AWS Big Data Blog
Turn Windows DHCP Server logs into actionable metrics using Amazon Kinesis Agent for Windows
Understanding Windows system and service health on a global scale is challenging. You capture server log data, and then analyze and manipulate the data in real time to create actionable telemetry insights. Amazon Kinesis Agent for Microsoft Windows makes it efficient to ingest Windows server log data into your AWS ecosystem for analysis. This blog post discusses using Kinesis Agent for Windows to capture and aggregate Windows Dynamic Host Configuration Protocol (DHCP) server logs. Then turning that data into service health graphs in Amazon CloudWatch.
How do you quantify network access metrics of a team across the globe? Specifically, in the northeast corner of the ninth floor in that team’s building? Does the Wireless Access Point (WAP) in that part of the building provide the team network access reliably and consistently? Or does the subnet that WAP is configured with, run out of IP addresses and deny network access to that team? This is the more definitive problem this article solves using Kinesis Agent for Windows.
Detecting customer impact as a result of scope exhaustion
Windows DHCP leases are divided into network subnets, referred to as scopes. These scopes are mapped to dedicated physical locations on a large corporate network. A scope is considered to be full when all IP addresses that belong to it are in use. This is known as “scope exhaustion”. When “scope exhaustion” occurs, any new clients are denied an IP address lease on that subnet. This is referred to as a “lease refusal.” Commonly, a DHCP scope is defined for the exact number of devices that are expected, and no more. In these instances an exhausted scope is expected, which makes an alert meaningless if it is based purely on scope exhaustion.
When a Windows DHCP server refuses a lease due to “scope exhaustion,” it writes a specific record to the DHCP audit log. The record for this event is Event ID 14, “a lease request could not be satisfied because the scope’s address pool was exhausted.” The record itself has limited value unless the records are continuously observed and tallied for occurrences and patterns. Monitoring for this scenario is a challenge when there is a globally scaled DHCP service with hundreds of Windows Server DHCP failover relationships, meaning two servers per relationship. And moreover when the service has thousands of scopes and millions of IP addresses. Here’s where the Kinesis Agent for Windows provides quite an advantage.
The DHCP Server log files are in a default C:\Windows\System32\dhcp directory. The IPv4 log file names are prefixed with DhcpSrvLog. The IPv6 log file names are prefixed with DhcpV6SrvLog. This post focuses on the IPv4 logs.
The log files have a header at the top of each file that defines and describes the potential Event IDs. It also shows the order of the comma-separated values in each log record. For a better idea about these logs, refer to the ones generated by your DHCP service. For more information, see Analyze DHCP Server Log Files, which is the official documentation from Microsoft. The following is a set of example log records that include an Event 14 record, indicating that a scope is full.
Important – Windows DHCP Server logs do not include data to distinguish which server they were generated on, which is important information when analyzing an aggregated dataset for full scope events. The Kinesis Agent for Windows includes a feature called ObjectDecoration. It allows custom values to be injected into each log record. Values can be hardcoded or dynamically created from environment variables, such as ComputerName, located on each computer. In this use case, there are multiple DHCP failover relationships which metrics are posted for. So the values of the failover relationship names are interpreted from the server hostnames. An example hostname is: DHCP-<FailoverRelatioshipName>-nn. The appsettings.json file contents used for configuring Kinesis Agent for Windows is provided in this post, and includes ObjectDecoration used in this implementation.
Collecting, storing, and analyzing DHCP server logs
This section guides you through setting up the AWS serverless infrastructure to collect, store and analyze Windows DHCP server logs. You first define two workflows: log ingestion and log processing.
Log Ingestion
Kinesis Agent for Windows detects new records in near real-time and sends them to an Amazon Kinesis Data Firehose delivery stream. The delivery stream is configured to send batches of data, on a time interval or a size limit, in a compressed format to an Amazon S3 bucket.
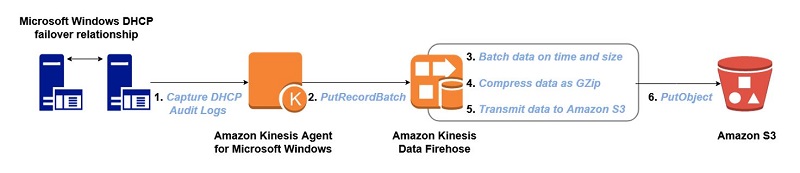
Log Processing
The S3 bucket is configured to send Amazon S3 Event Notifications to an Amazon Simple Notification Service (Amazon SNS) topic. An AWS Lambda function is subscribed to the SNS topic. When it is triggered, it gets the object from S3, and decompresses and processes the log data. It then posts an Amazon CloudWatch metric for every Event ID 14 found.
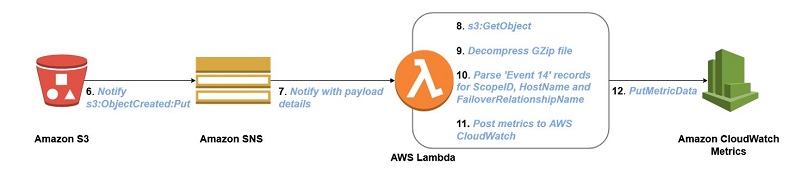
Note: By triggering from the S3 bucket to an Amazon SNS topic, other consumers of the data can subscribe to the same SNS topic. Also, you can filter out records other than Event 14 directly on the Kinesis Agent for Windows using the RegexFilterPipe feature, if you do not want to collect them. Additionally, you can configure Kinesis Agent for Windows to “pipe” another stream of the same log data or its filtered subset to a separate, dedicated, Kinesis Data Firehose, or other destination supported by the sink declarations for Kinesis Agent for Windows.
Build the log ingestion infrastructure
The next step is to create the AWS resources. Because the log source is a Windows environment, we use PowerShell to automate the build process. The AWS Tools for PowerShell provides cmdlets for developing and managing infrastructure within the AWS ecosystem.
For help with the log ingestion path, see this article about Using Amazon Kinesis Firehose that shows how to automate building the Amazon S3 bucket and Amazon Kinesis Firehose delivery stream. The Kinesis Agent for Windows setup part of this path is covered after the infrastructure components are built.
After creating your S3 bucket and Kinesis Firehose delivery stream, do the following to add the additional configurations:
- Enable a bucket lifecycle policy to archive data to Amazon Glacier. This helps to minimize storage costs.
- Compress the data prior to transmitting to Amazon S3. This helps to minimize storage costs.
- Batch the data prior to transmitting to Amazon S3. This batches the most data with the shortest delivery time.
- Include a S3 bucket prefix for the log destination. This helps to separate logs with different schemas.
- Enable CloudWatch logging on the delivery stream. This helps to help troubleshoot any potential problems with ingestion.
Here is a code sample for making these configurations.
Build the log processing infrastructure
Lambda function for processing logs and creating metrics
The Lambda function is where the log data is actually inspected for identifying Scope Full events and posting metrics. The code was originally written in Python. However, it could be converted to run with the recently released PowerShell language support in AWS Lambda. This script should be named LeaseRefusalMetrics.py. It should be in the contents of the LeaseRefusalMetrics.zip file as indicated in the buildout process shown in the previous section. The workflow is as follows:
- Get and decompress the S3 object.
- Read the S3 object data in as a byte stream and break it into individual records.
- Scan the data for Event 14 (scope exhausted).
- Break apart each comma-separated value from the Event 14 record.
- Parse out values for the metric dimensions.
- Post metric data to CloudWatch, resulting in three metrics.
Configure Kinesis Agent for Windows to send logs
Next, configure Kinesis Agent for Windows to start collecting log data so it can be processed. Follow the Installing Kinesis Agent for Windows guide to install and configure agents. The appsettings.json file contents used by the agents are shown below, along with some comments that are particular to this implementation.
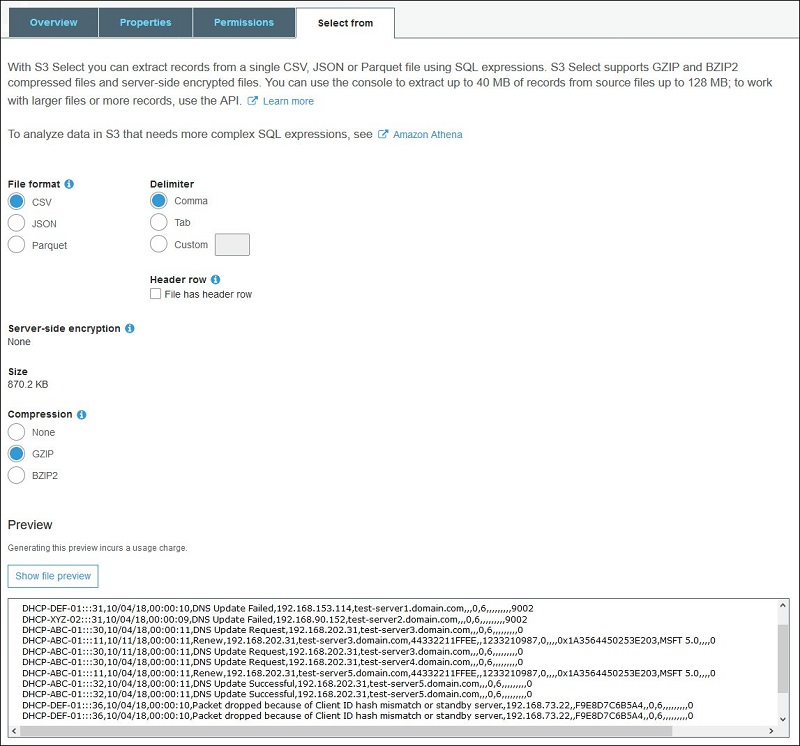
View the log data
The following is an efficient way to view the ingested data in Amazon S3:
- Sign in to the AWS Management Console and open the Amazon S3 console. Go to the S3 bucket that the Kinesis Data Firehose delivery streams are streaming to, and choose an object.
- Choose the Select from
- Under File format, choose CSV, and then choose Show file preview.
You should see DHCP logs appear in the preview text box. It includes the ObjectDecoration that was applied to the Kinesis Agent for Windows configuration:
Log processing output
The following set of metrics are populated in CloudWatch as a result of the log processing:
- An aggregate lease refusal metric of all DHCP failover relationships globally.
- A metric graph that shows lease refusals for each DHCP failover relationship.
- A metric graph for lease refusals for each scope, with the owning DHCP failover relationship.
View the graphs in CloudWatch Metrics
This section shows how to view the graphs that the Lambda function populated in CloudWatch metrics. This presumes there are Event 14 records that have been processed.
Note: You can inject a test Event 14 record into your DHCP log file. For more information, see Using Amazon CloudWatch Metrics or, more specifically, how to View Available Metrics.
To view the graphs:
- Sign in to the Amazon CloudWatch console.
- In the navigation pane, choose Metrics, and browse to the DHCPService namespace that the Lambda function populated. In the namespace, you should see a set of three metric dimensions that were also created (“DHCPScopeId, DHCPFailoverRelationship“, “DHCPFailoverRelationship“, and “ScopeFullLeaseRefusal“).
- You can drill down further into any one of the metric dimensions to view the graphs. Choose the ScopeFullLeaseRefusal metric dimension. There should be one metric present, AggregateLeaseRefusal, which is the aggregate of all lease refusals, globally.
- Choose the metric to view the data points.
Here, the graphs for each of our metric dimensions have been added to a CloudWatch dashboard for an overall snapshot. For more information about how to accomplish this, see Using Amazon CloudWatch Dashboards. The following graphs show one failover relationship name (ABC).
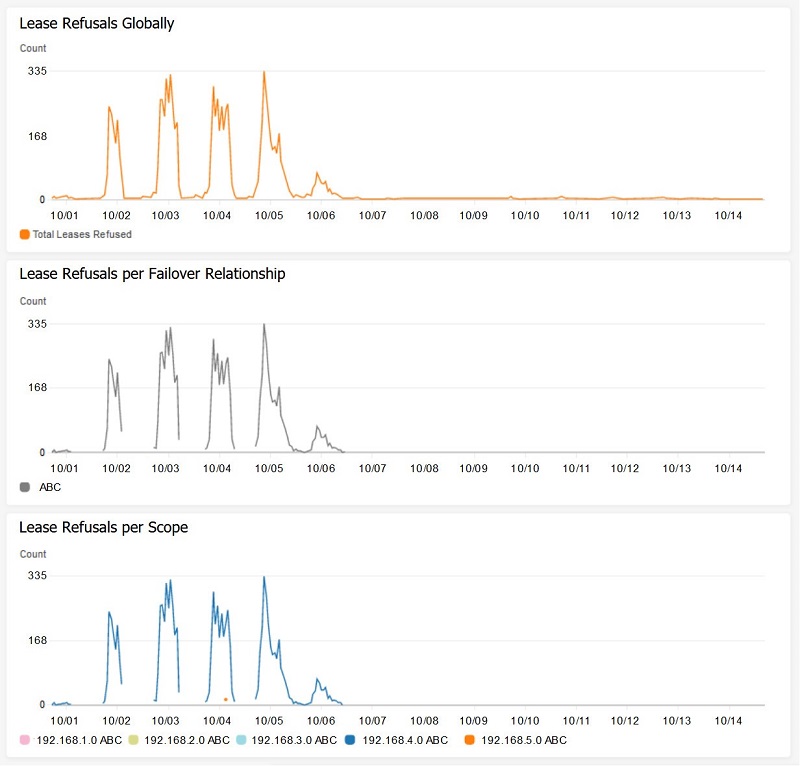
The graphs show that a particular DHCP scope (192.168.4.0) in the ABC failover relationship has a high volume of lease refusals as a result of scope exhaustion. In fact, it can be as many as 335 lease refusals per hour at one point in time.
Another observation is that the lines in the metric graphs break at certain times, and also never return to zero. This is because a value is posted only when Event 14 is detected. A zero is not posted at times when Event 14 is not detected. This simplifies the Lambda function and eliminates the need to make determinations at runtime about whether to post zeros. If there are a large number of failover relationships or scopes, the additional data visualization can have the effect of muddying the waters. Because the only concern is seeing when, where, and how many lease refusals are occurring, these metric graphs work efficiently and serve their purpose.
Conclusion
Using Kinesis Agent for Windows, our disparate DHCP server log data has been transformed into actionable CloudWatch metrics. This gives us the ability to identify DHCP scope exhaustion and the resulting customer impact. We can then work with the network engineering team to expand certain DHCP scopes with additional IP addresses to improve the overall customer experience.
The Amazon Kinesis Agent for Microsoft Windows makes your job more efficient. It speeds up results by letting you focus on building your solution. You don’t get bogged down with implementing solutions to collect and store log data. We hope that this use case sparked your curiosity to use Amazon Kinesis Agent for Microsoft Windows for more creative and sophisticated purposes, especially when taking advantage of the full breadth of AWS services. There are so many possibilities when using Amazon Kinesis Agent for Microsoft Windows.
Additional Resources
- Kinesis Agent for Windows User Guide
- Kinesis Agent for Windows download
- Kinesis Agent for Windows source code
- Blog: Collect, parse, transform and stream Windows events, logs, and metrics using Amazon Kinesis Agent for Microsoft Windows
- Blog: Build More Reliable and Secure Windows Services Using Amazon Kinesis Agent for Microsoft Windows
- Blog: Persist Streaming Data to Amazon S3 using Amazon Kinesis Firehose and AWS Lambda
- Blog: Amazon Kinesis – Setting up a Streaming Data Pipeline
About the Author
 Ted Balsimo is a Systems Development Engineer at Amazon Web Services.
Ted Balsimo is a Systems Development Engineer at Amazon Web Services.