Front-End Web & Mobile
Using Okta as an Identity Provider for GraphQL APIs with AWS AppSync
This article was written by Jana Gnanachandran and Raghavarao Sodabathina, Enterprise Solutions Architects, AWS
September 14, 2021: Amazon Elasticsearch Service has been renamed to Amazon OpenSearch Service. See details.
AWS AppSync is a managed serverless GraphQL service that simplifies application development by letting you create a flexible API to securely access, manipulate, and combine data from one or more data sources with a single network call. With AppSync, developers can build scalable applications on a range of data sources, including Amazon DynamoDB NoSQL tables, Amazon Aurora Serverless relational databases, Amazon OpenSearch Service (successor to Amazon Elasticsearch Service) clusters, HTTP/REST APIs, and serverless functions powered by AWS Lambda.
There are four ways you can authorize applications to interact with your GraphQL API in AppSync. You define which authorization type to use by specifying one of the following modes in your AWS AppSync API:
- API_KEY, to authorize clients based on API keys.
- AWS_IAM, to authorize clients based on AWS Identity and Access Management (IAM).
- OPENID_CONNECT, to authorize clients based on OpenID Connect identity providers such as Okta or Auth0
- AMAZON_COGNITO_USER_POOLS, to authorize clients based on Amazon Cognito User Pools.
You can also mix and match multiple authorization modes in a single API. For more information on AppSync’s built-in security and authorization features, see our GraphQL security primer blog post.
In this article we walk you through the integration between Okta, an AWS Competency Partner and popular Identity-as-a-Service (IDaaS) solution, and AppSync using OpenID Connect (OIDC) to authorize GraphQL API calls. The following diagram depicts a sample architecture of a generic integrated solution between Okta and AppSync over OpenID Connect.

In the following sections you learn how to configure both Okta and AppSync then test the integration with a secure GraphQL API backed by DynamoDB in minutes and in 22 easy steps.
Okta Setup
1.Sign up for an Okta account then log in to the service.
2. After activation, you will be assigned an Okta domain URL and a temporary password. This domain URL is your OpenID Connect provider domain (issuer URL)
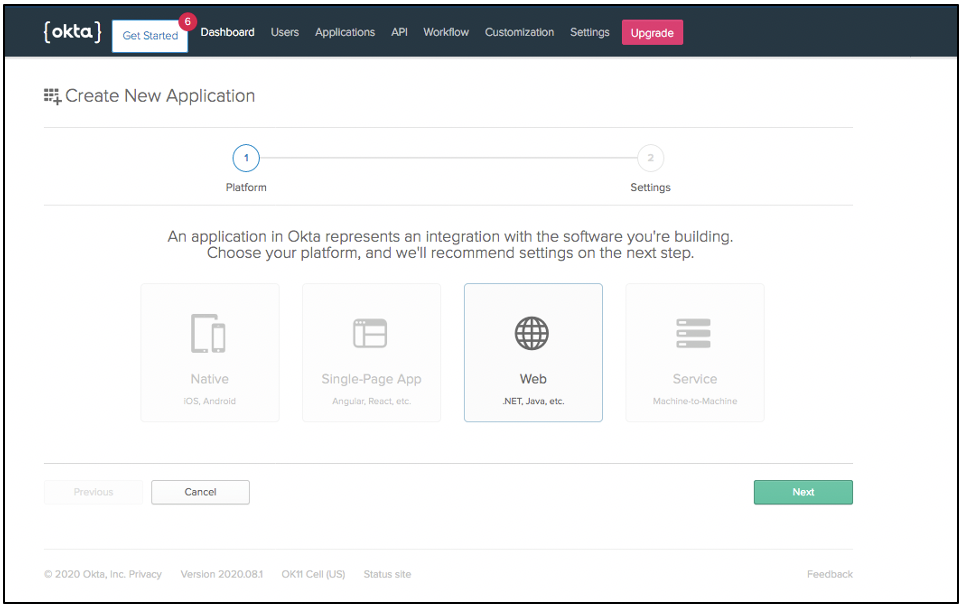
3. Create a Web application (.NET, Java,Node.js or Python) by selecting Add Web App. On the next screen, select Web (.NET , Java, etc) and then click on the Next button to proceed.
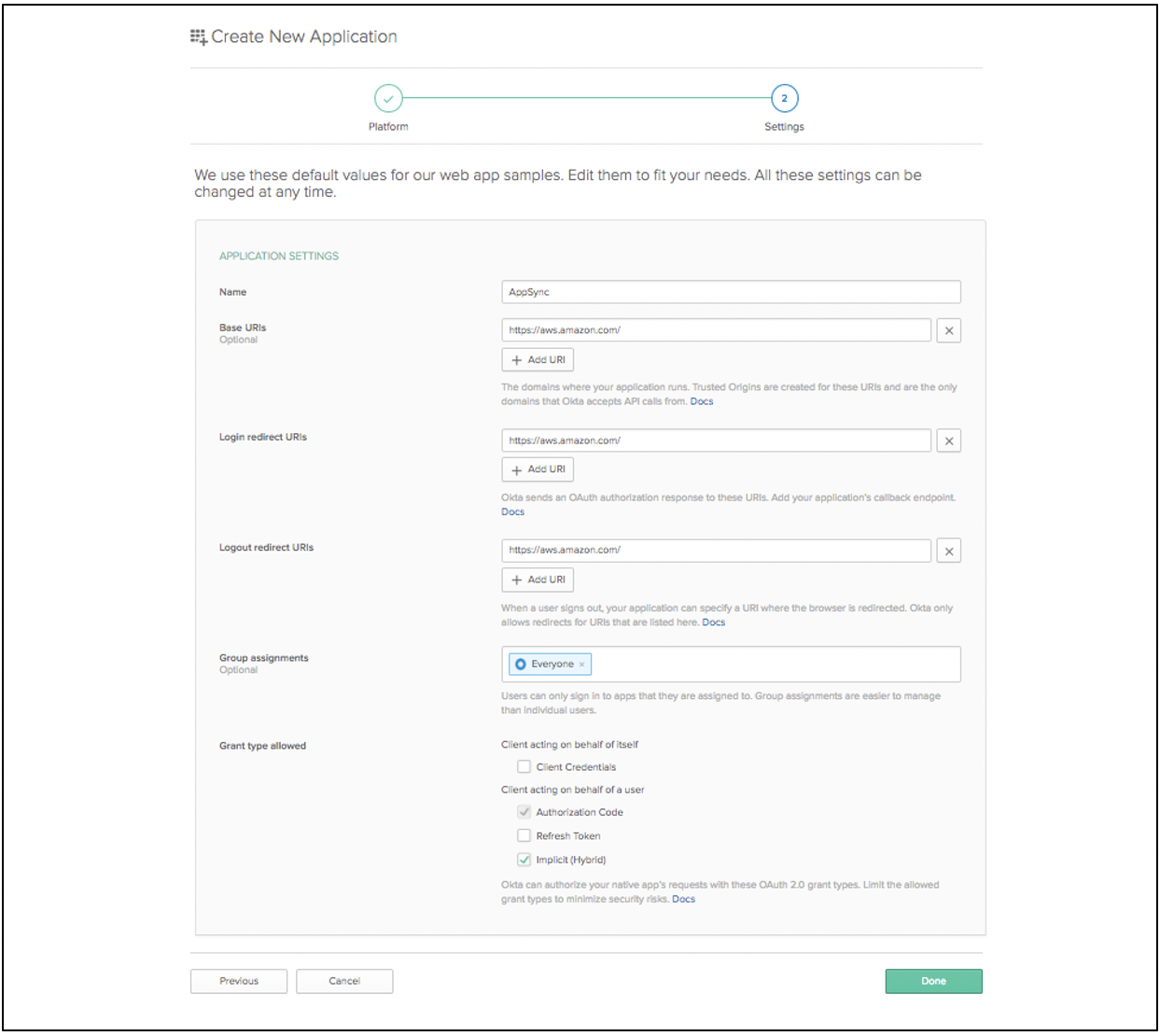
4. On the next screen, for the purpose of this article, we use https://aws.amazon.com as Base URI, Login redirect URI and Logout redirect URI. For Group assignments, keep the default Everyone. For Grant type allowed, check Authorization code and Implicit (Hybrid). Click on Done to complete the web application creation.
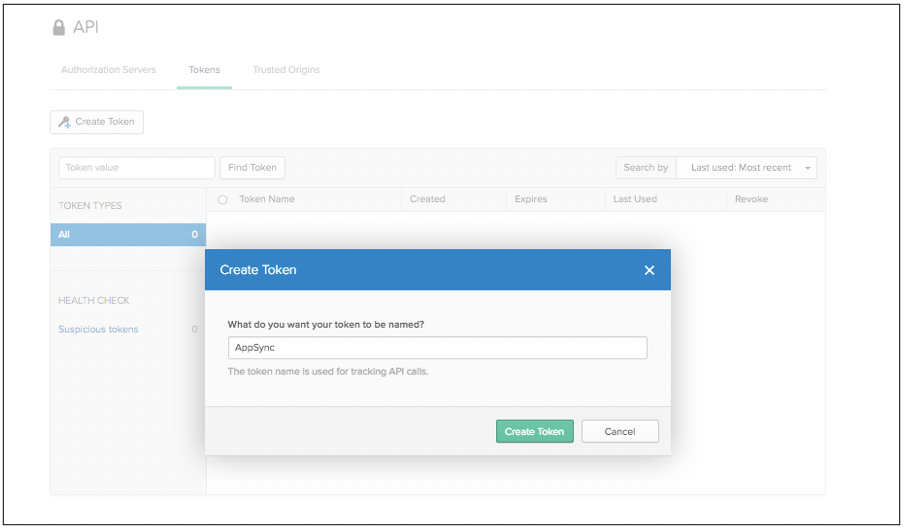
5. Next click on the Get Started button then the Create Token button.
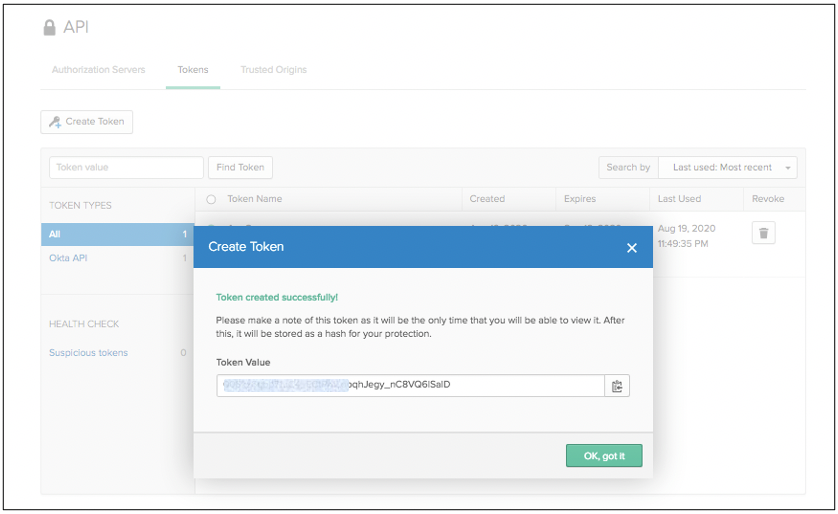
6. Take note of the generated token.
7. On the dashboard also take a note of the Org URL.

8. Finally, select Applications and take note of your web application Client ID.

AppSync Setup
1. Log in to the AppSync console and click the create API button.
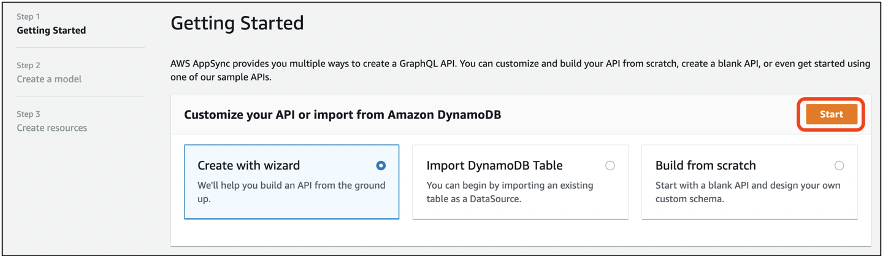
2. Select the Create with wizard option and click on the Start button.
3. For this example, we create a main Employee type comprised of employee id, name, city, state, and country. In the Configure model fields section add the required fields of your API and use the default options in the Configure model table section. Click the Create button to proceed.

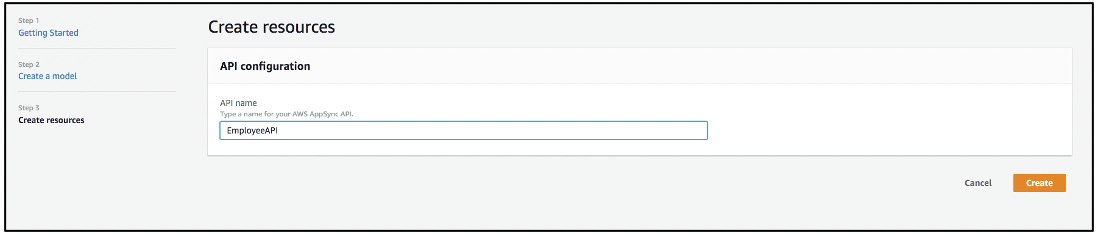
4. Next define a name for your API and click the Create button to start the GraphQL API as well as the DynamoDB data source creation process.
5. Go to Settings on the left menu. Under Default authorization mode, select Open ID Connect from the drop-down.
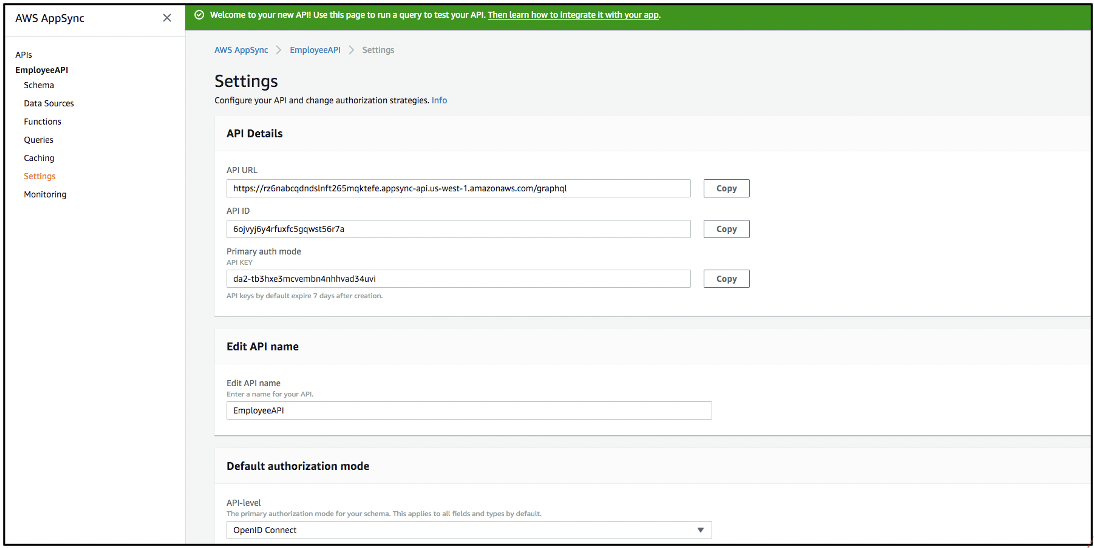
6. Under Configuration, enter your Okta domain name in the OpenID Connect provider domain (URL) and your Okta client ID under Client ID then, click on the Save button.
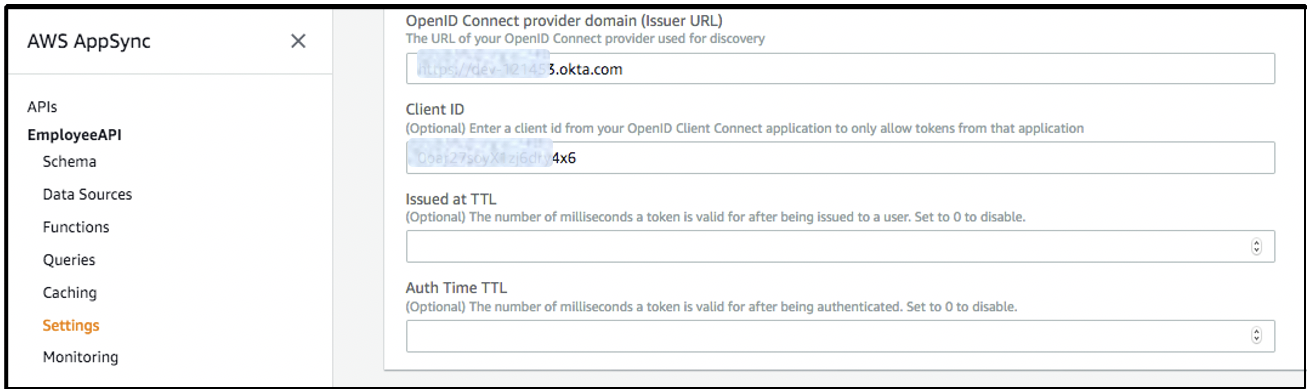
Your AppSync API has been created and it’s ready for testing. You have completed the OpenID Connect configuration steps to set up Okta as an identity provider in AppSync.
Testing
1. Once you have an ID Token from Okta, you can test your AppSync API. Access tokens from Okta do not work in this tutorial as they use a different base URL.
2. Use the following URL to get a JWT token from Okta:
https://<ACCOUNTID>.okta.com/oauth2/v1/authorize?client_id=<CLIENT_ID>&response_type=id_token&nonce=1234&scope=openid%20profile&state=test&redirect_uri=https://YOUR DOMAIN/
3. After logging in successfully, Okta will redirect to the redirect_url, for example:
https://www.YOURDOMAIN.com/#id_token=<ID_TOKEN …..> &state=test
4. Copy the JWT ID_TOKEN value.
5. On the AppSync console, select Queries from the left menu and paste the token from Okta in the text box next to the orange execute query button.
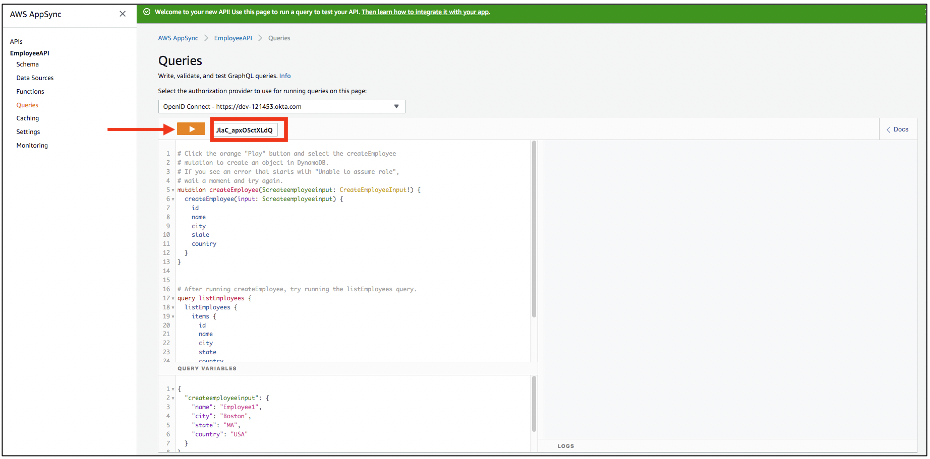
6. We can add new employee records using a GraphQL mutation. In this example, we add two employee records, Employee1 from Boston, MA, and Employee2 from Dallas, TX as shown below. You can add the employee details under the Query Variables section. Click on the execute query button, and select the createEmployee mutation as highlighted below.

7. The employee records can be fetched using GraphQL queries. Select the listEmployees query and click the execute query button to fetch the employee records created in the previous step.

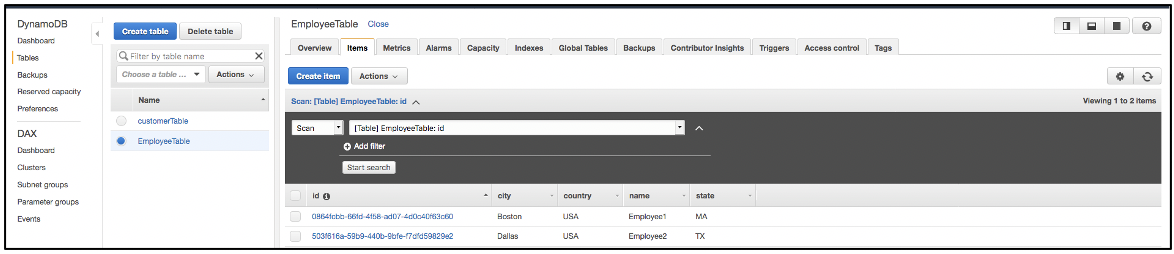
8. To confirm the employee records were created in the DynamoDB table, go to the Data Sources section on the left menu, select the DynamoDB table to open the DynamoDB console. You should see the two employee records created through AppSync and authorized by Okta.
Now your AppSync API is ready and you can connect to it from a client application using the AppSync SDK, the Amplify clients, or any other GraphQL client. You can also configure additional authorization business logic directly in AppSync resolvers as well as capture user information directly from the JWT tokens by leveraging the $context.identity object.
Conclusion
In this post, we showed how to set up Okta as identity provider on AppSync. We also demonstrated how quickly and easily you can create APIs by using AppSync with DynamoDB as an AppSync data source. With this solution, you now have a fully managed, highly available GraphQL API that uses Okta as the custom identity provider for your users. You can also get a jump-start by checking the AWS AppSync Developer Guide, which provides guidance on how to build applications using GraphQL with robust database, search, and compute capabilities with AppSync.
 Jana Gnanachandran is an Enterprise Solutions Architect at AWS, focusing on Data Analytics, AI/ML and Serverless platforms. He helps AWS customers across numerous industries to design and build highly scalable data-driven analytical solutions and accelerate their cloud adoption. In his spare time, he enjoys playing tennis, 3D printing and photography.
Jana Gnanachandran is an Enterprise Solutions Architect at AWS, focusing on Data Analytics, AI/ML and Serverless platforms. He helps AWS customers across numerous industries to design and build highly scalable data-driven analytical solutions and accelerate their cloud adoption. In his spare time, he enjoys playing tennis, 3D printing and photography.
 Raghavarao Sodabathina is an Enterprise Solutions Architect at AWS, focusing on Data Analytics, AI/ML and Serverless platforms. He engages with customers to create innovative solutions that address customer business problems and accelerate the adoption of AWS services. In his spare time, Raghavarao enjoys spending time with his family, reading books, and watching movies. Raghavarao holds a Masters of Engineering from the Indian Institute of Science, Bangalore.
Raghavarao Sodabathina is an Enterprise Solutions Architect at AWS, focusing on Data Analytics, AI/ML and Serverless platforms. He engages with customers to create innovative solutions that address customer business problems and accelerate the adoption of AWS services. In his spare time, Raghavarao enjoys spending time with his family, reading books, and watching movies. Raghavarao holds a Masters of Engineering from the Indian Institute of Science, Bangalore.