudFormation, visit the CloudFormation detail page, documentation or watch this introductory video. We also have a large collection of sample templates that makes it easy to get started with CloudFormation within minutes.
— Chetan Dandekar, Senior Product Manager