AWS Security Blog
Coming March 2015: Upgrades to IAM Policy Validation
Several weeks ago, we released documentation for the AWS Identity and Access Management (IAM) policy grammar and published a back-to-school policy grammar blog post to let you know of common errors in policies. To help you ensure that your policies match your intentions, we are taking policy validation a step further. Starting March 2015, any new or updated policy must comply with the IAM policy grammar. The good news is that the majority of your policies are probably not affected by this change—they are fine as they are! If you have noncompliant policies, you will be able to identify and correct them more easily. If you have a policy that does not comply, you will notice a new notification in the IAM console along with a validation tool you can use to help correct your policies.
Why are we making this change?
We want to help ensure that your policies reflect your intentions. For example, if you have a policy statement with contradictory “Allow” and “Deny” Effect elements, the policy is accepted, but interpreted using only the last Effect element in the statement. For example, the following policy will evaluate to “Allow.” However, you might have intended for “Deny” to be used instead.
{
“Version”: “2012-10-17”,
“Statement”: [
{
“Effect”: “Deny”,
“Effect”: “Allow”,
“Action”: “ec2:* “,
“Resource”: “*”
}
]
}
What does this change mean for your policies?
Rest assured that all of your existing policies will continue to be enforced as they currently are. However, starting March 2015, you will not be able to revise and save any policy that does not comply with the IAM policy grammar. If you have created your own policy templates or use automated scripts to create new policies, you might need to update them.
How do I know if my policies are noncompliant?
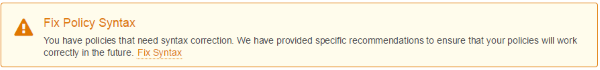
All you need to do is sign in to the IAM console. If you see the yellow banner (shown following this paragraph), your AWS account has policies that require editing. If you don’t see the banner, all your policies are compliant and you’re good to go!
How do I fix my noncompliant policies?
To help you fix your policies, a tool is provided that lists all the noncompliant policies in your account along with a policy recommendation. Let’s walk through how to fix your policies using the IAM console.
Step 1: Sign in to the IAM console.
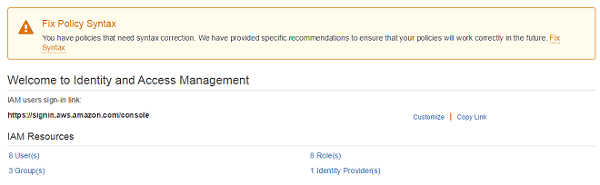
Step 2: Click Fix Syntax.

A page with a list of all your noncompliant policies appears.
Note: If you have only a few policies to update, we recommend using the console. However, if you have a large number of noncompliant policies that were generated from a script, we recommend you correct your script and rerun it to update your policies.

Step 3: Click the policy you want to update. In this example, I am going to update EC2Policy.

Step 4: Review the recommended changes to your policy.
Note: You should make modifications in the top policy window if our recommended policy does not convey your intentions. The existing policy is shown below the recommended policy.
Step 5: Click Apply Changes after you are comfortable with the changes. At this stage, the policy is updated in your account and you are brought back to your list of remaining invalid policies, if any remain.

Repeat these steps for all noncompliant policies. As soon as your account has no more noncompliant policies, the yellow banner will disappear.
Conclusion
To ensure that your policies reflect your intentions, we encourage you to address as soon as possible policies that do not pass the stricter validation.
Please feel free to reference the policy validation documentation and policy grammar language to help guide you through this process. As always, if you have questions or suggestions, please visit our AWS IAM forum.
–Brigid