AWS Cloud Operations Blog
Create AWS Config rules efficiently with Generative AI
AWS Config enables businesses to assess, audit, and evaluate the configurations of their AWS resources by leveraging AWS Config rules that represent your ideal configuration settings. For example a Security Group that allows ingress on port 22 should be marked as noncompliant. AWS Config provides predefined rules called managed rules to help you quickly get started in evaluating your resources and AWS Config can be further leveraged to automate compliance at scale by using custom rules.
You can create Config custom rules that use AWS Lambda functions written in Node.js or in Python. However, writing AWS Config custom rules can be a challenge for those who are new to writing code and this is where Amazon CodeWhisperer can help. Trained on billions of lines code, Amazon CodeWhisperer is a general purpose, machine learning-powered code generator that provides you with code recommendations in real time. As you write code, CodeWhisperer automatically generates suggestions based on your existing code and comments. . Whether you have experience writing AWS Config custom rules or you are just getting started, CodeWhisperer can help you generate the code needed to start evaluating your resources with AWS Config custom rules.
The AWS Config Rules Development Kit (RDK) helps developers set up, author and test AWS Config custom rules. The RDK is designed to support a Compliance-as-Code workflow that is intuitive and productive. It abstracts the undifferentiated heavy lifting associated with deploying AWS Config rules backed by custom lambda functions, and provides a streamlined develop-deploy-monitor iterative process. By using the RDK and CodeWhisperer together, an experienced or novice developer can efficiently create AWS Config custom rules and easily deploy them into their AWS environment.
In this blog post, you will learn how you can get started with Amazon CodeWhisperer in your Integrated Development Environment (IDE) and use it with the RDK to create an AWS Config custom rule. The solution deploys an AWS Config custom rule that evaluates Amazon Elastic Block Store (Amazon EBS) volumes that are not gp3 volumes. Amazon EBS volumes of type gp3 can provide savings of up to 20% over gp2 volumes. We will be using CodeWhisperer to create an AWS Config custom rule which will identify EBS volumes as noncompliant that are not taking advantage of this cost savings opportunity.
Overview of solution
The solution starts with an AWS Cloud9 instance as the IDE where you will author the code and install the RDK. The AWS RDK will create the file and folder structure needed in order to start authoring AWS Config custom rule to evaluate EBS volumes. Amazon CodeWhisperer will help you generate the code needed to create the AWS Config custom rule and use the code suggestions for the custom rule function logic. Once the rule function is complete, you will then use the RDK to deploy the rule into your AWS environment which the RDK will automate by leveraging AWS CloudFormation in background. CloudFormation will then provision your AWS Config custom rule to allow you to evaluate the Amazon EBS volumes. If one of your EBS volumes is found to be non-compliant, you can then run an automation to update the volume type to gp3 by using AWS Systems Manager Automation. The diagram below highlights the data flow for this solution.
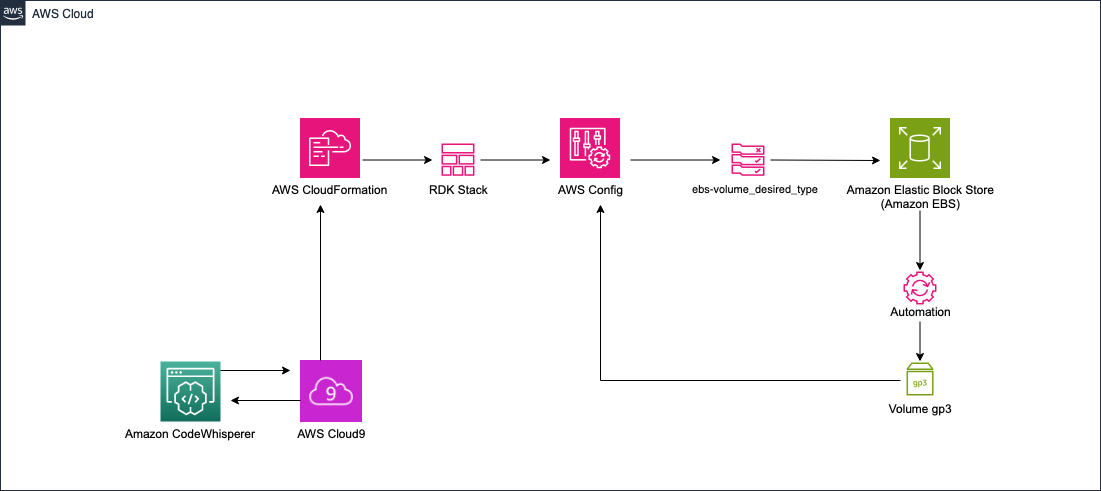
Figure 1 – Solution overview of custom AWS Config rule written using Amazon CodeWhisperer
Walkthrough
At a high level, you will complete the following steps throughout this blog post:
- Install the AWS Rules Development Kit (RDK)
- Create an AWS Config custom rule with the RDK
- Generate function logic for AWS Config custom rule
- Deploy AWS Config custom rule using the RDK
- Clean up environment
- (Optional) Remediate noncompliant resource(s)
Prerequisites
For this walkthrough, you should have the following prerequisites:
- An AWS account
- An Integrated Development Environment (IDE) supported by Amazon CodeWhisperer
- AWS Config enabled
- Amazon CodeWhisperer set up in a supported IDE (This example uses AWS Cloud9)
- One or more Amazon EBS volumes of type gp2
Install the RDK
Lets get started by installing the RDK in your existing Cloud9 environment.
- Navigate to your Cloud9 environment.
- In the terminal run the command:
python3 -m venv env
- Activate the environment by running:
source env/bin/activate
- Install the RDK by running:
pip install rdk
- If properly installed, you will see information about RDK usage, positional arguments, and optional arguments. You will also see:
“The RDK is a command-line utility for authoring, deploying, and testing custom AWS Config rules.” - Verify that the RDK is properly installed by running:
rdk -h.
- Run the following command to set up your AWS Config environment:
rdk init
Create AWS Config custom rule
- When you create the rule, specify that the runtime is python3.9, the resource type is an EBS volume, and the proper input parameters. In this example, the desired type is gp3 volumes.
- Enter the following command:
rdk create ebs-volume_desired_type --runtime python3.9 --resource-types AWS::EC2::Volume --input-parameters '{"desiredvolumeType":"gp3"}' - Your local Rule files are now created. Navigate to the parameters.json file. Make sure you have the proper parameters set up.
- Ensure that the key:value pair on line 10 is “SourceEvents”: “AWS::EC2::Volume”
By default your parameters.json file may have “SourceEvents”:”AWS::EC2::Instance” See figure 2:
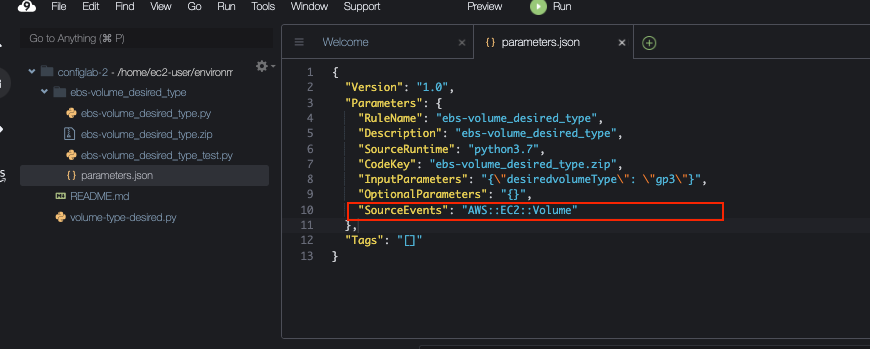
Figure 2 – Parameters file created for you by the RDK
- Next, add the custom logic to mark any EBS volume as non-compliant if it is not the gp3 type.
- To do this, open the file named ebs-volume-desired-type.py.
- Navigate to line 50, where it says # Add your custom logic here. This is where you will add the function code that you generate with CodeWhisperer.
Generate function logic for AWS Config custom rule
- Make sure that the auto-suggestions are resumed
- Prompt CodeWhisperer with :
The user actions to get the code recommendations on Cloud9 for Windows and MacOS are listed below. As you start typing, CodeWhisperer will start suggesting. To accept a suggestion hit TAB key.
To manually fetch a code suggestion:
MacOS: Option + C
Windows: Alt + C
Figure 3 – Generate the function code by prompting CodeWhisperer.
- If you review the code suggestion provided. It will evaluate the configuration item property of volumeType equals rule parameter of desired_volume_type. But if you notice the rule parameter will need to be updated to match the desiredvolumeType rule parameter you defined when creating the rule. Below is what the code would look like:
Deploy custom AWS Config rule using the RDK
- After you see “OK”, deploy the rule by running the command:
rdk deploy ebs-volume_desired_type
In the background, when deploying an AWS Config custom rule with the RDK, you are provisioning an AWS CloudFormation stack that deploys a Lambda function with the custom rule.
- After you see “Config deploy complete” navigate to the AWS Config console.
- When you select Rules, you now see the ebs-volume_desired_type rule as shown in figure 5.
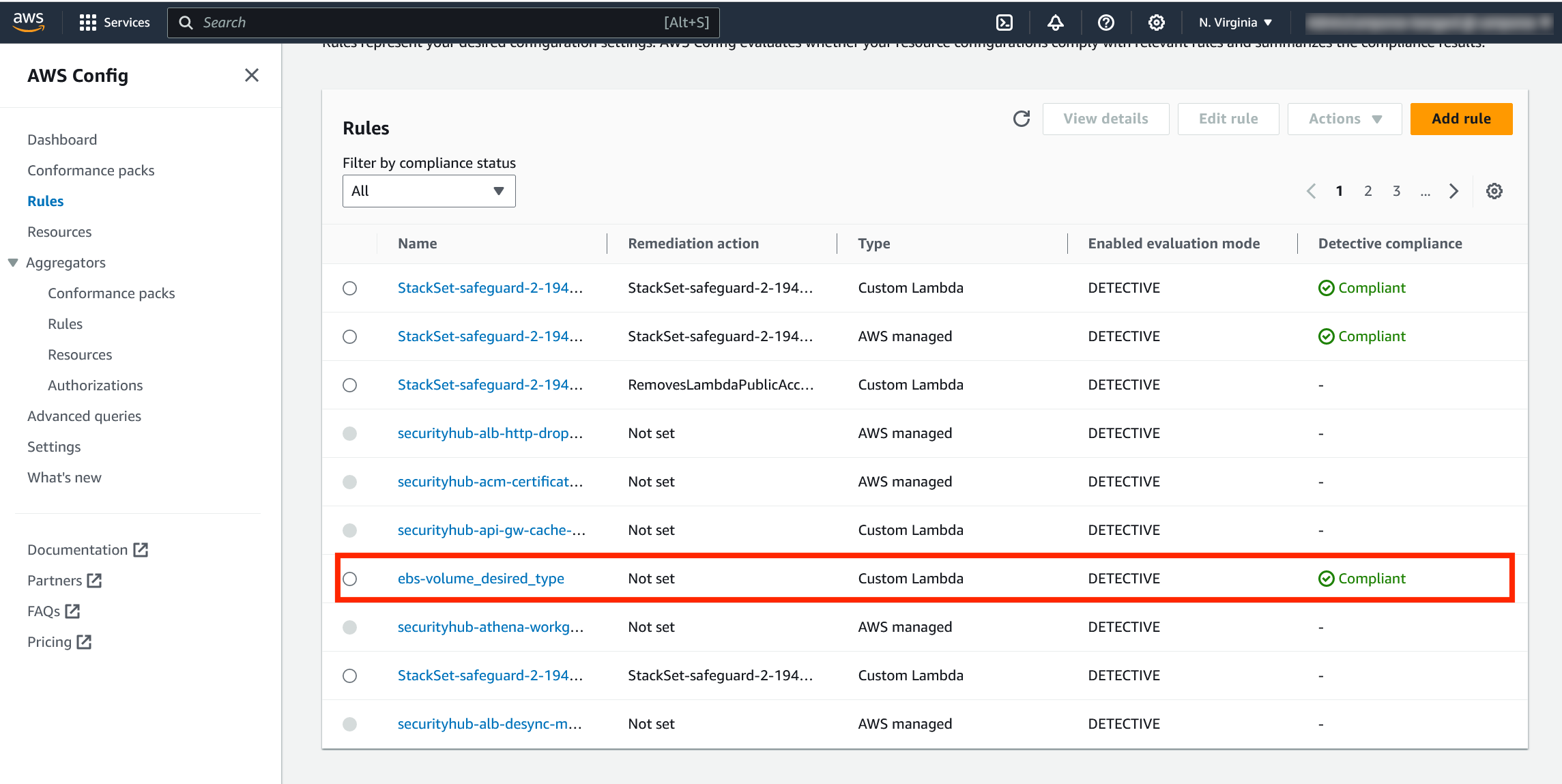
Figure 5 – Custom AWS Config rule in deployed via the RDK
- Select the AWS Config custom rule to view the details.
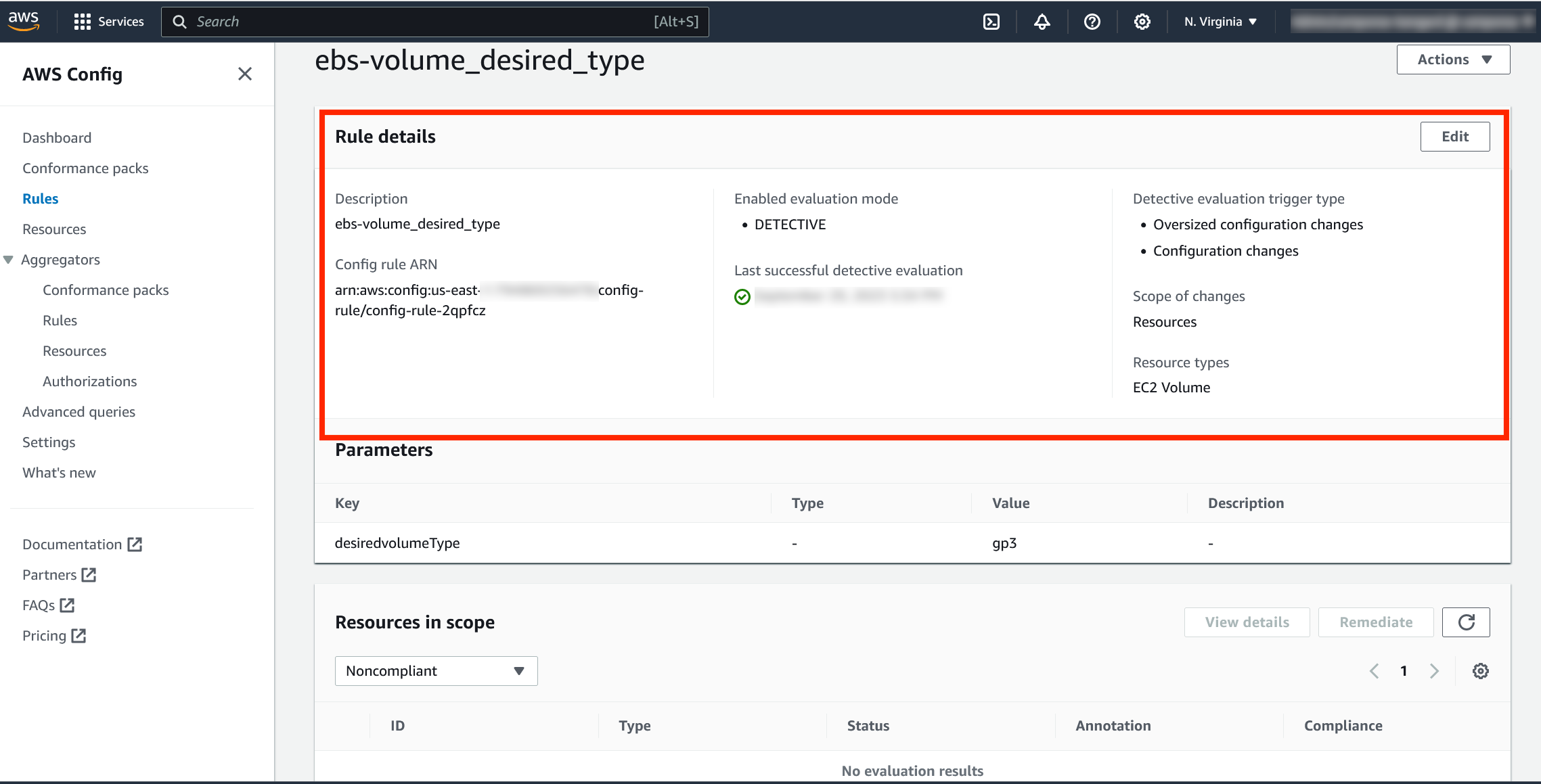
Figure 6 – Rule details for the custom AWS Config rule deployed via the RDK
- Scroll to the bottom of the console and view the resources in scope. Once the rule evaluates, you will see any EBS volumes that are not of type gp3 marked as Noncompliant.
Note: It may take a few minutes for the rule to successfully evaluate the first time. Refresh the page if you do not see any non gp3 EBS volumes marked as Noncompliant.

Figure 7 – Resources in scope of our custom AWS Config rule
Next steps
If you would like to take the solution further, you can add a remediation action to the rule which can automatically modify your EBS volumes to be of the desired type with the AWS Systems Manager AWSConfigRemediation-ModifyEBSVolumeType automation document. See the following documentation to add a remediation action to the Config custom rule that you created:
- Remediating noncompliant resources with AWS Config rules
- Remediate noncompliant AWS Config rules with AWS Systems Manager Automation runbooks
Cleaning up
To avoid incurring future charges, delete the resources you will no longer use.
- Navigate to the CloudFormation console.
- Delete the stack created by the AWS Config RDK, the name should be similar to the rule that you created. For example, the stack is named ebs-volumedesiredtype.
Conclusion
In this blog post, you were able to create a AWS Config custom rule to evaluate the EBS volumes in your AWS account for your desired volume type. Since gp3 volumes can be extremely cost effective, you want to make sure that you leverage these volume types wherever possible. By leveraging CodeWhisperer, you were able to create an AWS Config custom rule with minimal knowledge of Python or the RDK. CodeWhisperer can generate code recommendations that can help you efficiently develop code no matter your coding experience.
