Containers
Cross region replication in Amazon ECR has landed
Michael Brown and Michael Hausenblas
Replicating container images across regions in Amazon Elastic Container Registry (ECR) automatically has been one of the most asked features and we’re glad to be able to share the good news with you: it has landed. Where previously you had to implement the replication yourself you can now leave the heavy lifting to us and focus on building and running your applications. In this post we explain how the Cross Region Replication (CRR) feature works in ECR and how you can start benefiting from it.
Replication is configured at the ECR private registry level. This means, when you turn it on, all private ECR repositories in the registry automatically copy images to multiple other repositories in different accounts and/or regions, reducing pull latency that make your containers start up faster as they can now pull images in-region. Images in different regions also help you comply with disaster recovery requirements since the artifacts are geographically dispersed.
To get started you simply enable replication, choose the destination accounts and regions you want ECR to copy images to. After this, every time you push an image to the private repository, ECR automatically replicates the image. If the repository does not yet exist in the destination region, CRR automatically creates it. If you replicate across accounts, your destination account must first grant necessary permissions to the source account.
Use case scenario
As a motivational use case scenario, consider two teams working in different geographical regions. Let’s say the development team is based out of the US and the team responsible for the deployment is based out of Europe. In such a setup the CRR-enabled workflow would now look as follows:

The development team would, for example, use AWS CodePipeline to create a container image and pushes it into a private CRR-enabled ECR repository in the us-west-2 region. This is what we call the source region and said image is now, thanks for CRR, automatically replicated to the destination region eu-west-1 where the deploy team can use the image in container orchestrators such as Amazon EKS or Amazon ECS.
With this overall setup out of the way, let’s move on to a practical walkthrough.
CRR in action
In the following we walk you through the usage of the new ECR CRR feature, based on the motivational use case example above. We publish an image in the us-west-2 region, let the CRR magic do its work and then pull in eu-west-1.
First, you need to enable CRR from us-west-2 region as the source, choosing the destination regions (eu-west-1 in our case, a single region). To do that, select “Registries” from the left-hand menu, select your “Private” registry and click the “Edit” button in the right upper corner. This should take you to a view as shown in the following:
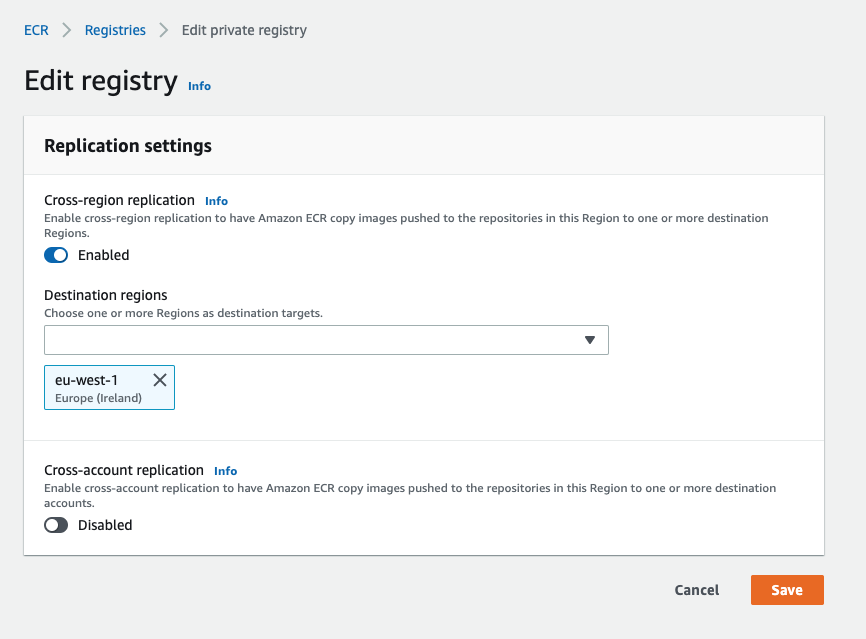
NOTE In this walkthrough we’re replicating the container image in the same account. If you’re using different accounts for source and destination regions, you would enable cross-account replication above and in addition would have to configure a registry permissions policy to allow CRR across accounts.
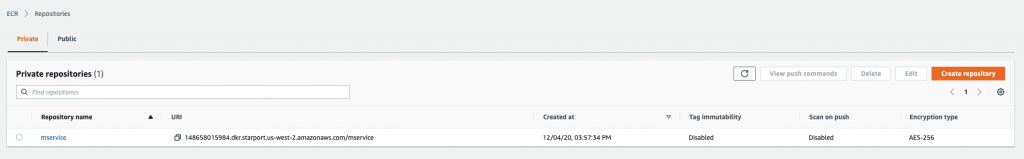
Now we can create the repository in the source region (us-west-2):
Next, we authenticate in the source region:
aws ecr get-login-password --region us-west-2 | \
docker login --username AWS --password-stdin \
123456789012.dkr.ecr.us-west-2.amazonaws.comIn above command as well as in the following shown below, make sure that you replace 123456789012 with your own account ID.
And now we can push a container image to our repo, in the source region (us-west-2):
$ docker push 123456789012.dkr.ecr.us-west-2.amazonaws.com/mservice:42 16:10:49
The push refers to repository [123456789012.dkr.ecr.us-west-2.amazonaws.com/mservice]
30cca227097d: Pushed
cd7100a72410: Pushed
42: digest: sha256:497108730bb719d606c1f75be33f310b018ed30d18be884fa00b189aceed5e59 size: 738Let’s now switch our roles mentally and move to the destination region eu-west-1. Let’s verify that ECR CRR works and in fact automatically replicated our image across the two regions.
We do this by pulling the image in the destination region (note the region in the image URL 123456789012.dkr.ecr.eu-west-1.amazonaws.com/mservice:42):
$ aws ecr get-login-password --region eu-west-1 | \
docker login --username AWS --password-stdin \
123456789012.dkr.ecr.eu-west-1.amazonaws.com
$ docker pull 123456789012.dkr.ecr.eu-west-1.amazonaws.com/mservice:42 16:17:02
42: Pulling from mservice
Digest: sha256:497108730bb719d606c1f75be33f310b018ed30d18be884fa00b189aceed5e59
Status: Downloaded newer image for 123456789012.dkr.ecr.eu-west-1.amazonaws.com/mservice:42
123456789012.dkr.ecr.eu-west-1.amazonaws.com/mservice:42That was easy, right? Note that the flow stays the same if you’re replicating across accounts, only the permissions required change.
Before we wrap up, let’s consider some operational things, from costs to replication semantics.
Considerations
With CRR you can now enjoy fine-grained replication in ECR, just like in ECR Public where we automatically replicate images. We replicate the container images along with the metadata, however vulnerability findings are not replicated.
This feature does not introduce any new pricing dimensions. Images stored in a destination repository incur ECR storage charges in that account, similar to what a you see if you push images yourself. Data transferred when copying images across regions incur ECR data transfer out charges based on the source repository’s Region. See the ECR Pricing page for more details on ECR storage and data transfer out charges. To give you a better estimate for data transfer charges, ECR will display the amount of data that was replicated in each source repository in GB-months.
What’s next?
We’re working on a number of CRR enhancements to make it even more useful and convenient to use for you. We expect to release in the near to mid future, amongst others, the following:
- Replication status APIs to surface the progress of the replication process for an image.
- The ability to add filters so that only a subset of repositories and images are replicated.
- Notifications on replication events such as the completion of a copy.
- Support for manifest lists.
We hope that with the introduction of Cross Region Replication in ECR you are now in a position to move another piece of undifferentiated heavy lifting off your plate. Let us know how you’re using this new feature and keep an eye on our container roadmap for more news.
