AWS Security Blog
Tag: Permissions
New Features for IAM Policy Summaries – Resource Summaries
In March, we introduced policy summaries, which make it easier for you to understand the permissions in your AWS Identity and Access Management (IAM) policies. Today, we added three new features to policy summaries to improve the experience of understanding and troubleshooting your policies. First, we added resource summaries for you to see the resources […]
Introducing an Easier Way to Delegate Permissions to AWS Services: Service-Linked Roles
Some AWS services create and manage AWS resources on your behalf. To do this, these services require you to delegate permissions to them by using AWS Identity and Access Management (IAM) roles. Today, AWS IAM introduces service-linked roles, which give you an easier and more secure way to delegate permissions to AWS services. To start, […]
Move Over JSON – Policy Summaries Make Understanding IAM Policies Easier
Today, we added policy summaries to the IAM console, making it easier for you to understand the permissions in your AWS Identity and Access Management (IAM) policies. Instead of reading JSON policy documents, you can scan a table that summarizes services, actions, resources, and conditions for each policy. You can find this summary on the […]
How to Assign Permissions Using New AWS Managed Policies for Job Functions
Today, AWS Identity and Access Management (IAM) made 10 AWS managed policies available that align with common job functions. AWS managed policies enable you to set permissions using policies that AWS creates and manages, and with a single AWS managed policy for job functions, you can grant the permissions necessary for network or database administrators, […]
How to Enable MFA Protection on Your AWS API Calls
Multi-factor authentication (MFA) provides an additional layer of security for sensitive API calls, such as terminating Amazon EC2 instances or deleting important objects stored in an Amazon S3 bucket. In some cases, you may want to require users to authenticate with an MFA code before performing specific API requests, and by using AWS Identity and […]
IAM Service Last Accessed Data Now Available for the Asia Pacific (Mumbai) Region
In December, AWS Identity and Access Management (IAM) released service last accessed data, which helps you identify overly permissive policies attached to an IAM entity (a user, group, or role). Today, we have extended service last accessed data to support the recently launched Asia Pacific (Mumbai) Region. With this release, you can now view the […]
AWS IAM Service Last Accessed Data Now Available for South America (Sao Paulo) and Asia Pacific (Seoul) Regions
In December, AWS Identity and Access Management (IAM) released service last accessed data, which helps you identify overly permissive policies attached to an IAM entity (a user, group, or role). Today, we have extended service last accessed data to support two additional regions: South America (Sao Paulo) and Asia Pacific (Seoul). With this release, you […]
Now Available: Get Even More Details from Service Last Accessed Data
In December, AWS Identity and Access Management (IAM) released service last accessed data, which shows the time when an IAM entity (a user, group, or role) last accessed an AWS service. This provided a powerful tool to help you grant least privilege permissions. Starting today, it’s easier to identify where you can reduce permissions based […]
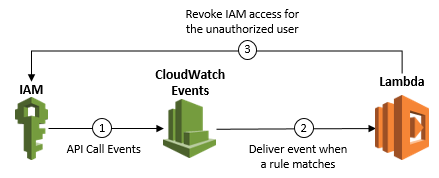
How to Detect and Automatically Revoke Unintended IAM Access with Amazon CloudWatch Events
Update on October 24, 2018: Note that if you do not author the Lambda function correctly, this setup can create an infinite loop (in this case, a rule that is fired repeatedly, which can impact your AWS resources and cause higher than expected charges to your account). The example Lambda function I provide in Step […]
The IAM Console Now Helps Prevent You from Accidentally Deleting In-Use Resources
Deleting unused resources can help to improve the security of your AWS account and make your account easier to manage. However, if you have ever been unsure of whether an AWS Identity and Access Management (IAM) user or role was being used actively, you probably erred on the side of caution and kept it. Starting […]