Integration & Automation
Recap: Five ways custom resources help your automated deployments
When you build automated deployments for the Amazon Web Services (AWS) Cloud, custom resources can give you more flexibility. Using custom resources, you can extend the AWS CloudFormation templates. The following five blog posts investigate different ways that you can create custom resources to enhance your deployments from start to stack cleanup.
- Speed up instance bootstrapping by using dynamically created images
- AWS CloudFormation custom resource creation with Python, AWS Lambda, and crhelper
- Deploying AWS Lambda functions using AWS CloudFormation (the portable way)
- Multiple-account, multiple-Region AWS CloudFormation
- Scheduling automatic deletion of AWS CloudFormation stacks
For a few more details, see the following summaries.
Custom resources for spinning up instances
Speed up instance bootstrapping by using dynamically created images — When working with relatively large binary downloads, you might experience a noticeable lag. To avoid this, you can use a custom resource to invoke an AWS Lambda function that builds an Amazon Machine Image (AMI) of the Amazon Elastic Compute Cloud (Amazon EC2) instance.
AWS CloudFormation custom resource creation with Python, AWS Lambda, and crhelper — Follow the steps in this post to write custom resources that extend AWS CloudFormation beyond AWS resources. Using these custom resources, you can then provision other resources, including third-party software as a service (SaaS) products. You can also provide utility resources that transform or process infrastructure properties.
Custom resources for cross-account support
Deploying AWS Lambda functions using AWS CloudFormation (the portable way) — When using AWS CloudFormation to deploy Lambda functions, you want your deployments to be available in all AWS Regions that are supported by Lambda. However, Lambda requires the bucket for its zip files to reside in the same Region as the function. This post covers three patterns to address this challenge and discusses the benefits of each approach.

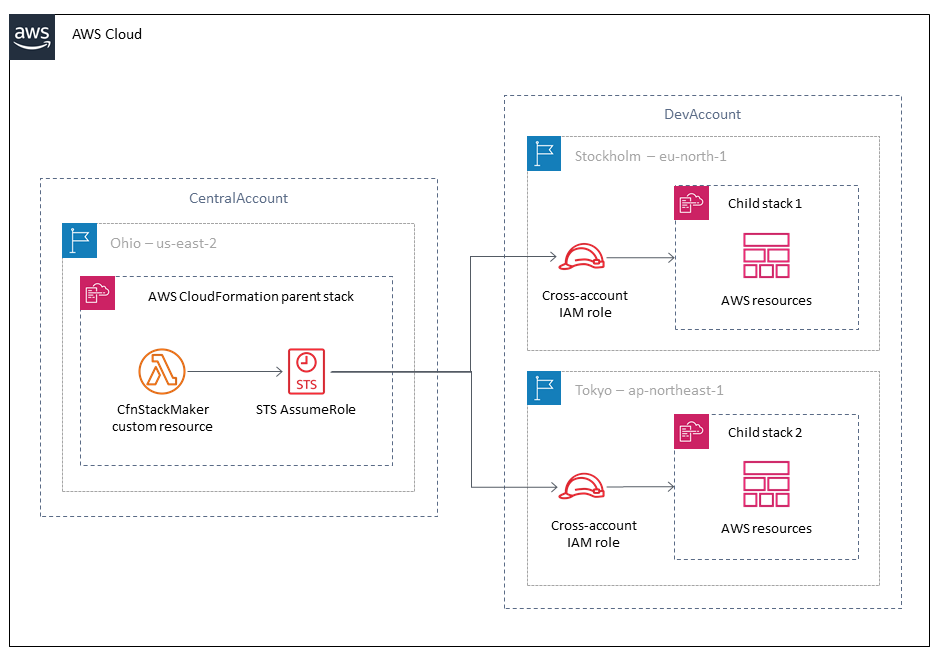
Multiple-account, multiple-Region AWS CloudFormation — AWS CloudFormation supports nested stacks, so you can reuse components and separate groups of resources. But what if you don’t want the child stack in the same account or Region as the parent stack? Learn how to use a custom resource that allows your customers to specify a target account, Region, and AWS Identity and Access Management (IAM) role for their child stacks.
A custom resource for automating stack cleanup
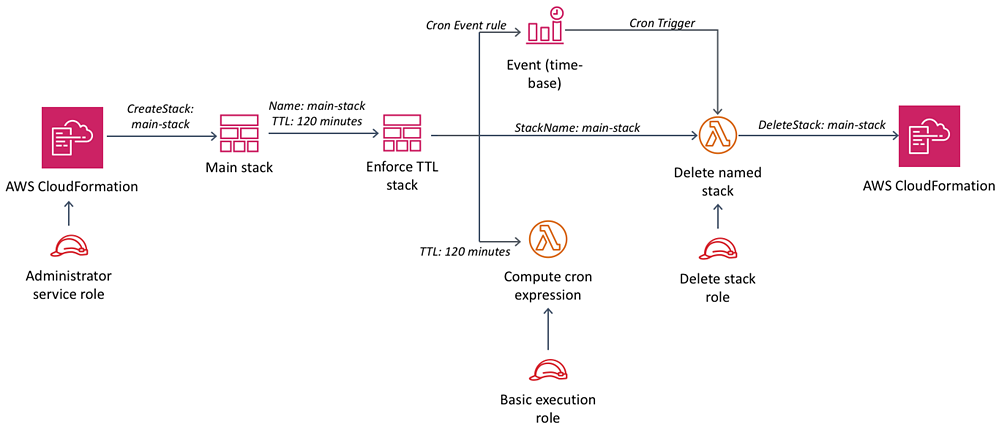
Scheduling automatic deletion of AWS CloudFormation stacks — When you set up a temporary CloudFormation stack for testing, wouldn’t it be handy to have that stack automatically delete? That would save you from needing to remember or incurring additional costs. This post shows you how to use a cron expression and a Lambda function to build an automatic delete time frame into your stack.
I hope that you find these custom resource scenarios helpful when building your own automated deployments. Visit the Infrastructure & Automation blog for more tips and tricks on building Quick Starts and other automation tools for the AWS Cloud.