AWS Cloud Operations Blog
Set up an organization-wide aggregator in AWS Config using a delegated administrator account
AWS Config provides a detailed view of the configuration of AWS resources in your AWS account. With AWS Config, you can review changes in configurations and relationships between AWS resources, explore resource configuration histories, and use rules to determine compliance. An aggregator is an AWS Config resource type that collects AWS Config configuration and compliance data from multiple AWS accounts and Regions into a single account and Region to get a centralized view of your resource inventory and compliance.
You can also use an aggregator to collect configuration and compliance data from an organization in AWS Organizations and all the accounts in that organization that have AWS Config enabled. Previously, organization-wide data aggregation was available only from the organization management account, but AWS Config recently announced support for organization-wide resource data aggregation in a delegated administrator account.
A delegated administrator account is an account in an AWS Organizations that is granted additional administrative permissions for a specified AWS service. This means that in addition to the management account, you can also use a delegated admin account to aggregate data from all the member accounts in AWS Organizations without any additional authorization. With this capability, different teams in an organization (auditing, security, or compliance) can use separate accounts and aggregate organization-wide data in their respective administration accounts for centralized governance. This capability also eliminates the need for those teams to gain access to the management account to fetch the aggregated data.
In this blog post, I show how you can deploy organization-wide resource data aggregation in a delegated admin account and use the advanced query feature to query your entire AWS footprint from a central account.
Prerequisites
To follow the steps in this post, see Getting Started with AWS Config. You can enable the service for all accounts in AWS Organizations using AWS CloudFormation StackSets with all features, the default feature set that is available to AWS Organizations.
To enable AWS Config access to AWS Organizations
Run the following command from your organization management account:
aws organizations enable-aws-service-access --service-principal=config.amazonaws.com
Use the following command to verify the enable-aws-service-access command is complete:
aws organizations list-aws-service-access-for-organization
Under EnabledServicePrincipals, you should see config.amazonaws.com.
To register a delegated administrator account for AWS Config
To set up an aggregator from a non-management account, you must register a delegated admin account, which is a member account of your organization. From the management account, use the RegisterDelegatedAdministrator action to register a delegated admin. In the following AWS CLI command, replace MemberAccountID with the appropriate delegated admin account ID.
aws organizations register-delegated-administrator --service-principal config.amazonaws.com --account-id MemberAccountID
Note: The maximum number of delegated admins that the management account can assign for AWS Config (config.amazonaws.com) is 3.
Run the following command to verify the delegated admin has been registered successfully from the management account:
aws organizations list-delegated-administrators --service-principal=config.amazonaws.com
You should see the output similar to the following:
{
"DelegatedAdministrators": [
{
"Id": "MemberAccountID",
"Arn": "arn:aws:organizations::MemeberAccountID:account/o-**********/DelegatedAdministratorAccountID",
"Email": "Email_ID_MemberAccount",
"Name": "name",
"Status": "ACTIVE",
"JoinedMethod": "INVITED",
"JoinedTimestamp": 1604867734.48,
"DelegationEnabledDate": 1607020986.801
}
]
}To set up an aggregator using delegated admin
You can use the AWS Config console or the API to add an aggregator using the delegated admin account. In this post, I provide console steps for adding an organization-wide aggregator.
- Sign in to the AWS Management Console using the delegated admin account you just registered and open the AWS Config console at https://console.aws.amazon.com/config/.
- In the left navigation pane, choose Aggregators, and then choose Create aggregator.

Figure 1: Aggregators page

Figure 2: Create aggregator page
- On the Create aggregator page, under Allow data replication, select the Allow AWS Config to replicate data from source account(s) into an aggregator account checkbox.
- In Aggregator name, enter DelegatedAdminAggregator.
- Under Select source accounts, choose Add my organization to include all accounts in your organization to the aggregator.
- Under Choose IAM role, choose Create a role and enter the IAM role name. This newly created IAM role has the AWSConfigRoleForOrganizations managed policy, which allows AWS Config to call AWS Organizations APIs.
- Choose the AWS Regions for which you want to aggregate data. I select all Regions and then select the Include future AWS regions checkbox to aggregate data from AWS Regions where multi-account multi-region data aggregation is enabled. Choose Create aggregator.

Figure 3: Choose AWS Regions
- The newly created aggregator should appear on the Aggregators page:

Figure 4: DelegatedAdminAggregator
AWS Config starts aggregating data from all the member accounts in your organization into an aggregator. It might take a few minutes for AWS Config to display resource configuration and rule compliance status on this page.
- In the navigation pane, choose Aggregators, and then review the configuration data of your AWS resources and compliance state of your rules using the delegated admin account.

Figure 5: Resources page

Figure 6: Rules page
Now, run some advanced queries from the delegated administrator account.
- From the left navigation pane, choose Advanced queries to query your resource configurations for a single account and Region or for multiple accounts and Regions. On the Advanced queries page, you can use sample queries to query data from aggregated configuration items. You can also use the configuration properties in the AWS Config Resource Schema on GitHub to write a custom query.

Figure 7: Advanced queries page
Here are some sample queries:
Count EC2 instances and group them by instance type
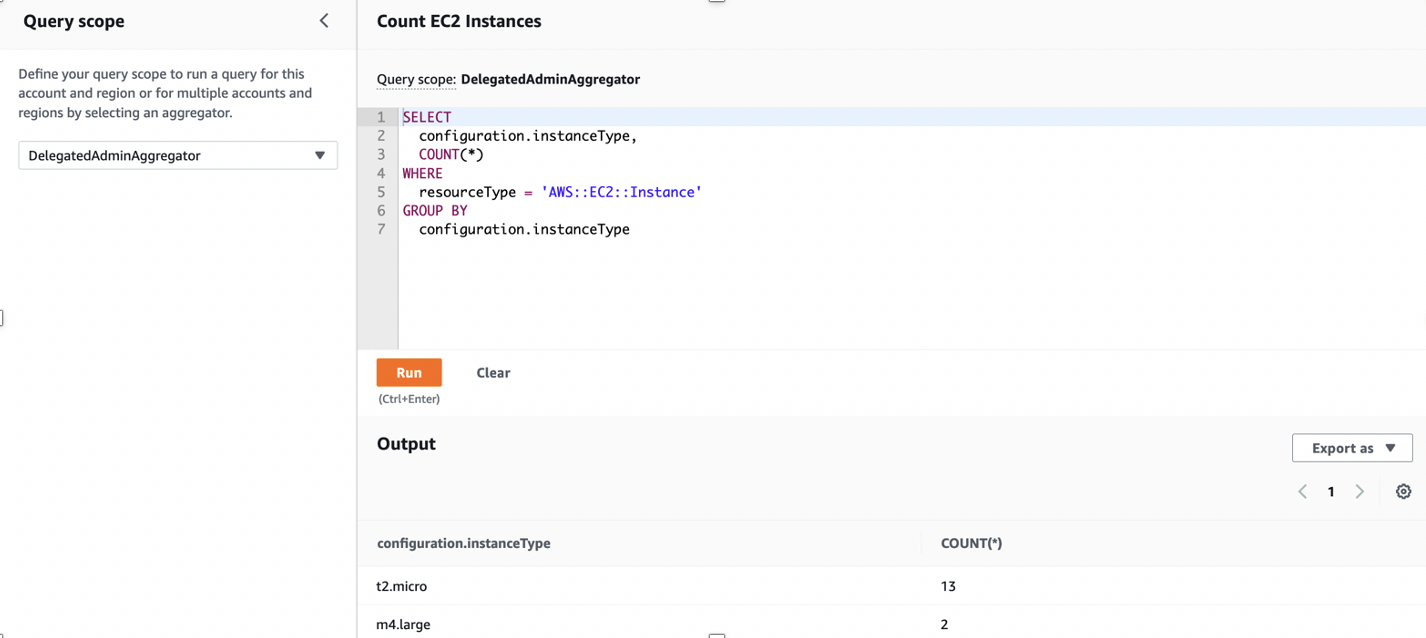
Figure 8: Count EC2 Instances sample query
List all EBS volumes that are not in use
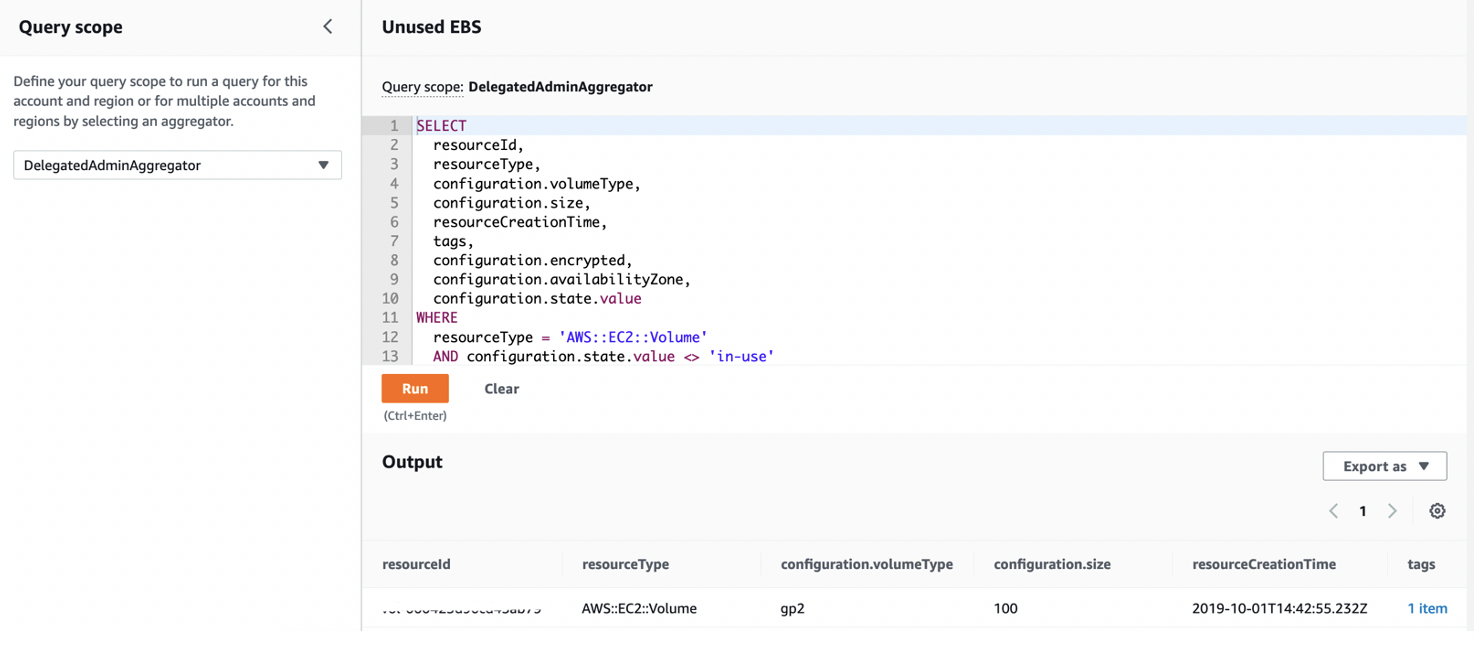
Figure 9: List EBS volumes sample query
To customize a query, in Advanced queries, choose a query from the list, and then choose Copy to editor.
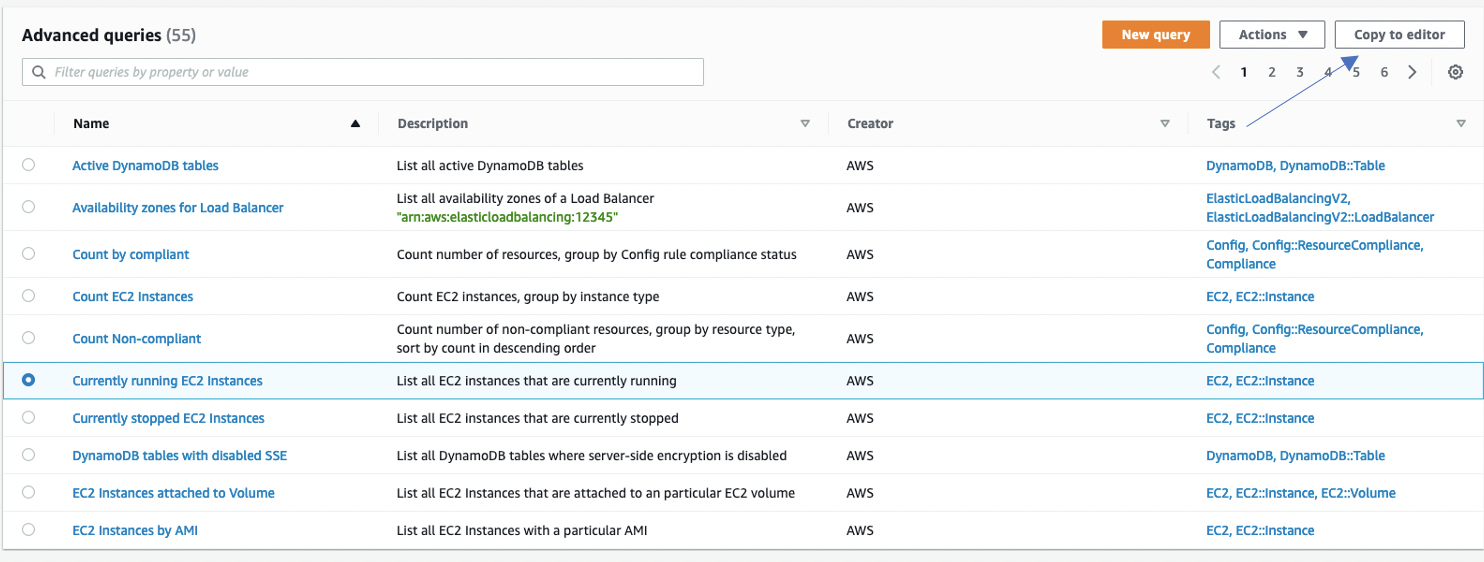
Figure 10: Copy to editor
In the Currently running EC2 Instances query, change configuration.state.name to stopped, and then choose Save as.
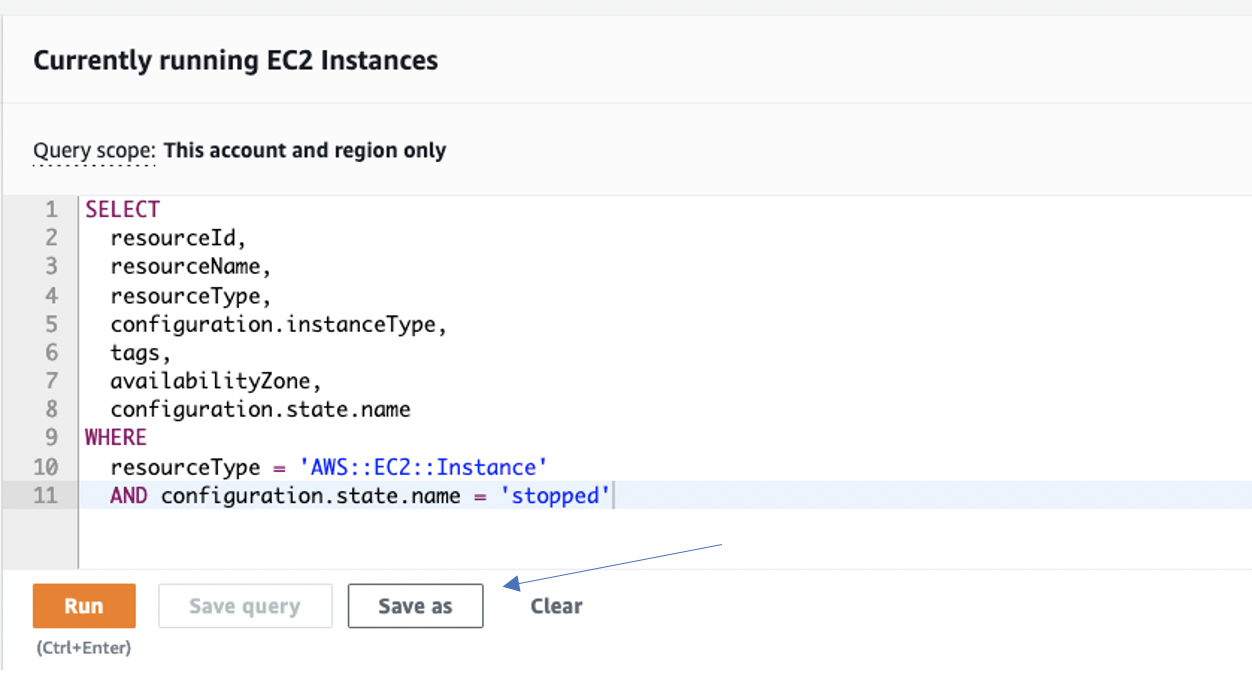
Figure 11: configuration.state.name
Enter a name, description, and tags for the query, and then choose Save.
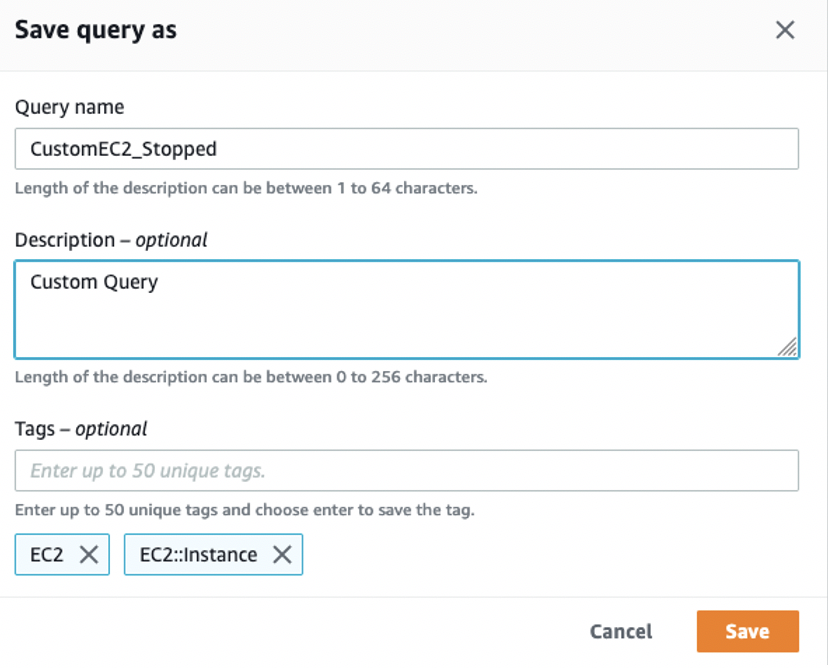
Figure 12: Save query as
The newly saved custom query should now appear in Advanced queries.
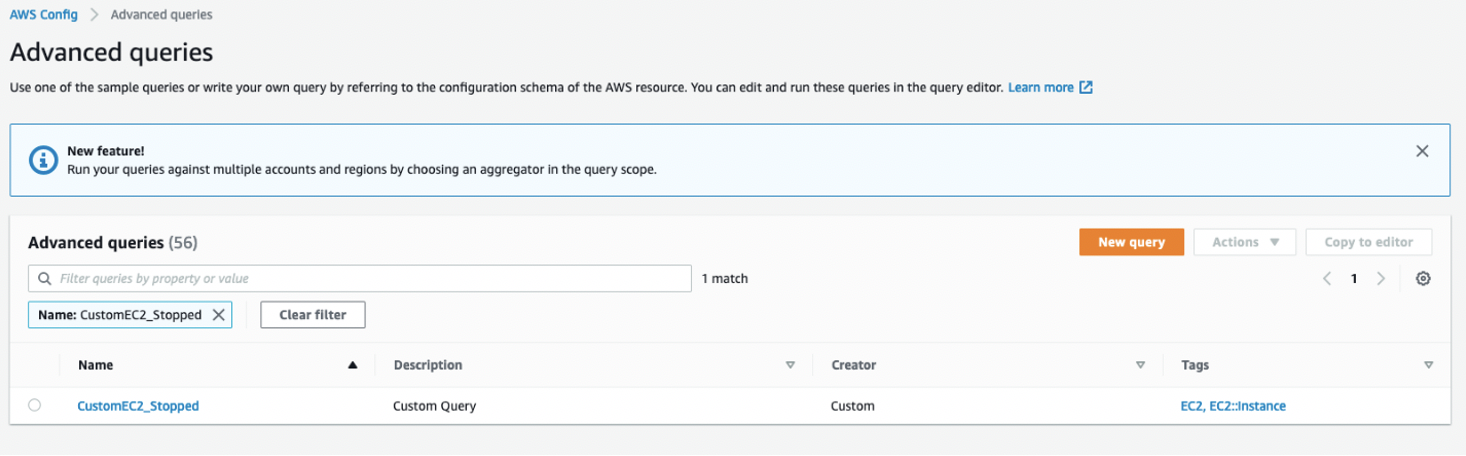
Figure 13: View custom query in advanced query view page
Conclusion
In this blog post, I showed how you can aggregate organization-wide AWS Config resource configuration and compliance data in a delegated admin account and run advanced queries on the aggregated data. This capability offers you more flexibility and eliminates the need for multiple teams to access your management account in order to use organization-wide data.
About the authors
 Vinay Nambiar is a Cloud Support Engineer at Amazon Web services. He holds MS in Computer Networking Telecommunication from Northeastern University and enjoys helping AWS customers to implement security best practices. Vinay specializes in AWS Config and likes to develop articles for our customers. Outside of work, he loves solving rubix cube, watching tennis, reading and visiting national parks.
Vinay Nambiar is a Cloud Support Engineer at Amazon Web services. He holds MS in Computer Networking Telecommunication from Northeastern University and enjoys helping AWS customers to implement security best practices. Vinay specializes in AWS Config and likes to develop articles for our customers. Outside of work, he loves solving rubix cube, watching tennis, reading and visiting national parks.
 Priyesh Bansal is a Senior Product Manager with Amazon Web services. He helps customers meet their configuration, compliance, and auditing needs. In his free time, Priyesh enjoys reading, cooking, and hiking.
Priyesh Bansal is a Senior Product Manager with Amazon Web services. He helps customers meet their configuration, compliance, and auditing needs. In his free time, Priyesh enjoys reading, cooking, and hiking.