AWS Security Blog
Tag: Announcements
Building AI defenses at scale: Before the threats emerge
At AWS, we’ve spent decades developing processes and tools that enable us to defend millions of customers simultaneously, wherever they operate around the world. AI has been an extremely helpful addition to the automation our security and threat intelligence teams do every day, and we’re still early in this journey. Our AI-powered log analysis system […]
ACM will no longer cross sign certificates with Starfield Class 2 starting August 2024
February 20, 2026: We updated the first question in the FAQ to list to add Amazon ClodFront as a representative AWS service with an example. This is not the full list of services that consume certificates from ACM and should only be used as a reference. November 13, 2025: We updated the first question in […]
AWS achieves QI2/QC2 qualification to host critical data and workloads from the Italian Public Administration
Italian version June 24, 2024: This post has been updated to inform you that all AWS cloud services have been qualified by the Italian National Cybersecurity Agency (ACN). Amazon Web Service (AWS) is pleased to announce that, starting from April 15, 2024, all AWS cloud services are now QC2 qualified according to the Italian Agency […]
How to seamlessly domain join Amazon EC2 instances to a single AWS Managed Microsoft AD Directory from multiple accounts and VPCs
You can now share a single AWS Directory Service for Microsoft Active Directory (also known as an AWS Managed Microsoft AD) with multiple AWS accounts within an AWS Region. This capability makes it easier and more cost-effective for you to manage directory-aware workloads from a single directory across accounts and Amazon Virtual Private Clouds (Amazon […]
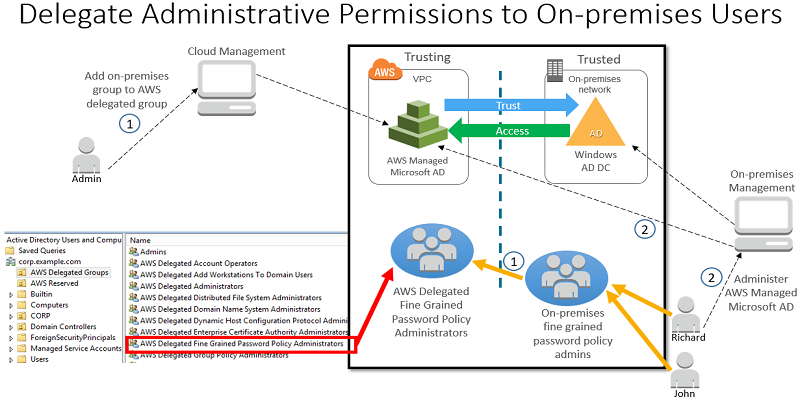
How to Delegate Administration of Your AWS Managed Microsoft AD Directory to Your On-Premises Active Directory Users
You can now enable your on-premises users administer your AWS Directory Service for Microsoft Active Directory, also known as AWS Managed Microsoft AD. Using an Active Directory (AD) trust and the new AWS delegated AD security groups, you can grant administrative permissions to your on-premises users by managing group membership in your on-premises AD directory. […]
Announcing the New AWS Customer Compliance Center
AWS has the longest running, most effective, and most customer-obsessed compliance program in the cloud market. We have always centered our program around customers, obtaining the certifications needed to provide our customers with the proper level of validated transparency in order to enable them to certify their own AWS workloads [download .pdf of AWS certifications]. […]
Announcing AWS Organizations: Centrally Manage Multiple AWS Accounts
Today, AWS launched AWS Organizations: a new way for you to centrally manage all the AWS accounts your organization owns. Now you can arrange your AWS accounts into groups called organizational units (OUs) and apply policies to OUs or directly to accounts. For example, you can organize your accounts by application, environment, team, or any […]
Automated Reasoning and Amazon s2n
In June 2015, AWS Chief Information Security Officer Stephen Schmidt introduced AWS’s new Open Source implementation of the SSL/TLS network encryption protocols, Amazon s2n. s2n is a library that has been designed to be small and fast, with the goal of providing you with network encryption that is more easily understood and fully auditable. In […]
Coming March 2015: Upgrades to IAM Policy Validation
Several weeks ago, we released documentation for the AWS Identity and Access Management (IAM) policy grammar and published a back-to-school policy grammar blog post to let you know of common errors in policies. To help you ensure that your policies match your intentions, we are taking policy validation a step further. Starting March 2015, any new or updated policy must […]
AWS Secures DoD Provisional Authorization
I’m very excited to share that AWS has received a DISA Provisional Authorization under the DoD Cloud Security Model’s impact levels 1-2 for all four of AWS’s Infrastructure Regions in the U.S., including AWS GovCloud (US). With this distinction, AWS has shown it can meet the DoD’s stringent security and compliance requirements; and as a […]