AWS Security Blog
Tag: Amazon EventBridge
How to export AWS Security Hub findings to CSV format
December 22, 2022: We are working on an update to address issues related to cloudformation stack deployment in regions other than us-east-1, and Lambda timeouts for customers with more than 100,000 findings. AWS Security Hub is a central dashboard for security, risk management, and compliance findings from AWS Audit Manager, AWS Firewall Manager, Amazon GuardDuty, […]
Automatically block suspicious DNS activity with Amazon GuardDuty and Route 53 Resolver DNS Firewall
In this blog post, we’ll show you how to use Amazon Route 53 Resolver DNS Firewall to automatically respond to suspicious DNS queries that are detected by Amazon GuardDuty within your Amazon Web Services (AWS) environment. The Security Pillar of the AWS Well-Architected Framework includes incident response, stating that your organization should implement mechanisms to […]
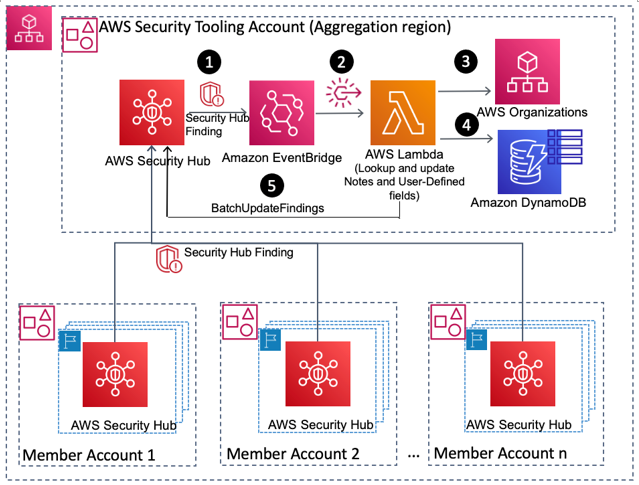
How to enrich AWS Security Hub findings with account metadata
In this blog post, we’ll walk you through how to deploy a solution to enrich AWS Security Hub findings with additional account-related metadata, such as the account name, the Organization Unit (OU) associated with the account, security contact information, and account tags. Account metadata can help you search findings, create insights, and better respond to […]
Automatically resolve Security Hub findings for resources that no longer exist
In this post, you’ll learn how to automatically resolve AWS Security Hub findings for previously deleted Amazon Web Services (AWS) resources. By using an event-driven solution, you can automatically resolve findings for AWS and third-party service integrations. Security Hub provides a comprehensive view of your security alerts and security posture across your AWS accounts. Security […]
Correlate security findings with AWS Security Hub and Amazon EventBridge
March 31, 2022: We updated the CloudFormation template, accessed via the Launch Stack link, in this blog post. In this blog post, we’ll walk you through deploying a solution to correlate specific AWS Security Hub findings from multiple AWS services that are related to a single AWS resource, which indicates an increased possibility that a […]
How to automate incident response to security events with AWS Systems Manager Incident Manager
Incident response is a core security capability for organizations to develop, and a core element in the AWS Cloud Adoption Framework (AWS CAF). Responding to security incidents quickly is important to minimize their impacts. Automating incident response helps you scale your capabilities, rapidly reduce the scope of compromised resources, and reduce repetitive work by your […]
Creating a notification workflow from sensitive data discover with Amazon Macie, Amazon EventBridge, AWS Lambda, and Slack
Following the example of the EU in implementing the General Data Protection Regulation (GDPR), many countries are implementing similar data protection laws. In response, many companies are forming teams that are responsible for data protection. Considering the volume of information that companies maintain, it’s essential that these teams are alerted when sensitive data is at […]