AWS Big Data Blog
Enabling Amazon QuickSight federation with Microsoft Entra ID (formerly Azure AD)
June 2025: This post was reviewed and updated for accuracy.
| As of August 2023, Amazon QuickSight is now an AWS IAM Identity Center enabled application. This capability allows administrators who subscribe to QuickSight to use IAM Identity Center to enable their users to log in with Azure AD and other external identity providers. For more information, see Simplify business intelligence identity management with Amazon QuickSight and IAM Identity Center (AWS blog post) and Configure your Amazon QuickSight account with IAM Identity Center in the QuickSight documentation. We recommend that you use this new integration. This blog post is provided as a reference for existing account configurations. |
Customers today want to establish a single identity and access strategy across all of their own apps, such as on-premises apps, third-party cloud apps (SaaS), or apps in AWS. If your organization use Microsoft Entra ID for cloud applications, you can enable single sign-on (SSO) for applications like Amazon QuickSight without needing to create another user account or remember passwords. You can also enable role-based access control to make sure users get appropriate role permissions in QuickSight based on their entitlement stored in Entra ID attributes or granted through Entra ID group membership. The setup also allows administrators to focus on managing a single source of truth for user identities in Entra ID while having the convenience of configuring access to other AWS accounts and apps centrally.
In this post, we walk through the steps required to configure federated SSO between QuickSight and Entra ID. We also demonstrate ways to assign a QuickSight role based on Entra ID group membership. Administrators can publish the QuickSight app in the MyAppsPortal to enable users to SSO to QuickSight using their Entra ID credentials.
The solution in this post uses an identity provider (IdP)-initiated SSO, which means your end-users must log in to Entra ID and choose the published QuickSight app in the Entra App Portal to sign in to QuickSight.
Registering a QuickSight application in Microsoft Entra admin center
Your first step is to create a QuickSight enterprise application in Microsoft Entra ID.
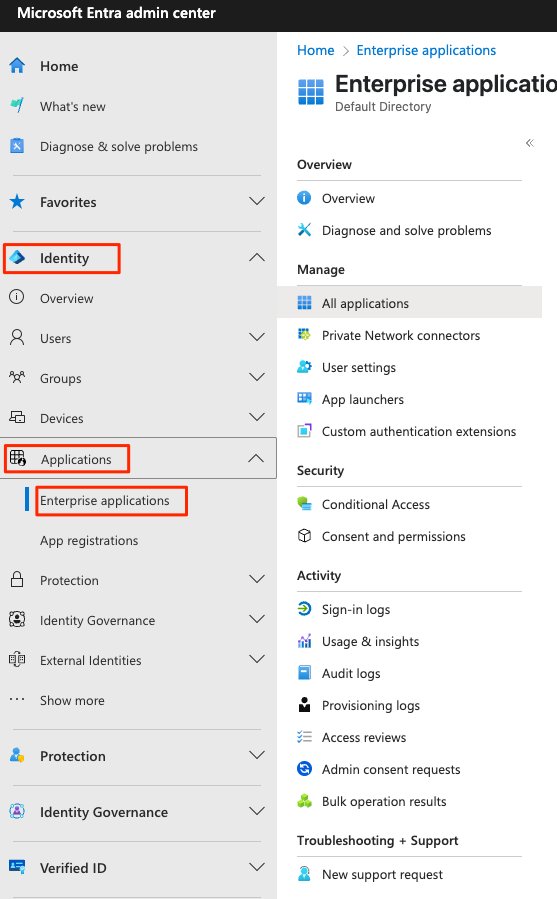
- Log in to your Entra Admin center using the administrator account in the tenant where you want to register the QuickSight application.
- Under Identity, expand Applications and choose Enterprise Applications.
- Choose New Application.
- Browse Microsoft Entra Gallery and search for Amazon Web Services
- Choose AWS Single – Account Access.
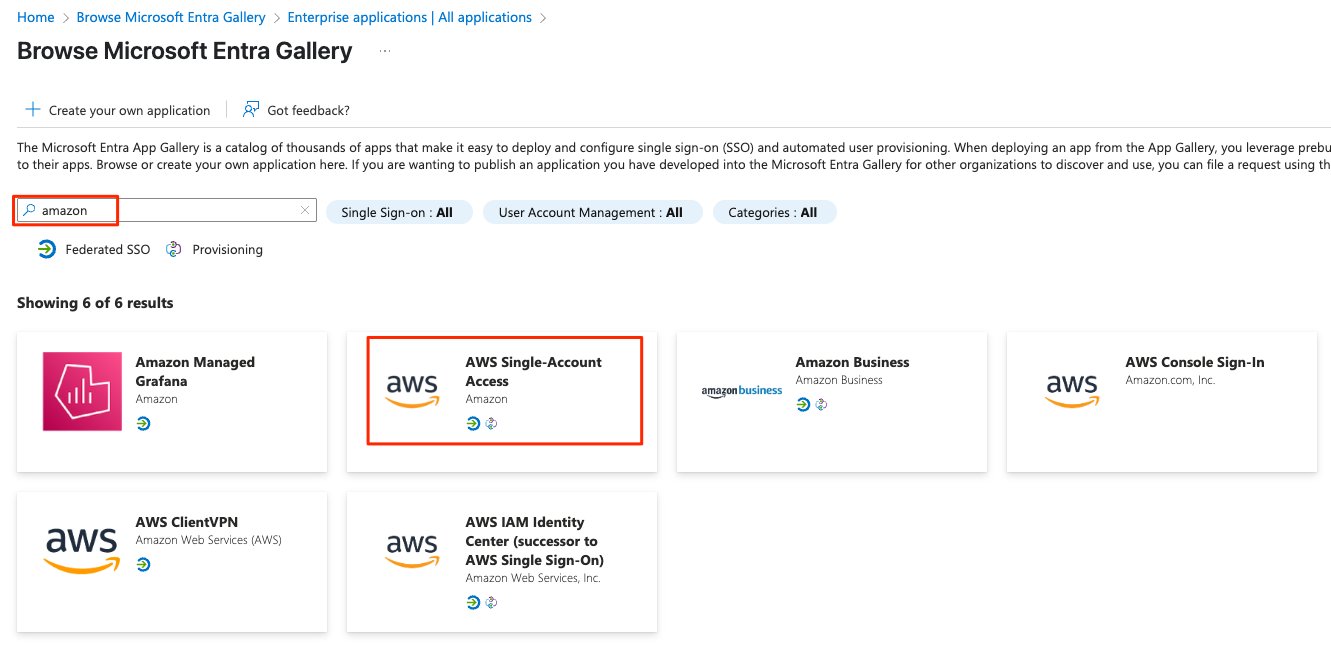
- For Name, enter
Amazon QuickSight. - Click on create the application.
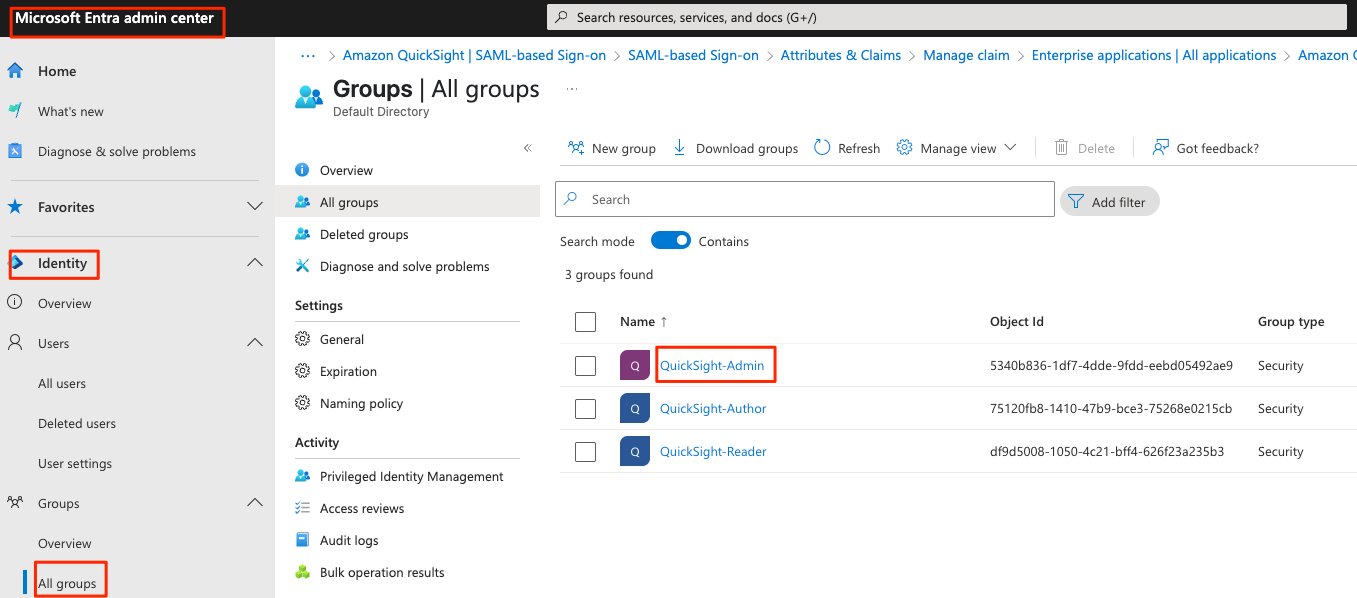
Creating users and groups in Microsoft Entra ID
You can now create new users and groups or choose existing users and groups that can access QuickSight.
- Under Identity, choose All groups and create New group
- For this post, you create three groups, one for each QuickSight role:
QuickSight-AdminQuickSight-AuthorQuickSight-Reader
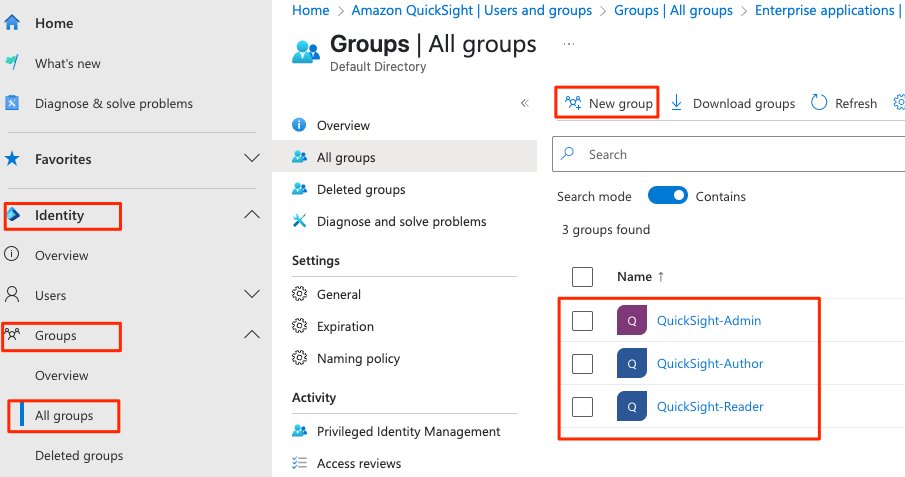
For instructions on creating groups in Microsoft Entra ID Center, see How to manage user and groups.
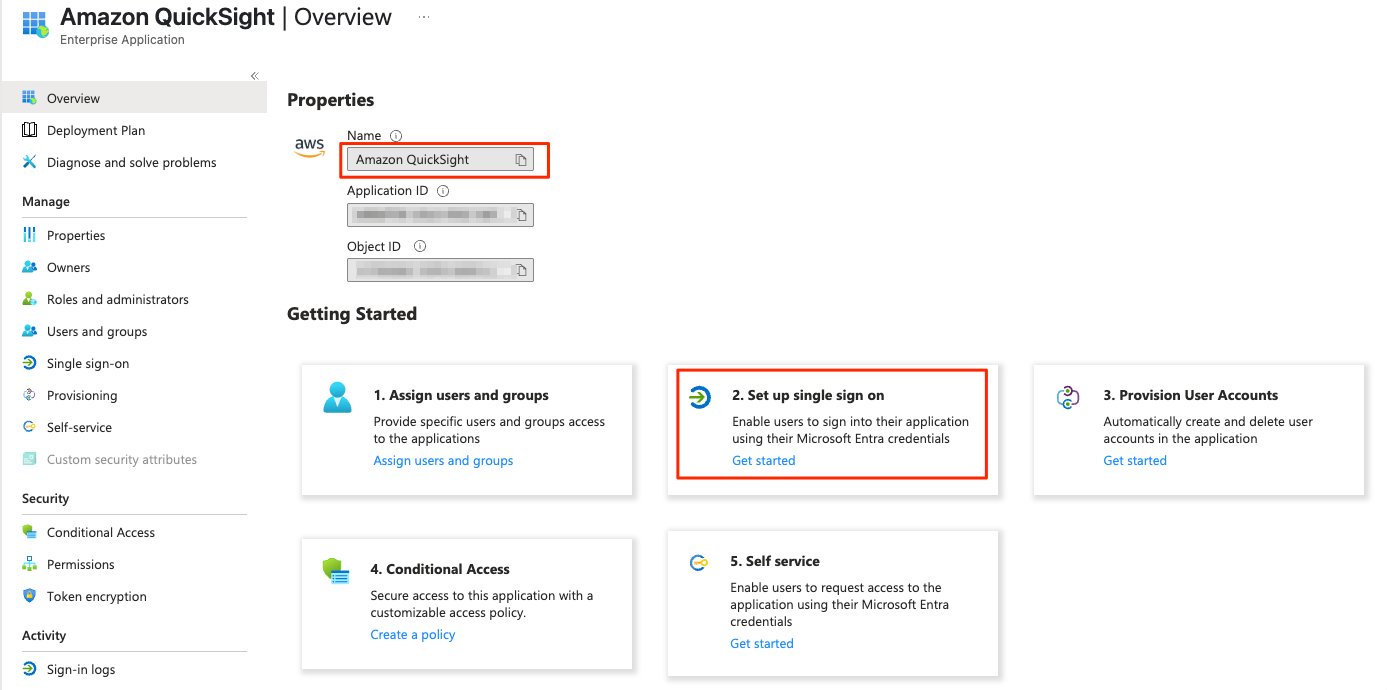
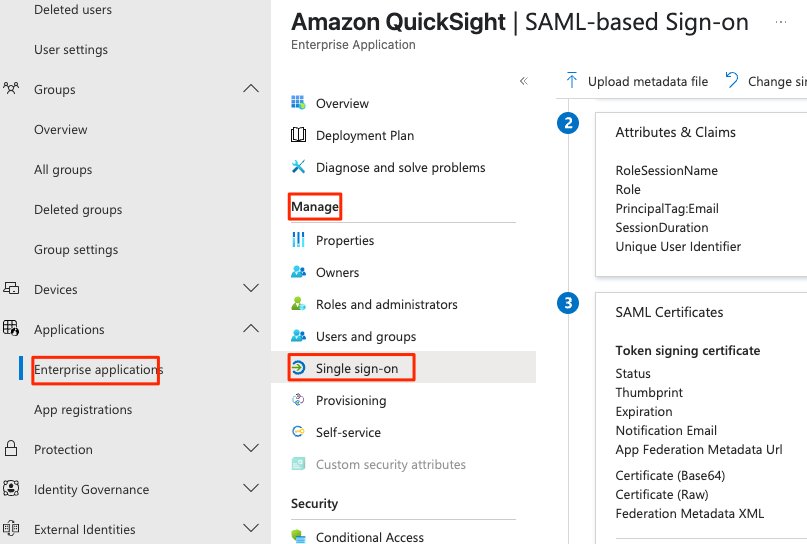
Configuring Entra SSO Integration in Entra ID
You can now start configuring the SSO settings for the QuickSight app.
- Choose Amazon QuickSight application that you created earlier.
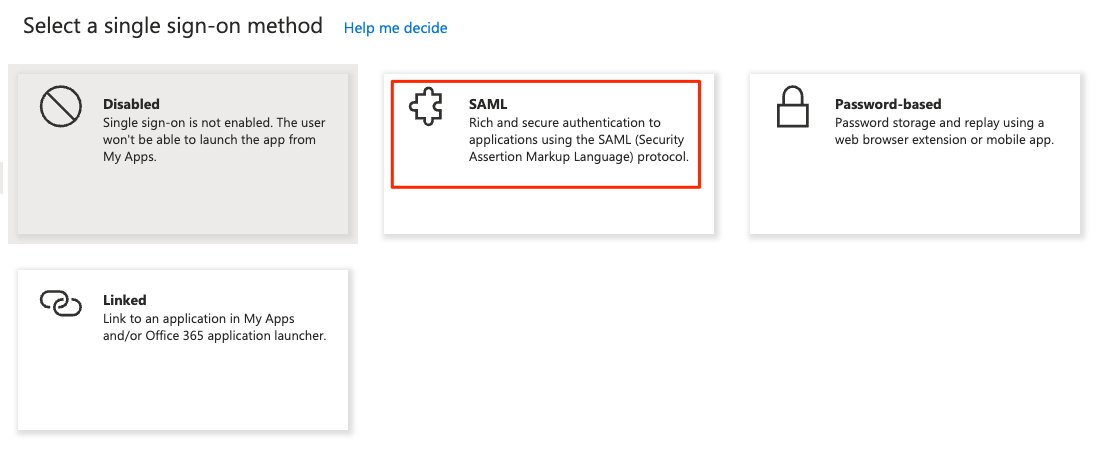
- Choose Set up a single sign-on , choose SAML.
- Under Set up Single Sign-On with SAML, choose Edit.
- In the Basic SAML Configuration
- For Identifier (Entity ID), enter
https://signin.aws.amazon.com/saml - For Reply URL (Assertion Consumer Service URL), enter
https://signin.aws.amazon.com/saml. - Leave Sign on URL blank.
- For Relay State, enter
https://quicksight.aws.amazon.com. - Leave Logout Url blank.
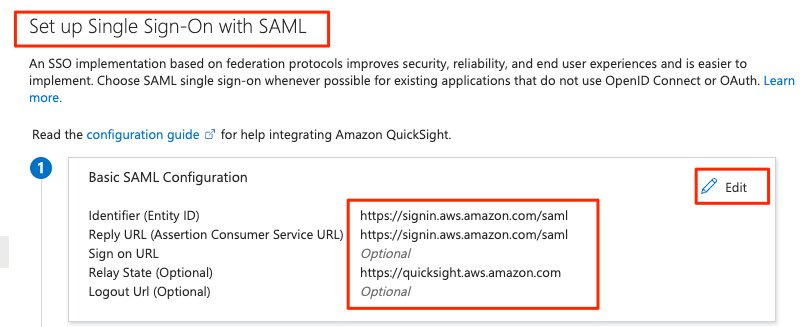
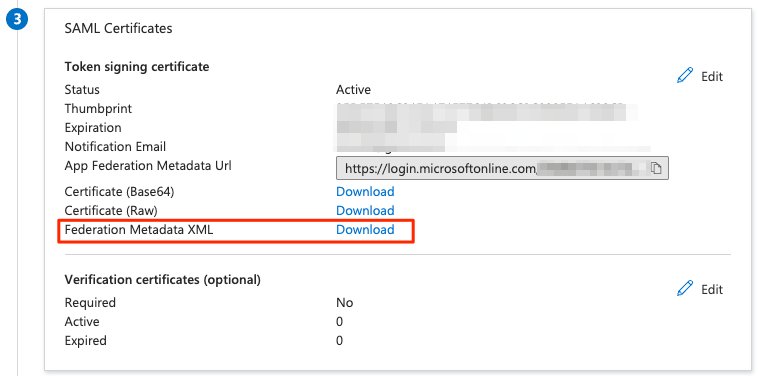
- Under SAML Certificates, choose Download next to Federation Metadata XML.
- You use this XML document later when setting up the SAML provider in AWS Identity and Access Management (IAM).
- Leave this tab open in your browser while moving on to the next steps.
Creating Microsoft Entra ID as your SAML IdP in AWS
- Open a new tab in your browser.
- Log in to the IAM console in your AWS account with admin permissions.
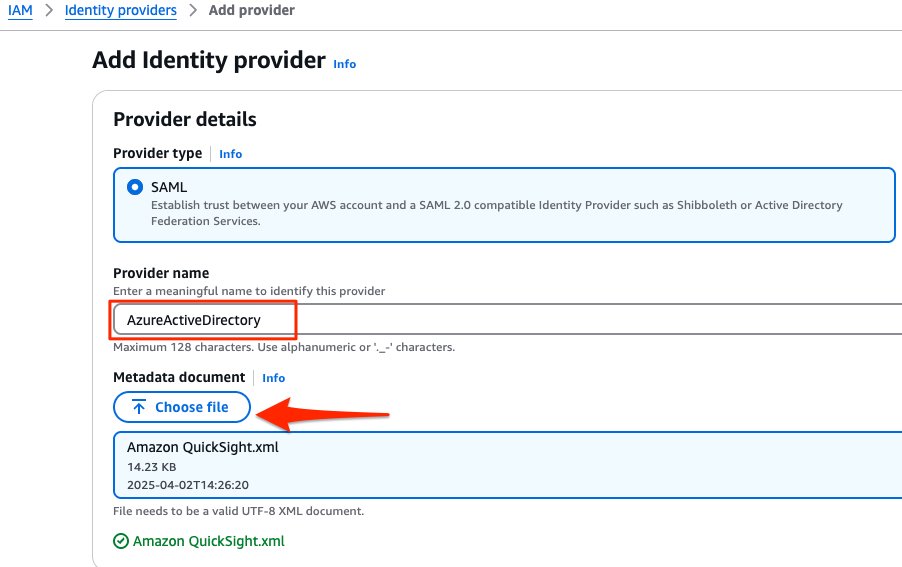
- On the IAM console, choose Identity providers.
- Choose Create provider.
- For Provider name, enter
AzureActiveDirectory. - Choose Choose File to upload the metadata document you downloaded earlier.
- Choose Next Step.
- Verify the provider information and choose Create.
- On the summary page, record the value for the provider ARN
(arn:aws:iam::<AccountID>:saml-provider/AzureActiveDirectory)
You need this ARN to configure claims rules later in this post.
Configuring IAM policy to list roles
Use the following steps to set up AzureListRole_policy. This policy will allow to fetch the roles from AWS Accounts in Microsoft Entra ID:
- On the IAM console, choose Policies.
- Choose Create Policy.
- Choose JSON and replace the existing text with the following code:
- Choose Review policy
- For Name enter AzureListRole_policy.
- Choose Create policy.
Create an IAM user
- On the IAM console, choose Users.
- Choose Create user “ AzureSSOUser”
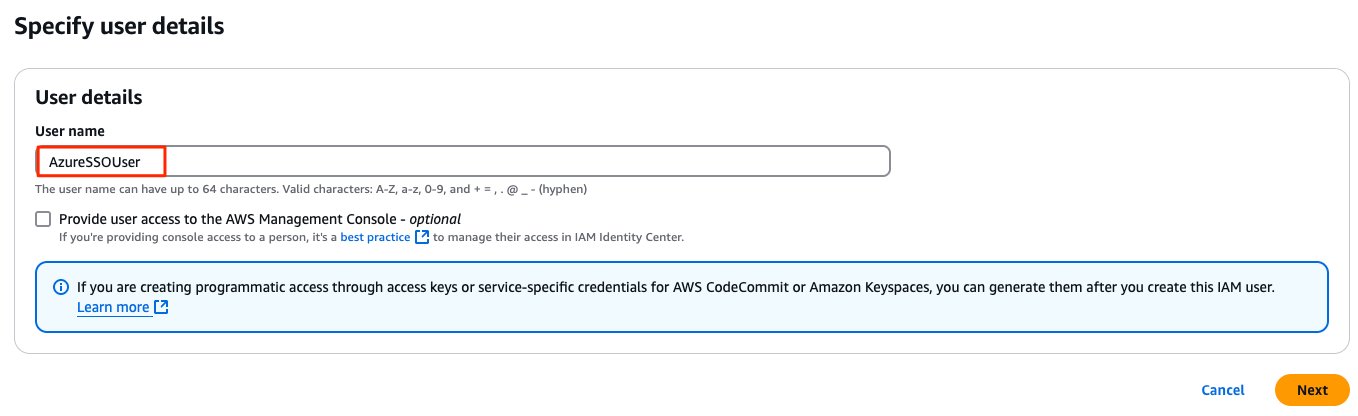
- Set Permissions.
- Choose the AzureListRole_policy IAM policy you created earlier.
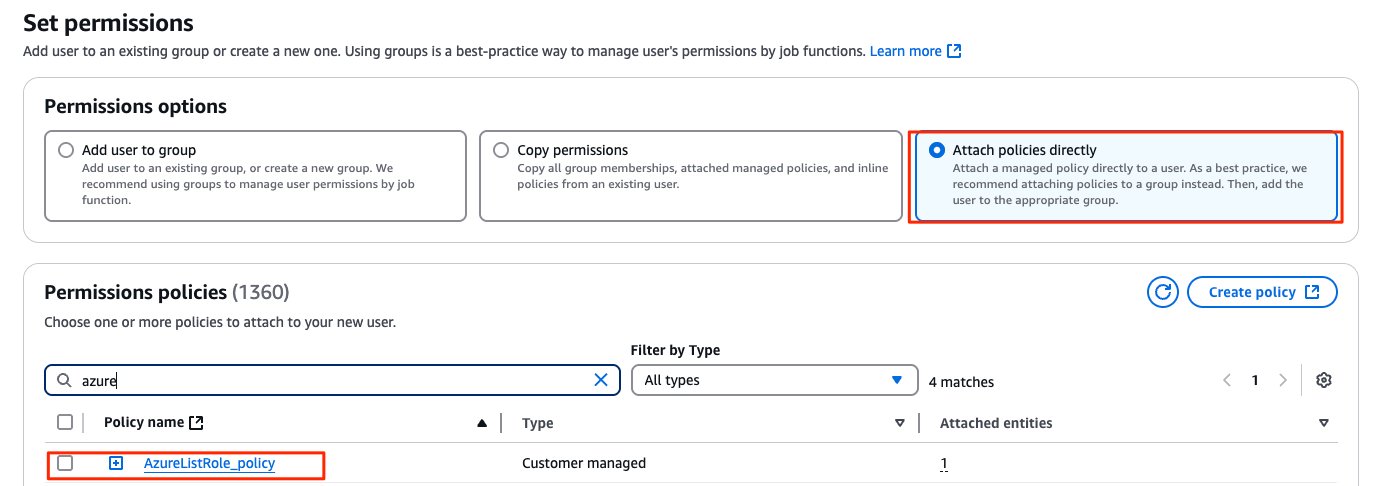
- Choose Next: Tags.
- Choose Review and Create
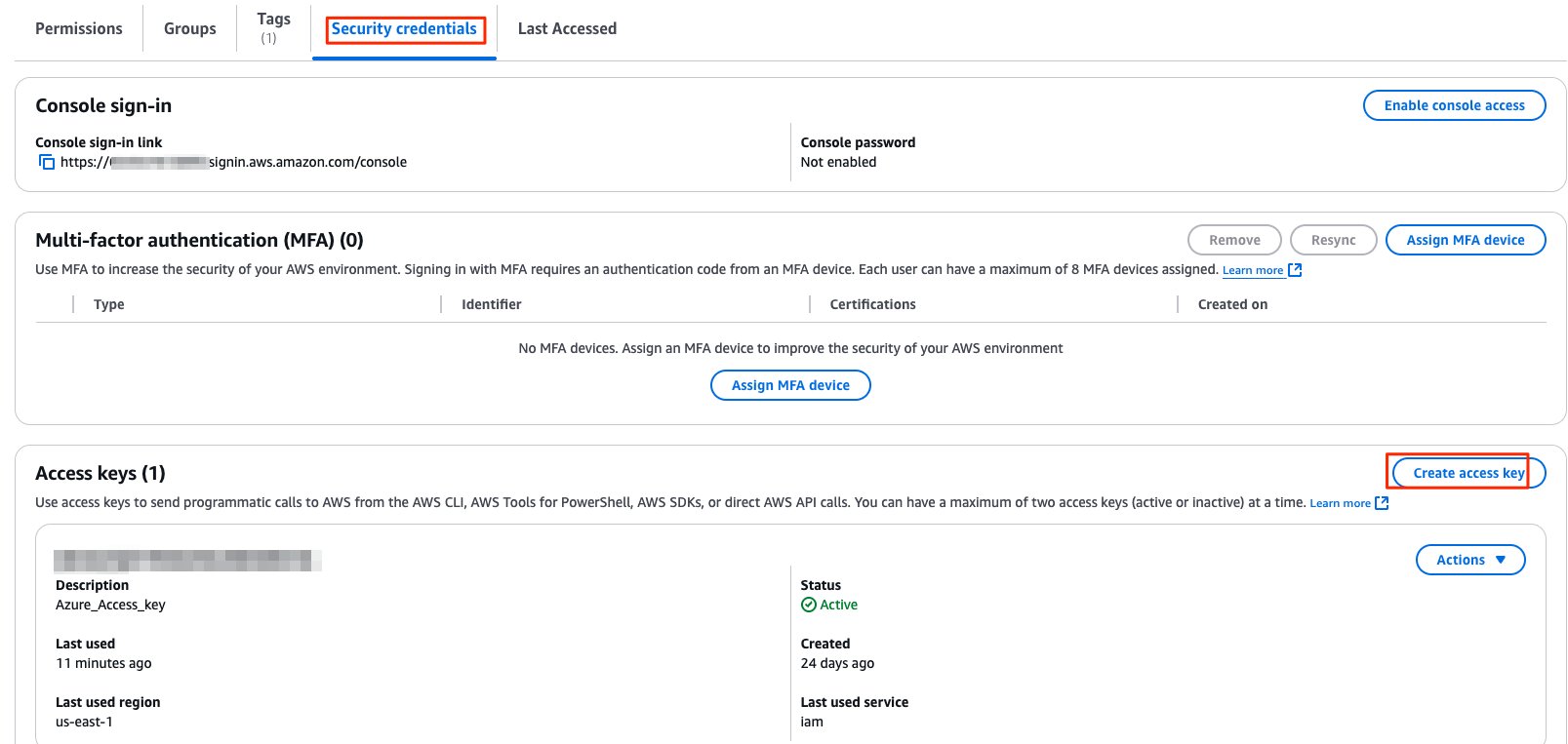
- Under the Security credential tab, create an access key. The security credential is used in the Microsoft Entra user provision section to connect to Amazon QuickSight’s API and synchronize user data.
Configuring IAM policies for roles in QuickSight
In this step, you create three IAM policies for different role permissions in QuickSight:
QuickSight-Federated-AdminQuickSight-Federated-AuthorQuickSight-Federated-Reader
Use the following steps to set up QuickSight-Federated-Admin policy. This policy grants admin privileges in QuickSight to the federated user:
- On the IAM console, choose Policies.
- Choose Create Policy.
- Choose JSON and replace the existing text with the following code:
- Choose Review policy
- For Name enter QuickSight-Federated-Admin.
- Choose Create policy.
Now repeat the steps to create QuickSight-Federated-Author and QuickSight-Federated-Reader policy using the following JSON codes for each policy:
QuickSight-Federated-Author
The following policy grants author privileges in QuickSight to the federated user:
QuickSight-Federated-Reader
The following policy grants reader privileges in QuickSight to the federated user:
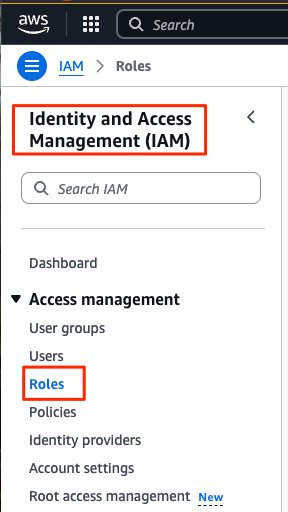
Configuring IAM roles
Next, create the roles that your Microsoft Entra users assume when federating into QuickSight. The following steps set up the admin role:
- On the IAM console, choose Roles.
- Choose Create role.
- For Select type of trusted entity, choose SAML 2.0 federation.
- For SAML 2.0-based provider, choose the provider you created earlier (AzureActiveDirectory).
- Select Allow programmatic and AWS Management Console access.
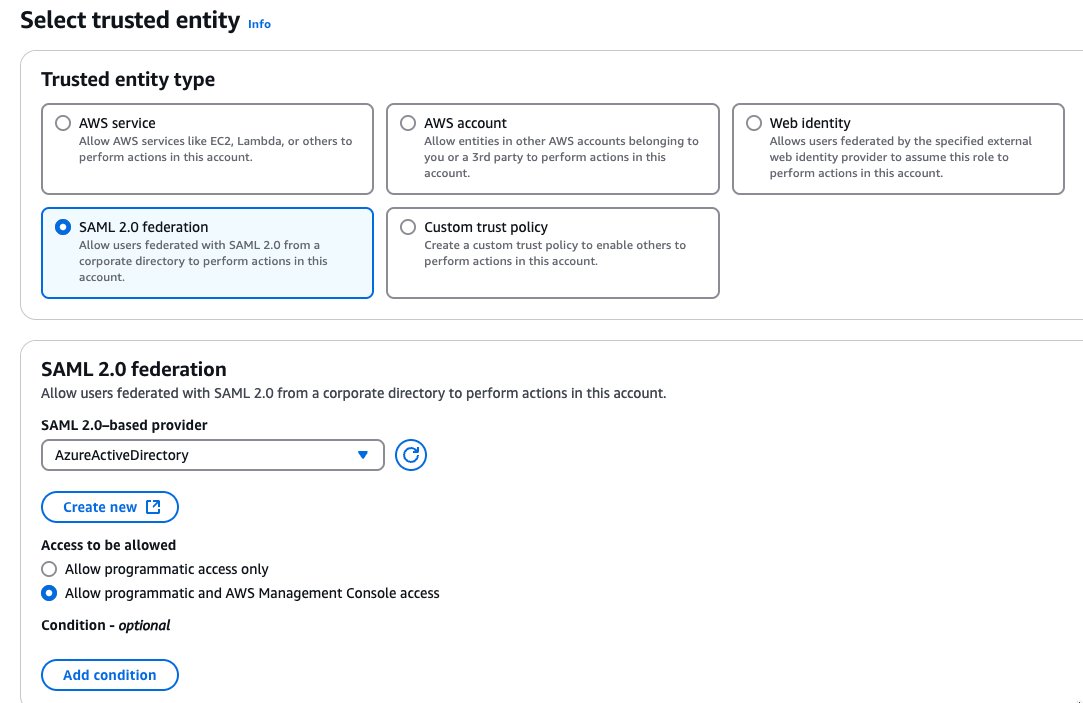
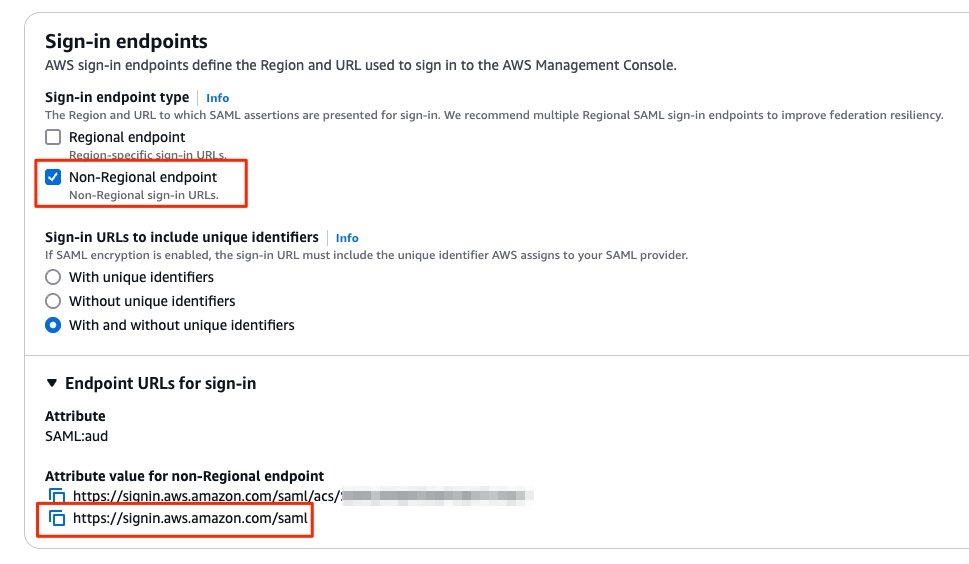
- For Attribute, make sure SAML:aud is selected.
- Value should show https://signin.aws.amazon.com/saml.
- Choose Next: Permissions.
- Choose the
QuickSight-Federated-AdminIAM policy you created earlier. - Choose Next: Tags.
- Choose Next: Review
- For Role name, enter QuickSight-Admin-Role.
- For Role description, enter a description.
- Choose Create role.
- On the IAM console, in the navigation pane, choose Roles.
- Choose the
QuickSight-Admin-Rolerole you created to open the role’s properties. - Record the role ARN to use later.
- On the Trust Relationships tab, choose Edit Trust Relationship.
- Under Trusted Entities, verify that the IdP you created is listed.
- Under Conditions, verify that SAML:aud with a value of
https://signin.aws.amazon.com/samlis present. - Configure Email sync for federated users with value aws:RequestTag/Email“:”*“ –
When you configure email syncing for federated users in QuickSight, users who log in to your QuickSight account for the first time have preassigned email addresses. These are used to register their accounts. With this approach, users can manually bypass by entering an email address. Also, users can’t use an email address that might differ from the email address prescribed.
- Repeat these steps to create your author and reader roles and attach the appropriate policies:
- For
QuickSight-Author-Role, use the policyQuickSight-Federated-Author. - For
QuickSight-Reader-Role, use the policyQuickSight-Federated-Reader.
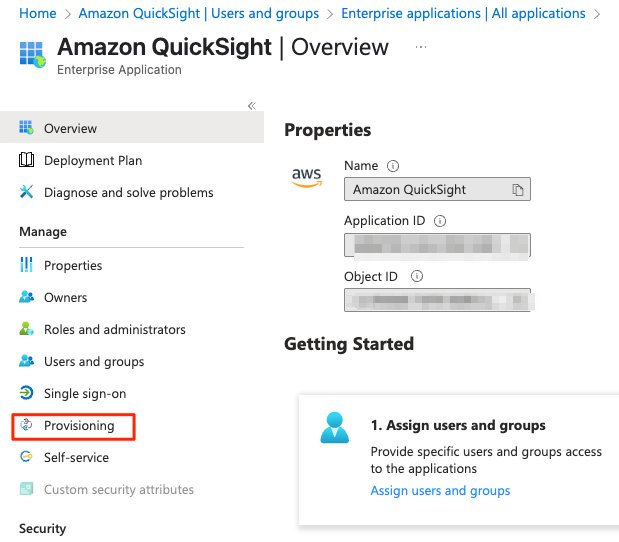
Configure an AWS access key for API Integration
Configuring Security Credential in Microsoft Entra which you have created and downloaded in the previous section.
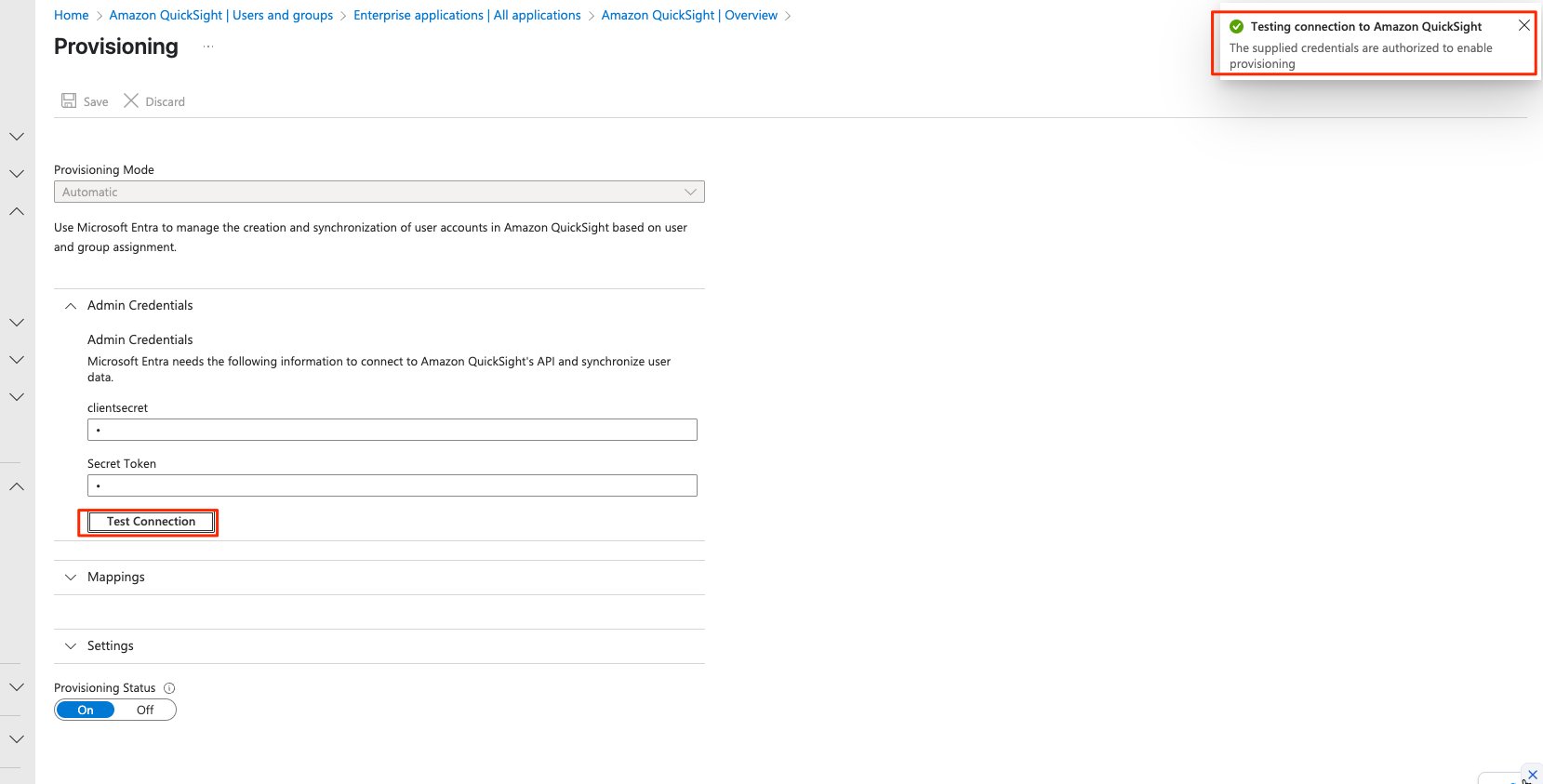
- Choose Amazon QuickSight application that you created earlier.
- Choose Provisioning.
- Choose Provisioning Mode to Automatic from drop down
- Enter Access key details under Admin Credentials add clientsecret and Secret Token
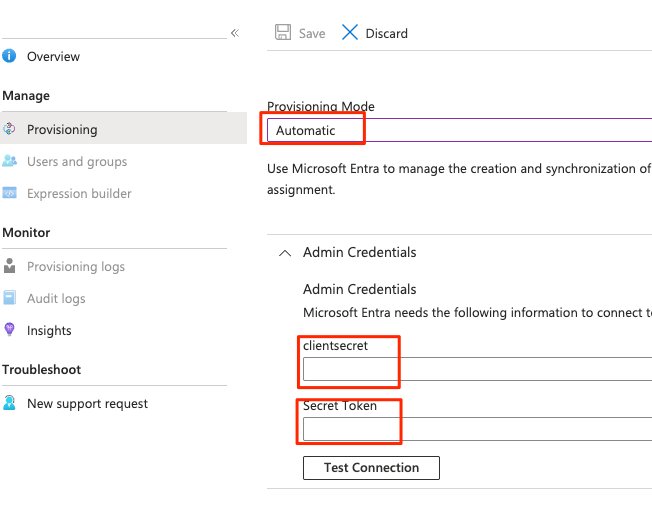
- Click on Test Connection, with correct credentials the connection would be established to enable provisioning
Configuring user Attributes and Claims in Microsoft Entra
In this step, you return to the application in Microsoft Entra admin center and configure the user claims that Entra ID sends to AWS. By default, several SAML attributes are populated for the new application, but you don’t need these attributes for federation into QuickSight. Under Required Claims edit the below 3 claims and update, delete unnecessary claims
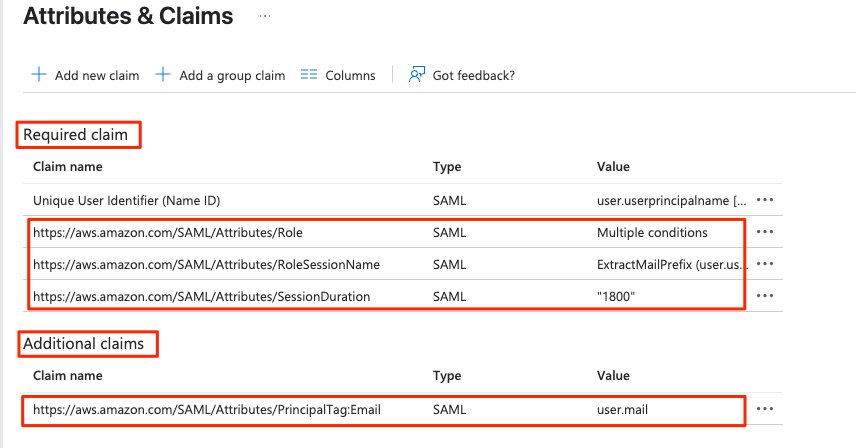
For this post, you update three required claims and add one additional claims:
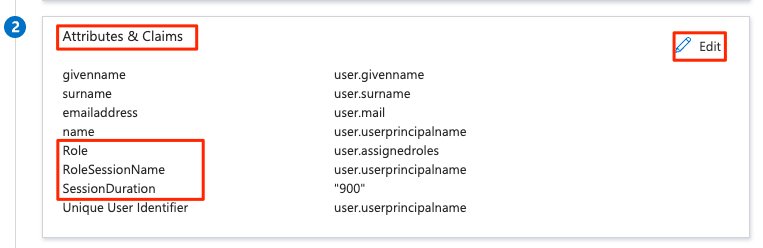
Required claims
RoleRoleSessionNameSessionDuration
Additional Claims
PrincipalTag:Email
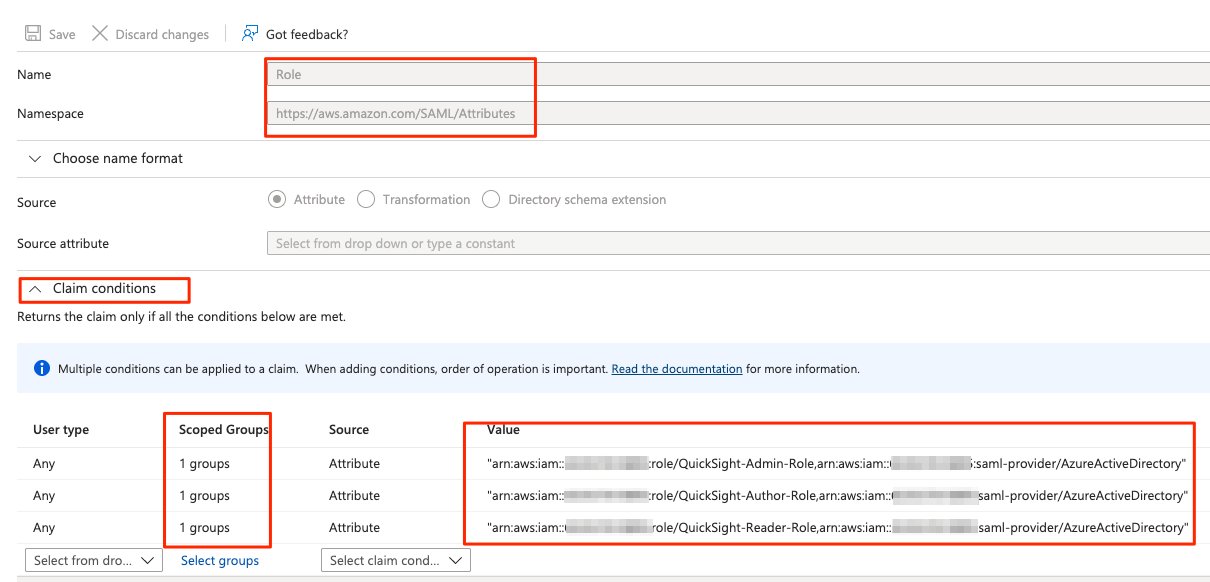
Update the Role claim
To update the Role claim, complete the following steps:
- Click Claim name https://aws.amazon.com/SAML/Attributes/Role
- Under Claim conditions, add a condition for the admin, author, and reader roles. Use the parameters in the following table and make sure to replace <Account ID> with your AWS account ID:
| User Type | Scoped Group | Source | Value |
| Any | QuickSight-Admin | Attribute | arn:aws:iam::<Account ID>:role/QuickSight-Admin-Role,arn:aws:iam::<Account ID>:saml-provider/AzureActiveDirectory |
| Any | QuickSight-Author | Attribute | arn:aws:iam::<Account ID>:role/QuickSight-Author-Role,arn:aws:iam::<Account ID>:saml-provider/AzureActiveDirectory |
| Any | QuickSight-Reader | Attribute | arn:aws:iam::<Account ID>:role/QuickSight-Reader-Role,arn:aws:iam::<Account ID>:saml-provider/AzureActiveDirectory |
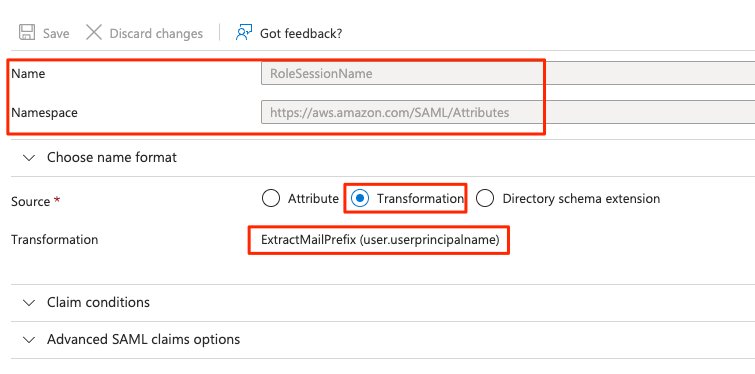
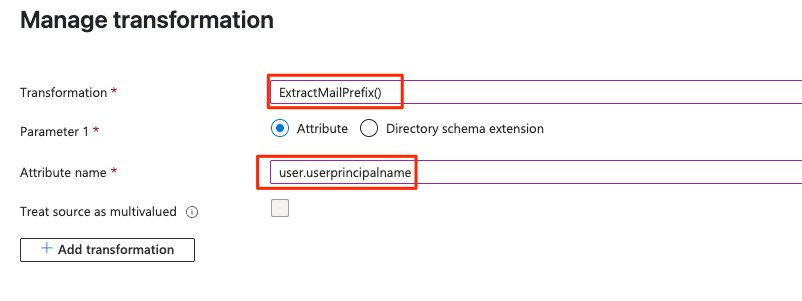
Update RoleSessionName claim
To update your RoleSessionName claim, complete the following steps:
- Click, Claim name https://aws.amazon.com/SAML/Attributes/RoleSessionName
- For Source, choose Transformation.
- For Transformation, enter ExtractMailPrefix().
- For Parameter 1, enter user.userprincipalname.
We use the ExtractMailPrefix() function to extract the name from the userprincipalname attribute. For example, the function extracts the name joe from the user principal name value of joe@example.com. IAM uses RoleSessionName to build the role session ID for the user signing into QuickSight. The role session ID is made up of the Role name and RoleSessionName, in Role/RoleSessionName format. Users are registered in QuickSight with the role session ID as the username.
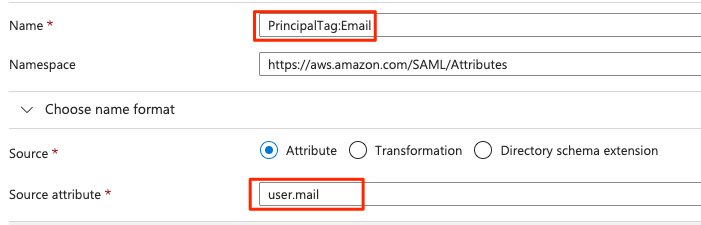
Creating the PrincipalTag:Email for Additional claim
To create claim, PrincipalTag:Email, complete the following steps:
- Choose Add new claim.
- For Name, enter PrincipalTag:Email
- For Namespace, enter https://aws.amazon.com/SAML/Attributes.
- For Source, choose Attribute.
- For Source attribute, enter “user.mail”
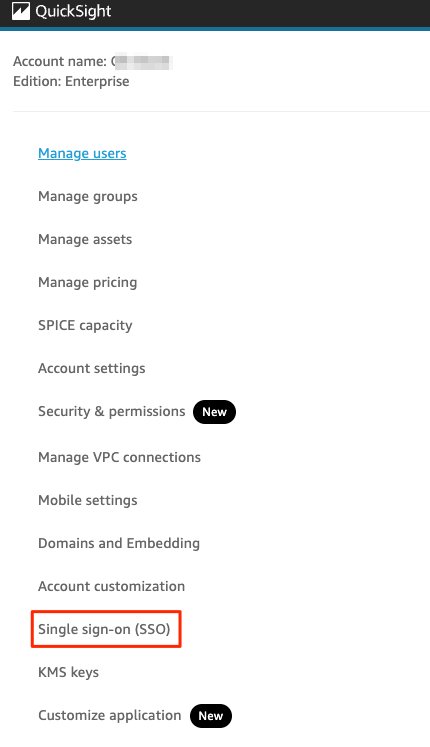
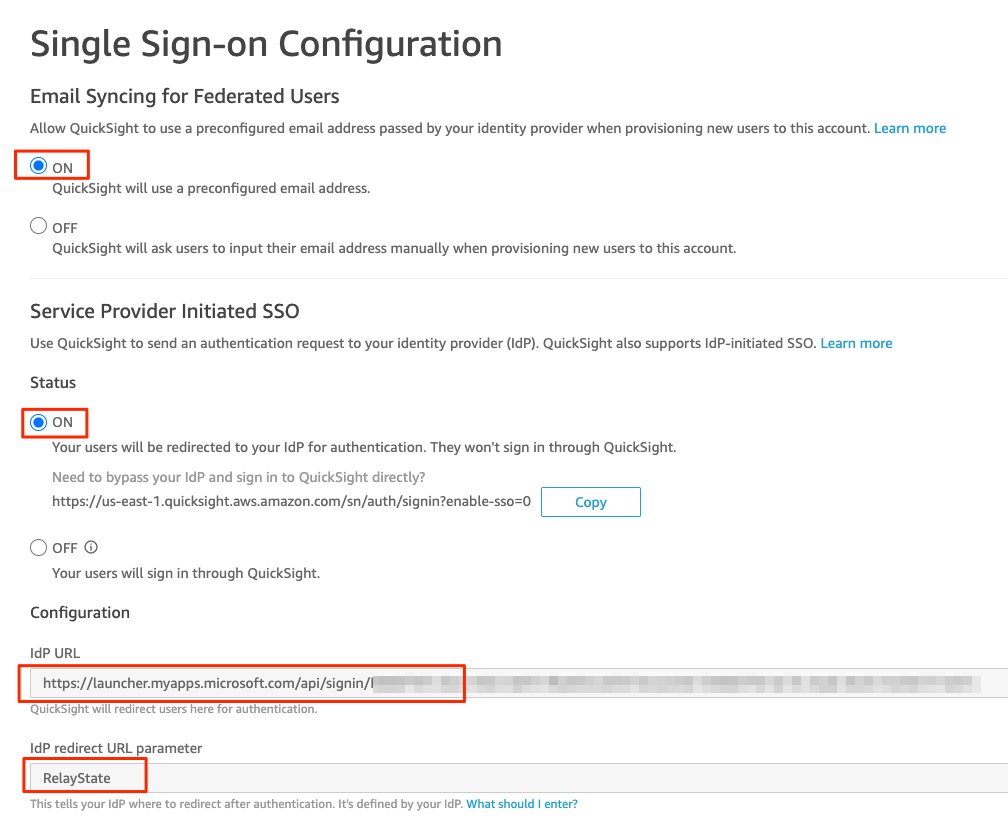
Configuring Single Sign-on in Amazon QuickSight
To enable the SSO Configuration in QuickSight, Follow the steps
- Login to QuickSight with Admin role
- Click Manage QuickSight
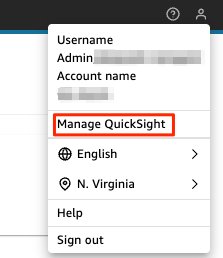 On the left panel, click Single sign-on (SSO)
On the left panel, click Single sign-on (SSO)- Select ON for Email syncing for Federated Users
- Select ON for Service Provider Initiated SSO
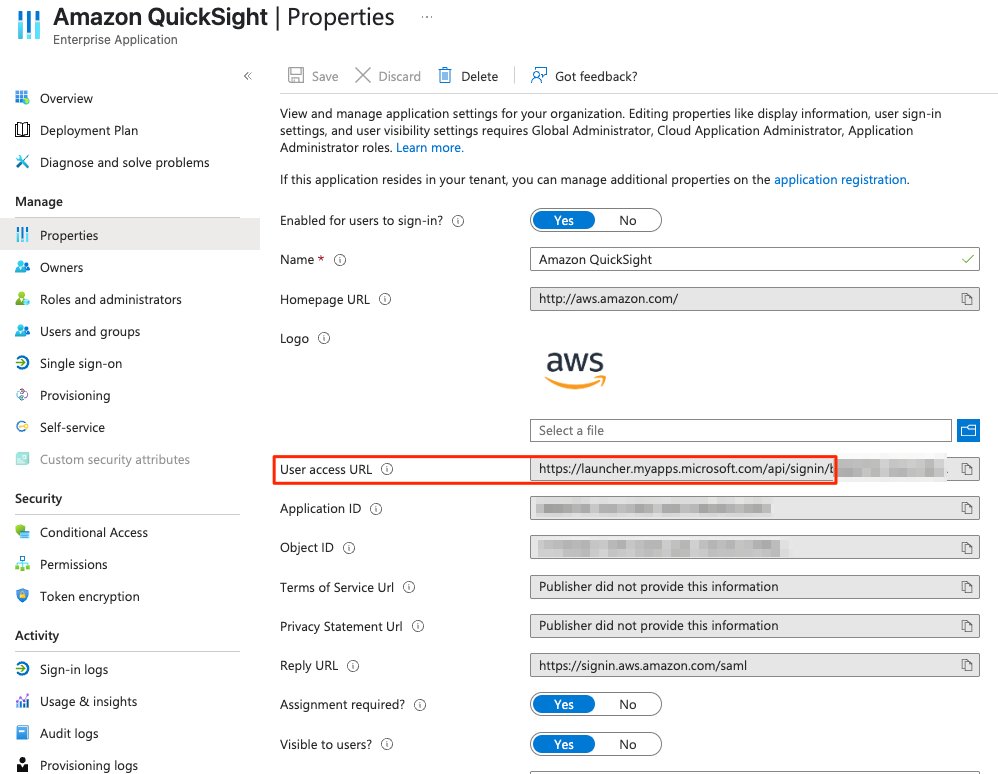
- Under configuration, provide the appropriate User access URL as Idp URL from your Entra ID Application properties
- Idp redirect URL parameter, set RelayState
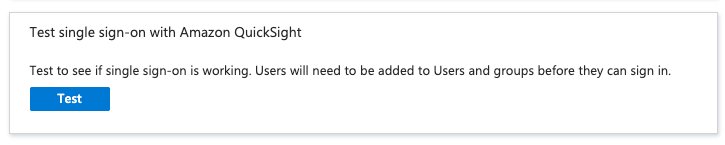
Testing the application
You’re now ready to test the application.
- In the Microsoft Entra admin Center, under Identity, choose All groups.
- Update the group membership of the
QuickSight-Admingroup by adding the current user to it.
- Under Enterprise Applications, choose Amazon QuickSight.
- Under Manage, choose Single sign-on.
- ClickTest to test the authentication flow.
- Log in to QuickSight as an admin.
The following screenshot shows you the QuickSight dashboard for the admin user.
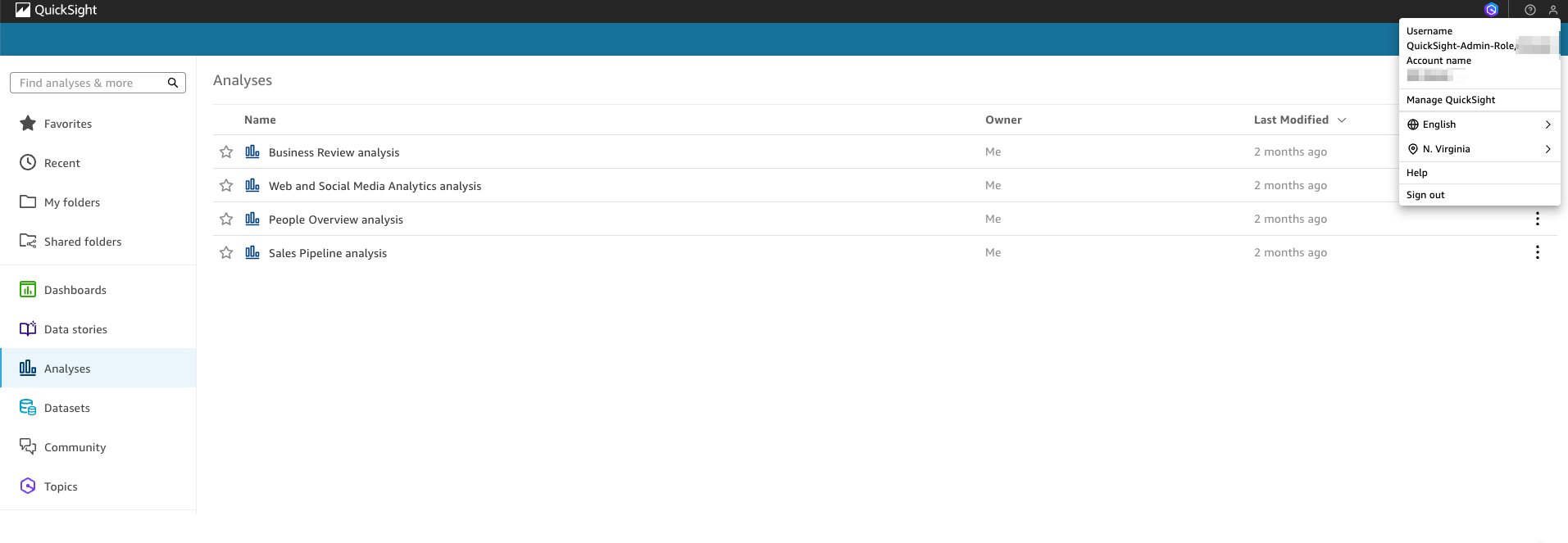
- Remove the current user from
QuickSight-AdminEntra group and add it toQuickSight-Authorgroup.
When you test the application flow, you log in to QuickSight as an author.
- Remove the current user from
QuickSight-Authorgroup and add it toQuickSight-Readergroup.
When you test the application flow again, you log in as a reader.
Removing the user from the Entra group will not automatically remove the registered user in QuickSight. You have to remove the user manually in the QuickSight admin console. For details on user management inside QuickSight, see managing user access.
Deep-linking QuickSight dashboards
You can share QuickSight dashboards using the sign-on URL for the QuickSight application published in the Microsoft Entra Apps portal. This allows users to federate directly into the QuickSight dashboard without having to land first on the QuickSight homepage.To deep-link to a specific QuickSight dashboard with SSO, complete the following steps:
- Under Enterprise Applications, choose Amazon QuickSight
- Under Manage, choose Properties.
- Locate the User access URL.
- Append
?RelayStateto the end of the URL containing the URL of your dashboard. For example,
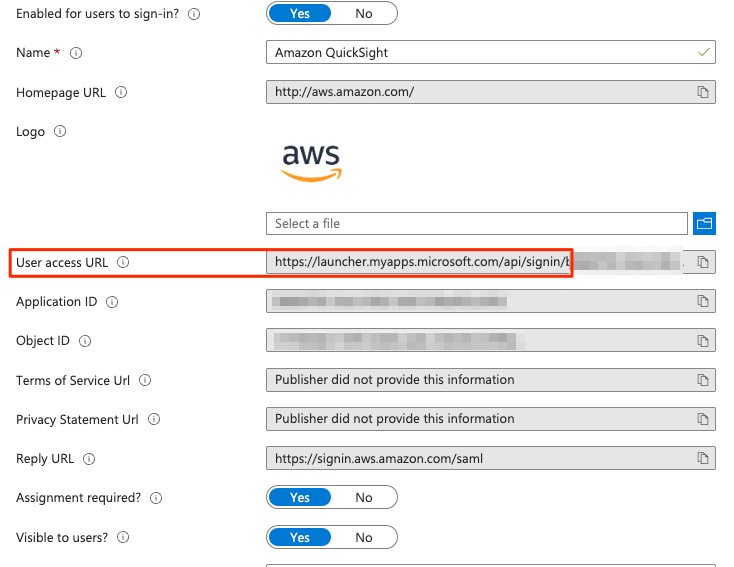
You can test it by creating a custom sign-in URL using the RelayState parameter pointing to an existing dashboard. Make sure the user signing in to the dashboard has been granted proper access.
Summary
This post provided step-by-step instructions to configure a federated SSO with Microsoft Entra ID as the IdP. We also discussed how to map users and groups in Entra Admin Center to IAM roles for secure access into QuickSight.If you have any questions or feedback, please leave a comment.
About the authors
 Adnan Hasan is a Global GTM Analytics Specialist at Amazon Web Services, helping customers transform their business using data, machine learning and advanced analytics.
Adnan Hasan is a Global GTM Analytics Specialist at Amazon Web Services, helping customers transform their business using data, machine learning and advanced analytics.
 Deepak Sahi is a Solutions Architect at AWS based out of Zurich, Switzerland. He has close to two decades of experience in the field of Data Analytics, primarily in Business intelligence and data warehousing. He has worked worldwide as a consultant in domains such as Telcom, Finance, Insurance, Healthcare etc. for many Fortune 500 Companies. He is currently focusing on manufacturing companies in Switzerland at the same time he is a member of SME for Amazon QuickSight. He helps them build secure and innovative cloud solutions, enable data-driven decisions and solve their business challenges.
Deepak Sahi is a Solutions Architect at AWS based out of Zurich, Switzerland. He has close to two decades of experience in the field of Data Analytics, primarily in Business intelligence and data warehousing. He has worked worldwide as a consultant in domains such as Telcom, Finance, Insurance, Healthcare etc. for many Fortune 500 Companies. He is currently focusing on manufacturing companies in Switzerland at the same time he is a member of SME for Amazon QuickSight. He helps them build secure and innovative cloud solutions, enable data-driven decisions and solve their business challenges.