Front-End Web & Mobile
Amplify Framework adds authentication features and enhancements for iOS and Android Mobile SDKs
June 27, 2024: This blog post covers Amplify Gen 1. For new Amplify apps, we recommend using Amplify Gen 2. You can learn more about Gen 2 in our launch blog post.
Authentication and authorization play a key role in mobile development. The AWS Amplify team has been busy improving on the previous simplified development changes for iOS and Android that introduced user state tracking, token management, and offline enhancements.
Based on your feedback, we’ve added new features and have made improvements to the way you add and configure authentication to your native mobile apps.
Here are a few of the latest additions and enhancements to authentication for native iOS and Android developers, starting with the AWS Mobile SDK for iOS 2.9.3 and AWS Mobile SDK for Android 2.12.15.
« (NEW) API operations for tracking and remembering devices »
Before covering the new API operations, let’s go over how the “remembering devices” feature works. When you’re using user pools with multi-factor authentication (MFA) enabled, you have the option to remember the authenticated users’ devices. What does this mean? With MFA, the user typically needs to provide a second form of authentication whenever their token expires, which requires them to reauthenticate.
When you set user pools to remember users’ devices, users no longer need to provide an additional MFA code for each authenticated session from that device. If they sign in to another device, they’re prompted to provide an additional MFA that one time. This is similar to the “remember me” option that you see when you authenticate on websites. In addition to enhancing the MFA feature, remembering devices can also be used to limit the number of logged-in devices for a single user. This is how airline or hotel Wi-Fi might limit the number of devices per user.
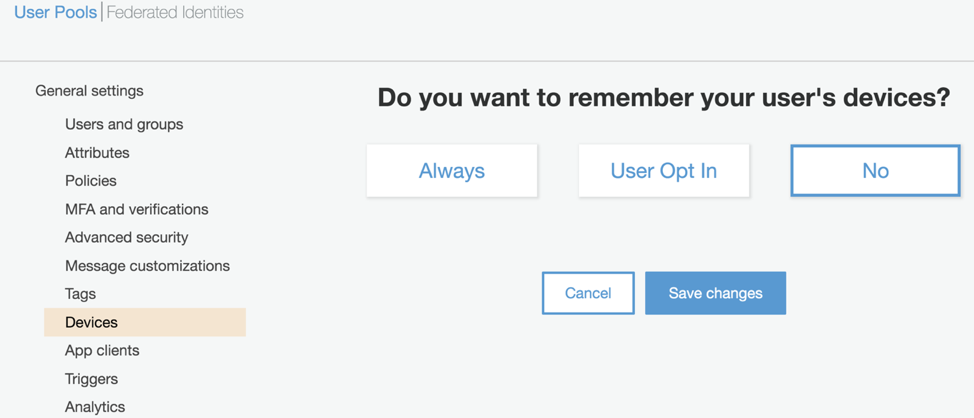
The Amazon Cognito user pools default configuration is set to No. The options available from the Amazon Cognito console are Always, User Opt In, and No (default).
Now, new API operations are available through the AWS Mobile SDKs for iOS and Android that enable your users to opt in to remembering their devices when they authenticate. Remembering devices is a great feature for users because they don’t have to send additional MFA codes each time they authenticate. It’s also helpful for you as a developer as a cost savings, because you send fewer SMS or email MFA codes to each user.
Here’s how the new API operations work from the mobile SDK:
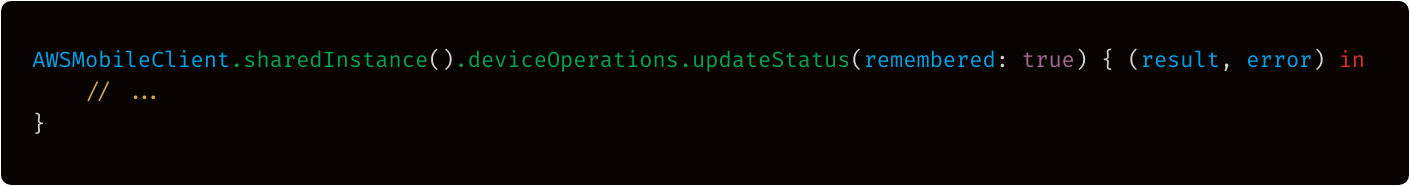
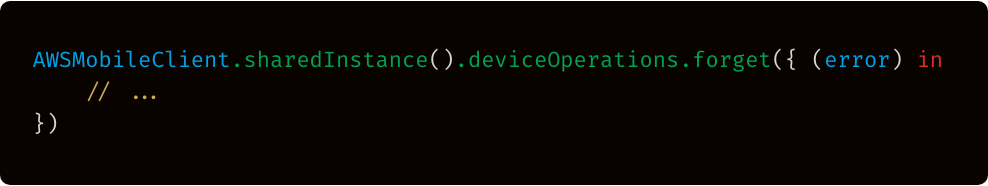
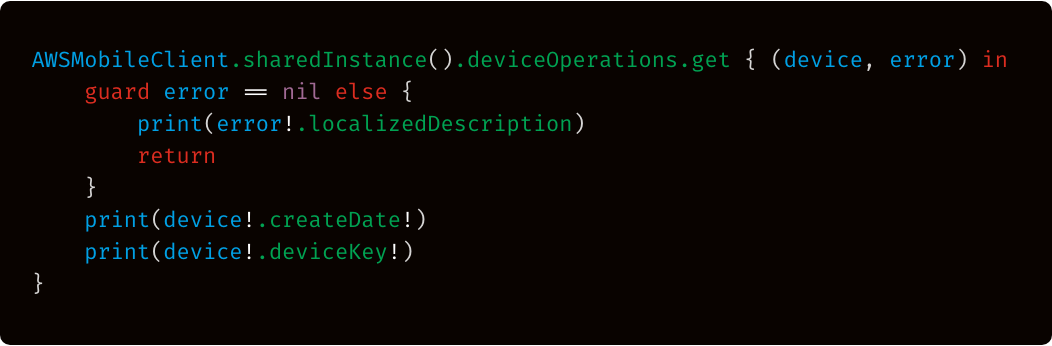
From the device, users can now choose to remember the current device, or not. Or they can choose to forget the device. You can choose whether to make this option available to the user. Here’s a snippet of code for the new API operations:
Remember Device > This option will mark the tracked device as remembered. Set false for not remember.
Forget Device > This option will stop tracking the device altogether.
Get device details of currently authenticated user.
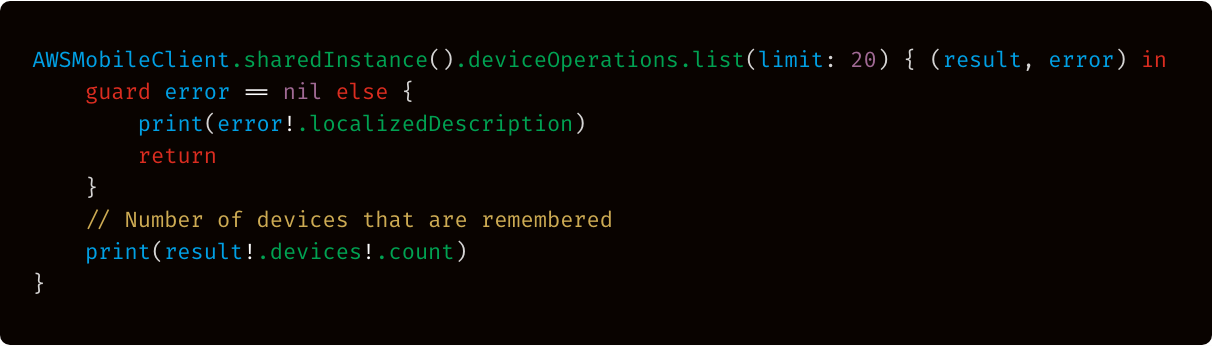
List all the devices that this user has authenticated on.
« (NEW) Option to add the Amazon Cognito hosted web UI to native iOS, Android, and React Native apps »
You now have the option to use the Amazon Cognito hosted web UI, in addition to the existing AWSMobileClient Drop-In Auth UI that’s available to native iOS and Android. The hosted UI supports OAuth 2.0, federated identities (such as Facebook Login, Login with Amazon, and Google Sign-in), and SAML providers.
To start, you need to do following to set up the hosted web UI (server side):
- Create an Amazon Cognito user pool.
- Add your identity providers to your user pools.
- Configure a user pool app client to enable the hosted web UI.
- Configure a user pool domain to configure the address of your sign-up and sign-in webpages. Your user pool domain looks something like this: domain_prefix.auth.us-east-1.amazoncognito.com.
To set up an iOS native client to use the hosted web UI:
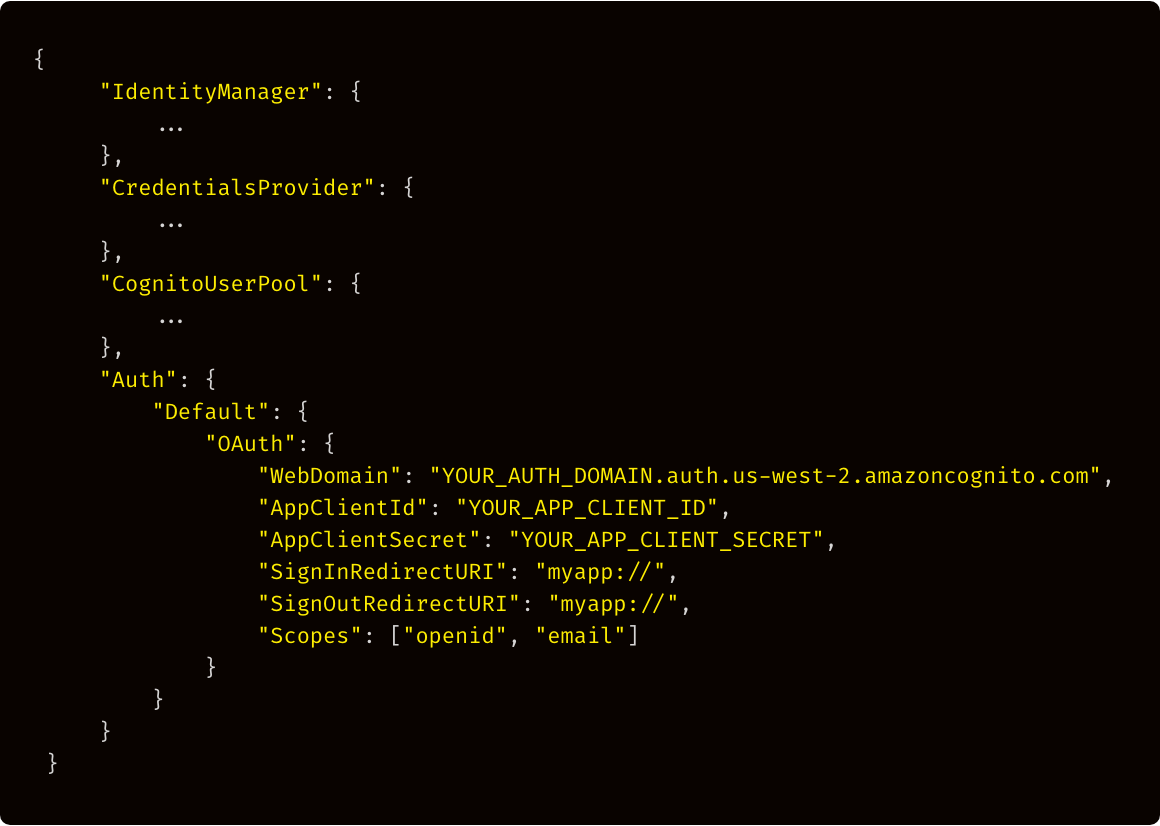
1. Add a new Auth configuration to the awsconfiguration.json file that looks like this:
2. Add myapp:// to your app’s URL scheme.
From Xcode, right-click Info.plist, and then choose Open As > Source Code
Add the following entry in the URL scheme:
3. To launch the hosted web UI from a native iOS app, use the showSignIn() API operation of AWSMobileClient.sharedInstance().
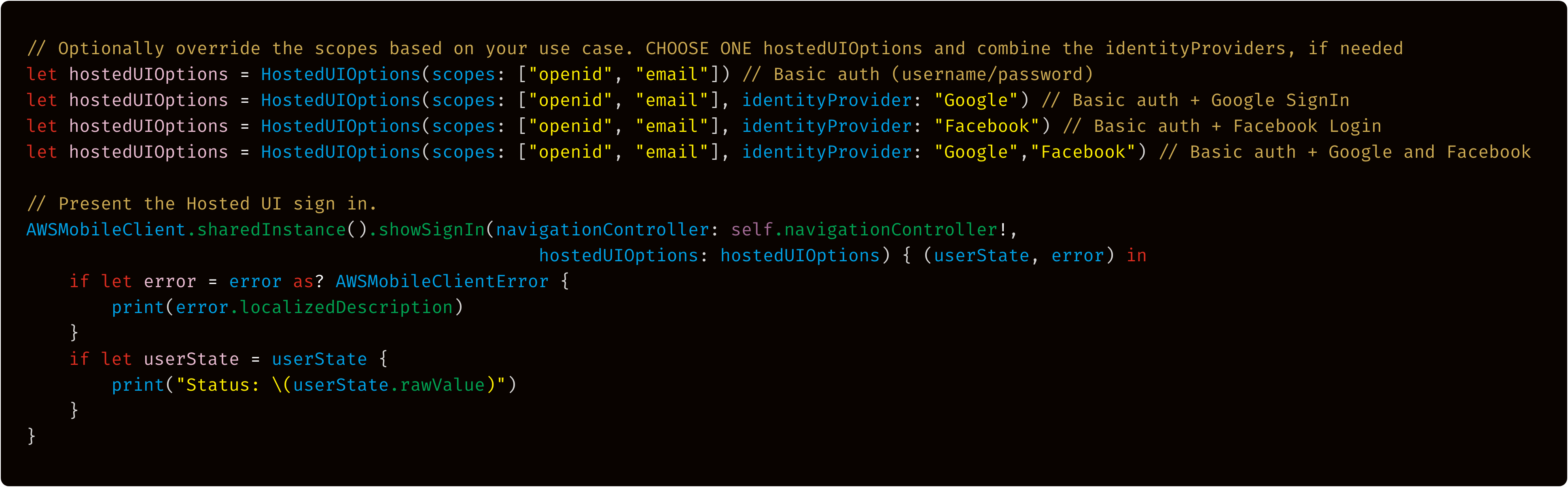
By default, the hosted UI shows all sign-in options—the basic authentication (username/password) flow, in addition to any identity providers that you configured in step 2 of the service configuration.
The following screenshot shows what the web UI looks like on an iPhone X that’s prompting the user to sign up and sign in.

If you want to sign out of the web UI from a mobile device, call signOut():
« (Enhanced) SAML federation with Amazon Cognito »
We’ve significantly improved the SAML federation flow on the client by using our AWSMobileClient to pass the SAML tokens via the federatedSignIn() function. This is the same call that you use for any other federated login.
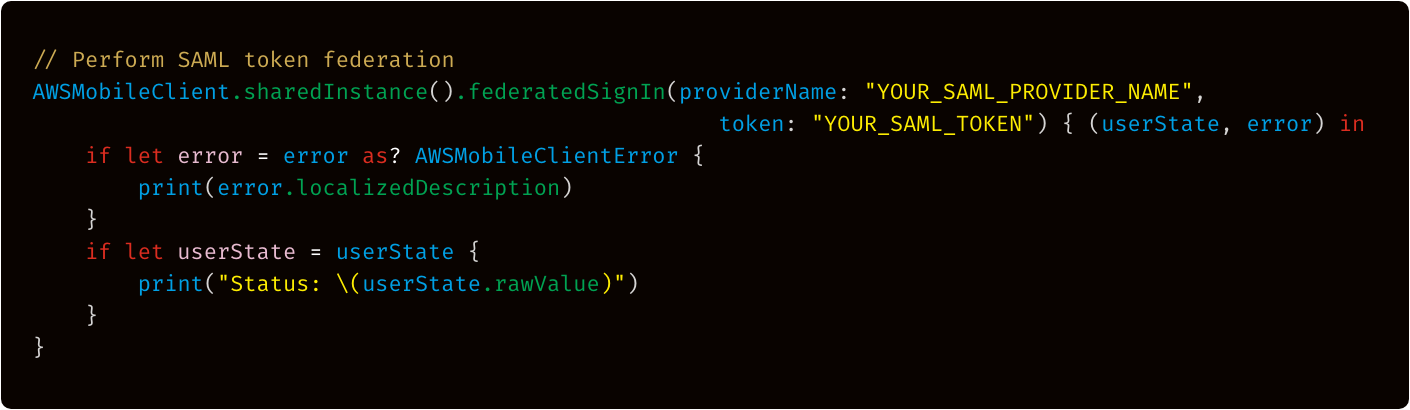
To add SAML federation to your mobile app, you must first register your SAML application with AWS Identity and Access Management (IAM).
Note: Currently, the SAML federation feature only supports SAML assertion tokens that have a one role Amazon Resource Name (ARN). If the assertion token has more than one role ARN, an error occurs.
« (NEW) OAuth 2.0 Authorization Code Grant flows »
Amplify Framework now includes support for OAuth 2.0 Authorization Code Grant flows in the native (iOS and Android) and React Native libraries. This enables developers to use any OAuth 2.0 compliant Identity Provider to authenticate their end users. Previously, developers had to use third-party libraries to achieve this use case, or write the logic by hand.
« (NEW) Global sign-out »
The global sign-out API operation enables you to sign out an Amazon Cognito user from all sessions on all devices. By calling this API operation, you’re revoking all the OIDC tokens (ID token, access token, and refresh token) for that user from all the devices they’ve ever logged into.
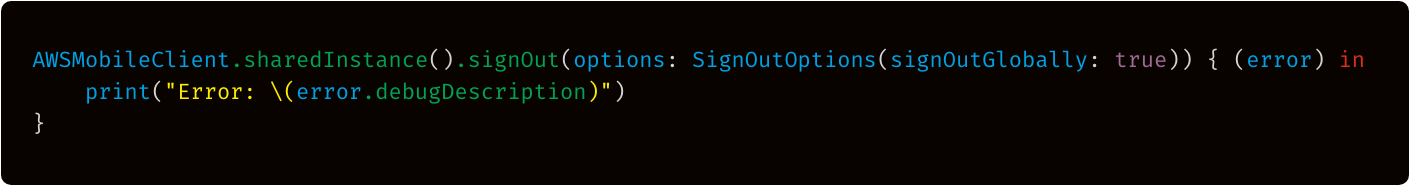
Here’s a little deeper dive into how this operation works. After the user has been globally signed out, the active AWS credentials for that user remain valid until they expire—up to one hour. In a typical authentication flow, AWS credentials that are granted to a user are only valid for one hour. Those credentials are recycled (at least once per hour) by the client SDK by using the refresh token. When the global sign-out API operation is called, any valid AWS credentials that were granted to that user in the past hour are valid until they expire. When they expire, the SDK attempts to retrieve new credentials with the refresh token, but fails permanently until the user signs in.
Note: Global sign-out is only available when you’re using Amazon Cognito user pools as an identity provider.
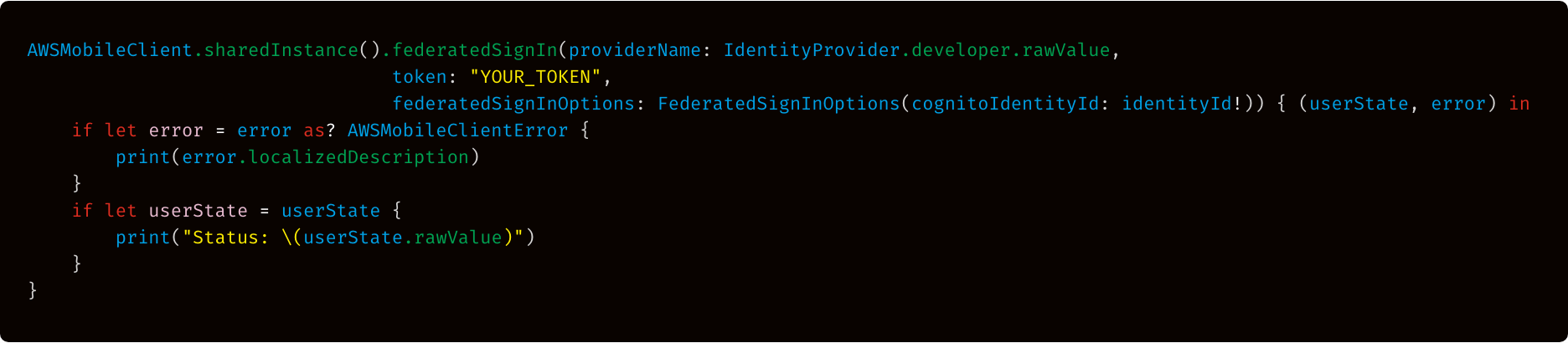
« (NEW) Developer authenticated identities »
With developer authenticated identities, you can register and authenticate your users by using your own existing authentication process, while still being able to use Amazon Cognito to access AWS resources.
First, register yourself with Amazon Cognito Identity in the console as the custom authentication provider. Then, after the end-user has authenticated with you, the app should receive an Amazon Cognito identity ID and token that confirms the sign-in with you from your servers. The app federates your sign-in with Amazon Cognito Identity to receive AWS credentials by making the following call:
Feedback
We hope you like these new features! We’re continuing to improve authentication routines for client applications. Also, we’re enhancing Amplify categories for web and mobile applications such as authentication, APIs, storage, and analytics—in addition to the AWS Mobile SDKs for iOS and Android. We welcome your comments in our GitHub repos on how we can improve more.
Documentation
Check out our updated authentication docs: