AWS Marketplace
Automate Cloud Storage Security deployment using Account Factory Customization
AWS customers of all sizes often need to customize their accounts due to internal or regulatory requirements. Until now, customers have used predefined account baselines with default resources, configurations, and Amazon Virtual Private Cloud (Amazon VPC). This can result in time- and labor-intensive alternative solutions to add customizations to their AWS account post-creation.
You can use Customizations for AWS Control Tower to add customizations to your AWS Control Tower landing zone using an AWS CloudFormation template and service control policies (SCPs). To do so, customers have used a manual and self-managed deployment that can be labor-intensive and time-consuming to maintain. To overcome this challenge, AWS has introduced Account Factory Customization, where these customizations are available as a native AWS feature.
Cloud Storage Security (CSS) is an AWS Public Sector Partner and AWS Marketplace seller. CSS has an AWS qualified software offering, AWS security competency, and an AWS Authority To Operate designation. CSS helps you detect and prevent the spread of malware as well as locate and protect sensitive data with its antivirus and data classification offerings.
In this post, Ed and I show you how to automate CSS deployment using Account Factory Customization in your AWS Control Tower environment.
Prerequisites
- Deploy AWS Control Tower. You must already have AWS Control Tower deployed in your AWS account. Refer to Getting started with AWS Control Tower for more information.
- Subscribe to CSS in AWS Marketplace. To deploy CSS from AWS Control Tower, a subscription to Antivirus for Amazon S3 or Data Classification for Amazon S3 is required.
- Find CSS in AWS Marketplace and select the desired listing, either Antivirus for Amazon S3 or Data Classification for Amazon S3.
- To subscribe, select Continue to Subscribe. Review the end user license agreement (EULA) and accept the terms.
- Note that Effective Date and Expiration Date will briefly change to Pending. Once they are approved, select Continue to Configuration. You are now officially subscribed to the product.
- Configure CSS. To configure the product, select the correct option from the Delivery Method and Software Version dropdowns. We recommend you leave the default options and select Continue to Launch.
- Deploy CSS. To launch the software, scroll down under Container Images, under Deployment Templates, and select Click to Launch Antivirus for Amazon S3 Deployment or Click to Launch Data Classification for Amazon S3. This will open the AWS CloudFormation console in a different tab. Leave this tab open just in case you need to restart the stack.
- You can now deploy the product from AWS Control Tower.
Solution overview
Account Factory Customization adds a section to the bottom of AWS Control Tower called blueprint. A blueprint is the collection of configurations and best practices required for your target account that is standardized and repeatable. You can use predefined blueprints built and managed by CSS to quickly and easily deploy the CSS solution into your AWS account.
When you use this CSS Blueprint via Account Factory Customization, the blueprint automatically deploys a CSS AWS CloudFormation stack to launch antivirus or data classification tooling. The CloudFormation template creates the following resources in your AWS account:
- AWS Fargate with Amazon Elastic Container Service (Amazon ECS) cluster with one service and task to run the AWS Management Console.
- Amazon DynamoDB and AWS AppConfig to save software data.
- AWS Identity and Access Management (IAM) roles and policies.
- Amazon Cognito user pools for user management.
- Amazon Simple Notification Service (Amazon SNS) topic and CloudWatch log groups for logging and notification.
- Amazon Elastic Load Balancing (Amazon ELB). This one is optional for when you are using your own domain or to abstract the console’s public access a step further.
Through Account Factory Customization, CSS increases the visibility into product offerings in the Getting Started Library and simplifies the configuration and deployment of the CSS solution in your AWS account. You can now create custom accounts natively in AWS Control Tower while reducing the account maintenance overhead.
Solution architecture
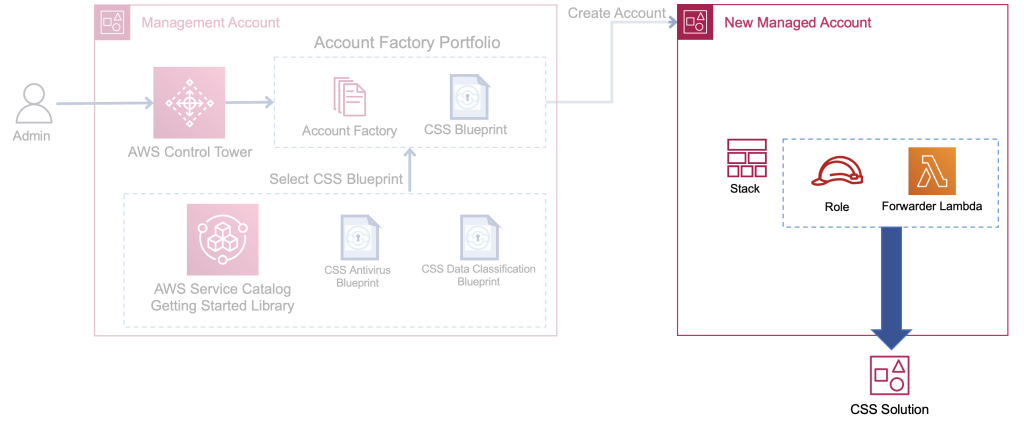
The following architecture diagram illustrates the Account Factory Customization component of AWS Control Tower and CSS integration. The AWS Control Tower management account contains the following components:
- In AWS Service Catalog, an administrator browses and finds the CSS blueprint.
- The administrator adds the blueprint to an existing portfolio or provisions a new portfolio with the blueprint.
- The administrator then adds the blueprint in the AWS Control Tower under Account Factory Customization. Refer to the following diagram.

- After the administrator successfully provisions a new account, an AWS Control Tower lifecycle event triggers an Amazon CloudWatch Events rule.
- The AWS CloudWatch Events rule triggers an AWS Lambda function.
- An AWS CloudFormation StackSet launches the CSS stack instance in the AWS Control Tower managed account. Refer to the following diagram.
Solution walkthrough: Automating Cloud Storage Security deployment using Account Factory Customization
When you follow this tutorial and select the CSS blueprint for linked accounts, deploying any new AWS account from AWS Control Tower connects to the existing CSS console deployment. This means that every bucket in your new AWS account will automatically be visible in the CSS console, so you can add protection to it.
To deploy the CSS solution using Account Factory Customization, follow these steps:
Step 1: Access the Getting Started Library
To deploy the CSS blueprint from AWS Control Tower, sign in to the AWS Service Catalog console. In the left navigation menu under the Administration section, choose the Getting Started Library.
Step: Choose the CSS blueprint
In the Getting Started Library screen, scroll down to the Products section and in the search bar, enter Cloud Storage Security. From the results that appear, select the Cloud Storage Security blueprint and choose the Add to Portfolio button.
Step 3: Add the CSS blueprint to your portfolio
On the next screen, select the radio button next to Select an existing portfolio and choose an existing portfolio from the drop-down menu. Alternatively, you can create a new AWS Service Catalog portfolio by selecting the radio button next to Create a new portfolio, fill the fields Portfolio name, Portfolio description, and Owner. To add the blueprint, choose the Add to Portfolio button.
Step 4: Navigate to AWS Control Tower and deploy the CSS blueprint
You must access AWS Control Tower from the AWS account in which you run AWS Organizations. In the AWS Control Tower console left navigation menu, select Organization and then Create Account. Under Account Factory Customization, select the CSS blueprint. Blueprints can be deployed to a home Region or all governed Regions.
Step 5: Validate CSS deployment
Gather the CSS console access information from the CloudFormation Stacklet. In the AWS CloudFormation window left navigation, choose Stacks. Select the stack corresponding to Cloud Storage Security, and choose Outputs tab. The value for the key ConsoleWebAddress contains the URL for the CSS console. Navigate to the CSS management console and validate the deployment. Refer to the CSS console access document for additional details.
Step 6: Turn on antivirus and scan the buckets
To turn on antivirus or classification scanning for a bucket, do the following:
- In the CSS management console main menu, select Bucket Protection.
- At the top of the page, to turn on antivirus scanning, choose the checkbox next to AV. If you want to turn on sensitive data discovery, choose the checkbox next to Classification.
- In the Bucket Protection table under Bucket Name, choose the checkbox next to the buckets you want to scan. To protect all buckets, above the table, choose the Select Visible button.
- From the drop-down menu, choose Actions and then Turn On Selected. Follow the prompts in the popup. To begin scanning, choose Scan Selected.
Step 7: Explore key reports
The CSS console is now populated with critical information and results that are displayed throughout curated reports. Some of the key reports include:
- Dashboard – This report is suitable for a high-level view of activities within your environment. It summarizes notable stats such as total GB scanned, total number of problem files, and bucket protection status. To access this report, in the CSS console main menu, select Dashboard.
- Problem Files Summary – This report is a running tally of all discovered issues, such as files that are infected with malware, files that have classified data, or files that couldn’t be scanned. To access this report, in the CSS console main menu, select Findings. Under the Filter Problem Files section in the report, you can sort by accounts, problem file types, date range and the analysis type, if applicable.
- Bucket Settings Overview – The Bucket Settings page offers a configuration overview for all of your buckets, showing whether a bucket is publicly accessible, encrypted, or has access logging enabled. To access this report, in the CSS console main menu, choose Monitoring and then from the dropdown, choose Bucket Settings. You can then filter buckets by account ID and Region.
Conclusion
In this post, we showed you how to automate Cloud Storage Security (CSS) deployment using Account Factory Customization in your AWS Control Tower environment. We also showed you how to turn on antivirus and classification scanning for your S3 buckets and how to access key reports.
Next steps
Try out CSS in AWS Marketplace with a fully featured 30-day no-cost trial. The product offers a consumption-based pricing structure. Prepaid discounts and private offers are also available. Contact CSS for more information about CSS solutions.
For additional information regarding the CSS and AWS Control Tower integration, refer to the Cloud Storage Security Help Docs.
About the authors
Ed Casmer
 |
Ed is a 20-year technology veteran with deep experience in cloud security. As CTO of Cloud Storage Security, he leads the development of the company’s antivirus and data classification solutions. Previously he served as Cloud CTO for Symantec. |
Gokhul Srinivasan
 |
Gokhul is a Senior Partner Solutions Architect supporting AWS Global Startup Partners. Gokhul has over 18 years of industry IT experience helping organizations modernize their digital platforms and deliver business outcomes. |