AWS Open Source Blog
AWS Service Broker with Ease – and Now for GovCloud
 中文版 – AWS customers are increasingly asking for easier implementation across all services, so they can focus on what is important to their customers. In this post, we’ll explain some changes in the installation and configuration process for the AWS Service Broker which make it easier and faster to get up and running on your application platform. AWS Service Broker is now also available for AWS GovCloud (US), so that customers running critical workloads in GovCloud (US) can use it to provision and expose native AWS services through their application platform of choice.
中文版 – AWS customers are increasingly asking for easier implementation across all services, so they can focus on what is important to their customers. In this post, we’ll explain some changes in the installation and configuration process for the AWS Service Broker which make it easier and faster to get up and running on your application platform. AWS Service Broker is now also available for AWS GovCloud (US), so that customers running critical workloads in GovCloud (US) can use it to provision and expose native AWS services through their application platform of choice.
First, some prerequisites:
- A DynamoDB table for tracking state.
- An S3 bucket to store templates used by the Broker to manage the AWS services. This has been a request from many customers seeking a private catalog of customized solutions tailored to their business needs. You can now take the CloudFormation templates for each service supported by AWS Service Broker, assess and modify these as needed, and store them in their own catalog. Or, even better, you can add your own completely new and customized solutions to work with the broker.
- An IAM role with permissions to interact with the DynamoDB table, the S3 bucket, and AWS CloudFormation.
Full details are available in AWS Service Broker install prerequisites on GitHub.
To help you get up and running as quickly as possible, we have provided a CloudFormation template that builds out the DynamoDB table and IAM resources into the AWS account. The CloudFormation template to build out dynamoDB and IAM resources can be found here:
https://github.com/awslabs/aws-servicebroker/blob/master/setup/prerequisites.yaml
The templates provided in the Service Broker public S3 bucket will not work in GovCloud (US); you will need to copy them from Service Broker Public S3 bucket and then upload them to a private catalog (i.e., an S3 bucket) in the GovCloud (US) account and region.
The following command will download all the templates to a local system using the AWS CLI:
aws s3 cp s3://awsservicebroker/templates/latest/ ./ --recursiveThese can then be uploaded to a bucket in GovCloud (US):
aws s3 cp templates/ s3://mybucket/templates/latest --recursive --region us-gov-west-1For more detail, please see AWS GovCloud (US-West) Endpoints.
For workloads running in GovCloud, you will need to ensure that the S3 bucket and DynamoDB table are deployed into your GovCloud (US)-enabled account and region.
Once the resources are in place, update the config for the broker to point to the table, bucket, and IAM role, and you are good to go.
The next step is to install the AWS Service Broker into your platform of choice (this process is identical for all AWS account types).
Download the install tool for your platform, tile, helm chart, or script, and complete the install process. Each platform is described in the appropriate section of the AWS Service Broker Documentation.
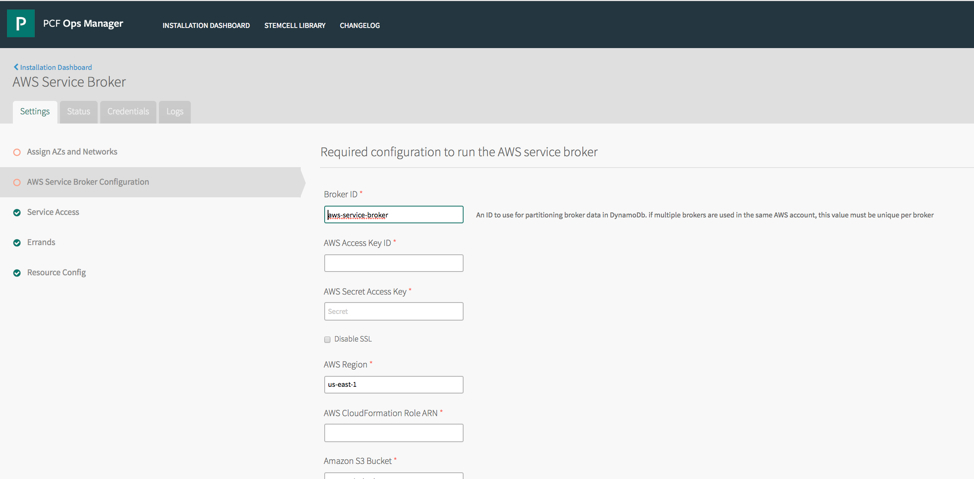
Finally, update the config to point to the S3 bucket, DynamoDB table, and IAM resources. GovCloud (US) customers should ensure that they are listing the resources within their GovCloud (US) account and region. The S3 Bucket being used for the template catalog will require at least one template in it. GovCloud (US) customers will need to make use of the custom catalog, i.e an S3 bucket in their GovCloud (US) region, for the template store.
Updating the Service Broker configuration can be done by updating values in environment variable or argument files for OpenShift and Kubernetes and tile configuration for Cloud Foundry.
Example config for OpenShift (note the S3 bucket and Region configuration):
TARGETACCOUNTID=
TARGETROLENAME=
VPCID=
REGION=us-east-1
IMAGE=awsservicebroker/aws-servicebroker:beta
IMAGEPULLPOLICY=Always
S3BUCKET=<YOUR S3 BUCKET IN GOVCLOUD>
S3KEY=templates/latest
S3REGION=us-gov-west-1
TABLENAME=awssb
VERBOSITY=10
BROKERID=awsservicebroker
PRESCRIBE_OVERRIDES=trueExample config for CloudFoundry:
Now is the perfect time to integrate the AWS Service Broker into your application platform on GovCloud (US). The AWS Service Broker is an open source project that welcomes feedback via issues, and we’d love to have you contribute!