AWS Security Blog
Securing Access to AWS Using MFA–Part 1
In this series of blog posts, we’ll walk through different ways to keep your AWS resources secure using AWS Multi-Factor Authentication (MFA).
As a best practice, we strongly recommend that you secure access to your account with AWS MFA. It’s a simple way to add an extra layer of protection on top of your username and password.
With AWS MFA enabled, when a user signs in to an AWS website, they’ll be prompted for their username and password (the first factor – what they know), as well as for an authentication code from their AWS MFA device (the second factor – what they have). Taken together, these multiple factors provide increased security by preventing access to your AWS environment unless a valid MFA code is supplied.
Accessing the AWS Management Console
The console is a widely used web GUI for managing your AWS environment. Both your root account and any AWS Identity and Access Management (IAM) users who have been assigned a password can access the console. We recommend activating MFA on both root and highly privileged IAM users (e.g. able to access sensitive data, manage key resources, or have IAM management permissions).
Root account – You should always activate MFA on your root account because it has unlimited privileges (i.e. can use any service, modify any resource, access any data in your AWS environment). From a security perspective, using root for everyday use of AWS isn’t ideal because you can’t control root permissions. In fact, best practice is to store your root account credentials in a safe place and only interact with AWS using IAM users granted minimal necessary privileges.
IAM users – Depending on the permissions assigned to an IAM user, it can have admin-level privileges similar to root or be limited to access a single service or resource. Just as with root accounts, best practice is to secure IAM user login with MFA if your IAM user is highly privileged.
Getting Started
Step 1: Get an MFA token
AWS supports multiple device formats that work for both root accounts and IAM users. Visit the links below to download a virtual MFA app or purchase a physical MFA token.
Virtual MFA – Use an MFA app on your smartphone, tablet, or computer. Download the official AWS MFA app or another compatible app such as Google Authenticator. Virtual MFA is available at no extra charge.
Hardware MFA – Made by Gemalto, a third-party partner. These cost $12.99 per token, with free shipping if you have Amazon Prime.
Step 2: Activate the MFA token
Root account – Visit the IAM console, click Manage MFA Device, and follow the on-screen instructions.

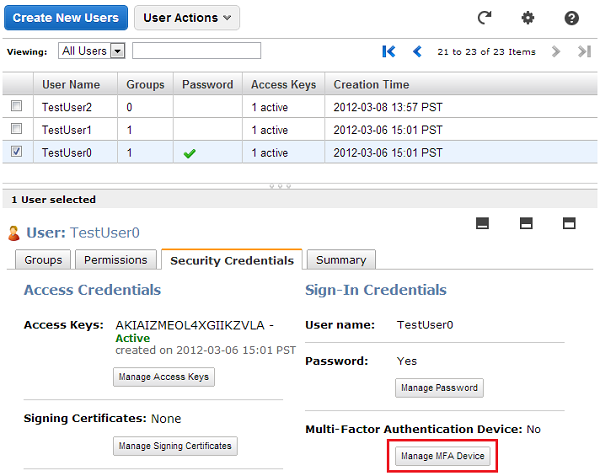
IAM user – Visit the IAM console, select an IAM user in the Users tab, and then click Manage MFA Device on the Security Credentials tab. Follow the on-screen instructions.
Step 3: Sign in
After MFA is activated, whenever you try to sign in to an AWS website as root or as an IAM user, you’ll be prompted to enter an MFA code. After entering the code, you’ll have access as normal to AWS.
Now you know how to further enhance the security of your AWS Management Console access using MFA. In part 2 of this series, we’ll discuss how you can use MFA to secure programmatic AWS API access for your IAM users.
Jim Scharf
Director, AWS Identity and Access Management