AWS News Blog
New Amazon CloudFront Feature: Private Content
|
|
You can now use Amazon CloudFront to distribute private content such as digital downloads, training materials, personalized documents, or media files. You can use this new feature to implement the following types of access models:
- Access only allowed after a specified date/time.
- Access only allowed between a pair of dates/times.
- Access only allowed before a specified date/time.
You can then enable access from a designated IP address or IP address range by using the CIDR notation. You can allow a single IP address (one user or client system) or a range of addresses (perhaps a school or a corporate network) to access the content.
The system is very flexible. Here’s what you need to do to start distributing your private content:
- Store your content in Amazon S3, protected by a restrictive ACL (Access Control List).
- Create a CloudFront origin access identity. This identifier is effectively a special AWS user identifier.
- Update the ACL on the private S3 objects to grant read permission to the origin access identity generated in the previous step. This must be done separately for each object; it is not sufficient to make this change at the bucket level.
- Create a new private content distribution or mark an existing distribution as private.
- Create a key pair (or locate the one that you already use for Amazon EC2). You can also upload an existing key pair, or you can use a set from another AWS account. If you want to allow other AWS accounts to sign your CloudFront requests, you must also designate these accounts as Trusted Signers in your CloudFront distribution.
- Design the access policy for the content. You can use a simple canned access policy that specifies nothing more than an expiration date, or you can create a more sophisticated policy which can include a date range, an IP address range, an a resource identifier (a URL to the private content) using optional wildcard characters.
- Construct a URL using the base-64 encoded form of the policy, the public portion of the key pair, the partial URL of the private content, and the base URL of the CloudFront distribution.
- Sign the URL using the RSA-SHA1 signature algorithm. Note that this is a different algorithm than the HMAC-SHA1 algorithm used by other parts of AWS.
- Distribute the signed URL as desired.
You can generate and sign multiple URLs for the same content, each with a unique access policy, if necessary. This could be useful if you are making the private content available to members of a mailing list, or if you want to generate the URLs after one of your user has registered and/or paid for the content.
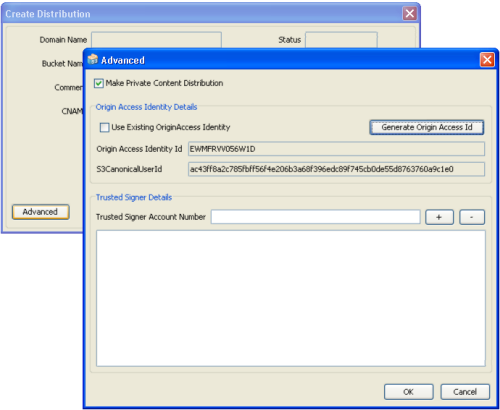
The newest version of the CloudBerry S3 Explorer includes full support for this exciting new feature, as does the newest Bucket Explorer. Here’s a picture of Bucket Explorer in action:
The JetS3T toolkit for Amazon S3 already supports CloudFront Private Content.
We expect other tools and other toolkits to do so in the very near future. Stay tuned to this blog for more information. If you are are a tool or toolkit developer and are in need of any special help in order to implement this feature, please post a note to the CloudFront forum.
A number of blogging tools and content management systems now support CloudFront. Here’s a quick roundup:
- Joomla!:
- Drupal:
- WordPress:
- Mark’s Blog: How to copy your WordPress files to CloudFront efficiently
- The Inquisitr: Amazon Cloudfront CDN with a WordPress Blog
- WordPress.org: Plugin Directory: CloudFront
- OM4: Using Amazon CloudFront with WordPress and WordPress MU
- BitsyBox:
- Bits On The Run:
We are interested in hearing how you plan to put this new feature to use. Feel free to post a comment!
— Jeff;