AWS Security Blog
Category: Amazon EC2
Easily Tag Amazon EC2 Instances and Amazon EBS Volumes on Creation
In 2010, AWS launched resource tagging for Amazon EC2 instances and other EC2 resources. Since that launch, we have raised the allowable number of tags per resource from 10 to 50 and made tags more useful with the introduction of resource groups and Tag Editor. AWS customers use tags to track ownership, drive their cost accounting […]
How to Monitor Host-Based Intrusion Detection System Alerts on Amazon EC2 Instances
September 9, 2021: Amazon Elasticsearch Service has been renamed to Amazon OpenSearch Service. See details. To help you secure your AWS resources, we recommend that you adopt a layered approach that includes the use of preventative and detective controls. For example, incorporating host-based controls for your Amazon EC2 instances can restrict access and provide appropriate […]
Easily Replace or Attach an IAM Role to an Existing EC2 Instance by Using the EC2 Console
April 13, 2022: This blog is out of date. Please refer to this documentation for updated info: Amazon Elastic Compute Cloud User Guide AWS Identity and Access Management (IAM) roles enable your applications running on Amazon EC2 to use temporary security credentials. IAM roles for EC2 make it easier for your applications to make API […]
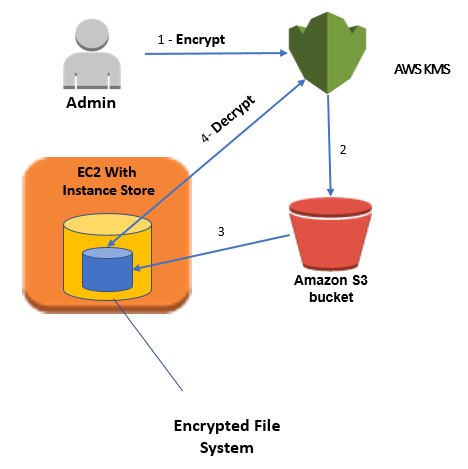
How to Protect Data at Rest with Amazon EC2 Instance Store Encryption
April 25, 2023: We’ve updated this blog post to include more security learning resources. Note: By default, an instance type that includes an NVMe instance store encrypts data at rest using an XTS-AES-256 block cipher. See this FAQ about NVMe-supported instance types. If you’re using an NVMw instance type, then data at rest is encrypted […]
How to Monitor AWS Account Configuration Changes and API Calls to Amazon EC2 Security Groups
You can use AWS security controls to detect and mitigate risks to your AWS resources. The purpose of each security control is defined by its control objective. For example, the control objective of an Amazon VPC security group is to permit only designated traffic to enter or leave a network interface. Let’s say you have […]
How to Manage Secrets for Amazon EC2 Container Service–Based Applications by Using Amazon S3 and Docker
Docker enables you to package, ship, and run applications as containers. This approach provides a comprehensive abstraction layer that allows developers to “containerize” or “package” any application and have it run on any infrastructure. Docker containers are analogous to shipping containers in that they provide a standard and consistent way of shipping almost anything. One […]
How to Automatically Tag Amazon EC2 Resources in Response to API Events
Note: As of March 28, 2017, Amazon EC2 supports tagging on creation, enforced tag usage, AWS Identity and Access Management (IAM) resource-level permissions, and enforced volume encryption. See New – Tag EC2 Instances & EBS Volumes on Creation on the AWS Blog for more information. Access to manage Amazon EC2 instances can be controlled using […]
How to Configure Your EC2 Instances to Automatically Join a Microsoft Active Directory Domain
Seamlessly joining Windows EC2 instances in AWS to a Microsoft Active Directory domain is a common scenario, especially for enterprises building a hybrid cloud architecture. With AWS Directory Service, you can target an Active Directory domain managed on-premises or within AWS. How to Connect Your On-Premises Active Directory to AWS Using AD Connector takes you […]
How to Help Lock Down a User’s Amazon EC2 Capabilities to a Single VPC
As a cloud support engineer, I am frequently asked this question: “How can I lock down my user’s Amazon EC2 access to a single VPC?” This blog post will answer the question and explain how you can help control this level of access through the use of AWS Identity and Access Management (IAM) policies and […]
Granting Permission to Launch EC2 Instances with IAM Roles (PassRole Permission)
When you launch an Amazon EC2 instance, you can associate an AWS IAM role with the instance to give applications or CLI commands that run on the instance permissions that are defined by the role. When a role is associated with an instance, EC2 obtains temporary security credentials for the role you associated with the […]