AWS News Blog
New – Server-Side Encryption for Amazon Simple Queue Service (SQS)
As one of the most venerable members of the AWS family of services, Amazon Simple Queue Service (Amazon SQS) is an essential part of many applications. Presentations such as Amazon SQS for Better Architecture and Massive Message Processing with Amazon SQS and Amazon DynamoDB explain how SQS can be used to build applications that are resilient and highly scalable.
Today we are making SQS even more useful by adding support for server-side encryption. You can now choose to have SQS encrypt messages stored in both Standard and FIFO queues using an encryption key provided by AWS Key Management Service (AWS KMS). You can choose this option when you create your queue and you can also set it for an existing queue.
SSE encrypts the body of the message, but does not touch the queue metadata, the message metadata, or the per-queue metrics. Adding encryption to an existing queue does not encrypt any backlogged messages. Similarly, removing encryption leaves backlogged messages encrypted.
Creating an Encrypted Queue
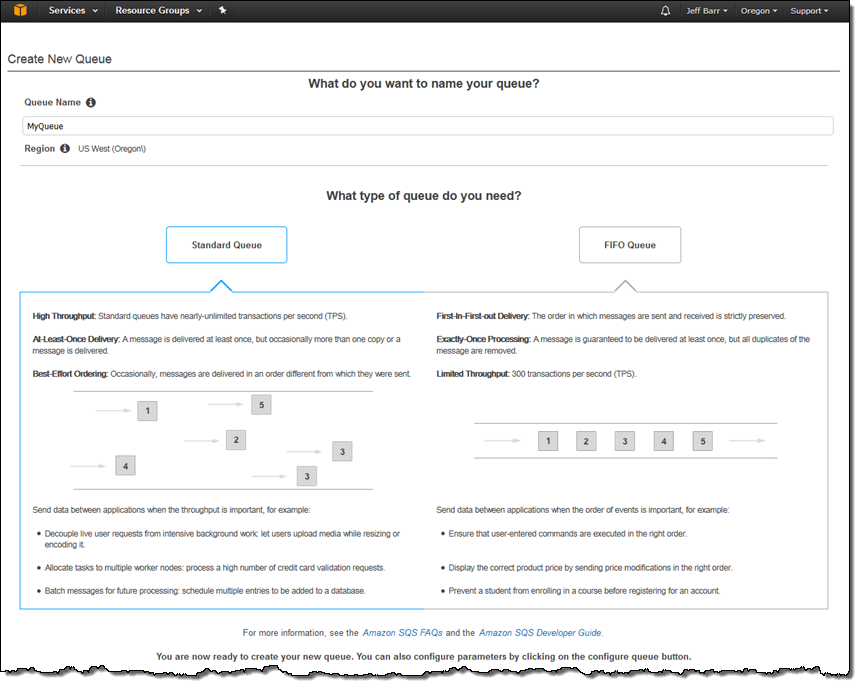
The newest version of the AWS Management Console allows you to choose between Standard and FIFO queues using a handy graphic:
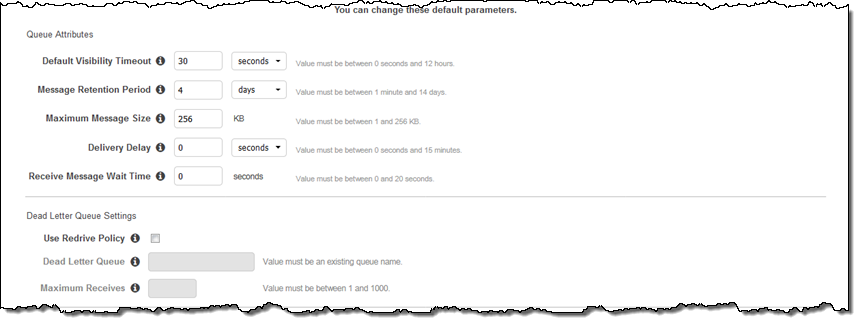
You can set the attributes for the queue and the optional Dead Letter Queue:
And you can now check Use SSE and select the desired key:
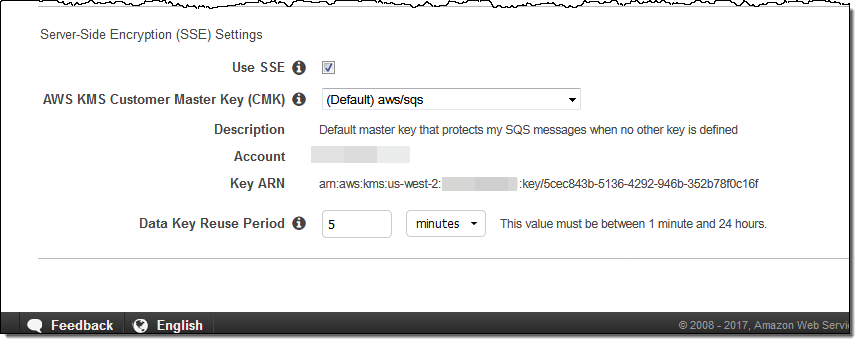
You can use the AWS-managed Customer Master Key (CMK) which is unique for each customer and region, or you can create and manage your own keys. If you choose to use your own keys, don’t forget to update your KMS key policies so that they allow for encryption and decryption of messages.
You can also configure the data reuse period. This interval controls how often SQS refreshes cryptographic information from KMS, and can range from 1 minute up to 24 hours. Using a shorter interval can improve your security profile, but increase your KMS costs.
To learn more, read the SQS SSE FAQ and the documentation for Server-Side Encryption.
Available Now
Server-side encryption is available today in the US West (Oregon) and US East (Ohio) Regions, with support for others in the works.
There is no charge for the use of encryption, but you will be charged for the calls that SQS makes to KMS. To learn more about this, read How do I Estimate My Customer Master Key (CMK) Usage Costs.
— Jeff;