AWS Security Blog
Tag: Security Blog
New IRAP reports for Australian customers are now available in AWS Artifact
Following our Information Security Registered Assessors Program (IRAP) assessment in December 2019, we are excited to announce that we have additional new IRAP documents now available in AWS Artifact as a result of the recent IRAP assessment at the PROTECTED level that was finished in June 2020. This includes an IRAP compliance report for 33 […]
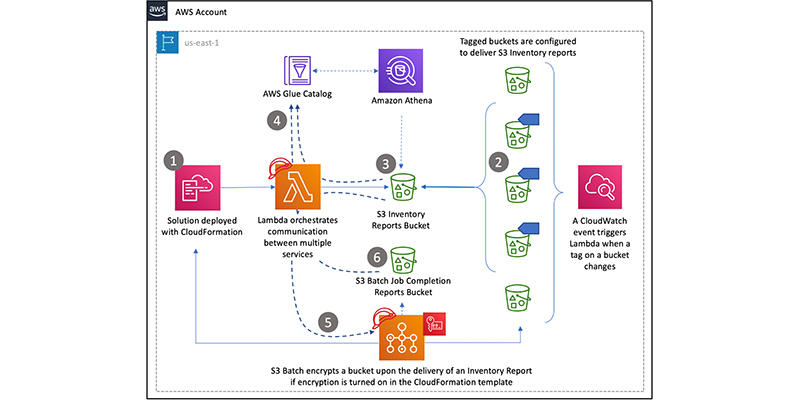
How to retroactively encrypt existing objects in Amazon S3 using S3 Inventory, Amazon Athena, and S3 Batch Operations
November 1, 2021: AWS KMS is replacing the term customer master key (CMK) with AWS KMS key and KMS key. The concept has not changed. To prevent breaking changes, AWS KMS is keeping some variations of this term. More info. Amazon Simple Storage Service (S3) is an object storage service that offers industry-leading scalability, performance, […]
Identify, arrange, and manage secrets easily using enhanced search in AWS Secrets Manager
AWS Secrets Manager now enables you to search secrets based on attributes such as secret name, description, tag keys, and tag values. With this launch, you can easily identify, arrange, and manage your secrets into logical groups that can then be used by specific applications, departments, or employees. For example, you can use the Secrets […]
How to use resource-based policies in the AWS Secrets Manager console to securely access secrets across AWS accounts
AWS Secrets Manager now enables you to create and manage your resource-based policies using the Secrets Manager console. With this launch, we are also improving your security posture by both identifying and preventing creation of resource policies that grant overly broad access to your secrets across your Amazon Web Services (AWS) accounts. To achieve this, […]
Updates to the security pillar of the AWS Well-Architected Framework
We have updated the security pillar of the AWS Well-Architected Framework, based on customer feedback and new best practices. In this post, I’ll take you through the highlights of the updates to the security information in the Security Pillar whitepaper and the AWS Well-Architected Tool, and explain the new best practices and guidance. AWS developed […]
New PCI DSS on AWS Compliance Guide provides essential information for implementing compliant applications
Our mission in AWS Security Assurance Services is to ease Payment Card Industry Data Security Standard (PCI DSS) compliance for all Amazon Web Services (AWS) customers. We work closely with the AWS audit team to answer customer questions about understanding their compliance, finding and implementing solutions, and optimizing their controls and assessments. The most frequent […]
Monitoring AWS Certificate Manager Private CA with AWS Security Hub
Certificates are a vital part of any security infrastructure because they allow a company’s internal or external facing products, like websites and devices, to be trusted. To deploy certificates successfully and at scale, you need to set up a certificate authority hierarchy that provisions and issues certificates. You also need to monitor this hierarchy closely, […]
Code signing using AWS Certificate Manager Private CA and AWS Key Management Service asymmetric keys
August 31, 2021: AWS KMS is replacing the term customer master key (CMK) with AWS KMS key and KMS key. The concept has not changed. To prevent breaking changes, AWS KMS is keeping some variations of this term. More info. In this post, we show you how to combine the asymmetric signing feature of the […]
Spring 2020 PCI DSS report now available with 124 services in scope
Amazon Web Services (AWS) continues to expand the scope of our PCI compliance program to support our customers’ most important workloads. We are pleased to announce that six services have been added to the scope of our Payment Card Industry Data Security Standard (PCI DSS) compliance program. These services were validated by Coalfire, our independent […]
What is a cyber range and how do you build one on AWS?
In this post, we provide advice on how you can build a current cyber range using AWS services. Conducting security incident simulations is a valuable exercise for organizations. As described in the AWS Security Incident Response Guide, security incident response simulations (SIRS) are useful tools to improve how an organization handles security events. These simulations […]