AWS for SAP
Improving SAP Fiori Performance with Amazon CloudFront and AWS Global Accelerator Part 2: How-to Guide
In a previous blog, we have concluded that Amazon CloudFront is recommended to accelerate the SAP Fiori Launchpad use case, while AWS Global Accelerator is recommended to accelerate the external system integration scenario via OData API calls such as Data extraction for analytics and reporting. We observed improvement in the time to first load SAP Fiori Launchpad, when accelerated through CloudFront, and improvement on OData API call times through Global Accelerator.
This post will discuss in details on how-to implement each of these solutions including the key parameters to pay attention to ensure successful deployment of CloudFront and Global Accelerator for SAP Fiori.
Solution Overview
The demo solution architecture above describes a simple deployment of SAP S/4HANA 2020 with embedded Fiori in the AWS us-east-1 (Northern Virginia) region that can be accessed over the internet, while the users are in Singapore.
- SAP Fiori launchpad will be accelerated by Amazon CloudFront.
- In another scenario, we will simulate the acceleration of the SAP OData API calls with AWS Global Accelerator.
- The Application Load balancer (ALB) will act as reverse proxy to SAP S/4HANA 2020. Please note that in productive deployment, to improve the security posture, we recommend you install SAP S/4HANA with embedded Fiori in a private subnet, and setup an SAP Web dispatcher in a public subnet.
- AWS Certificate Manager will be used to manage the wildcard SSL certificate for CloudFront and Application Load balancer.
- Amazon Route 53 will manage the DNS entries required to support the solutions.
Pre-Requisites
You will need to ensure the following are configured before the solution implementation step:
- Windows RDP (Remote Desktop Protocol) is installed. You will use this to administer and maintained various configuration of SAP S/4HANA and SAP Fiori.
- SAP S/4HANA 2020 is installed. You can use AWS Launch Wizard to do this .
- After the SAP S/4HANA vanilla installation is done, please follow these steps to update the system using SAP Maintenance Planner tool to have embedded Fiori component enabled. References: SAP S/4HANA 2020 Maintenance planner, SAP S/4HANA 2020 Installation, SAP S/4HANA 2020 Best Practice Activation and SAP S/4HANA 2020 Ravid Activation for Fiori
- You must have a valid internet domain; you can procure this from Amazon Route 53 or another DNS provider. It will be used to maintained DNS Entry (e.g., Alias in Route53 or CNAME in other DNS) records for ALB, CloudFront and Global Accelerator.
- For ease of deployment, I use a Wildcard SSL certificate signed by public Certificate Authority (example: Verisign). You can import this into AWS Certificate Manager and SAP Fiori back-end (example *.example.com). SSL public certificates that are generated from AWS Certificate Manager (ACM) will not work with SAP because it requires a signed SSL certificate to be imported to SAP Fiori system using Certificate Signing Request (CSR) method.
Solution Implementation
1. Configure Application Load Balancer
You can follow this documentation to create Application Load Balancer.
1.1 Create Target Group
|
Input Parameters |
Considerations |
|
Protocol Port |
In this example, we use HTTPS port 8443 |
|
Health Check Path |
/sap/public/ping Please ensure this path is enabled in SICF transaction code in SAP Fiori |
|
Stickiness |
As SAP is a stateful application, you will need ALB to always point to certain SAP instance for that particular user session. This must be enabled. |
|
Stickiness duration |
You can set to 1 day or 8 hours stickiness to cover user activities for the day. |
1.2 Create Load Balancer
|
Input Parameters |
Considerations |
|
DNS Name |
Let’s name this “sap-alb” which later in this document be defined as an alias record in Route53 or CNAME in other DNS |
|
Scheme |
Define as “internet-facing”
|
|
Security
|
Port 443 of the Load Balancer security group (you can name this security group as “sgLBSAP” for example) must be open to Internet Port 8443 of the SAP Fiori security group (you can name this security group as “sgSAPPAS” for example) is opened from ALB security group (you can name this security group as “sgLBSAP” for example) to SAP Fiori |
|
Listener. ID |
HTTPS: 443 |
|
SSL Certificate |
You can point this to AWS Certificate Manager which holds the wildcard SSL Certificate |
|
Rules |
Forwarding to “tgSAP” target group which contains the SAP Fiori system |
2. Create CloudFront Distribution
You can follow this documentation to create CloudFront Distribution.
2.1 General Settings
|
Input Parameters |
Considerations |
|
Price Class |
CloudFront has edge locations all over the world.
You can align this to the user’s location and performance expectation. |
|
Alternate Domain Names (CNAMEs) |
You will set this to the target website name. This must to be in line with the alias or CNAME record and SSL Certificate, so when the user browse to SAP Fiori, it connects through the CloudFront end-point. (example: sap.example.com) |
|
SSL Certificate |
You point this to the wildcard SSL Certificate SSL certificate in Certificate Manager. The Common Name must correspond to the Domain name above. (example:CN=*.example.com) |
|
Domain Name |
You can take note of this when maintaining target “sap” alias record in Route 43 or CNAME record in other DNS |
|
Security Policy |
At the time of writing TLSv1.2_2019 is the latest security policy recommended that are supported by both CloudFront and SAP |
|
Supported HTTP versions |
Ensure that HTTP/2 is enabled, as this provides many performance improvements compared to 1.1 and 1.0, by reducing latency, minimizing protocol overhead via compression and support over requests prioritization. |
|
Log Bucket & Log Prefix |
You will need this to troubleshoot, analyse and monitor the solution. |
2.2 Origin Settings
|
Input Parameters |
Considerations |
|
Origin Domain Name |
You will point this to the ALB. Please ensure that it is aligned with the SSL wildcard domain (example: sap-alb.example.com) |
|
Minimum Origin SSL Protocol |
Please specify TLSv1.2, as at the time of writing this is the highest supported by SAP. |
|
Origin Protocol Policy |
You will use HTTPS only. This will be the protocol used between CloudFront and ALB to implement end-to-end encryption. |
2.3 Behaviour
|
Input Parameters |
Considerations |
|
Path Pattern |
You set this as per the table below, with a Precedence zero of *FioriLaunchpad.html Below is the example Default (*) |
|
Viewer Protocol Policy |
You can set this to “Redirect HTTP to HTTPS” to achieve better user experience (most of browsers are still going to HTTP port as default when HSTS is not enabled) and better security posture. |
|
Non-Cacheable Objects |
Please set *FioriLaunchpad.html to cache policy : Managed-CachingDisabled request policy : Managed-AllViewer The GET, HEAD, OPTIONS, PUT, POST, PATCH, DELETE operation must be allowed This is required to ensure all the session cookies, query strings, HTTP headers
|
|
Cacheable Objects |
The cacheable objects include : *.html, *.js, *.css, *.jpg, *.png, *.ttf, *.ico, must have the following settings cache policy : Managed-CachingOptimized request policy : Managed-AllViewer The GET, HEAD operation must be allowed |
|
Default (*) |
As fallback, if none of the objects do not fall into the above policy, it must
cache policy : Managed-CachingDisabled request policy : Managed-AllViewer The GET, HEAD, OPTIONS, PUT, POST, PATCH, DELETE operation must be allowed |
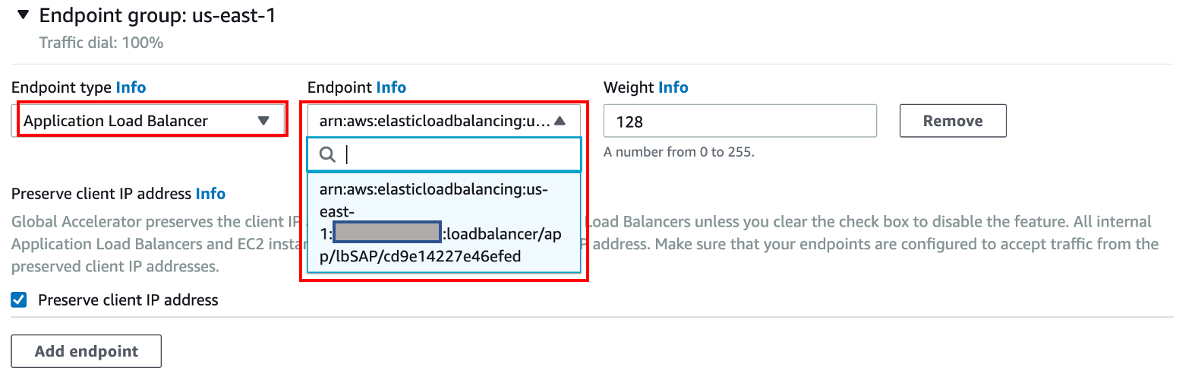
3. Create Global Accelerator
You can follow this documentation to create Global Accelerator.
|
Input Parameters |
Considerations |
|
Accelerator name |
You set this value as “gaSAP” for example |
|
Accelerator type |
You select “Standard” here |
|
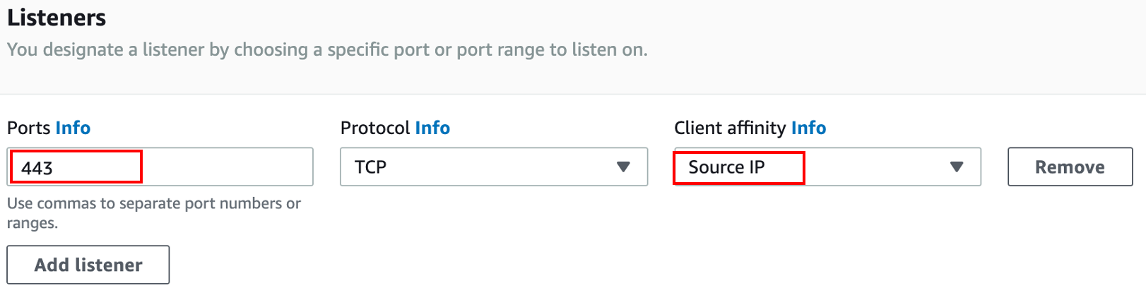
Ports |
443, default for HTTPS |
|
Client Affinity |
Client affinity is set to “Source IP” as SAP Fiori is stateful application |
|
Region |
This is where the Application Load Balancer and SAP Fiori located at |
|
Endpoint type |
You set this to Application Load Balancer ARN |
|
Listener port |
TCP:443 (default HTTPS Port of Application Load Balancer) |
4. Maintain alias record in Route53 or CNAME in other DNS Server and Perform test
You have registered domain “example.com”, and created a hosted zone for “example.com” in Route53. The alias records in Route53 or CNAME records in other DNS server are maintained for each of the components that were created earlier.
|
Record Name |
Record Type |
Value |
|
sap-alb |
A (Route53) or CNAME (other) |
xxxxxxxxxx.cloudfront.net |
|
sap |
A (Route53) or CNAME (other) |
lbsap-xxxxxxxxxx.us-east-1.elb.amazonaws.com |
|
sap-ga |
A (Route53) or CNAME (other) |
xxxxxxxxxx.awsglobalaccelerator.com |
5. Once the DNS is propagated, you can test using each of the URL below
|
Component |
URL Address for testing |
|
Application Load Balancer |
https://sap-alb.example.com/<urlpath> |
|
CloudFront |
https://sap.example.com/<urlpath> |
|
Global Accelerator |
https://sap-ga.example.com/<urlpath> |
Legend: <urlpath> = sap/bc/ui5_ui5/ui2/ushell/shells/abap/FioriLaunchpad.html
Example: = https://sap.example.com/sap/bc/ui5_ui5/ui2/ushell/shells/abap/FioriLaunchpad.html
Conclusion
Today, we have shown you how to implement CloudFront for SAP Fiori Launchpad step-by-step. This allows you to achieve better SAP Fiori performance, user experience and increased user productivity, while ensuring the standard SAP Fiori behavior is not altered.
We have shown you how to implement Global Accelerator to accelerate SAP OData API Calls. This will be useful in system integration scenarios where accelerated traffic is required to reduce latency between systems.
You can find out more about SAP on AWS, CloudFront and Global Accelerator from the AWS product documentation.