The Internet of Things on AWS – Official Blog
AWS IoT Greengrass now enables simplified deployments, enhanced security, and greater flexibility
Note: This blog covers AWS IoT Greengrass version 1, which has stopped receiving updates, fixes, and security patches since June 30, 2023. AWS IoT Greengrass Version 2 is a major update to the core software, APIs, and console that improves upon V1 with modular applications, better fleet device deployments, and expanded platform support. Learn more about AWS IoT Greengrass Version 2 here.
AWS IoT Greengrass allows you to bring local compute, messaging, data caching, sync, and ML inference capabilities to edge devices. Our newest release introduces features that simplify the deployment of Lambda functions to Greengrass, provide more flexibility so you can deploy Greengrass to new environments, and add easy-to-use security capabilities. Starting today, you can use new features that extend the capabilities of AWS IoT Greengrass devices, including connections to third-party applications and AWS services, isolation and permission settings that increase AWS IoT Greengrass configuration options, and hardware root of trust private key storage.
Simplified deployments: AWS IoT Greengrass connectors
You can use AWS IoT Greengrass at the edge to perform a variety of functions: from translating between devices that use different industrial protocols, moving data from devices to on-premises applications and services, and extending the fabric of AWS and third-party services to their edge environments. With new AWS IoT Greengrass connectors, you can enable these common edge use cases in AWS IoT Greengrass without writing code. You can simply install reusable, configurable connectors to popular services like Amazon Simple Notification Service (Amazon SNS) or Amazon CloudWatch and start building!

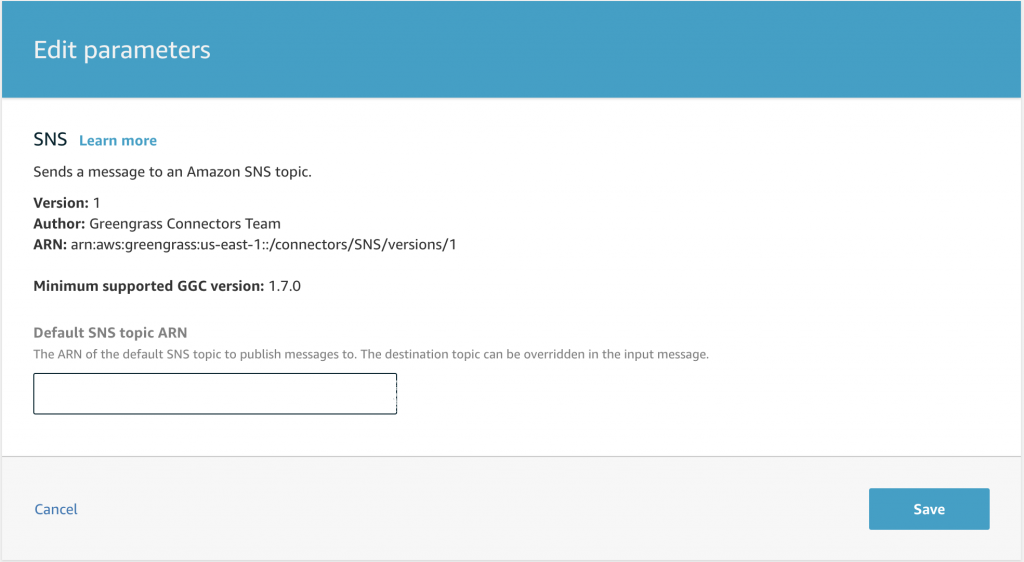
You can use the AWS IoT Greengrass console, CLI, or API to attach and deploy AWS IoT Greengrass connectors to AWS IoT Greengrass groups. Each connector is individually configurable and has editable parameters that control its operation. For example, an Amazon SNS connector prompts you for the Amazon Resource Name (ARN) of an SNS topic to send notifications. After this parameter is set, you can deploy the connector to your AWS IoT Greengrass core. Then, messages sent to the connector through a predefined MQTT topic are sent to Amazon SNS automatically as notifications.
Greater flexibility: AWS IoT Greengrass groups and per-Lambda isolation and permission configurations
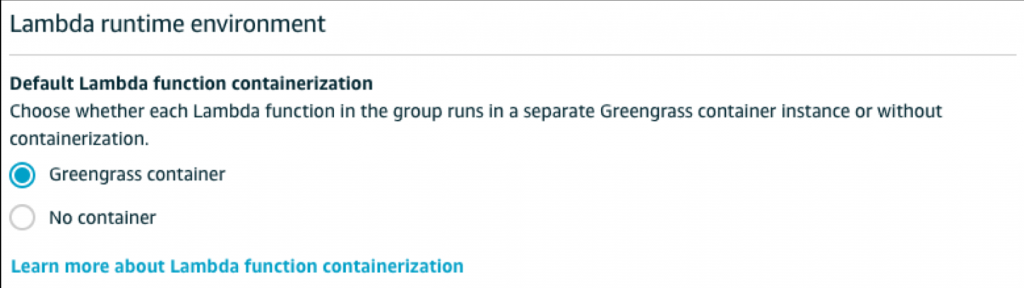
You can now use your preferred deployment mechanism and access a range of device resources. With new isolation configurations, you can get proof of concepts up and running faster by deploying AWS IoT Greengrass to other Open Container Initiative (OCI) container environments and directly accessing device resources like Bluetooth Low Energy (BLE) devices, sensors, or USB devices like Wi-Fi or camera dongles. You can also have more granular control over the permissions that you grant each function.
New configuration options allow you to run AWS IoT Greengrass groups and individual Lambda functions without the Greengrass container environment.
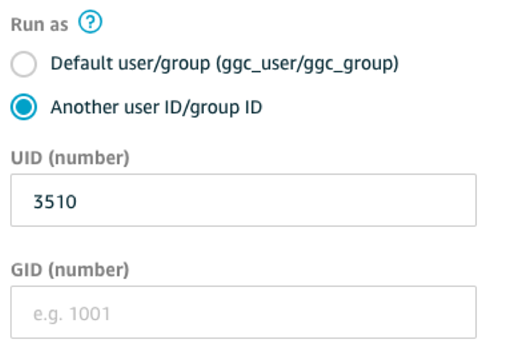
You can also choose to assign new group IDs and user IDs to a Lambda function, allowing functions to run with the permissions associated with that identity.
Running Greengrass Lambda functions as OS processes without containers allows you to run AWS IoT Greengrass in a Docker container. You can now run Greengrass inside a Docker container on Windows 10 or macOS X machines.
Enhanced security: AWS IoT Greengrass and Secrets Manager
Security is a top concern as more edge devices gather and analyze sensitive information using services like AWS IoT Greengrass. A new integration between AWS IoT Greengrass and AWS Secrets Manager makes it easier to securely store, access, rotate, and manage secrets (credentials, keys, configurations, and more) at the edge. AWS IoT Greengrass connectors and Lambda functions can now access secrets as resources from an AWS IoT Greengrass group, eliminating the need to manually manage secrets or hard-code into Lambda functions or environment variables.
You can begin by storing, versioning, and rotating your secrets in AWS Secrets Manager. After you’ve stored secrets in AWS Secrets Manager, they become available for deployment on the Resources tab in the AWS IoT Greengrass console and are ready for use by Lambda functions and AWS IoT Greengrass connectors.

AWS IoT Greengrass Secrets Manager is fully integrated with AWS IoT Greengrass connectors. If a AWS IoT Greengrass connector needs a secret to authenticate with an application or service, you can select and deploy a secret to the AWS IoT Greengrass core as part of the connector configuration.

Enhanced security: AWS IoT Greengrass hardware security integration
AWS IoT Greengrass hardware security integration introduces hardware root of trust private key storage to the AWS IoT Greengrass security model. You can leverage hardware secure elements in addition to the use of X.509 certificates for Transport Layer Security (TLS) mutual authentication and encryption of data both in transit and at rest. You can also use AWS IoT Greengrass connectors to more securely store secrets on an AWS IoT Greengrass core by storing private keys on a hardware secure element.
To get started, you can configure your AWS IoT Greengrass core to use a private key generated on a secure element. Then, the Greengrass core will make calls through an integrated PKCS#11 crypto-standard interface to use this private key as the key that verifies the Greengrass core’s identity during messaging with the AWS IoT Cloud and local devices with the AWS IoT Greengrass SDK.
Secure element vendors Intel, NXP, Microchip, Infineon, Yubico, Soracom, STMicroelectronics, and Zymbit will support secure element integration with AWS IoT Greengrass. Vendors including Logic Supply and Vitro Technology offer boards and gateways with integrated secure elements.
How to get started
Looking to get started and try out a connector, change your Lambda isolation configurations, or add new security capabilities to your IoT architecture?
- For the list of available AWS IoT Greengrass connectors, see the developer guide.
- To test new isolation and permissions configurations, you can change your AWS IoT Greengrass group and Lambda settings in the AWS IoT Greengrass console. For more information about isolation and permission configurations, see the developer guide.
- You can find documentation about how you can pull the Greengrass Docker image from AWS ECR here.
- If you want to purchase a device with root of trust security capabilities, you can use this link to filter for AWS IoT Greengrass Hardware Security Integration in our APN Device Portal to see compatible hardware devices. If you have a piece of hardware qualified by eligible vendors already, update to Greengrass v1.7, and reach out to your vendor for the firmware update that will enable this capability.