AWS News Blog
The New AWS Security Blog
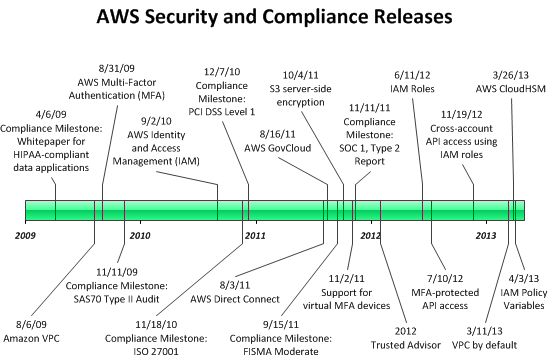
The AWS team works non-stop to improve the security of our services. As you can see from the timeline below, many of our recent releases have made it easier for you to secure your cloud resources.
The new AWS Security Blog is your one-stop shop for best practices, how-to guides, customer stories, and more. Like the existing Java, Mobile, and Ruby blogs, the AWS Security Blog focuses on a single topic. We are thinking about creating other blogs of this type; please leave a comment to suggest a topic.
Here’s a timeline of the most recent security and compliance releases:
The following table provides more detail:
| Date | Security or Compliance Event | Description |
| 4/3/13 | IAM Policy Variables | Create policies containing variables that will be dynamically evaluated using context from the authenticated user’s session. |
| 3/26/13 | AWS CloudHSM | Use dedicated Hardware Security Module (HSM) appliances within the AWS Cloud. |
| 3/11/13 | VPC by default | EC2 instances will be launched in a VPC for new customers. |
| 11/19/12 | Cross-account API access using IAM roles | Delegate temporary API access to AWS services and resources within your AWS account without having to share long-term security credentials. |
| 7/10/12 | MFA-protected API access | Enforce MFA authentication for AWS service APIs via AWS Identity and Access Management (IAM) policies. |
| 6/11/12 | IAM Roles | Simplifies the process for your applications to secure access AWS service APIs from EC2 instances. |
| 1/30/12 | AWS Trusted Advisor | Self-service access to proactive alerts that identify opportunities to save money, improve system performance, or close security gaps. |
| 11/11/11 | Compliance Milestone: SOC 1, Type 2 Report | |
| 11/2/11 | Support for virtual MFA devices | Use your existing smartphone, tablet, or computer running any application that supports the open TOTP standard. |
| 10/4/11 | S3 server-side encryption | Request encrypted storage when you store a new object in Amazon S3 or when you copy an existing object. |
| 9/15/11 | Compliance Milestone: FISMA Moderate | |
| 8/16/11 | AWS GovCloud | AWS Region designed to allow US government agencies and customers to move more sensitive workloads into the cloud by addressing their specific regulatory and compliance requirements. |
| 8/3/11 | AWS Direct Connect | Enables you to bypass the public Internet when connecting to AWS. |
| 12/7/10 | Compliance Milestone: PCI DSS Level 1 | |
| 11/18/10 | Compliance Milestone: ISO 27001 | |
| 9/2/10 | AWS Identity and Access Management (IAM) | Enables you to securely control access to AWS services and resources for your users. |
| 11/11/09 | Compliance Milestone: SAS70 Type II Audit | |
| 8/31/09 | AWS Multi-Factor Authentication (MFA) | Provides an extra level of security that you can apply to your AWS environment. |
| 8/26/09 | Amazon VPC | Provision a logically isolated section of the Amazon Web Services (AWS) Cloud where you can launch AWS resources in a virtual network that you define. |
| 4/6/09 | Compliance milestone: whitepaper for HIPAA-compliant data applications |
Check out the AWS Security Blog and let us know what you think.
— Jeff;