Networking & Content Delivery
Using Microsoft Active Directory MFA with AWS Client VPN
You can now enable multi-factor authentication (MFA) for users connecting to an AWS Client VPN endpoint. This solution is ideal for organizations that want additional security when remote users are accessing AWS or on-premises resources. MFA improves the authentication process by requiring more than a user name, password, and certificate (the first factor). MFA requires an additional authentication code (the second factor), usually delivered by SMS message, card, app, or similar mechanism, before the user is granted access.
To enable MFA for the AWS Client VPN Service, you need a Remote Authentication Dial-In User Service (RADIUS) MFA server with a One Time Password (OTP) solution. RADIUS is an IETF standard client/server protocol that provides authentication, authorization, and accounting.
There are many options to choose from when selecting an MFA solution. You can use Duo, Okta, a freeradius server with Google Authenticator, or any number of other solutions. In this example, I am using the RADIUS Server with DUO Authentication Proxy Service, and Duo for generating OTP.
In this blog post, we enable MFA for your AWS Client VPN users in four steps:
- Duo account set-up and configuration.
- Configure your RADIUS server to accept Microsoft Active Directory requests.
- Configure your Microsoft Active Directory to enable MFA.
- Create the AWS Client VPN.
Getting started
There are two steps to setting up MFA for end users that use Duo to connect to a Client VPN endpoint. First, complete the IT administrator configuration tasks to set up the required services. Next, have each end user complete the end user configuration tasks to establish their secure connection to the Client VPN endpoint.
This solution assumes you are already running Microsoft Active Directory and have an Active Directory Manager instance. To learn more about how to set up AWS Managed Microsoft AD and create an AD Manager Instance, see Tutorial: Setting Up Your Base AWS Managed Microsoft AD Test Lab in AWS.
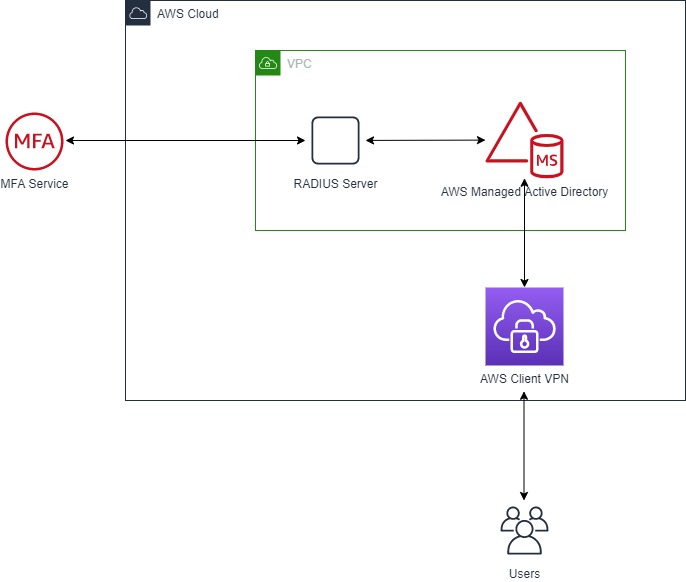
Solution overview
This diagram shows the components that you need to enable MFA for AWS Client VPN users. The left side in the diagram (covered in step 1) represents your Duo setup. The right side (covered in step 2) shows your RADIUS server, ready to proxy Microsoft Active Directory requests to Duo for OTP. It also covers the steps to enable MFA on Microsoft Active Directory (covered in step 3).
Configuration tasks for the IT-Admin
Step 1- Duo account set-up and configuration
- Create your Duo account. (If you don’t have one yet, you can create one at https://signup.duo.com/.)
- Install the “Duo-Mobile” application on your Mobile device. You use your Mobile Device to log in into the Duo-web console for configuring and managing Duo.
- Log in into your Duo web account and configure it as follows:
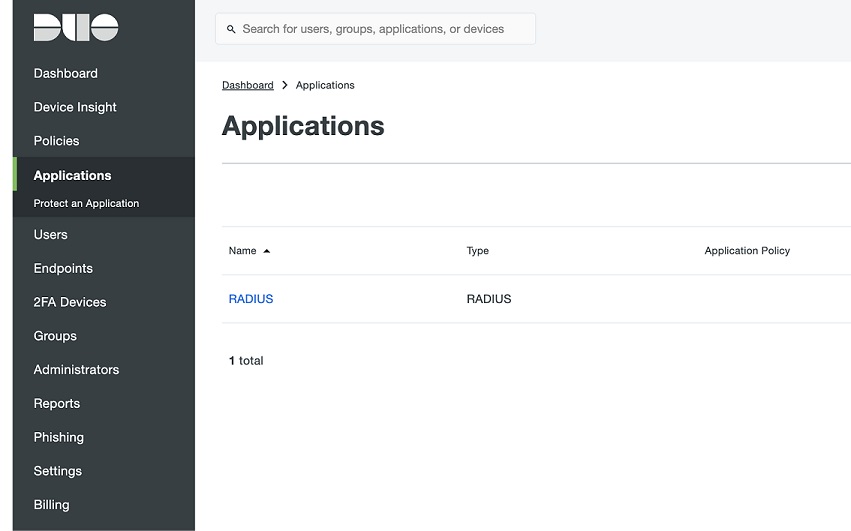
- Under Applications, install RADIUS. While configuring RADIUS, choose “Username Normalization as Simple” (Optional).
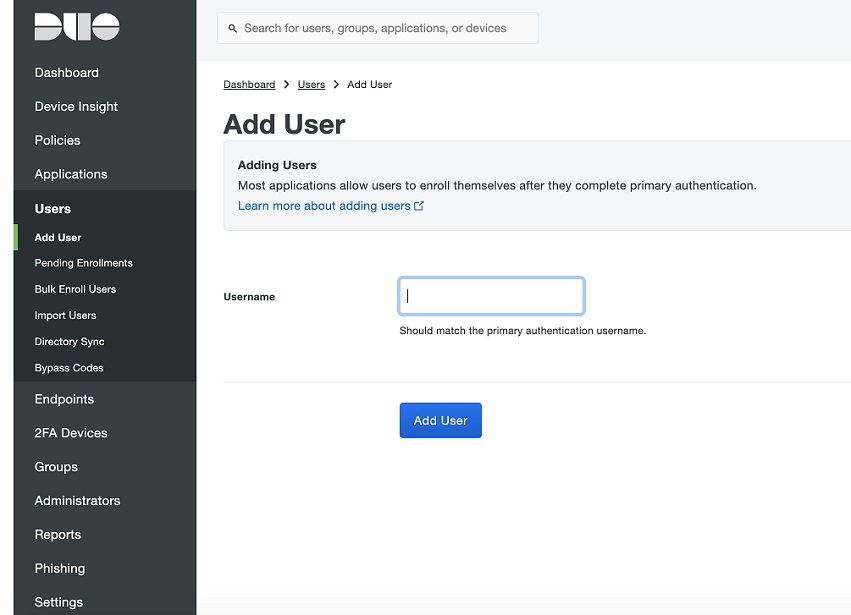
- Under Users, add your usernames. The usernames have to match what the end user enters when connecting to an AWS Client VPN endpoint.
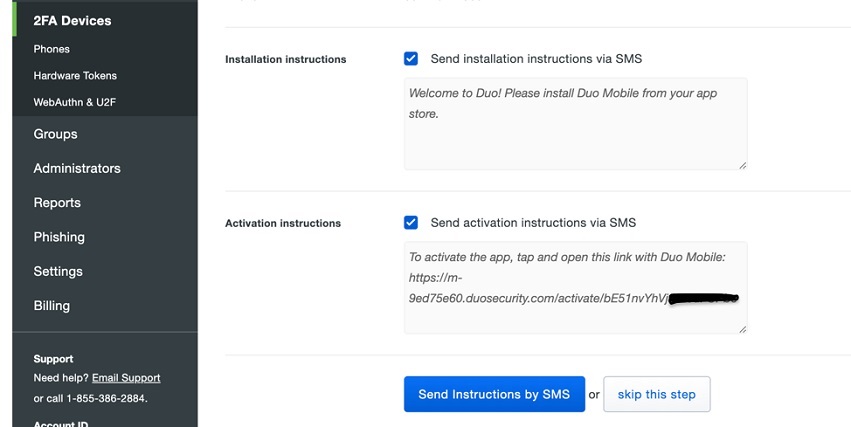
- Add Phone Number of above End Users/Clients (Clients get their OTP on this Phone Number when connecting to Client VPN). Once the phone-number has been added, you would further “Activate Duo Mobile” application associated with these Clients/Usernames.
- For that, select “Activate Duo Mobile” and Generate Duo Mobile Activation Code. Once the Activation link is generated, choose either “Send Instruction via SMS” or you can “skip this step” by copying the activation link and sending it via email.
For more information, take a look at: configuring Duo for Radius Application.
Step 2 – Configure your RADIUS server to proxy authentication requests from Microsoft AD to Duo for OTP Code
To configure your RADIUS server to proxy authentication requests from your Microsoft AD:
- Launch a Windows EC2 Instance inside the same VPC as the Microsoft AD. Make sure it is joined to the Active Directory. (You can also put your RADIUS server in a different VPC or on premises locations, however you would must set up connectivity accordingly)
- Log in into this new instance (Windows EC2), and download and install the Duo Authentication Proxy for Windows.
- Once “Authentication Proxy” has been installed, navigate to C:\Program Files (x86)\Duo Security Authentication Proxy\conf\authproxy.cfg and edit the file, ‘authproxy.cfg’.
- Remove everything from this file and replace it with:
[duo_only_client]
[radius_server_auto]
ikey=XXX
skey=YYY
api_host=api-ZZZ.duosecurity.com
radius_ip_1=<AD-DNS-address#1>
radius_secret_1=<My-password>
radius_ip_2=<AD-DNS-address#2>
radius_secret_2=<My-password>
failmode=safe
client=duo_only_client
port=1812
Note-1: To get the values for “ikey (integration-key), skey (secret-key), and api_host (Your Duo’s API hostname)”, login into your Duo web account, and navigate to:
Dashboard> Applications> RADIUS
Under Details:
Integration key
Secret key
API hostname
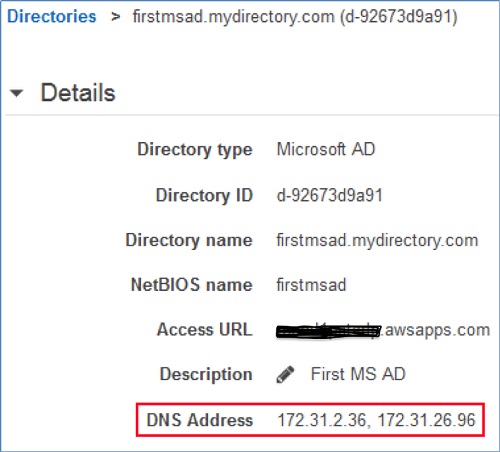
Note-2: To obtain the Microsoft AD domain controller (DC) IP addresses for your RADIUS server, open the AWS Management Console, choose Directory Service, and then copy your Directory ID link.
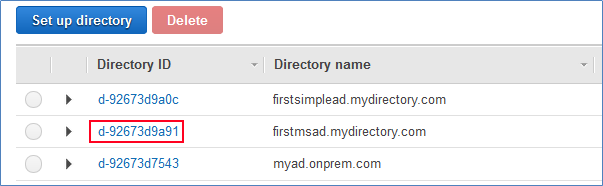
On the Directory details page, you see the two DC IP addresses for your Microsoft Active Directory (shown in the following screenshot as DNS Address). Your Microsoft Active Directory Domain Controllers are the RADIUS Clients to your RADIUS server.
- Further, set your own radius_secret_key (and make sure both are same).
- If needed, you can also change the port.
Note-3: Add a rule to the Amazon security group of your Microsoft Active Directory to allow inbound traffic from the RADIUS server IP address and port number. Also, allow outbound traffic to the Radius Server’s IP address and port number.
Activate Duo Authentication Service (Duo Security Authentication Proxy Service) from Services, make sure that the Duo Security Authentication Proxy service is in the ‘running’ state. If you make changes to the config file, authproxy.cfg, it is a good idea to restart the service after saving changes.
Step 3: Configure AWS Managed Microsoft AD to enable MFA
The final step is to configure your Microsoft AD directory to enable MFA. When you enable MFA, AWS Client VPN users are required to enter an MFA code along with their user name and password.
To enable MFA in your Microsoft Active Directory:
- Open the AWS Management Console, choose Directory Service, and then select your Directory ID.
- Under the Network and Security Tab, choose multi-factor authentication.

- Enter the following to configure your Microsoft AD directory to connect to your RADIUS server:
- Display Label: It’s a display name for RADIUS Server Configuration.
- RADIUS server DNS name or one or more IP addresses: Enter the IP addresses of your RADIUS server. If you have more than one RADIUS server, you can enter multiple IP addresses of Radius Server, separated by comma (for example, 192.0.0.0, 192.0.0.12). Alternatively, you can use a DNS name for your RADIUS server.
- Port: Enter the port number of your RADIUS server that you set at the end of Step 2.
- Shared secret code: Enter the same shared secret you created in your RADIUS server in Step 1.
- Confirm shared secret code: Reenter your shared secret code.
- Protocol: Select the authentication protocol between the Microsoft AD and the RADIUS server. Supported protocols are PAP, CHAP MS-CHAPv1, and MS-CHAPv2.
- Server timeout (in seconds): Enter the amount of time to wait for the RADIUS server to respond to authentication requests. If the RADIUS server does not respond in time, authentication is retried (see Max retries). This value must be from 1 to 50. There is no recommended value as it depends on the latency between RADIUS Server and AWS Managed Microsoft AD.
- Max retries: Specify the number of times that communication with the RADIUS server is attempted before failing. This must be a value from 0 to 10.
- Choose Edit to update the RADIUS settings for your directory. The update process takes less than two minutes to complete. When it’s done RADIUS Status changes to Completed.
Note – If you want to achieve resiliency or high availability at Radius server, we always recommend to use at-least two radius server such that if one becomes unavailable, authentication requests could be served via second radius server.
If you receive a Failed status after choosing the Edit button, check the following common issues:
- A mismatch between the shared key provided in the RADIUS server and Microsoft Active Directory configurations.
- Network connectivity issues between your Microsoft Active Directory and RADIUS server can also cause problems. These are often found in security groups, network access control lists, route table configurations, or Windows Firewall.
- The authentication protocol configured in Microsoft Active Directory does not match, or is not supported, by the RADIUS server.
Step 4: Create the AWS Client VPN endpoint
- Once the Microsoft Active Directory, RADIUS Server with proxy service, and Duo are in place, you can create the AWS Client VPN endpoint
- Download the VPN Client configuration file using the AWS Management Console, CLI, or API, and make sure it includes the following text (add if not):
auth-user-pass
static-challenge "Enter MFA code” 1
Apart from that, if you are using dual authentication (that is, Mutual Authentication + Active Directory) then make sure to add the client <cert> and <key> to the above downloaded config file as per the documentation. Now, you can pass the configuration file to end user.
Configuration tasks for End-User(s):
Install Duo mobile application
Each end-user must install the Duo application on their mobile device, then use the activation link their IT-admin provided. The activation link associates the user’s Duo application with the Duo account’s username (the one the Duo link was generated for).
Install the Client-VPN tool and connect to the VPN endpoint server
- Download and Install the AWS VPN Client tool available for macOS, Windows, or any open VPN-based Clients (For example: Tunnel Blick, Viscosity, Open VPN, etc.).
- Try connecting to the AWS Client VPN endpoint.
- Once you enter the user’s credentials, you are prompted to enter the MFA code from the Duo mobile application.
- You connect when the credentials are successfully verified by the Client VPN endpoint.
Cleaning up: Deleting the Client VPN endpoint
When you delete a Client VPN endpoint, its state changes to “deleting” and clients can no longer connect to it. Before you can delete a Client VPN endpoint, however, you must first disassociate all target networks. This can be done using the AWS Management Console or the AWS CLI.
Summary:
This blog post walked through the four steps to implementing MFA with AWS Client VPN using RADIUS and Microsoft Active Directory. Together, AWS Client VPN with MFA provides an extra layer of security for organizations with large numbers of remote users.
To learn more about AWS Client VPN, see the AWS Client VPN admin page.
To learn more about AWS Directory Service, see the AWS Directory Service home page. If you have questions, please post them on the Directory Service forum.
| Blog: Using AWS Client VPN to securely access AWS and on-premises resources | ||
| More on AWS VPN services | ||
 |
Watch re:Invent 2019: Connectivity to AWS and hybrid AWS network architectures |
